Computer disposal san jose: A Practical Guide for Businesses
For businesses managing computer disposal in San Jose, the process isn't just a cleanup task—it's a critical operational necessity. Here in the heart of Silicon Valley, technology moves incredibly fast, making a secure and compliant IT asset disposition (ITAD) strategy absolutely essential for protecting sensitive data and meeting California's tough environmental laws.
Why a Strategic Approach to E-Waste Matters in San Jose
Managing the lifecycle of IT assets in San Jose comes with its own unique set of challenges. The sheer volume of retired technology creates a massive stream of electronic waste. To put it in perspective, one major local facility processes nearly 1.2 million pounds of electronics every month.
That staggering figure really highlights the need for IT managers to have a formal disposition strategy in place. You can find more details on the scale of local e-waste and what it means for the region on our blog.
Failing to manage this process properly opens the door to serious risks. For any organization, the primary concerns are always the same:
- Data Security: Old hard drives, servers, and even networking gear can be goldmines of confidential company, customer, or employee data. One misstep in disposal can lead to a very expensive data breach.
- Environmental Compliance: California law, specifically the Electronic Waste Recycling Act, has a zero-tolerance policy for dumping electronics in landfills. Getting caught can mean substantial fines and a black eye for your company's reputation.
- Resource Management: Just handing off old equipment to a recycler might mean you're leaving money on the table. A lot of assets can be refurbished and resold, recovering some of your initial investment.
A well-defined computer disposal plan is your first line of defense against data breaches and regulatory penalties. It transforms a potential liability into a structured, secure, and even profitable business function.
This guide goes beyond the basic recycling tips. We're laying out a step-by-step framework specifically for San Jose IT directors and managers, covering everything from the initial risk assessment and certified data destruction to navigating complex regulations. We’ll show you how to turn a compliance chore into a strategic advantage that reinforces your commitment to both data security and environmental stewardship.
Starting with an Asset Inventory and Risk Assessment
Before a single piece of equipment leaves your office, your first line of defense is a detailed inventory and risk assessment. For any business tackling computer disposal in San Jose, this isn't just a box-checking exercise; it's the foundation for a secure, compliant process that prevents data from walking out the door.
Think of it as creating a manifest for every retiring device. This step is about more than just counting computers. You need a comprehensive log that connects each physical asset to the data it holds, giving you a clear roadmap for what comes next.
Building Your Disposition Log
A solid inventory log captures a few critical details for every asset you're getting rid of. Don't overcomplicate it, but make sure you get the essentials down.
- Serial Number: The unique ID that lets you track a device from your office to its final destination.
- Asset Tag Number: Your company's internal number, linking the hardware back to your own records.
- Device Type: Is it a laptop, desktop, server, switch, or something else? Be specific.
- Data Sensitivity Level: This is the most important part. Classify the data on it—is it public, internal, confidential, or regulated information like PII?
This audit-secure-recycle workflow is the core of any responsible ITAD strategy.
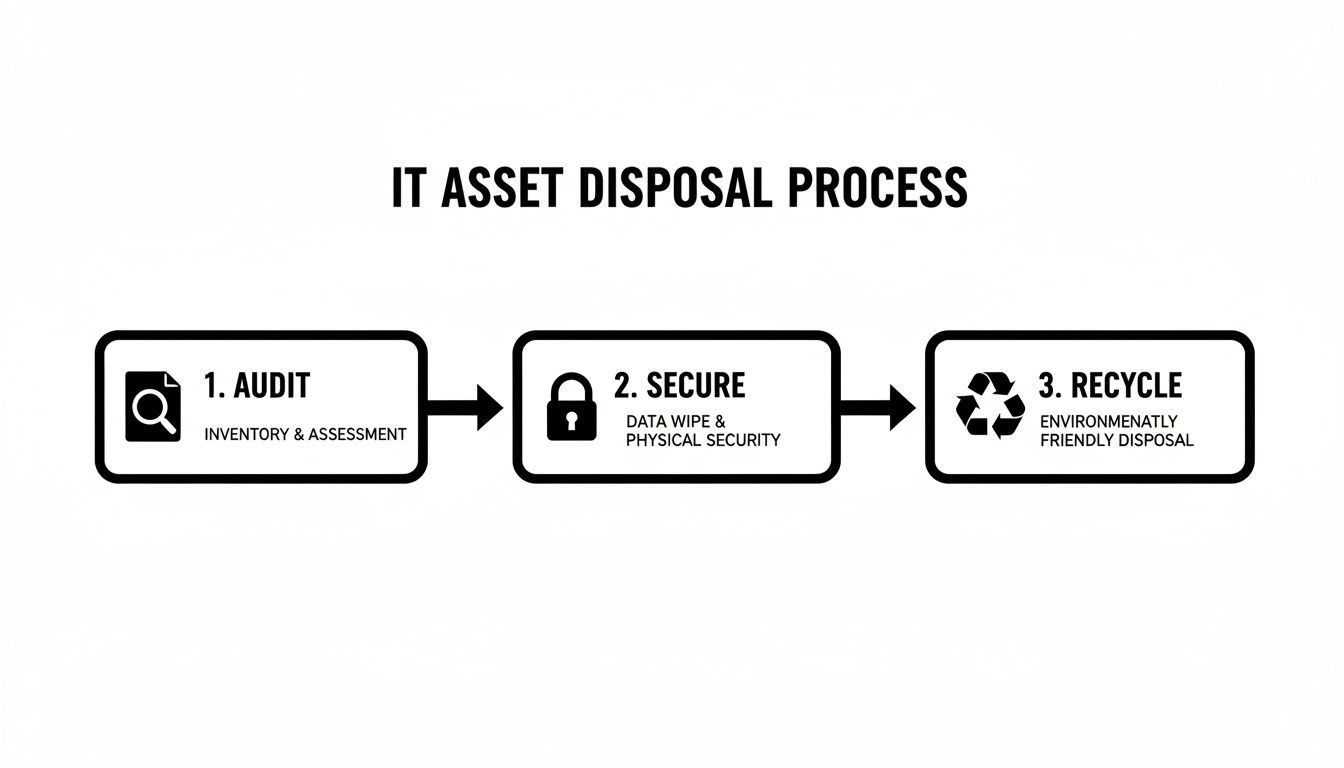
As you can see, it all starts with that initial audit. Get that right, and the securing and recycling stages become much more straightforward and defensible.
Classifying Assets for Different Paths
Not all hardware is the same, and your inventory helps you sort everything into the right buckets. For instance, an IT manager might see a batch of three-year-old laptops with sales data and tag them for certified data wiping and potential resale to recoup some value.
On the other hand, a ten-year-old server that once held sensitive customer PII? That gets flagged immediately for physical destruction. No questions asked.
Documenting the disposition path for each asset isn't just a best practice; it's your proof of due diligence. This record becomes invaluable during an audit, demonstrating you took deliberate, risk-based steps to protect sensitive information.
This classification process lets you build a disposition plan that fits your security policies while also maximizing any potential return. To get more hands-on with this, check out our guide on IT asset management best practices for some practical frameworks.
A good partner can help you with this critical assessment, pointing out hidden risks and ensuring every device is handled correctly from the very start.
Choosing The Right Data Destruction Method
Here’s something a lot of people don't realize: simply hitting 'delete' on a file does absolutely nothing to remove it from a hard drive. For any San Jose business, where your client data and internal IP are your most valuable assets, making sure that data is gone for good isn't just a suggestion—it's a critical part of the disposal process.
The method you choose will come down to your specific security needs, what kind of assets you're retiring, and whether you want to try and resell the equipment.
This decision is much more than a simple operational choice. It's a core risk management function. Getting it wrong can leave your company exposed, but the right approach provides verifiable proof that you've met your compliance obligations.
Software Wiping For Asset Resale
If you’re retiring newer laptops or servers that still have some life left in them, software-based data wiping is usually the way to go. This process uses specialized software to overwrite every single sector of a hard drive with random data, often in multiple passes.
This makes the original data completely unrecoverable, meeting strict standards like NIST 800-88. The biggest advantage here is that the drive and the computer itself are left fully functional, which makes them perfect for refurbishment and resale. Think about a tech company upgrading a sales team's two-year-old MacBooks—this is the ideal scenario.
Degaussing For Magnetic Media
Degaussing is a bit more specialized but incredibly effective for magnetic storage like old tape backups or certain types of hard disk drives (HDDs). It involves a powerful machine that blasts the media with an intense magnetic field, instantly scrambling the magnetic domains on the drive's platters and destroying all the data.
It's fast and thorough, but it also renders the hard drive totally useless afterward. Degaussing is a great choice for wiping huge batches of old magnetic media, though it won't work on Solid-State Drives (SSDs) since they don't rely on magnetism to store data.
Physical Shredding For Maximum Security
When you absolutely, positively cannot afford for data to be recovered, nothing beats physical destruction. This is the only acceptable method for devices that held highly sensitive financial records, patient information governed by HIPAA, or your company's secret sauce.
An industrial shredder literally grinds hard drives, SSDs, and other media into tiny, mangled pieces of metal and plastic.
On-site shredding is the gold standard for security. It allows your team to watch your assets get destroyed with their own eyes before they even leave your building. This creates an airtight chain of custody and undeniable proof that the data is gone forever.
Deciding which method is best often comes down to balancing security needs, compliance mandates, and the potential for asset reuse.
Comparing Data Destruction Methods
| Method | Best For | Compliance Level | Allows for Reuse? | Key Benefit |
|---|---|---|---|---|
| Software Wiping | Newer, valuable assets (laptops, servers) intended for resale or redeployment. | High (Meets NIST 800-88) | Yes | Preserves asset value for remarketing. |
| Degaussing | Large quantities of old magnetic media like HDDs and backup tapes. | Very High | No | Extremely fast for bulk magnetic media. |
| Physical Shredding | Highly sensitive data, end-of-life assets, or when maximum security is required. | Highest | No | Irreversible destruction, perfect for compliance. |
Ultimately, the goal is to make a choice that aligns with your risk tolerance and operational goals. For any San Jose business, the sheer volume of old tech makes this a constant challenge. In fact, global e-waste was projected to hit 93.5 million tons back in 2016, and it's only grown since. This is why having a certified partner is so important.
No matter which path you take, always demand a Certificate of Data Destruction. This document is your official proof that you followed proper procedures to protect sensitive information. You can explore a variety of secure data destruction services that provide this critical documentation.
Meeting California and Industry Compliance Standards
When you're handling computer disposal in San Jose, you're not just recycling—you're navigating a dense web of regulations. The biggest one on the radar is California's Electronic Waste Recycling Act. This state law is crystal clear: it's illegal to dump computers, monitors, and other electronics into landfills. Everything must go to a certified recycling facility.
Getting this wrong isn't just an environmental mistake. It can lead to some pretty hefty fines and put a serious dent in your company's reputation. That’s why partnering with a certified vendor isn't just a good idea; it's a fundamental requirement for doing business responsibly here.
Why R2 and E-Stewards Certifications Matter
As you look for a disposal partner, two certifications should be non-negotiable: R2 (Responsible Recycling) and e-Stewards. These aren't just logos for a website. They represent rigorous, third-party audited standards that prove a recycler is committed to top-tier environmental protection, data security, and worker safety.
- R2 Certification: This standard covers the entire lifecycle of your old electronics, from the moment they leave your office to their final destination. It guarantees that hazardous materials are handled correctly and that every data destruction process is secure and fully documented.
- e-Stewards Certification: Often considered the gold standard, e-Stewards enforces a strict zero-tolerance policy against exporting hazardous e-waste to developing nations. It puts an even stronger emphasis on airtight data security and environmental justice.
Choosing a certified recycler is your best defense against future liability. You can get a better sense of what it takes to become an R2 certified electronics recycler and see why it’s such a critical credential. These certifications are your assurance that your old IT assets won't become the source of a data breach or an environmental headache down the road.
Adhering to Industry-Specific Rules
On top of California's laws, your own industry likely has specific rules for handling data. For healthcare organizations, HIPAA sets strict guidelines for protecting patient health information, even on equipment that's been retired for years. Likewise, financial institutions have to follow the Gramm-Leach-Bliley Act (GLBA) to protect customer financial data.
Your disposal process has to tick all these boxes. A hospital, for example, might require on-site physical shredding of every single hard drive to maintain a perfect, unbroken chain of custody and stay compliant with HIPAA.
A certified disposal process simplifies everything. It provides the necessary documentation—like Certificates of Data Destruction and Recycling—that serves as your official proof of compliance for any potential audit.
San Jose is a trailblazer in responsible waste management, boasting an impressive 74% diversion rate from local landfills. That sets a high bar. For IT directors managing computer disposal, it underscores just how important it is to work with partners who can meet these exacting standards. Businesses dealing with servers, laptops, and other e-waste can find similar success by partnering with compliant IT asset disposition specialists. You can discover more insights about electronic recycling standards at gerecycle.com.
Managing Logistics and Chain of Custody
A secure disposal process doesn’t end at your office door. Once you’ve identified, assessed, and wiped your assets, the next critical phase is getting them from your facility to their final destination. This is where a documented chain of custody becomes the backbone of your entire computer disposal san jose strategy.
This isn’t just about moving boxes from point A to point B. It's about ensuring every single device is tracked, accounted for, and secure at every moment. For a San Jose business decommissioning a data center, this meticulous tracking provides irrefutable proof that hundreds of sensitive assets were handled correctly, satisfying both internal policies and external auditors.

A professional ITAD partner manages this entire process for you. We use secure, GPS-tracked vehicles and trained personnel to handle your equipment, removing the logistical burden from your team and providing complete peace of mind.
The Anatomy of an Airtight Chain of Custody
The chain of custody is your official paper trail. It’s a series of documents that detail the journey of each IT asset, creating an unbroken and auditable record of who had what, and when. A weak or incomplete record can create significant compliance gaps, leaving your organization exposed.
Your vendor should provide comprehensive documentation that includes a few key elements.
- Serialized Asset List: This is the master manifest, matching the inventory you created. It lists every device by its unique serial number.
- Signed Transfer Receipts: Every time the assets change hands—from your team to our pickup driver, for instance—a signed receipt confirms the transfer.
- Secure Transport Records: Details about the vehicle and the logistics to ensure your assets are transported securely.
- Final Disposition Reports: This includes the essential Certificate of Data Destruction and Certificate of Recycling, which confirm the final outcome for each and every asset.
Think of the chain of custody as the legal story of your retired IT assets. It should be clear, detailed, and strong enough to stand up in an audit, proving you met your due diligence from beginning to end.
Preparing for a Seamless Pickup
When pickup day arrives, having your assets prepared ahead of time can make the whole process smooth and efficient. It also helps reinforce the security of the transfer itself.
- Stage Equipment Securely: Consolidate all assets in a secure, designated area with limited access. Avoid leaving pallets of computers sitting out in an open loading dock where they're vulnerable.
- Verify Pickup Personnel: We'll always provide the names of our drivers in advance. You should always verify their identity before releasing any equipment.
- Confirm the Asset Count: Before the truck is sealed and departs, your representative and our driver will sign off on the asset count, confirming it matches the initial manifest.
This meticulous approach ensures nothing gets lost in transit. For assets requiring the highest level of security, some businesses explore bringing onsite shredding near me directly to their facility, eliminating the transportation risk entirely for hard drives and other media. This approach provides immediate, witnessed destruction, offering the ultimate level of assurance before the remaining components are sent for recycling.
Turning Old Tech Into New Revenue with IT Asset Recovery
Not every retired computer needs to end up at the recycling plant. For many San Jose businesses, a good chunk of their old equipment still has significant market value. This is where IT Asset Value Recovery (ITAVR) comes in, turning what would be a disposal cost into a fresh revenue stream that can help offset the expense of your next technology upgrade.
It all starts with a straightforward assessment of your equipment's age and condition. A two-year-old fleet of high-performance laptops, for example, is going to have a much higher resale potential than a rack of decade-old desktops. An experienced partner can quickly size up your assets, cherry-picking the items that can be refurbished and sold on established secondary markets. It's the best way to squeeze every last drop of value from your original investment.
Strategic Donations and Building Community Goodwill
Beyond just selling old gear, donating functional equipment is another powerful option. This path offers strategic benefits that go far beyond just clearing out a storage closet. Gifting computers to local nonprofits, schools, or community centers not only helps organizations in need but can also unlock significant tax advantages for your business.
This approach is a direct investment in your corporate social responsibility (CSR) goals, strengthening your company's reputation right here in the San Jose community.
The most important thing to remember with any donation is data security. Your disposal partner absolutely must guarantee that every single device undergoes certified data wiping before it gets a second life. This protects your organization from risk while empowering local groups with the technology they need.
The Role of a Recovery Partner
Figuring out how to assess, wipe, refurbish, and sell used IT assets is a specialized skill. You don't want your IT team spending their valuable time trying to become e-commerce experts. That's why partnering with a specialist in computer disposal san jose who can manage the entire value recovery journey is so critical.
A good partner takes care of all the details for you, including:
- Fair Market Valuation: Accurately assessing what your equipment is actually worth on the open market.
- Certified Data Sanitization: Providing auditable proof that every byte of data has been permanently and securely erased.
- Logistics and Sales: Managing the entire resale process, from refurbishment and cleanup to finding qualified buyers.
This turnkey approach lets you focus on your core business while your partner works to maximize your financial return and ensure every asset is handled responsibly. It's how you turn a logistical headache into a smart financial decision.
Common Questions About Computer Disposal in San Jose
Even with a solid plan in place, we find that businesses still have questions when it's time to retire old IT gear. Here are a few of the most common things we get asked about computer disposal in San Jose.
Can My Business Just Throw Old Computers in the Dumpster?
That’s a hard no. Under California's Electronic Waste Recycling Act, it's illegal to send computers, monitors, or any other electronics to a landfill.
Think about it—those devices are full of materials like lead and mercury. Getting caught can lead to some hefty fines. All e-waste has to go to a certified recycler who knows how to handle those materials safely and responsibly.
What Kind of Paperwork Should I Get from My Disposal Vendor?
You need proof that you did everything by the book. At a minimum, you should always walk away with two key documents: a Certificate of Data Destruction for your hard drives and a Certificate of Recycling for the equipment itself.
For businesses that need an airtight audit trail, we also provide a serialized chain-of-custody report. This document follows every single asset—by serial number—from the moment we pick it up to its final destination, giving you a detailed, defensible record of your due diligence.
When security is paramount, nothing beats on-site hard drive shredding. You can physically watch us destroy your data-bearing devices before they even leave your building. It’s the go-to choice for companies in healthcare, finance, and other highly regulated fields.
Of course, secure off-site shredding is also an extremely safe and common option. The real key is working with a vendor who provides a fully documented chain of custody from start to finish. That's how you know nothing was left to chance.
Ready to take the complexity out of your IT asset disposition process? Dallas Fortworth Computer Recycling delivers secure, compliant, and nationwide computer disposal services. We provide certified data destruction and a fully documented chain of custody to protect your business. Learn more at https://dallasfortworthcomputerrecycling.com.
