Secure ITAD & electronic recycling austin tx — Your Austin guide
For any business in Austin, mishandling electronic recycling isn't just an environmental oversight—it's a massive security and financial liability. When you fail to properly manage old IT equipment, you're essentially leaving sensitive company files out in the open, exposing your organization to data breaches and serious regulatory penalties.
Why E-Waste Is a Major Business Risk in Austin

It’s easy for Austin businesses to see electronic waste, or e-waste, as just another disposal task—something to get off the to-do list. But this view misses the huge risks hiding inside that retired tech. Every old server, laptop, and company smartphone holds a treasure trove of sensitive information, from client lists and financial records to your most valuable intellectual property.
Simply tossing these devices in a dumpster or handing them over to an uncertified recycler is an open invitation to data thieves. The fallout from a breach goes way beyond a PR nightmare; it can lead to expensive lawsuits, a total loss of customer trust, and crippling fines for not complying with data privacy laws.
More Than Just a Green Initiative
While being environmentally responsible is important, professional e-waste management for businesses is really about managing risk. The City of Austin has a landfill ban on electronics, which means you can’t legally throw this equipment in the regular trash. That local rule alone forces companies to find a compliant way to handle their old IT assets.
This is where the line between consumer drop-off recycling and commercial IT asset disposition (ITAD) becomes crystal clear. A professional partner provides services built specifically to shield your organization from business risks:
- Legal Penalties: Staying clear of fines from Austin's landfill ban and other state regulations.
- Financial Loss: Preventing data breaches that can easily cost millions in recovery and legal fees.
- Data Security: Guaranteeing the complete, certified destruction of all sensitive information.
For IT leaders and procurement teams, the real goal of electronic recycling isn't just disposal. It's the secure and documented transfer of liability. A certified process ensures that once an asset leaves your building, your organization is no longer on the hook for what happens to it.
The Hidden Dangers in Your Storage Closet
Take a minute to think about that back closet filled with old computers and hard drives. That isn't just clutter—it's a stockpile of dormant risk. Every single device represents a potential backdoor for a data breach if it ever falls into the wrong hands. A professional electronic recycling Austin TX service is designed to turn that liability into a secure, buttoned-up process.
A certified partner gives you a documented chain of custody, covering everything from secure pickup and transport to certified data destruction and responsible materials recycling. This end-to-end management creates an auditable paper trail, proving your company did everything by the book. It’s all about changing your perspective—from seeing e-waste as trash to recognizing it as a critical piece of your company's security and compliance strategy.
Navigating Austin E-Waste Rules for Businesses
For any business in Austin, figuring out the local and state rules for electronics recycling isn't just about being green—it's a fundamental part of staying compliant. The regulations can feel like a maze at first, but they really come down to a few key ideas that protect both your company and the community. Get it wrong, and you could be looking at serious fines and legal trouble.
The biggest rule to know is the City of Austin's ban on landfilling electronics. This is non-negotiable. Your business cannot legally toss old computers, servers, monitors, or phones into the regular commercial trash. This one local ordinance puts the responsibility squarely on your shoulders to find a proper, documented way to dispose of all your retired IT equipment.
This ban completely changes how you have to manage your old gear. Unlike a household with an old TV, commercial operations generate e-waste at a scale and complexity that a simple drop-off center just can't handle.
The Texas Recycles Computers Program Gap
Now, you might have heard about the Texas Recycles Computers Program and thought, "Great, the state has this covered." Unfortunately, this is where a huge compliance gap opens up for most businesses. While the program was a good first step, its focus is surprisingly narrow.
The state program is really aimed at equipment sold to consumers and maybe a small home-based business. Back in 2007, the Texas Commission on Environmental Quality (TCEQ) knew that used computers were a fast-growing problem full of heavy metals that needed to stay out of landfills. The program they created requires manufacturers to handle consumer-grade stuff, but it almost completely ignores the commercial-grade servers, network gear, and specialized equipment that your business relies on. You can learn more about its limited scope on the TCEQ website.
This leaves a big, unregulated hole for B2B e-waste. It means you simply can't rely on the manufacturer take-back programs designed for individuals when you're retiring a data center's worth of servers.
Why Documentation Is Your Best Defense
Since there aren't specific state laws dictating B2B e-waste disposal, the burden of proof is entirely on your company. This is where getting meticulous documentation from a certified partner becomes your best risk management tool. Think of it as your insurance policy against any future questions about compliance.
With no specific commercial e-waste mandate to follow, a detailed audit trail isn't just a best practice—it's your legal shield. It proves you took deliberate, professional steps to comply with data security standards and environmental rules like Austin's landfill ban.
A certified electronic recycling Austin TX partner is set up to provide the exact paperwork you need to build this defense. Here’s what that essential audit trail should always include:
- Serialized Inventory Report: A detailed manifest of every single asset collected, identified by its serial number. This is your proof of what left your building.
- Secure Chain of Custody: Paperwork that tracks your assets from the moment they leave your door to the moment they arrive at the secure processing facility.
- Certificate of Data Destruction: The legally binding document confirming that every bit of data on your hard drives and media was professionally destroyed.
- Certificate of Recycling: Your final confirmation that all the materials were processed in an environmentally sound and legally compliant way.
This collection of documents proves you did your due diligence and effectively transfers the liability from your shoulders to your recycling partner. For businesses trying to understand what a professional partnership looks like, exploring corporate e-waste solutions can offer a much clearer picture. Ultimately, getting Austin’s rules right means being proactive and insisting on certified processes and bulletproof documentation.
How Certified Data Destruction Protects Your Company

When your Austin company retires a laptop, server, or smartphone, just dragging files to the trash is a huge mistake. It’s like leaving locked filing cabinets on the curb with the keys taped to the front. The data might seem gone, but it’s often shockingly easy to recover for someone with basic tools.
This is exactly why certified data destruction is the most critical step in your entire electronics recycling process. It’s not just about deleting files; it’s a verified, permanent, and irreversible process that renders data completely unrecoverable. Think of it as a digital shredder for your most sensitive information, ensuring client records, proprietary formulas, and financial data are gone for good.
Without this crucial step, your company stays exposed to massive data breach risks, long after the equipment has left your building.
Beyond the Recycle Bin: Two Paths to Data Security
When it’s time to permanently destroy data, certified IT Asset Disposition (ITAD) partners rely on two primary, industry-approved methods. The right choice depends on the type of device, its potential for reuse, and just how sensitive the data is.
DoD-Compliant Data Wiping: Imagine digitally power-washing a hard drive until every trace of the original data is gone. Specialized software writes patterns of meaningless ones and zeros over every single sector of the drive, often multiple times. This method meets the tough Department of Defense (DoD 5220.22-M) standard and is perfect for devices that still have market value and can be refurbished. The hardware stays intact, but the data is history.
Physical Shredding: For devices at the end of their life or those containing extremely sensitive information, physical destruction is the ultimate guarantee. Industrial shredders grind hard drives, solid-state drives, and other media into tiny, unrecognizable fragments. This method is absolute. There is no coming back from it.
Choosing between them is a strategic decision. Wiping allows for asset value recovery, which can put money back into your budget. Shredding, on the other hand, provides the highest level of physical security for non-functional or high-risk assets. A professional partner in electronic recycling Austin TX will help you map out the best approach for each piece of equipment.
The Certificate of Data Destruction: Your Legal Proof
Once the data on your retired assets is destroyed, a certified recycler provides a Certificate of Data Destruction (CoDD). This isn't just a receipt—it’s a vital legal document that serves as your official record of compliance and a powerful liability shield.
Your Certificate of Data Destruction is the final, auditable proof that your organization fulfilled its duty to protect sensitive data. It formally transfers the liability for that data from your company to your certified recycling partner, closing a significant compliance loop.
This document is essential for any Austin business, especially those in regulated fields like healthcare (HIPAA), finance (SOX), or government. It contains specific details that are crucial for any audit, including:
- A unique serial number for tracking
- The specific destruction method used (e.g., DoD 5220.22-M wipe, physical shredding)
- A serialized list of the media that was sanitized or destroyed
- A legal statement confirming the data is unrecoverable
Ultimately, certified data destruction is the foundation of a secure ITAD program. It’s what elevates electronic recycling in Austin TX from a simple disposal task into a core part of your company's risk management strategy. If you need more details on how this works, you can find a wealth of information about secure data destruction services that protect businesses just like yours. Insisting on a certified process with an auditable CoDD gives you the peace of mind that your company's digital past won’t become its biggest liability.
Choosing the Right Certified Recycling Partner in Austin
Picking a vendor to handle your company's old IT equipment is a much bigger decision than just comparing prices. You're not just hiring a hauler; you're choosing a security partner. The right choice protects your business from data breaches and legal headaches, while the wrong one can expose you to massive, long-term risk. For any organization serious about electronic recycling austin tx, making a smart, risk-averse choice is absolutely critical.
This all comes down to verifying a potential partner's credentials, security protocols, and downstream processes. Without that due diligence, you have no real guarantee that your sensitive data is actually being destroyed or that your e-waste isn't ending up in a landfill—potentially with your company's asset tags still on it. A true IT Asset Disposition (ITAD) partner offers a transparent, auditable process that transfers that liability away from you.
Decoding Key Industry Certifications
When you start looking at vendors, you’ll quickly run into acronyms like R2 and e-Stewards. These aren't just fancy badges for their website; they are tough, third-party audited standards that dictate exactly how a recycler must operate. Understanding what they mean is your first line of defense.
R2 (Responsible Recycling): This is a globally recognized standard that covers the entire lifecycle of an electronic device. An R2-certified partner is regularly audited on everything from data security and environmental practices to worker safety. A key requirement is their downstream accountability—they have to track and verify where all materials go, ensuring nothing is illegally exported or dumped.
e-Stewards: Developed by the Basel Action Network, this certification is known for having the strictest standards, especially when it comes to exporting hazardous e-waste to developing nations. An e-Stewards certified facility guarantees that no toxic materials will be shipped overseas, giving you a higher level of environmental and social assurance.
Having one of these certifications means a vendor has invested a ton of money and effort into secure, accountable processes. It’s a clear signal they are a serious, professional operation, not just a scrap metal collector. You can learn more about why these standards matter by exploring what it takes to become an R2 certified electronics recycler.
Your Vetting Checklist: Essential Questions to Ask
Once you’ve confirmed a potential partner has the right certifications, it's time to dig a little deeper. How they answer specific questions about their operations will reveal their true capabilities and their commitment to security. Don't be afraid to ask for specifics—a professional partner will welcome the scrutiny.
Here are the critical questions every Austin business should be asking:
Can You Detail Your Chain-of-Custody Process? A secure chain of custody is non-negotiable. Ask them to walk you through their entire process, from locked transport and GPS-tracked vehicles to facilities with controlled access and video surveillance.
What Documentation Will We Receive? A verbal promise is worthless in an audit. Insist on seeing samples of their key documents: a serialized inventory report, a Certificate of Data Destruction, and a final Certificate of Recycling. This is your legal paper trail.
How Do You Audit Your Downstream Partners? No single recycler processes every material in-house. Ask how they vet and audit the partners who handle the final processing of materials like glass, plastics, and precious metals. This ensures your environmental liability is covered all the way to the end of the line.
The process of finding the right partner involves several distinct steps, moving from high-level certifications to detailed security and audit procedures.
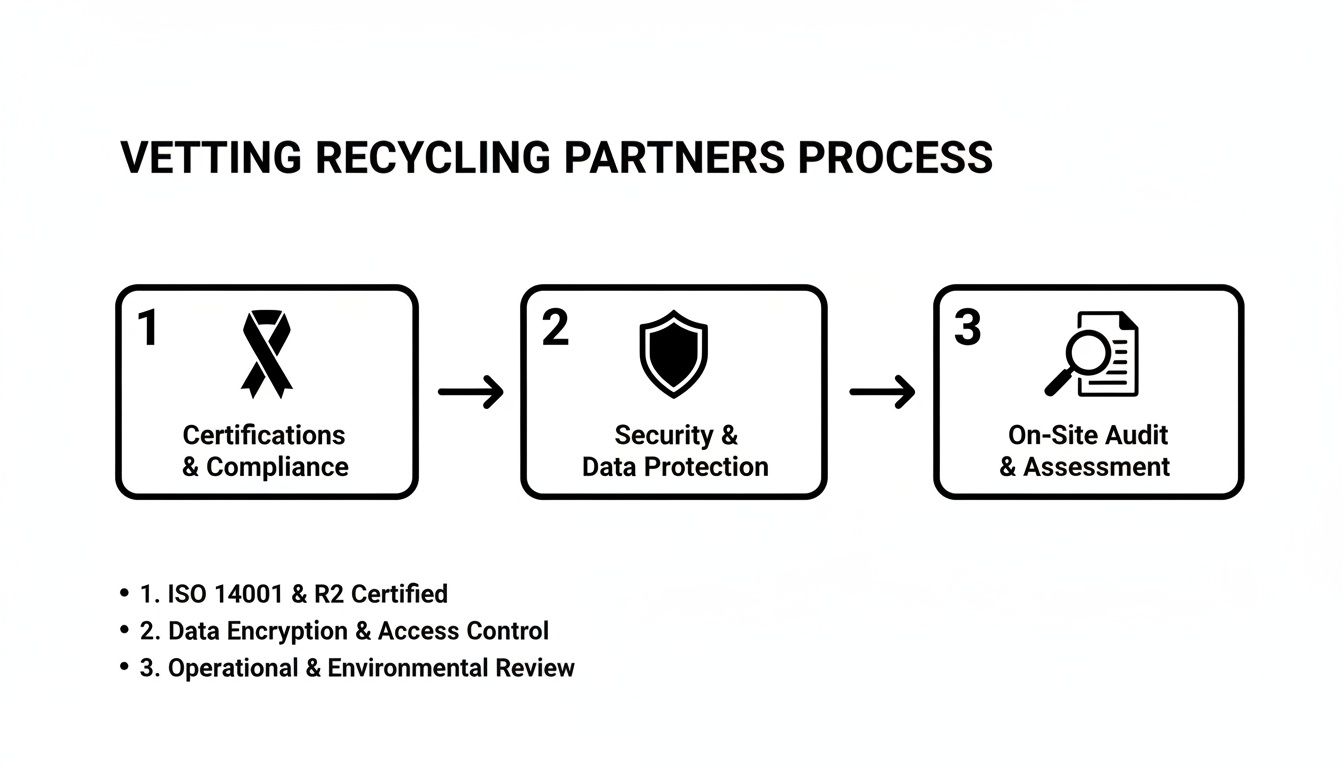
This highlights that a solid selection process is a multi-stage effort, not a single decision, ensuring you're covered at every step.
The difference between a basic recycler and a certified ITAD partner becomes clear when you start asking these detailed questions. A standard recycler might just focus on disposal, while a true partner manages your risk.
Vendor Vetting Checklist Key Comparison Points
| Evaluation Criteria | Standard Recycler | Certified ITAD Partner |
|---|---|---|
| Certifications | May have basic local permits, if any. | Holds R2v3 and/or e-Stewards certifications. |
| Data Destruction | Offers basic hard drive shredding, often unverified. | Provides NIST 800-88 compliant data destruction with auditable reports. |
| Chain of Custody | Loose or non-existent tracking. | Documented, secure process from pickup to final disposition. |
| Reporting | Provides a simple weight ticket or invoice. | Delivers serialized asset reports and Certificates of Destruction/Recycling. |
| Downstream Vetting | Little to no transparency on where materials end up. | Conducts rigorous audits of all downstream partners. |
| Liability | Liability and risk often remain with your business. | Assumes liability through a transparent, documented process. |
Ultimately, the checklist shows that a certified ITAD partner is built around protecting your organization, while a standard recycler is focused on processing material.
The best partner is one who can clearly show you how their process mitigates your risk. Their certifications, security protocols, and transparent documentation all work together to provide the peace of mind you need when dealing with your company's retired assets.
The Commercial E-Waste Recycling Process from Start to Finish

So, you've scheduled a pickup for your retired IT assets. What happens after the truck pulls away? For many Austin businesses, it's a "hope for the best" moment, but a truly certified process is far more transparent and secure than you might think. This isn't just a hauling job; it's a documented, armored-car-style service for your digital assets.
The entire workflow hinges on a secure chain of custody. This is simply a documented trail that tracks your equipment from the second it leaves your control to its final recycling or destruction. For any data center operator or IT manager, knowing this process inside and out is the key to proving every device was handled correctly and every bit of data was destroyed for good.
Step 1: On-Site Inventory and Secure Packing
The process kicks off right at your facility. A professional ITAD team doesn’t just show up and start grabbing gear. First, they perform a meticulous on-site inventory, scanning the serial number of every single piece of equipment you're getting rid of. This initial manifest is the bedrock of your entire audit trail.
Next, the crew securely packs everything into locked, sealed containers or onto wrapped pallets. This is a deliberate process designed to prevent any tampering or loss while the equipment is on its way. For high-security projects, every container is cataloged and sealed before it even leaves your building.
Step 2: Secure Logistics and Transport
With all your assets inventoried and packed, they're loaded onto a secure, GPS-tracked vehicle. This step is a critical link in the chain of custody. Being able to see the truck's location in real-time adds a serious layer of security and accountability, assuring you that your equipment is on a direct, monitored path to the certified facility.
This level of logistical control is what separates professional electronic recycling Austin TX services from the rest. It closes the door on the risk of assets "going missing" on the road, which is a legitimate worry with unvetted haulers.
Step 3: Secure Facility Reception and Auditing
Once the truck arrives at the secure recycling facility, the container seals are broken in a controlled area, often under video surveillance. The team immediately performs a second audit, checking the received assets against the original inventory list created at your site. Every serial number has to match.
This receiving audit isn't optional; it's a mandatory step in a compliant ITAD process. It confirms that everything that left your building arrived securely, officially closing the transportation loop and transferring custody to your recycling partner.
Step 4: Sorting, Data Destruction, and Recycling
Inside the facility, the real work begins. Assets are sorted, and any data-bearing devices like hard drives, servers, or backup tapes are immediately segregated. They're moved to a secure cage for certified data destruction, which could mean DoD-compliant wiping or complete physical shredding, depending on your needs. You can dig deeper into how these methods work in our guide on shredding and recycling services.
In a city like Austin, which banned electronics from its landfill back in 2009, this final step is especially important. The EPA reports that a shocking 82% of e-waste in the U.S. ends up in the wrong place, like landfills or incinerators. By working with a certified recycler, you're directly helping to combat that problem and align with local goals.
The remaining non-data components are then disassembled. Valuable commodities like metals, plastics, and glass are recovered and sent to audited downstream partners to be turned back into raw materials.
Turning Old Tech into New Value for Your Business
Most businesses see managing old tech as just another cost on the balance sheet. But in Austin, smart companies are flipping that script. A strategic IT Asset Disposition (ITAD) program isn't just about responsible disposal; it's about turning your retired hardware into a real source of revenue.
This approach stops you from thinking about old equipment as worthless junk. A certified partner can help you unlock the hidden value in those assets. You'd be surprised how much your used enterprise-grade servers, laptops, and networking gear are still worth on the secondary market. Tapping into that value directly boosts your bottom line.
Embracing the Reuse Hierarchy
The simplest, most effective way to get that value back is to follow the reuse hierarchy. It’s a straightforward principle: prioritize finding a new home for functional equipment before breaking it down for scrap.
Think of it like selling a well-maintained used car. You’ll almost always get more money selling the car to a new driver than you would by sending it straight to the scrapyard for its value in raw metal. The same logic applies to your IT assets. Refurbishing and reselling a pallet of three-year-old business laptops will generate far more cash than recycling them for their base materials. This isn’t just better for your finances—it’s a huge win for the environment, too.
By focusing on reuse first, your business can actively participate in Austin's circular economy. This strategy turns a potential expense into a new revenue stream and enhances your brand’s reputation as an environmentally conscious organization.
How Asset Value Recovery Works
This whole process is managed through a formal asset value recovery (AVR) program. Your ITAD partner will first audit your retired inventory, identifying any devices that still have resale potential.
From there, they securely wipe all your data, test the hardware, and refurbish whatever is needed to get it ready for sale. Once sold, you get a share of the profits. That financial return can be surprisingly significant, often offsetting—or even completely covering—the costs of your entire ITAD project. You can explore the various benefits of e-waste recycling to see how this fits into the bigger picture.
Globally, the e-waste problem is massive, projected to hit 53.6 million metric tons by 2026, with a dismal 17.4% being properly recycled. While Texas doesn’t have a statewide landfill ban for electronics, Austin’s local policies and state environmental rules mean businesses here can’t just toss their old tech. This proactive stance has helped create a powerful local reuse market. Finding the right electronic recycling Austin TX partner lets your business turn old equipment from a liability into a tangible financial asset.
Common Questions About Business E-Waste in Austin
As Austin businesses move toward a professional IT asset disposition (ITAD) strategy, plenty of questions come up. Getting straightforward answers is the key to making smart, compliant decisions for your company. Here are some of the most common questions we hear from organizations just like yours.
What Types of Electronics Can My Business Recycle?
A certified partner specializing in electronic recycling for Austin, TX businesses can handle just about any piece of commercial equipment you have. This goes way beyond standard office desktops, servers, and monitors. They are fully equipped to manage specialized hardware from data centers, diagnostic machines from medical facilities, and sensitive lab equipment.
Unlike consumer drop-off sites that often have strict limits, a commercial vendor is built to handle the sheer volume and complexity of the equipment that keeps your entire operation running. This gives you a single, secure solution for your whole inventory.
Is Our Company Data Truly Secure During Recycling?
Yes—but only if you partner with a certified recycler who provides a documented, secure chain of custody. Real data security isn't just a promise; it's a process you can verify from start to finish.
Reputable vendors use DoD-compliant data destruction methods, like multi-pass data wiping or physical shredding. They then issue a Certificate of Data Destruction, a legal document that proves your data was permanently destroyed and officially transfers liability away from your company.
This certificate is your definitive proof of due diligence and data security.
What Documents Should We Get From Our Partner?
A professional ITAD partner will provide a complete, auditable paper trail. This documentation is your defense in any compliance audit and proves you managed your retired assets responsibly. You should always receive:
- A Detailed Asset Inventory: A serialized list of every single item that was collected.
- Certificate of Data Destruction: The legal proof that data on all media was destroyed beyond recovery.
- Certificate of Recycling: Final confirmation that all materials were processed in an environmentally sound way.
Can We Get Money Back for Our Old Equipment?
Absolutely. This happens through a process called asset value recovery, where your partner refurbishes and resells retired IT assets that still have market value. It's a common and effective way to generate a financial return from your old gear.
This revenue can significantly offset—or even completely cover—the costs of your entire disposition project. It can turn what would have been an expense into a net positive for your budget.
Ready to implement a secure, compliant, and profitable IT asset disposition strategy? Dallas Fortworth Computer Recycling offers nationwide services with the expertise to protect your business. Learn more at https://dallasfortworthcomputerrecycling.com.
