How to Find the Right Local Computer Recycling Center
Picking a local computer recycling center isn't just about clearing out old equipment—it's a critical decision that directly impacts your data security, regulatory compliance, and company reputation. For an IT director, this is less about disposal and more about choosing a strategic IT Asset Disposition (ITAD) partner.
The right partner protects your organization from very real risks. The wrong one can be a disaster waiting to happen.
Why Your Choice of Recycling Partner Matters
Choosing the right ITAD vendor turns what feels like a logistical headache into a strategic win. It’s the difference between just getting rid of old gear and executing a secure, compliant, and environmentally sound end-of-life process for your technology.
A poor choice can expose your company to crippling data breaches, massive regulatory fines, and permanent damage to your brand. A properly vetted partner, on the other hand, delivers complete peace of mind with documented proof that every asset was handled responsibly.

The Stakes of Improper Disposal
The consequences of working with an uncertified or careless vendor are severe. Imagine a stack of your company's old laptops showing up on a secondary market, still loaded with sensitive client data. That kind of data breach can easily lead to millions in fines under regulations like GDPR or HIPAA, not to mention the irreparable harm to customer trust.
This isn't just a hypothetical. The sheer volume of electronic waste makes this a global problem. In 2022, the world generated a staggering 62 million tonnes of e-waste, an 82% jump since 2010. Even more shocking, only 22.3% of it was properly collected and recycled. That massive gap highlights just how important it is to pick a partner who is part of the solution, not the problem.
The Pillars of a Trustworthy ITAD Partner
A reliable local computer recycling center stands on three essential pillars. These are the non-negotiables you have to verify before handing over a single piece of equipment.
- Unwavering Security: This means certified data destruction methods that meet NIST 800-88 standards, a secure chain-of-custody process, and facilities with controlled access.
- Certified Compliance: Your partner must hold key industry certifications like R2 or e-Stewards, which prove they follow the highest environmental and safety standards.
- Genuine Sustainability: A true partner focuses on refurbishment and reuse first to extend the life of your assets. Only then do they move to responsible materials recovery, and they should be able to provide transparent reports on their environmental impact.
The goal is to find a partner who doesn't just take your old equipment but gives you a fully auditable trail. You need proof that every single asset was handled securely and responsibly from the moment it left your building.
This kind of partnership doesn't just protect your data; it strengthens your company's commitment to corporate social responsibility. When you understand the core benefits of e-waste recycling, your team can better justify a professional ITAD program to stakeholders. The right vendor helps you avoid risks and turns a necessary expense into a powerful statement of your company's values.
Your Vetting Checklist for E-Waste Partners
You need to know the difference between a professional IT Asset Disposition (ITAD) partner and a simple scrap hauler. Anyone can pick up old computers, but only a certified expert can shield your business from the very real data, environmental, and financial fallout of doing it wrong. This checklist will help you ask the right questions and demand the right proof.
Don’t just take a vendor’s website at face value. A professional local computer recycling center will welcome your questions and have the documentation to back up every claim. This is more than just a routine task—it’s a critical risk management decision.
Demystifying Key Industry Certifications
The world of e-waste is messy, and the stakes are high. Globally, the electronic waste recycling rate was a dismal 22.3% in 2022. It’s projected to get worse, potentially dropping to 20% by 2030 as we create new devices nearly five times faster than we collect the old ones. This massive gap is exactly why certifications are not negotiable.
Two certifications are the gold standard in the ITAD industry. Don't settle for less.
- R2 (Responsible Recycling): The R2 standard is all about accountability. It sets tough requirements for environmental protection, worker safety, data security, and tracking materials all the way through the recycling chain. An R2-certified facility has passed independent audits to prove they prioritize reuse and refurbishment before recycling.
- e-Stewards: Often seen as the strictest standard out there, e-Stewards was developed by the Basel Action Network. It completely prohibits exporting hazardous e-waste to developing nations and puts a heavy emphasis on data security and social responsibility.
When a vendor says they're certified, ask for a copy of their current certificate. Then, go online and verify it yourself on the official R2 or e-Stewards directories. This one simple step will weed out anyone making false claims. You can also learn more about what it means to be an R2-certified electronics recycler and see how it protects your company.
Conducting a Thorough On-Site Facility Audit
A facility tour is the most revealing part of your vetting process. What you see—or don't see—tells you everything about a vendor’s professionalism and security. If a potential partner is hesitant to let you visit, that’s a huge red flag.
During your audit, keep an eye on these key areas:
- Secure Receiving and Storage: Is there a specific, access-controlled area where your assets are dropped off and stored? Look for security cameras, locked cages, and a clear separation from other, less secure parts of the facility.
- Organized Processing Lines: A well-run plant has a logical flow. You should see a clear path from initial triage and data destruction to component testing and material baling. Chaos is a sign of poor process control.
- Data Destruction Zone: This needs to be the most secure spot in the building. Is it physically isolated? Is access restricted? Ask them to show you their wiping, degaussing, or shredding equipment in action.
- Downstream Material Organization: Look at how they sort and store materials (plastics, metals, circuit boards) heading to their own downstream partners. This shows you how carefully they manage every part of the recycling stream.
A professional ITAD facility should feel more like a secure data center than a scrapyard. The level of organization, security, and process discipline you witness directly reflects the level of care your assets will receive.
Verifying Insurance and Downstream Vendor Networks
Your due diligence doesn't stop at the recycler's front door. Your liability extends all the way to the final disposition of your equipment, so you need to check their coverage and their partners.
Ask to see their Certificate of Insurance. You need to verify they have adequate coverage, specifically looking for Data Breach/Cyber Liability and Pollution Liability policies. A standard general liability policy isn't enough to cover the unique risks of handling IT assets.
Just as important is their downstream vendor network. No single facility processes every single material in-house. Ask for a list of their primary downstream partners and find out how they vet them. A reputable ITAD provider will have a formal audit program to ensure their partners also meet strict environmental and security standards. This is your best defense against finding out your equipment ended up in an overseas landfill.
Verifying Data Destruction and Ensuring Compliance
Let’s be honest. For any IT leader, data security is the single most critical part of this entire process. A single hard drive slipping through the cracks can unleash a nightmare of financial and reputational damage.
That’s why you have to demand absolute, verifiable proof of data destruction from any local computer recycling center you’re considering. Taking a vendor’s word for it isn’t just risky—it’s negligent. You need audit-proof documentation. Period.
This all starts with understanding the tools of the trade. Not all data destruction methods are the same, and picking the right one is crucial for both security and compliance.
Choosing the Right Data Destruction Method
The gold standard for media sanitization is the National Institute of Standards and Technology (NIST) Special Publication 800-88. Any professional ITAD partner worth their salt builds their entire data destruction program around these guidelines. Knowing the basics helps you ask the right questions.
Your recycling partner will typically use one of three core methods:
- Data Wiping (NIST Clear/Purge): This is a software-based approach that overwrites every single sector of a hard drive with random data, making the original information impossible to get back with standard software. The "Purge" level is even stronger, designed to thwart laboratory-level recovery attempts. Wiping is perfect for newer, working hard drives that you want to refurbish and resell, since it preserves their value.
- Degaussing (NIST Purge): This method uses an incredibly powerful magnetic field to scramble the magnetic domains on traditional spinning hard drives (HDDs), where all the data lives. It instantly bricks the drive and makes the data completely unrecoverable. It's fast and highly effective, but keep in mind—it does nothing for Solid-State Drives (SSDs), which store data electronically.
- Physical Shredding (NIST Destroy): This is the end of the line. The hard drive is fed into a shredder and pulverized into tiny, mangled pieces of metal and plastic. There’s no coming back from this. Shredding is the only choice for failed drives, SSDs, or any device that held extremely sensitive data where you can’t afford to take any chances.
This decision tree visualizes the key checkpoints—certifications, facility audits, and data security protocols—that form the foundation of a reliable vetting process.
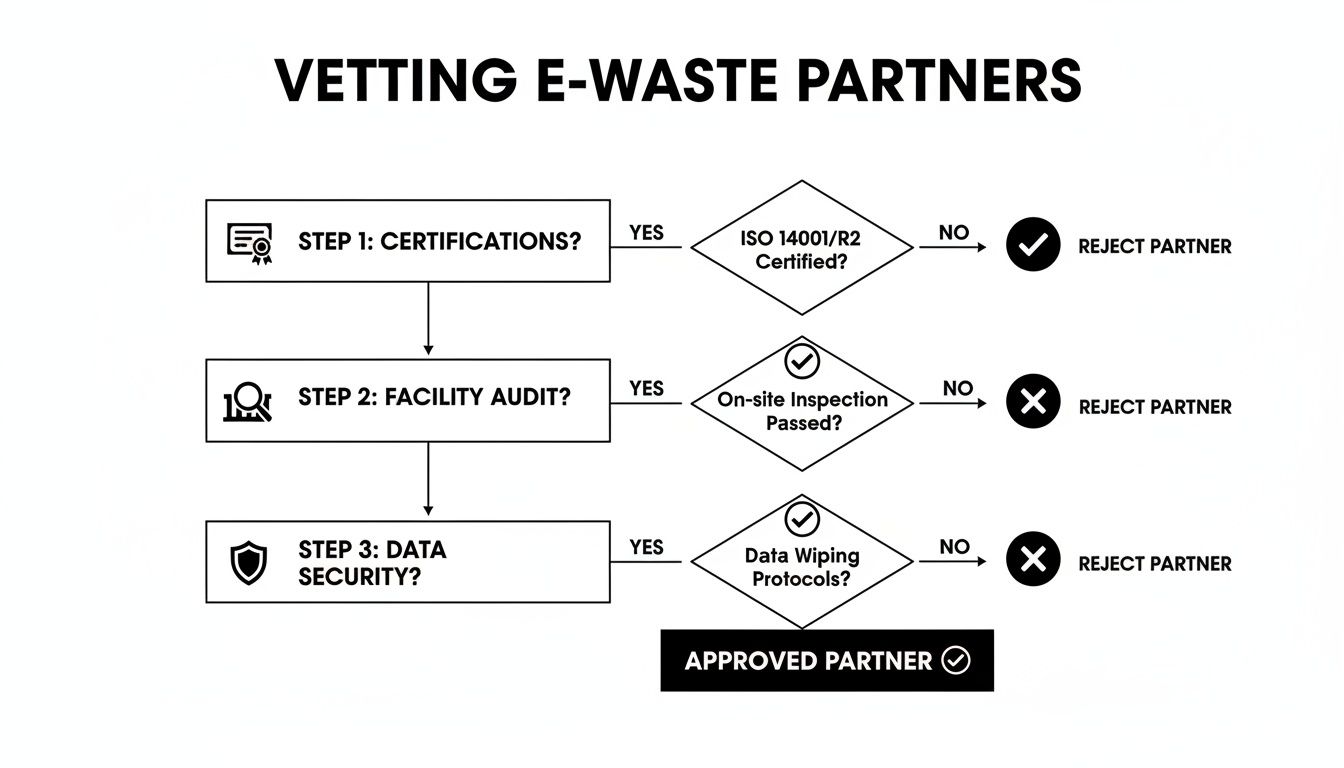
This kind of structured approach ensures you only work with partners who can back up their security claims with verifiable proof every step of the way.
To help you decide which method is right for your assets, here's a quick comparison of the common techniques and how they align with NIST 800-88.
Data Destruction Methods and Compliance Standards
| Destruction Method | Description | Best For | NIST 800-88 Level | Verification |
|---|---|---|---|---|
| Software Wiping | Overwrites drive sectors with random data using certified software. | Functional HDDs and SSDs intended for reuse or resale. | Clear / Purge | Software-generated wipe report with drive serial numbers. |
| Degaussing | Exposes HDDs to a powerful magnetic field, erasing data. | End-of-life HDDs containing sensitive data. Not effective for SSDs. | Purge | Visual confirmation; the drive is rendered inoperable. |
| Physical Shredding | Mechanically pulverizes drives into small fragments. | Failed drives, SSDs, and any media with highly sensitive data. | Destroy | Visual confirmation; serialized log of shredded assets. |
Choosing the appropriate method based on the data's sensitivity and the asset's lifecycle is key to a cost-effective and secure disposition strategy.
The Non-Negotiable Documentation
Here’s a hard truth: the proof of destruction is just as important as the destruction itself. Without a complete, auditable paper trail, you have no defense if an auditor comes knocking or a security incident occurs. Your ITAD partner must provide specific, detailed documents for every single job.
The Certificate of Data Destruction (CoDD) is the cornerstone of this entire process. And a real CoDD is much more than a simple "we did it" letter. It has to include:
- A unique serial number for the certificate itself.
- Your company's name and the date of service.
- A detailed, itemized list of asset serial numbers for every single hard drive that was sanitized or destroyed.
- The specific destruction method used for each asset (e.g., NIST 800-88 Purge, Shred).
- A signature from an authorized person at the recycling company.
Insist on a serialized, asset-level report. A vague certificate that just says "100 hard drives were destroyed" is completely worthless for compliance. You need a one-to-one match between the assets you handed over and the assets they confirm were destroyed.
This paperwork is your legal shield. It proves you did your due diligence to protect sensitive information and is essential for meeting regulatory demands. To get a better sense of what this should entail, you can see how a professional process for secure data destruction services is structured.
Maintaining Regulatory Compliance
If you're in a regulated industry, the stakes are even higher. Compliance with standards like HIPAA (healthcare), GDPR (data privacy), and FACTA (financial) isn't optional, and the penalties for messing up are severe. A certified ITAD partner is your best ally for navigating these rules.
Think about it: a hospital system getting rid of old workstations must ensure all patient health information (PHI) is destroyed in a HIPAA-compliant way. Their recycling partner needs to provide a CoDD that ties the serial numbers of the destroyed hard drives directly back to the hospital’s original asset tags. That creates an unbroken chain of custody that will satisfy any HIPAA audit.
Likewise, a bank has to comply with FACTA, which mandates the proper disposal of consumer financial data. By using a certified partner who provides NIST-compliant destruction and rock-solid documentation, the bank can prove it protected its customers from potential identity theft.
At the end of the day, your local computer recycling center shouldn't just be a disposal vendor—they should be your compliance partner.
Navigating ITAD Logistics and Costs
Choosing a local computer recycling center often boils down to the brass tacks: logistics and cost. How do you get a pile of retired equipment from your server room to their facility without security gaps or surprise fees? This is where a well-thought-out plan becomes absolutely essential.
It all starts with knowing what you have. Before you can even get a ballpark quote, you need a detailed inventory of every desktop, laptop, server, monitor, and keyboard you plan to decommission. That initial count is the foundation for everything that follows.

Planning for a Secure Pickup
Once you have your inventory list, the real work begins. You can't just stack old computers in a vacant office and expect a smooth pickup. A professional ITAD partner will have specific packing requirements to protect the equipment and make the collection process safe and efficient.
For instance, they’ll likely ask you to palletize and shrink-wrap the gear. This isn't just about making it tidy; it protects the assets from damage and makes loading faster. Be sure to ask any potential vendor for their specific preparation guidelines.
- Palletizing: Securely stack desktops, servers, and other hardware on standard pallets.
- Shrink-wrapping: Tightly wrap the loaded pallet in industrial-grade shrink-wrap to keep everything stable and secure.
- Labeling: Apply a unique label to each pallet that matches up with your inventory list.
Unpacking Different Cost Structures
The price tag for IT asset disposition can be tricky. Reputable vendors are typically transparent, but you need to understand the different pricing models to avoid hidden fees and forecast your total project cost accurately.
A few common structures you'll see include:
- Per-Pound Pricing: Often used for bulk recycling. You're charged a simple rate for the total weight (e.g., $0.50 per pound). It's straightforward but doesn't account for the potential value of newer assets.
- Flat-Fee Pickup: Some partners charge a single fee that covers transportation, data destruction, and recycling for a set amount of equipment.
- Itemized Services: This model breaks down every cost, charging separately for hard drive destruction, transportation, and special handling for items like old CRT monitors.
The smartest play often involves value recovery. If you have newer, functional equipment, a good partner can refurbish and resell it. This can generate rebates or revenue-sharing that can dramatically reduce—or even completely cover—your disposal costs.
The sheer scale of the e-waste market puts these costs in perspective. The global electronic waste recycling market was valued at USD 70.1 billion in 2024 and is projected to hit an incredible USD 251.9 billion by 2034. This explosive growth is driven by the value of recoverable materials and the non-negotiable need for secure disposal services.
Maintaining an Unbroken Chain of Custody
If there's one thing you can't compromise on, it's the chain of custody. This is the documented, auditable paper trail that follows every single asset from the moment it leaves your building to its final destination. It’s your proof that nothing was lost, stolen, or mishandled.
A professional ITAD provider starts the chain of custody before the truck even pulls away from your loading dock. Their team should scan and log the serial number of every device they collect, and you should get a copy of that pickup report on the spot.
This obsessive tracking has to continue at their facility. Every step—from data destruction to final recycling or resale—must be logged and tied back to that asset's unique serial number. In the event of a compliance audit, this documentation is your ironclad defense. For a deeper look, check out our guide on professional IT asset disposition services.
Building a Long-Term ITAD Partnership
Finding the right IT Asset Disposition (ITAD) partner isn’t a one-and-done project. It’s the beginning of an ongoing relationship. The best ITAD programs are built on a solid foundation where your vendor stops being just a service provider and becomes a genuine strategic advisor. This shift can turn your end-of-life process from a necessary expense into a source of real value and rock-solid compliance.
A true partnership goes way beyond just scheduling pickups. It’s about regular communication, having shared goals, and a mutual dedication to making your security and sustainability efforts better over time. That ongoing dialogue is what separates a transactional vendor from a partner who's truly invested in your success.
From Disposal Costs to Revenue Generation
One of the biggest wins from a strong partnership is the ability to unlock the hidden cash in your retired assets. A reactive approach usually means all old equipment gets lumped together for recycling. A proactive, collaborative strategy, on the other hand, actively hunts for opportunities.
Your ITAD partner should be working with your team to pinpoint devices that are good candidates for refurbishment and resale. This takes trust and complete transparency. They can give you real market insights on which models of laptops, servers, or networking gear are hot right now. By separating these higher-value assets, you can create a revenue stream that helps offset—and sometimes even wipes out—your disposal costs.
For instance, a good partner might tell you that your three-year-old enterprise laptops are still holding 40% of their original value on the secondary market. By setting up a process to have them securely wiped (not shredded) and resold, you turn a disposal expense into a budget-positive outcome. This only works with a partner you can trust to handle the process ethically and give you a clear, itemized settlement report.
Think of your ITAD partner as an extension of your asset management team. Their expertise shouldn't just kick in at the end-of-life stage, but help you maximize the financial lifecycle of your entire hardware fleet.
Comprehensive Reporting for Audits and ESG Initiatives
In today’s business world, proving you’re compliant and environmentally responsible isn’t optional. A long-term partner gets this and provides reporting that’s much more than a simple Certificate of Destruction. They should deliver detailed data that serves two vital functions: satisfying internal audits and strengthening your Environmental, Social, and Governance (ESG) reports.
For audits, you need serialized asset reports that create a clear, unbroken chain of custody. This documentation is your proof that you did your due diligence. For ESG, your partner can give you metrics that add real weight to your sustainability claims.
Key reports a long-term partner should provide:
- Asset Disposition Summary: A high-level look at the total number of assets processed, how many were resold, and how many were recycled.
- Environmental Impact Report: This report translates your recycling work into tangible numbers, like pounds of e-waste diverted from landfills, estimated CO₂ emissions avoided, and the amount of precious materials recovered.
- Value Recovery Statement: A financial breakdown showing the gross revenue from resold assets, any fees for refurbishment, and your net profit or credit.
This level of detailed reporting makes it easy to show stakeholders the positive impact of your ITAD program. It gives you the hard data you need for annual reports and proves your company is serious about responsible operations.
Conducting Quarterly Business Reviews
A partnership lives and breathes on communication. A quarterly business review (QBR) is the perfect setting to make sure your local computer recycling center is still meeting your changing needs and that you're getting the most value out of the relationship. This isn't just a casual check-in; it's a strategic meeting to go over performance and plan for what's next.
These reviews should be data-driven and forward-looking. Use this time to talk about recent projects, check performance against your Service Level Agreements (SLAs), and tackle any challenges that have come up. It's also a great time to discuss upcoming hardware refreshes or data center projects so your partner can get ready logistically. To get a better feel for what a professional partner can offer, it's worth exploring the differences between various IT asset disposition companies and their service models.
Here are a few essential questions to bring to your QBR:
- Can you walk us through a performance scorecard for last quarter, including pickup times, reporting accuracy, and settlement report turnaround?
- Based on our recent projects, do you see any ways we could improve our internal process to make pickups even smoother?
- What trends are you seeing in the secondary market for the types of assets we’re retiring? Should we be thinking about adjusting our strategy?
- Have there been any changes to your certifications, insurance, or downstream vendor network we need to know about?
- Are there any new services or technologies you've brought on that could help us, like better on-site services or reporting tools?
Treating your ITAD provider like a long-term partner creates a powerful feedback loop. It ensures they stay aligned with your business goals and consistently deliver the security, compliance, and value your organization needs.
Answering Your Computer Recycling Questions
Even with a solid plan, you're going to have questions when evaluating a local computer recycling center. Getting straight answers isn't just a formality—it's how you make a confident, compliant decision for your business.
Let's cut through the noise and tackle the most common concerns we hear from IT directors and procurement teams during the vetting process. This is about understanding the real-world differences that separate an adequate vendor from a true partner.
What Is the Difference Between R2 and e-Stewards Certification?
Think of R2 (Responsible Recycling) and e-Stewards as the two leading standards in our industry. Both aim for responsible electronics handling, but they get there with slightly different philosophies.
The e-Stewards standard is famously strict. It enforces a complete, non-negotiable ban on exporting hazardous e-waste to developing nations. If your company has a zero-export mandate for corporate social responsibility, this is often the go-to certification.
The R2 standard also champions responsible management but does allow for the legal export of tested, working equipment under very specific, controlled conditions. It's important to know that many top-tier R2-certified recyclers voluntarily adopt a strict no-export policy anyway.
Here’s the pro tip: move beyond just the certificate. Ask any potential partner—regardless of their certification—to show you their downstream vendor map and provide a written policy on material exportation. This is the only way to ensure their actual practices align with your company's risk tolerance and ESG goals.
Ultimately, the best certification is the one held by a partner who gives you transparent, verifiable proof of their entire process, from start to finish.
How Much Does It Cost to Recycle Computer Equipment?
This is the big question, and the honest answer is: it depends. The final cost swings based on what kind of equipment you have, how much of it there is, your location, and the specific services you need, like on-site data destruction.
You'll typically see a few common pricing models:
- Per-Pound Fees: This is common for mixed electronics, often running from $0.25 to $0.75 per pound. Keep in mind that older, hazardous items like CRT monitors will always cost more to handle.
- Flat-Rate Pickups: Some vendors simplify budgeting by offering a single price for a truckload or a set number of pallets.
- Itemized Service Charges: This model breaks everything down, giving you a detailed quote for transport, data destruction per drive, and recycling fees for specific types of assets.
But the smartest approach is to focus on value recovery. If you have newer assets—like recent-generation servers, laptops, or networking gear—they can often be refurbished and resold. A great partner will offer a revenue-sharing agreement that can seriously reduce, or even completely cover, your recycling costs. Always insist on a quote that separates the recycling fees from the potential resale value.
What Documentation Should I Expect from a Recycling Partner?
Audit-proof paperwork is the hallmark of a professional. If a vendor can't produce it, that's your cue to walk away. After every single project, your partnership should generate three non-negotiable documents.
- A Serialized Chain of Custody Record: This document is your unbroken accountability trail, tracking every asset from the moment it leaves your building to its final disposition.
- A Certificate of Data Destruction (CoDD): This is your proof of compliance. It must confirm the sanitization method used (e.g., NIST 800-88 Purge) and, crucially, list the individual serial numbers of the destroyed hard drives.
- A Certificate of Recycling: This document confirms that all non-reusable materials were processed according to all local, state, and federal environmental laws.
If any of your assets were resold, you also need to receive a detailed settlement report. This report should clearly break down the resale value for each item and calculate your agreed-upon revenue share. Vague, summary-level reports are a massive red flag.
Can a Local Recycler Handle Our Nationwide ITAD Needs?
Absolutely. Many established local computer recyclers have spent years building robust national logistics networks to serve enterprise clients with offices scattered across the country. They do this through a smart mix of their own truck fleets and strategic partnerships with other vetted, certified logistics providers.
When you're evaluating a partner for national service, dig into the details. Ask them how they manage multi-site projects. How do they guarantee the same security protocols and service standards at every location? Can they provide consolidated, centralized reporting and invoicing? For any large organization, having a single point of contact and accountability for your entire ITAD program is a game-changer.
At Dallas Fortworth Computer Recycling, we provide secure, compliant, and fully documented IT asset disposition services for businesses nationwide. Our process is built on transparency and trust, ensuring you have the verifiable proof you need to protect your data and meet your sustainability goals. Learn more about our B2B services at https://dallasfortworthcomputerrecycling.com.
