Where to Sell Computer Parts: Secure, Profitable ITAD Guide
Before you even think about where to sell old computer parts, you need to know exactly what you have. The first and most critical step is a detailed internal audit of your IT assets. This isn't just about counting old laptops; it's a strategic valuation that gives you the data needed to get the best possible return.
A thorough inventory is the bedrock of a successful and compliant disposition project.
The First Step Before You Sell Any Computer Parts
Trying to find a buyer without a clear picture of what you have is like selling a car without knowing its make, model, or mileage. You’ll absolutely leave money on the table and open your organization up to unnecessary risks. A meticulous internal audit transforms a pile of retired hardware into a catalog of valuable, sellable assets.
This process goes way beyond a simple device count. It means creating a detailed spreadsheet that captures the specific, value-driving components inside each machine. For IT managers and procurement teams, this data is non-negotiable for making smart decisions.
Creating a High-Value Asset Inventory
Your inventory needs to be granular. Instead of just listing "50 Dell Laptops," you need entries that detail the specific components that actually determine resale value. A detailed inventory directly impacts your negotiating power and helps you accurately forecast your potential return.
To get started, you'll want to build a simple but comprehensive inventory list. Here’s a look at the essential data points to collect for every single asset.
Essential Data for Your IT Asset Inventory
A checklist of key data points to collect for each asset, ensuring anaccurate valuation and a smooth, compliant disposition process.
| Data Point | Why It's Critical | Example |
|---|---|---|
| Asset Type & Model | Clearly identifies the product family and generation, which is the starting point for valuation. | Dell Latitude 7420 |
| CPU (Processor) | This is a primary value driver. Newer generations and higher-end models are worth significantly more. | Intel Core i7-1185G7 |
| RAM (Memory) | Documents the total capacity and type. RAM is often in high demand and can be a key resale component. | 16GB DDR4 |
| Storage | Specifies the type, capacity, and technology. Fast SSDs are much more valuable than older HDDs. | 512GB NVMe SSD |
| Overall Condition | A simple cosmetic grade (e.g., A, B, C) sets realistic expectations and prevents disputes with buyers. | Grade B (minor scratches) |
| Functional Status | Confirms if the device powers on and works as expected. This separates valuable assets from e-waste. | Powers on, all ports tested |
This level of detail is what allows you to move from having "old computers" to possessing a portfolio of assets with distinct market values. That clarity is essential for every single step that follows.
Why This Audit Is a Game Changer
Putting in the effort up front pays off big time throughout the sales process. It allows you to sort your equipment into logical buckets: high-value items for resale, lower-value parts for a bulk sale, and obsolete electronics for certified recycling.
This kind of segmentation is a core component of effective IT asset management best practices, as it helps you match each asset category with the right disposition channel.
With a comprehensive inventory in hand, you can approach potential buyers—whether they are ITAD partners, wholesalers, or direct marketplaces—with precise information. This professional approach not only builds credibility but also ensures you receive fair market value, turning your IT refresh cycle into a predictable value recovery opportunity instead of just another disposal cost.
Choosing Your Sales Channel: From Marketplaces to ITAD Partners
With a detailed inventory in hand, you're no longer dealing with a closet full of mystery hardware. You now have a portfolio of tangible assets. The next crucial step is figuring out the smartest way to sell them. Deciding where to sell your old computer parts is a balancing act—you want to maximize your financial return without creating a logistical nightmare or, worse, a massive security risk.
For any business, the options really boil down to a few main channels. Each comes with its own set of trade-offs in terms of effort, return, and risk. It's critical to look at these choices through the lens of corporate responsibility, not just as a one-off sale to make a quick buck.
The Direct Resale Dilemma: Online Marketplaces
Platforms like eBay or Amazon Marketplace dangle the promise of the highest possible price for each individual component. Selling a high-end GPU or a batch of recent-gen RAM directly to an end-user will almost always bring in more money per unit than selling to a wholesaler. But that higher return comes at a steep price in operational headaches and security vulnerabilities that most businesses simply can't afford to take on.
Just think about the internal resources you'd need to pull this off:
- Serious Time Commitment: Every single item needs to be photographed, listed with detailed specs, and priced based on a constantly changing market.
- Customer Service Drain: Your IT team would suddenly become a support desk, answering endless buyer questions, managing shipping, and handling returns or disputes for dozens, if not hundreds, of separate transactions.
- The Data Security Minefield: This is the big one. Selling a device on a public marketplace without certified, auditable data destruction is a massive liability. A simple factory reset is nowhere near enough to stop someone from recovering sensitive company data.
An individual selling their old gaming rig might do just fine this way, but for corporate IT asset disposition, this approach just doesn't scale and completely lacks the compliance documentation you need.
Wholesalers and Bulk Buyers
A more practical option is working with wholesalers or bulk IT hardware brokers. These companies buy large quantities of equipment, refurbish what they can, and then resell it through their own networks. This route dramatically cuts down on the logistical burden compared to listing everything yourself.
You can offload hundreds of items in a single shot, which is a huge time-saver. The catch? The financial return will be lower, since the wholesaler has to build in their own profit margin for testing, repairs, and resale. Plus, while many brokers are reputable, the level of data security and environmental compliance can be all over the map. You’re still on the hook for vetting their processes to make sure they meet your company's standards.
Key Takeaway: Wholesalers offer speed and convenience for large lots of working equipment. But the burden of ensuring certified data destruction and compliant recycling often falls right back on your organization.
The Comprehensive ITAD Partnership
For most organizations, partnering with a certified IT Asset Disposition (ITAD) specialist is the most secure, compliant, and efficient solution by far. ITAD partners aren't just buyers; they're service providers who manage the entire end-of-life process for your technology. A true ITAD partnership shifts the focus from a simple transaction to a comprehensive risk management strategy.
This flowchart breaks down the initial assessment process you'd go through before even picking a channel.
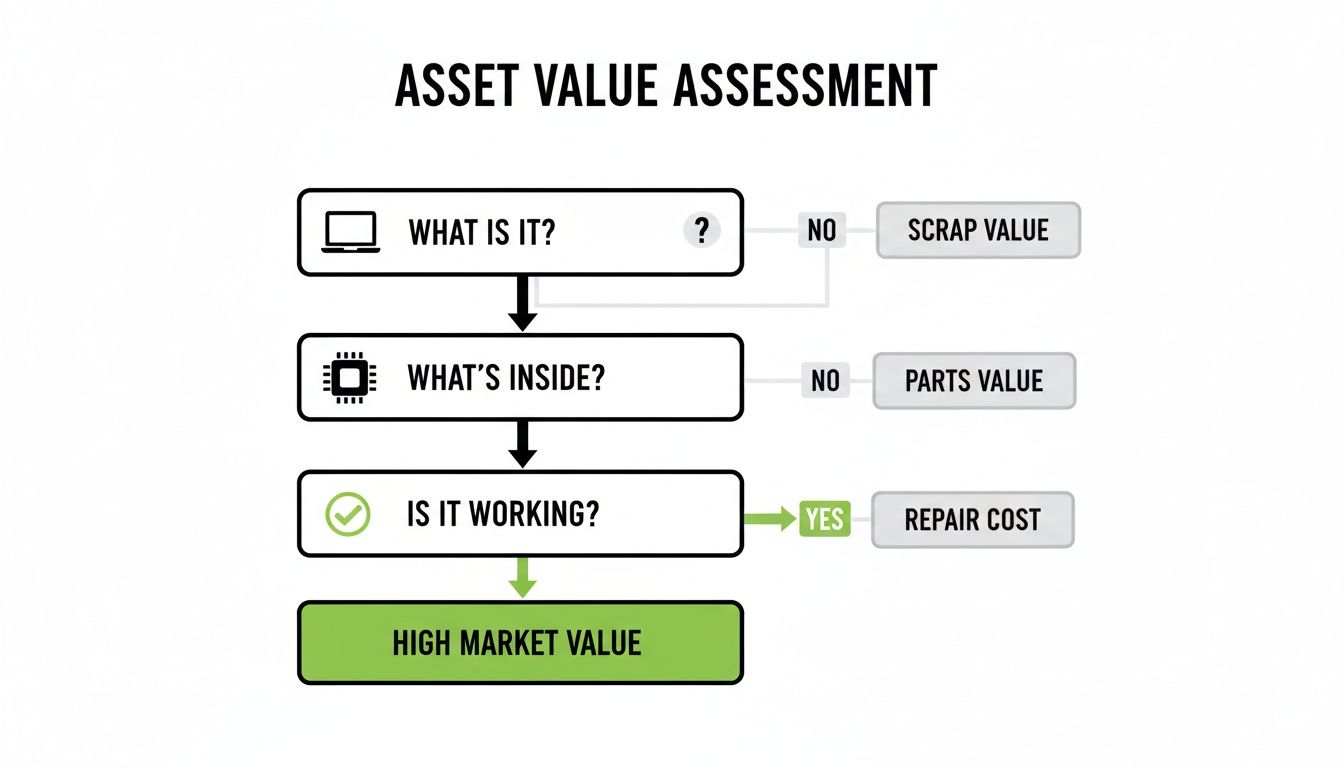
As you can see, knowing what you have, what's inside it, and whether it works is the foundation for making the right disposition choice.
An ITAD provider handles every critical step, including:
- Secure Logistics: Arranging insured and tracked pickup of all assets right from your location.
- Detailed Auditing: Performing their own audit upon receipt to verify your inventory and test every component for functionality.
- Certified Data Destruction: Wiping data to NIST 800-88 standards or physically shredding drives, then providing a Certificate of Data Destruction for every single serialized device.
- Value Recovery: Reselling functional equipment through their established global networks to maximize your financial return, often through a revenue-sharing model.
- Compliant Recycling: Responsibly dismantling and recycling all non-viable assets according to R2 or e-Stewards standards, complete with a Certificate of Recycling.
This end-to-end management is exactly why so many businesses turn to specialists. Personal computers and laptops make up the largest and most valuable slice of the electronics recycling market, commanding 45% of the total market share, which drives huge demand for professional disposition services. You can learn more about this from Fact.MR's electronics recycling research. The sheer volume and value involved make a documented, professional process non-negotiable.
Here's a quick comparison to help you weigh your options at a glance.
Comparing Sales Channels for Used Corporate Hardware
This table breaks down the core benefits and risks of each channel, helping IT managers decide which path best fits their organization's priorities.
| Channel | Best For | Key Benefit | Primary Risk |
|---|---|---|---|
| Online Marketplaces | Small batches of high-value, easy-to-ship items. | Highest potential financial return per unit. | Massive data security liability and high operational overhead. |
| Wholesalers/Brokers | Large quantities of uniform, functional equipment. | Speed and convenience; offload assets in bulk. | Inconsistent data security and compliance documentation. |
| Certified ITAD Partner | Any organization prioritizing security and compliance. | Fully managed, auditable process with risk transfer. | Lower direct return on individual items (offset by risk mitigation). |
Ultimately, choosing a certified ITAD partner means you offload the logistical work and, more importantly, you transfer the risk tied to data security and environmental compliance. Our guide to selecting the right IT asset disposition companies dives deeper into what you should look for. The peace of mind from a fully documented and auditable process is almost always worth more than the few extra dollars you might chase in a riskier channel.
Mastering Certified Data Destruction
Selling old hardware is about more than just making a transaction; it's a huge security responsibility. Every single hard drive and SSD that leaves your facility is a potential data breach waiting to happen. Simply dragging files to the trash bin is nowhere near sufficient for corporate data.
When you're deciding where to sell computer parts, the data destruction method your partner uses is just as important as the sales channel itself. Any professional buyer or ITAD provider must give you proof that your sensitive information has been irretrievably wiped out. This isn't just a best practice—it's a core requirement for compliance and managing risk.

Beyond the Delete Key
Recovering "deleted" files from a hard drive is often ridiculously easy for someone with basic data recovery tools. That's why professional IT asset disposition relies on established, verifiable methods to guarantee your data is gone for good. Knowing the difference is key to protecting your organization.
There are three primary methods a certified partner will use:
- Data Wiping (Sanitization): This is a software-based approach that overwrites every single sector of a drive with random data, often multiple times. The gold standard here is the NIST 800-88 guideline, which ensures data is unrecoverable even with advanced forensic tools. This method also preserves the drive, allowing it to be resold to maximize its value.
- Degaussing: Using a powerful magnet, degaussing obliterates the magnetic field on traditional hard disk drives (HDDs), instantly destroying all the data. It's extremely effective for HDDs, but it also renders the drive completely unusable and doesn't work on Solid-State Drives (SSDs).
- Physical Shredding: For the highest level of security or for drives that have failed, physical destruction is the final word. Industrial shredders grind drives and other media into tiny, unrecognizable fragments, making data recovery physically impossible.
Choosing the right method comes down to the asset's potential resale value and your own internal security policies. Wiping is perfect for valuable, modern drives, while shredding provides absolute certainty for obsolete or damaged hardware.
Real-World Scenario: A regional healthcare provider sold a batch of decommissioned office PCs to a local electronics broker. They thought a simple format was enough and failed to get certified proof of destruction. A year later, a security researcher bought one of those PCs from a reseller and easily recovered thousands of patient records. The result? A massive HIPAA violation, multi-million dollar fines, and irreversible damage to their reputation.
This story highlights a critical truth: without certified proof, you have no defense. The responsibility for the data stays with your company long after the hardware is gone.
The Non-Negotiable Certificate of Data Destruction
The single most important document in this entire process is the Certificate of Data Destruction (CoD). This isn't just a receipt; it's a legally binding record proving your organization did its due diligence. It’s your official evidence for compliance audits and internal security reviews.
For a CoD to be valid, it must include specific details:
- Unique Serial Numbers: Every single drive sanitized or destroyed needs to be listed by its unique serial number. A certificate that just says "50 hard drives" is worthless.
- Method of Destruction: The document has to specify the exact method used for each asset (e.g., "NIST 800-88 Purge," "Physical Shredding").
- Date of Destruction: It should clearly state when the service was completed.
- Service Provider Information: The certificate must be issued by the certified vendor who did the work.
This document effectively transfers liability from your organization to your ITAD partner. When you work with a provider that offers these detailed reports, you're investing in a critical layer of protection. For IT managers who need to ensure their processes are airtight, understanding the details of secure data destruction services is an essential part of the job. It's the only way to turn a potential liability into a verified, secure, and completed task.
Managing Logistics and Secure Chain of Custody
You’ve picked a partner and taken care of certified data destruction. Great. But now comes a challenge that trips up a lot of organizations: how do you get hundreds—or even thousands—of devices from your building to theirs without anything getting lost, damaged, or stolen?
The physical journey of your old computer parts is a massive point of risk. Getting this part right isn't optional.
This is where the idea of a secure chain of custody becomes absolutely essential. It’s nothing less than a documented, unbroken trail that tracks every single asset from the moment it’s unplugged at your office to its final destination. This isn't just about preventing theft; it’s about creating an auditable record that proves you handled everything responsibly—a key piece for both environmental and data security compliance.

What to Look for in a Logistics Plan
A true professional ITAD partner doesn’t just show up with a truck and a vague promise. They should come to the table with a detailed logistics plan that addresses security and tracking at every single stage. When you're evaluating where to sell computer parts, their transportation protocol is a dead giveaway of their overall professionalism.
Before you agree to any pickup, you need to demand absolute clarity on these key points:
- Serialized Asset Tracking: Every device needs to be tagged or scanned at your location before it's even loaded. This initial scan is ground zero for the chain of custody, creating a manifest that both you and the partner sign off on.
- Secure Transport Vehicles: Assets should only be moved in locked, GPS-tracked vehicles. For particularly high-value or sensitive equipment, some partners even offer sealed trucks or transportation with security escorts. Don't be afraid to ask for it.
- Professional, Vetted Personnel: The people handling your equipment—drivers, technicians, everyone—should be uniformed, badged employees of the ITAD company who have passed background checks. No third-party contractors unless they are also vetted to the same standard.
- Adequate Insurance Coverage: Your partner must carry enough insurance to cover the full replacement value of your assets while they're in transit.
A handshake and a smile aren't going to cut it here. Every one of these items should be spelled out clearly in your service level agreement (SLA).
A strong chain of custody is your proof of due diligence. If you ever face an audit or a security incident, this is the documentation that shows your organization took every reasonable step to secure its assets, even after they left your control.
The Arrival and Reconciliation Process
The chain of custody doesn't stop when the truck drives off. Once your assets arrive at the processing facility, the process should be just as strict. Your partner must perform a detailed audit, scanning every single asset again to reconcile the shipment against the original manifest created back at your site.
This is a critical step for transparency. Any discrepancies—a missing laptop, an extra monitor—should be flagged and reported to you immediately. This two-way verification process creates accountability and protects everyone involved. Any reputable partner will give you portal access to see these reports in near real-time.
This level of documentation goes hand-in-hand with the paperwork you get after data sanitization. In fact, if you want to dive deeper into why this is so important, our article on the Certificate of Destruction for hard drives explains exactly why serialized proof is non-negotiable.
Ultimately, a secure logistics plan turns what could be a chaotic mess into a controlled, predictable, and fully auditable operation. It ensures that the value and data locked inside your old computer parts are protected from your door to their final disposition, giving you verifiable peace of mind.
Maximizing Your Financial Return on Used Hardware
Your IT asset disposition program shouldn't be just another expense. Think of it as a strategic value recovery plan. When you figure out where to sell computer parts, you’re not just clearing out old equipment—you’re unlocking the cash that’s been sitting dormant in your storage closets. Getting a handle on the economics of this process is the key to setting realistic expectations and negotiating a better deal.
The financial models you'll come across all boil down to one simple equation: the market value of your hardware minus the costs to process it. Any professional partner worth their salt will be completely transparent about how they arrive at their offer, whether it's an outright purchase or a revenue-sharing agreement.
How Partners Determine the Value of Your Equipment
Valuing your old computer parts is a detailed process, not a ballpark guess. Reputable ITAD partners use a multi-factor approach to calculate the fair market value (FMV) for every single component. This ensures you get a return that accurately reflects what your assets are actually worth on the global secondary market.
Here are the key factors they look at:
- Age and Generation: It’s no surprise that a two-year-old Intel Core i7 processor is far more valuable than one that’s seven years old. The generation of components like CPUs and RAM is a primary driver of price.
- Current Market Demand: The tech market changes fast. For example, a sudden surge in AI data center construction can dramatically increase the demand—and price—for specific types of high-capacity RAM. That trend can directly impact the value of your old server components.
- Condition and Functionality: Every asset gets tested and graded. A fully functional laptop with minor cosmetic scratches (Grade B) is going to fetch a much higher price than a non-working unit that’s just destined for materials recovery.
- Brand and Model: Certain brands like Dell, HP, and Apple often hold more value simply due to their reputation for reliability and the widespread availability of parts.
By combining these factors, a partner builds a detailed valuation report. This document breaks down the value of your assets, giving you the clarity you need to see exactly where your financial return is coming from.
Understanding the Cost Side of the Equation
Recovering value isn't free. There are several essential services that carry costs, which are deducted from the gross resale value of your equipment. Knowing what these are helps you make sense of your final settlement report.
The net return you receive is the fair market value of your assets minus the partner's service costs. A transparent partner will itemize these fees, so you know exactly what you're paying for.
These necessary processing costs typically cover:
- Logistics and Transportation: Secure, insured pickup from your location.
- Labor for Auditing and Testing: The man-hours needed to inventory, test, and grade every single component.
- Certified Data Destruction: The process of wiping or shredding drives to NIST standards and generating the certificates to prove it.
- Responsible Recycling: The cost to properly dismantle and dispose of non-valuable or hazardous materials in compliance with environmental regulations.
This transparent approach is the hallmark of a true partnership.
Revenue Sharing vs. Outright Purchase Models
When it’s time to get paid, you’ll generally see two main models. The best choice really depends on your organization's appetite for risk and whether you want the potential for a bigger payout.
An outright purchase is clean and simple. The ITAD partner assesses your inventory and makes you a flat-rate offer to buy everything. This gives you a guaranteed, immediate payment and transfers all the market risk over to them. It’s a predictable transaction.
A revenue-sharing agreement, on the other hand, means you and the partner split the proceeds after the equipment is sold and all processing costs are covered. This model can often yield a higher return if your assets are in high demand, but the final payment is variable and hinges on market fluctuations.
This is all happening within a massive, growing industry. The global electronics recycling market was valued between USD 43.2 billion and USD 80.8 billion in 2025 and is projected to skyrocket, which shows just how much value is waiting to be recovered from used hardware. To see where this market is headed, you can discover more insights about the electronics recycling industry from Cognitive Market Research.
By viewing ITAD as a financial program, you shift your perspective from simple disposal to strategic asset management. When you need to find a local computer recycling center that truly understands these economics, you ensure your organization not only remains secure and compliant but also adds tangible value back to the IT budget.
Common Questions About Selling Used Computer Parts
When it's time to offload used corporate computer hardware, IT and procurement managers always have a few key questions. Getting clear, straightforward answers is the only way to make decisions that are secure, compliant, and make financial sense. Here are the things we get asked most often.
How Do You Figure Out What Our Old Computer Parts Are Worth?
The value of your used components isn't a guess—it's based on a handful of real-world factors. Any professional ITAD partner will start with a detailed audit, looking at the age, condition, brand, and specs of every single item. Most importantly, they'll check the current secondary market demand.
For example, a pallet of recent-generation CPUs or high-capacity DDR5 RAM is in high demand right now, partly because of the massive AI data center buildouts. That gives them a much higher value than older parts. After testing each component and grading its cosmetic condition, a total market value is calculated. This gross value is then offset by the costs for things like testing, certified data destruction, and recycling anything that can't be resold. You should always get a detailed report that breaks down exactly how they arrived at the final number.
What's the Essential Paperwork We Need When We Sell IT Gear?
The paperwork you get is your proof of due diligence, and frankly, it's just as important as the check you receive. For any corporate IT asset disposal project, there are a few documents you absolutely must have.
These are the non-negotiables:
- Certificate of Data Destruction: This document has to list the unique serial number for every single hard drive or SSD that was wiped or destroyed. It also needs to name the exact method used, like "NIST 800-88 Purge," to prove you met compliance standards.
- Chain of Custody Record: This is your audit trail. It tracks every asset from the moment it leaves your office to its final destination, ensuring nothing gets lost along the way.
- Certificate of Recycling: For any equipment that couldn't be resold, this proves it was handled and recycled in an environmentally compliant way.
A final settlement report that details the financial breakdown is also standard. Without this complete package from your ITAD provider, you have no way to prove you did things right during a security audit.
Can We Sell Parts That Are Broken or Obsolete?
Absolutely, but the approach is different. Instead of being sold for reuse, this equipment is managed for material recovery. Non-functional, damaged, or hopelessly obsolete parts have no resale value on the secondary market, so they enter a certified recycling stream.
A certified electronics recycler will safely dismantle the equipment to separate plastics, metals, and hazardous materials like mercury or lead, all in strict compliance with environmental regulations. While you will likely pay a service fee for this process instead of receiving a payment, you gain documented proof of responsible, compliant disposal, which protects your organization from potential fines for improper e-waste handling.
What Are the Biggest Risks of Using Public Marketplaces?
For a business, trying to sell computer parts on public marketplaces like eBay or Amazon opens the door to two huge risks: data breaches and a complete lack of compliance documentation.
Selling even a single office PC on one of those sites without professional, certified data wiping leaves a trail of sensitive corporate, financial, or customer data that the buyer could easily recover.
Worse yet, these platforms provide no formal, auditable records for environmental compliance or data destruction. If a computer you sold is later found illegally dumped or is discovered to contain sensitive data, your company could be held legally and financially responsible. These channels just don't have the security protocols or the paper trail required for responsible corporate IT asset disposition.
When your organization needs a trusted, nationwide partner for secure and compliant IT asset disposition, Dallas Fortworth Computer Recycling provides the expertise and certified processes you can rely on. We offer end-to-end services with a fully documented chain of custody and certified data destruction to protect your data and your reputation. Contact us today to schedule your secure electronics pickup.
