Computer Recycling Service: Secure IT Disposal & Data Protection
A professional computer recycling service is your partner for securely, legally, and responsibly retiring old IT equipment. It’s a lot more than just hauling away junk—it’s a managed process that includes certified data destruction and responsible materials recovery, protecting your organization from some very serious risks.
The Hidden Risks of Outdated Technology

Every time your business upgrades its servers, laptops, and networking gear, a pile of older devices gets left behind. Too often, this growing inventory of retired tech is seen as a simple storage problem. The reality is far more serious—it's a ticking clock of business risks.
Think about it: every one of those outdated assets, from a single hard drive to a full server rack, holds a ghost of its former life. That ghost is your sensitive company data, customer information, and intellectual property. When that equipment sits unsecured in a closet or is thrown away improperly, it becomes a goldmine for data thieves.
Just one breach can trigger devastating consequences. We're talking about hefty regulatory fines, legal battles, and deep, lasting damage to your company's reputation. And no, just wiping a drive isn't enough. Recoverable data fragments can still be pulled off by someone who knows what they're doing. This is exactly where a professional computer recycling service steps in, turning a huge potential liability into a secure, managed process.
The Scale of the E-Waste Challenge
The sheer volume of electronic waste is growing at a shocking pace. In 2022 alone, the world generated a staggering 62 million tonnes of e-waste. That marks an 82% increase from the 34 million tonnes produced back in 2010. Worse yet, projections show this number climbing another 32% to 82 million tonnes by 2030.
Here’s the real kicker: our recycling efforts aren’t even close to keeping up. Only 22.3% of that e-waste was properly collected and recycled in 2022.
This mountain of discarded electronics creates several critical problems for businesses:
- Data Security Vulnerabilities: Unsecured devices are wide-open doors for data thieves. Without certified destruction, your most sensitive information is completely exposed.
- Regulatory Compliance Penalties: Laws like HIPAA and NIST have strict rules for handling data. Disposing of equipment the wrong way can lead to severe fines and legal trouble.
- Environmental Responsibility: Old electronics are full of hazardous materials like lead and mercury. If they end up in a landfill, those toxins can contaminate soil and water. You can learn more about the environmental impact of electronic waste and how proper recycling stops this from happening.
When you partner with a certified recycling service, you're doing much more than just clearing out a storage room. You're executing a risk-mitigation strategy that protects your data, keeps you compliant, and supports your company’s sustainability goals.
This proactive approach gives IT leaders and data center operators total peace of mind. You know that every single retired asset is handled securely from the moment it leaves your facility to its final disposition. It's the only real way to defuse the hidden risks locked away in your outdated technology.
What a Secure Recycling Service Truly Provides

A top-tier computer recycling service is much more than a disposal company. Think of it as a complete risk management partner, one that's laser-focused on protecting your organization from every possible angle when technology reaches its end of life. This isn't just about hauling away old desktops and servers. It's a methodical process designed to neutralize data threats, ensure you meet all your legal obligations, and even pull maximum value out of those retired assets.
At its core, this service is your insurance policy against the hidden dangers lurking in obsolete equipment. Every IT leader eventually has to answer the same question: how do we get rid of this gear without letting our data walk out the door or accidentally violating a regulation? The answer is found in a suite of specialized services that create a secure, fully auditable chain of custody from your facility all the way to final disposition.
Let’s break down what a true recycling partner actually does for you. These are the pillars of a secure and responsible IT asset retirement strategy.
Certified Data Destruction: The Non-Negotiable First Step
The single most critical job of any computer recycling service is the permanent, irreversible destruction of your sensitive data. Simply deleting files or reformatting a hard drive is dangerously inadequate; anyone with basic recovery software can often pull that "deleted" data right back. Real security demands certified, professional destruction methods.
This process isn't a one-size-fits-all deal. A professional partner uses several techniques, matching the right method to the media type and your specific security needs to ensure nothing is left to chance.
- Physical Shredding: This is the gold standard for definitive destruction. Hard drives, SSDs, and backup tapes are fed into industrial shredders that pulverize them into tiny, unrecognizable fragments. At that point, data recovery is physically impossible.
- NIST-Compliant Data Wiping: For devices that might be refurbished and reused, specialized software overwrites the entire drive with random data multiple times. This process follows strict standards like NIST 800-88, effectively sanitizing the drive beyond recovery.
- Degaussing: A powerful magnetic field is used to instantly scramble the magnetic platters inside traditional hard drives and tapes, destroying all stored data in a single pass.
A Certificate of Destruction is your ultimate proof of compliance. This legally binding document confirms your data-bearing devices were destroyed according to industry best practices, giving you a critical piece of evidence for any audit.
For any organization that handles confidential information, understanding these options is essential. If you want to dig deeper, you can explore the details of secure data destruction services and see exactly how they protect your business.
IT Asset Disposition: A Broader Strategic Approach
While data destruction is absolutely critical, a top-tier service also manages the physical hardware itself through a process called IT Asset Disposition (ITAD). ITAD is a much bigger-picture discipline focused on managing the entire lifecycle of retired tech in a way that is secure, environmentally responsible, and financially intelligent.
Think of ITAD as the master plan for your old equipment. The process kicks off by creating a detailed inventory of every single asset, tracking each item by its serial number. This meticulous accounting ensures nothing gets misplaced and gives you a crystal-clear audit trail. From there, the assets are sorted and professionally evaluated.
Based on that evaluation, items are routed down one of a few paths:
- Responsible Recycling: Components that can’t be reused—like old circuit boards or damaged casings—are broken down into their base materials such as precious metals, copper, and steel. These commodities are then sent to certified downstream processors to be reintroduced into the manufacturing supply chain.
- Refurbishment and Remarketing: Devices that still have useful life, like recent-model laptops or servers, can be securely wiped, tested, and refurbished for resale. This not only supports a circular economy but can also generate a financial return for your organization, helping to offset recycling costs.
Specialized Services for Complex Needs
Beyond standard office gear, a truly capable computer recycling service has the expertise to handle large-scale, highly specialized projects. This is where a partner really proves their value by managing complex logistics and unique technical requirements that would overwhelm most teams.
One of the most demanding jobs is data center decommissioning. This involves the systematic teardown of an entire server environment, from unplugging and removing racks of servers to managing complex cabling and infrastructure. A professional team handles this with precision, ensuring every single asset is securely managed while minimizing disruption to your operations. They also handle specialized medical and lab equipment, which often contains sensitive patient data and must be managed in strict compliance with regulations like HIPAA.
Key Business Benefits of Professional E-Waste Management
Partnering with a professional computer recycling service offers serious advantages that go way beyond just clearing out old equipment. Think of it in terms of three core benefits for any business: bulletproof data security, simplified regulatory compliance, and a genuine boost to your corporate responsibility efforts.
Choosing the right partner isn't just a simple operational task. It’s a key business decision that directly protects your brand, your customers, and your bottom line. Let's break down how these benefits make a real-world impact on your company.
Achieve Bulletproof Data Security
In a world where a single data breach can cost millions, the biggest win you get from a professional service is airtight data security. Every old hard drive, server, and smartphone you retire is a potential backdoor for thieves. Just storing them in a closet or handing them off to an uncertified vendor is an unacceptable risk.
A certified computer recycling service is your last line of defense. They don't just "wipe" drives; they use irreversible methods to make absolutely sure your data is gone for good.
- Physical Shredding: This is exactly what it sounds like. Data-bearing devices are physically pulverized into tiny, mangled fragments, making it impossible for anyone to recover the data.
- Certified Wiping: For equipment that still has life in it, specialized software overwrites the storage media according to strict standards like NIST 800-88, effectively sanitizing it for reuse.
This process completely neutralizes the threat of a data breach from your end-of-life assets. The peace of mind you get from knowing your sensitive information has been verifiably destroyed is invaluable, protecting both your finances and your hard-won reputation.
Simplify Regulatory Compliance
Trying to navigate the tangled web of data privacy regulations is a major headache for any IT or compliance team. Laws like HIPAA, SOX, and NIST have strict rules for how sensitive information must be handled and disposed of. One wrong move can lead to heavy fines and legal trouble.
A professional recycling partner cuts through all that complexity. They give you a clear, auditable trail proving you've met every legal obligation from start to finish.
The most critical piece of this puzzle is the Certificate of Destruction. This is a legally binding document that serves as your official proof that all data-bearing assets were handled and destroyed according to industry best practices and specific regulatory standards.
This documentation is your get-out-of-jail-free card during an audit. Instead of scrambling to prove you did the right thing, you have a clean, concise record that shows complete due diligence. This turns a major compliance burden into a simple, documented procedure, freeing up your team to focus on their actual jobs.
Enhance Corporate Responsibility
In today's market, customers, investors, and even your own employees care about a company's environmental, social, and governance (ESG) principles. How you manage your electronic waste is a very visible part of that story. Tossing old computers into a landfill isn't just bad for the environment; it’s a black mark on your corporate character. You can find out more about the positive benefits of e-waste recycling and its role in sustainability.
Working with a certified e-waste recycler directly supports your ESG goals in a few key ways:
- Minimizing Landfill Waste: Responsible recycling makes sure hazardous materials like lead and mercury are kept out of our soil and water.
- Promoting a Circular Economy: Valuable materials like gold, copper, and aluminum are recovered and put back into the manufacturing supply chain, which reduces the need for destructive new mining.
- Boosting Brand Image: Showing a real commitment to sustainability improves your public reputation and can be a deciding factor for environmentally conscious clients and partners.
By choosing a professional computer recycling service, you’re actively contributing to a healthier planet while building a stronger, more respected brand.
The Secure IT Asset Disposition Process Explained
Ever wonder what really happens to your old IT equipment after it leaves your building? A professional computer recycling service doesn't just make things vanish. It follows a precise, secure, and fully documented process designed to protect your data, keep you compliant, and give you a rock-solid audit trail from beginning to end.
Think of it as a secure supply chain, but running in reverse. Instead of receiving assets, you're retiring them. Every single step—from scheduling the pickup to handing you the final compliance paperwork—is meticulously planned and tracked. This isn't about guesswork; it's a systematic approach that delivers total peace of mind.
This process turns the otherwise complex headache of asset retirement into a manageable, risk-free operation. Let’s walk through each stage to see how a true IT Asset Disposition (ITAD) partner handles your equipment with the security it demands.
Initial Consultation and Logistics Planning
The work begins long before a truck ever pulls up to your door. The very first step is a detailed consultation to get a handle on the scope of your project. A logistics expert will work directly with you to map everything out, ensuring there’s almost no disruption to your day-to-day operations.
This initial planning phase nails down the critical details:
- Asset Inventory: What exactly are you retiring? We're talking servers, laptops, networking gear, storage arrays—the whole lot.
- On-Site Requirements: Are there specific security protocols or access procedures for our team to follow inside your facility?
- Scheduling: A pickup window is scheduled that works for your team, not the other way around.
Getting this planning stage right is the key to a smooth, efficient pickup. It makes sure the right team with the right equipment shows up ready to handle your specific asset mix correctly from the start.
Secure Pickup and GPS-Tracked Transport
Once the plan is locked in, a trained and insured logistics team arrives on-site. They professionally pack and palletize all assets, making sure everything is secure for transit. Each pallet is inventoried and shrink-wrapped before it’s loaded onto a secure vehicle equipped with GPS tracking.
This isn't your standard delivery truck. These vehicles are a critical link in the secure chain of custody. You can track the movement of your assets in real-time, giving you complete visibility from the moment they leave your dock to the moment they arrive at our facility. That level of accountability is non-negotiable.
The moment your assets are loaded onto a GPS-tracked truck, the chain of custody begins. This verifiable trail is your first line of defense, proving that your equipment was securely managed from the instant it left your control.
This disciplined approach is becoming more critical than ever. With e-waste volumes soaring and global recycling rates stuck at a dismal 22.3%, the pressure is on. New regulations are gaining momentum, and IT leaders need a risk-managed disposition process with a guaranteed chain of custody to sidestep data breaches and hefty fines.
Facility Processing and Certified Data Destruction
Upon arrival at the secure processing facility, the real work starts. Your assets are received under constant video surveillance and immediately checked against the initial inventory list. Every single item is accounted for, maintaining that unbroken audit trail. From there, technicians sort the equipment to determine its next step.
This is where the most important part of the entire process happens: certified data destruction.
- Data-Bearing Devices Identified: All hard drives, SSDs, and other storage media are immediately segregated from non-data-bearing assets.
- Destruction Method Applied: Depending on your security requirements, devices are either physically shredded into tiny, irrecoverable fragments or sanitized using NIST 800-88 compliant data-wiping software.
- Verification: The entire destruction process is verified, and the serial numbers of all destroyed media are recorded for the final report.
This flowchart shows how the core benefits of security, compliance, and sustainability are woven together throughout the process.
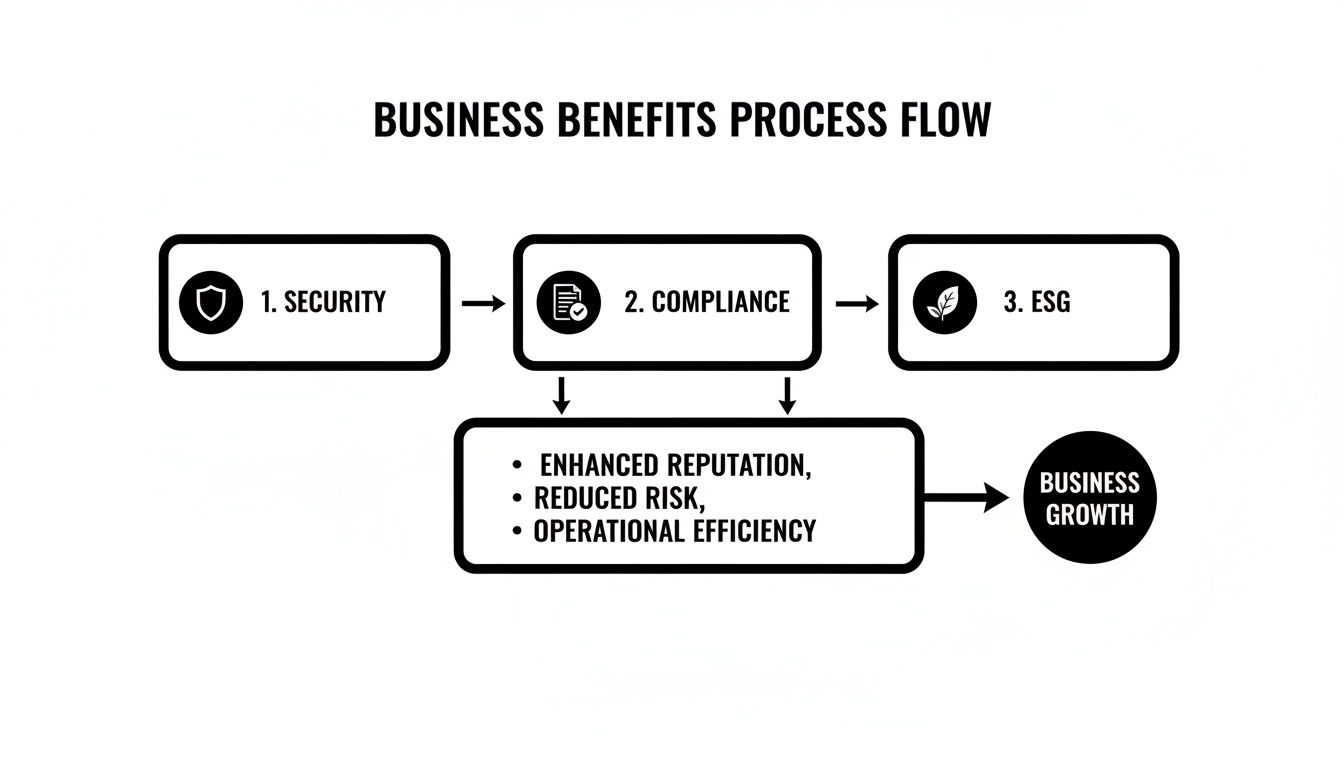
A secure process isn't just about security—it’s the foundation that supports your compliance posture and sustainability goals, creating a powerful, unified strategy.
The table below summarizes the key stages and security measures that define a truly professional ITAD process.
Key Stages of a Secure IT Asset Disposition Process
| Process Stage | Action Items | Key Security Measure |
|---|---|---|
| Consultation & Planning | Inventory assets, define on-site protocols, schedule pickup. | Pre-pickup security alignment ensures no surprises. |
| Secure Logistics | On-site packing, palletizing, and loading by insured teams. | GPS-tracked transport with a documented chain of custody. |
| Facility Intake | Assets received under video surveillance, checked against inventory. | Independent verification of all assets upon arrival. |
| Data Destruction | Media segregated, data wiped or drives physically shredded. | NIST 800-88 compliance and serial number verification. |
| Recycling & Remarketing | Components recycled responsibly, usable assets prepped for resale. | R2-aligned practices and secure data sanitization. |
| Final Reporting | Certificates of Destruction & Recycling are generated and delivered. | Auditable documentation provides legal proof of compliance. |
This end-to-end workflow is designed to leave no room for error, protecting your organization at every turn.
Final Reporting and Auditable Trail
The journey concludes with the most important deliverable of all: the paperwork. A professional computer recycling service provides a full suite of documentation that proves you performed your due diligence. This includes a Certificate of Destruction, which lists the unique serial number of every single drive that was destroyed, along with a Certificate of Recycling.
These documents are your official, legally defensible record. They prove you handled your end-of-life assets responsibly and securely, closing the loop and giving you the hard evidence needed to satisfy any internal audit or external compliance mandate. For a closer look at the bigger picture, check out our detailed guide on what IT asset disposition entails.
How to Choose the Right Recycling Partner
Picking a partner to handle your company's old IT gear is a serious business decision, not just another line item for disposal. The right computer recycling service is a strategic ally who protects your data, your reputation, and your bottom line. The wrong one is little more than a scrap hauler, exposing your organization to massive financial, legal, and reputational risks.
Making the right call means digging deeper than a simple price quote. You need to really vet potential vendors for their certifications, security protocols, and how transparent they are. A true partner provides a complete, auditable process that protects you at every single step, turning a potential liability into a secure, compliant, and closed-loop procedure.
Look for Industry-Leading Certifications
Certifications aren't just fancy logos for a website; they are your independent proof that a recycler meets the highest industry standards for security and environmental care. They mean a third-party auditor has gone through their facility and processes with a fine-tooth comb. The two most critical certifications you should be looking for are R2 and e-Stewards.
- R2 (Responsible Recycling): This certification covers a wide range of best practices, from worker health and safety to data security and ensuring hazardous e-waste isn't illegally exported. An R2-certified partner guarantees a secure chain of custody from start to finish.
- e-Stewards: Often seen as the gold standard, e-Stewards enforces a strict zero-landfill policy and an absolute ban on shipping hazardous e-waste to developing nations. It puts a heavy focus on environmental protection and corporate accountability.
Without these certifications, you have zero verifiable proof that your equipment will be handled the right way once it leaves your building. You can learn more about what it means to be an R2 Certified electronics recycler and why it should be a non-negotiable requirement for your business.
Verify Data Destruction Standards
By far, the biggest risk in getting rid of old IT equipment is a data breach. Any potential partner must show you they follow recognized data destruction standards. Don't be shy—ask them directly about their process and demand proof.
The gold standard for wiping data is NIST 800-88, a set of guidelines from the National Institute of Standards and Technology. A compliant vendor will offer different destruction methods, like physical shredding and certified data wiping, and must provide a detailed Certificate of Destruction that lists the serial number of every single drive they sanitized or destroyed.
Choosing a partner who can't provide a NIST 800-88 compliant Certificate of Destruction is like locking your front door but leaving the back window wide open. It gives you a false sense of security while leaving your data completely exposed.
Evaluate Logistics and Insurance Coverage
A professional service doesn't just start and end at the recycling facility. A vendor’s logistics capabilities tell you a lot about their professionalism and commitment to security. Do they have their own fleet of secure, GPS-tracked trucks? Are their employees trained, background-checked, and insured to handle sensitive equipment inside your office?
Also, ask about their insurance. A reputable computer recycling service should carry significant liability insurance, including specific policies for data breach and pollution liability. This coverage protects your company if something goes wrong during transit or processing. It shows the vendor is willing to stand behind their work.
This due diligence is critical. Global e-waste recycling rates were a dismal 22.3% in 2022, meaning a huge amount of electronics just disappears off the books. Much of this undocumented e-waste is dumped in landfills or illegally exported, creating enormous risks for the businesses that threw it out—especially when that gear contains sensitive data governed by HIPAA or NIST. You can read more about these global e-waste statistics and their implications on Statista.com.
Insist on Transparent Reporting
Finally, a true partner provides a clear, comprehensive, and auditable paper trail for every single asset they touch. Vague, summary-level reports just don't cut it. You should expect and demand detailed documentation, including:
- Itemized Asset Reports: A full list of all equipment they picked up, including makes, models, and serial numbers.
- Certificates of Destruction: Legally binding documents that confirm the secure destruction of every hard drive and data device.
- Certificates of Recycling: Proof that all non-reusable materials were processed in an environmentally responsible way.
This level of transparency is essential for your internal audits and proving regulatory compliance. It provides the concrete evidence you need to show you did your due diligence, confidently separating a real ITAD partner from a basic scrap hauler.
Frequently Asked Questions About Secure IT Recycling
When it's time to retire old IT gear, IT managers and compliance officers always have a few critical questions. That’s a good thing. Making the right choice protects your company's data, its reputation, and its bottom line. Here are some straightforward answers to the questions we hear most often.
What Kinds of Electronic Equipment Do You Handle?
We handle the full range of business and public-sector IT assets. Our services are built to manage everything from the desktops in your office to the complex hardware running your data center.
This includes, but isn't limited to:
- Servers, storage arrays, and networking gear
- Desktop computers, laptops, and tablets
- Monitors, printers, and peripherals
- Specialized medical and laboratory equipment
Basically, if it was part of your IT ecosystem, we have a secure and responsible process for its retirement. Our goal is to be the single partner you need for all your e-waste.
Choosing a partner who can manage your entire asset portfolio simplifies logistics and ensures consistent security standards across the board. It eliminates the hassle of vetting multiple vendors for different types of equipment.
How Can I Be Certain My Data Is Destroyed?
This is always the most important question, and the answer comes down to one thing: a verifiable, certified process. We guarantee complete data destruction using methods that strictly follow NIST 800-88 guidelines—the gold standard for media sanitization.
You have two main options for total peace of mind:
- Physical Shredding: We use industrial shredders to literally pulverize hard drives, SSDs, and other storage media into tiny, useless fragments. After this, data recovery isn't just difficult; it's physically impossible.
- Certified Data Wiping: For assets that might have a second life through refurbishment, we use specialized software to overwrite the entire drive with random data. This permanently erases the original information, rendering it completely inaccessible.
Once the job is done, we issue a legally binding Certificate of Destruction. This document lists the unique serial number of every single drive we destroyed, giving you an auditable and unshakeable record for your compliance files.
What Kind of Documentation Will I Receive?
Comprehensive documentation is the cornerstone of our service. It’s the proof you need to satisfy internal stakeholders, auditors, and external regulators. After we process your assets, you’ll get a complete reporting package.
This typically includes:
- A Certificate of Destruction: Your official record proving all data-bearing devices were securely and permanently destroyed.
- A Certificate of Recycling: Confirmation that all non-reusable materials were processed in an environmentally responsible manner.
- An Itemized Asset Report: A detailed inventory list of all equipment we received, often including serial numbers for precise tracking.
This paperwork closes the loop on your asset disposition process, providing a clear and defensible trail from start to finish.
How Are the Costs for Recycling Services Determined?
The cost of a professional computer recycling service depends on a few key factors. We believe in being transparent, so you’ll always understand exactly what you’re paying for.
The main cost drivers include:
- Logistics: This covers the complexity of the pickup—things like your location, the number of assets, and any on-site labor needed to pack and load the equipment.
- Processing: The specific services you require, primarily the method of data destruction, will influence the cost.
- Asset Value: Here’s the good news. If your equipment has remarketing potential, its resale value can often offset or even exceed the service costs. In some cases, this can result in a net return for your organization.
Partnering for a Secure and Sustainable Future
Deciding what to do with retired IT assets is a major strategic move that touches nearly every part of your business. This isn't just about clearing out a storage room full of old hardware. It’s about proactively protecting your sensitive data, meeting your legal duties, and backing up your public commitment to sustainability.
A professional computer recycling service is your expert partner in this critical work. They bring the certified processes and specialized knowledge needed to navigate the complex world of IT asset disposition. Without that expertise, you’re gambling with data breaches, regulatory fines, and brand damage that can take years to fix.
When you choose a secure, compliant, and responsible path for your old tech, you do more than just manage risk. You actively strengthen your reputation as a forward-thinking and responsible leader in your industry. It sends a clear message to customers, stakeholders, and employees that you take your obligations seriously.
More Than Disposal—A Strategic Partnership
Don't think of this as a simple vendor transaction. It's a strategic partnership. The right provider becomes an extension of your IT and compliance teams, helping you manage the entire end-of-life technology cycle. This collaboration ensures every retired asset is handled with the same level of care it received during its active service.
This partnership delivers real, tangible value:
- Risk Mitigation: It transfers the heavy burden of secure data destruction and environmental compliance to a certified expert.
- Operational Efficiency: It frees up your internal teams from the complicated logistics of managing obsolete equipment.
- Enhanced Reputation: It provides concrete proof of your commitment to corporate social responsibility and environmental stewardship.
Choosing a certified recycling partner is an investment in your organization's security and integrity. It turns a logistical headache into an opportunity to reinforce your commitment to responsible business practices, ensuring your technological legacy is one of security and sustainability.
This forward-looking approach ensures that as your technology evolves, your commitment to protecting data and the environment stays locked in. It’s the final, crucial step in a secure IT lifecycle, guaranteeing that your past innovations don’t become future liabilities. By embracing this strategy, you build a more resilient, reputable, and sustainable organization ready for whatever comes next.
Ready to turn your retired IT assets into a secure and sustainable advantage? Dallas Fortworth Computer Recycling offers nationwide, certified ITAD services to protect your data and enhance your ESG goals. Learn more and schedule your secure pickup today.
