How to Choose the Right Computer Recycle Companies
Picking the right computer recycling partner used to be an afterthought. Not anymore. Today, it’s a critical decision that directly impacts your company’s data security, regulatory standing, and even your brand's reputation. As the mountain of e-waste grows, so do the risks of getting it wrong.
This guide is designed to give IT leaders like you a clear, practical framework for navigating this complex choice.
Why Your Choice of Recycling Partner Matters More Than Ever
Think of your IT asset disposal (ITAD) vendor as a specialized security firm you’re entrusting with your most sensitive information. A decade ago, this was just about getting rid of old gear, usually by finding the lowest bidder. Now, it’s a strategic function that’s woven into your organization’s risk profile, budget, and public image. The stakes are simply too high to leave it to chance.
Constant tech upgrades mean businesses are retiring assets faster than ever, creating an unprecedented flood of e-waste. This isn't just a hunch; the numbers are staggering. The global computer recycling market is on track to hit USD 13,634.26 million in 2025 and is expected to jump to USD 22,981.53 million by 2033. This growth is fueled by everything from massive data center upgrades and 5G rollouts to the everyday cycle of hardware retirement.
The Four Pillars of Vendor Evaluation
With so many computer recycling companies out there, it’s easy to get lost in marketing fluff. To cut through the noise, you need a structured approach. We recommend focusing your vetting process on four essential pillars. These pillars will give you a solid foundation for assessing a partner's real-world capabilities and reliability.
Before you go any further, it's helpful to see how these pillars fit together. This table provides a quick-glance summary of what you should be looking for.
Key Evaluation Pillars for Computer Recycling Partners
| Pillar | What to Look For | Why It Matters |
|---|---|---|
| Security & Data Destruction | Certified, auditable data wiping or physical destruction that meets standards like NIST 800-88. | This is your frontline defense against a data breach that could cost you millions and destroy customer trust. |
| Compliance & Certifications | Industry certifications like R2v3 or e-Stewards. | These aren't just logos; they are third-party proof that a vendor follows strict environmental and data security rules. |
| Environmental Stewardship | Transparent downstream reporting that proves where every component goes. | You need to know that your assets aren't ending up in a landfill or being illegally exported, which can damage your brand. |
| Logistics & Value Recovery | The ability to handle complex pickups (nationwide, multi-site) and generate revenue from remarketable assets. | A true partner makes the process seamless and can even turn your retired IT into a revenue stream instead of a cost. |
Think of these pillars as the core of your evaluation. Each one is a non-negotiable part of a responsible ITAD program.
Your evaluation should be built around these key areas:
- Security and Data Destruction: Can the vendor prove they can securely erase or physically destroy your data? Anything less than a process meeting NIST 800-88 standards is a red flag.
- Compliance and Certifications: Look for R2v3 or e-Stewards certifications. These are the gold standards, showing a commitment to doing things the right way.
- Environmental Stewardship: Ask for their downstream reporting. A reliable partner will be able to show you exactly where every piece of your old equipment ends up. No exceptions.
- Logistics and Value Recovery: Can they handle the heavy lifting, literally? You need a partner who can manage nationwide pickups and has a system for getting you money back on still-valuable assets.
Choosing the right partner transforms IT asset disposition from a cost center into a risk mitigation strategy. The goal is to find a vendor who acts as an extension of your security and compliance teams, not just a disposal service.
Failing to vet a partner properly can backfire spectacularly, leading to massive fines, brand damage, and catastrophic data leaks. A thorough process isn't just about due diligence; it's about protecting your entire organization. If you need a starting point, you might be interested in finding a local computer recycling center that already meets these high standards.
Understanding Essential Certifications and Compliance
Diving into the world of IT asset disposition can feel like learning a new language, especially with an alphabet soup of certifications like R2, e-Stewards, and NAID AAA. These aren't just fancy logos a vendor slaps on their website; they're your primary guarantee that a potential partner meets strict, third-party-audited standards for security, environmental safety, and professional operations.
Think of these certifications like a building code for computer recycling companies. A building put up without following code might look okay from the outside, but it could be hiding serious structural flaws that expose you to massive risk. In the same way, an uncertified recycler might offer a low price, but they operate without the verified processes that protect your organization from data breaches and environmental fines.
The Gold Standard Certifications Explained
When you're vetting potential partners, a few key certifications should be on your non-negotiable list. They immediately signal a high level of professionalism and accountability, and any vendor who lacks them needs a whole lot of extra scrutiny.
Here are the certifications that really matter:
R2v3 (Responsible Recycling): This is the leading global standard for the electronics recycling industry. The latest version, R2v3, puts a heavy emphasis on data security, requiring certified companies to follow strict media sanitization protocols. It also mandates a transparent and accountable downstream vendor management system, ensuring that hazardous materials are never illegally dumped or exported. You can learn more about what it means to be an R2 certified electronics recycler and why it's a critical baseline.
e-Stewards: Developed by the environmental watchdog group Basel Action Network (BAN), the e-Stewards standard is famous for its hardcore environmental protections. It has a zero-tolerance policy for exporting hazardous e-waste to developing nations and a zero-landfill policy. While both R2 and e-Stewards are excellent, e-Stewards is often seen as the most rigorous from a purely environmental perspective.
NAID AAA Certification: This one is all about data destruction, period. Run by the International Secure Information Governance & Management Association (i-SIGMA), it puts vendors through tough, unannounced audits of their entire data destruction process—from employee screening and facility security to the destruction methods themselves. If data security is your absolute top priority, a partner with NAID AAA certification offers the highest level of assurance you can get.
Why Certifications Are Your Best Defense
These standards do more than just set guidelines; they build a framework of accountability. Choosing a certified partner isn't about checking a box—it's an active risk mitigation strategy. It gives you a defensible, auditable process that will stand up to scrutiny from your internal compliance teams, external auditors, and government regulators.
For example, if your company handles protected health information (PHI), you're bound by HIPAA regulations. One data breach could trigger devastating fines.
A certified data destruction process, verified by standards like R2v3 or NAID AAA, is a critical component of your HIPAA compliance strategy. It provides documented proof that you took every reasonable step to protect sensitive patient data on retired assets.
Without that third-party validation, the burden of proof falls entirely on your shoulders. You’re essentially just taking the vendor's word for it, which is a huge gamble when millions of dollars and your company’s reputation are on the line.
An uncertified vendor is a major weak link in your security chain. Asking for a copy of their current certifications should be one of the very first questions you ask any potential partner.
Mastering Data Security and Chain of Custody
When you hand over retired IT assets, you’re not just getting rid of old hardware. You're entrusting a partner with the keys to your kingdom—the sensitive data stored on every single device. Customer lists, financial records, proprietary information… it's all incredibly valuable, and in the wrong hands, incredibly dangerous. This is why top-tier computer recycling companies make data security and an unbreakable chain of custody their absolute top priorities.
The process of securing data on end-of-life assets isn't one-size-fits-all. It really comes down to two main approaches: software-based wiping and physical destruction. Knowing the difference is critical for choosing the right path for your organization's risk tolerance.
Think of it this way: software-based wiping is like meticulously scrubbing a whiteboard clean. A specialist using certified tools, often aligned with the NIST 800-88 standard, can wipe a hard drive so completely that the original information is gone for good. The big advantage here is that the drive can be reused, which is great for recovering value and supporting sustainability goals.
Physical destruction, on the other hand, is like running that same whiteboard through an industrial shredder. There is no coming back from that. The hard drive is pulverized into tiny, unrecognizable fragments, guaranteeing the data can never be accessed again. This is the go-to method for highly sensitive data or for drives that are too old or faulty to be wiped and reused.
The Unbroken Chain of Custody
No matter which destruction method you choose, the entire process must be governed by a strict chain of custody. This is easily the most important concept in secure IT asset disposition. It’s the documented, unbroken trail that tracks every single asset from the moment it leaves your facility to its final, verified destruction or reuse.
A strong chain of custody isn't just a process; it's your legal and operational shield. It provides the auditable proof that your organization acted responsibly, which is essential for meeting compliance standards and protecting yourself from liability.
A documented chain of custody is non-negotiable. It’s what separates a professional IT asset disposition partner from a simple scrap hauler. The process has to be transparent and verifiable at every single step.
This flowchart gives a great overview of the key certifications that back up these secure processes.
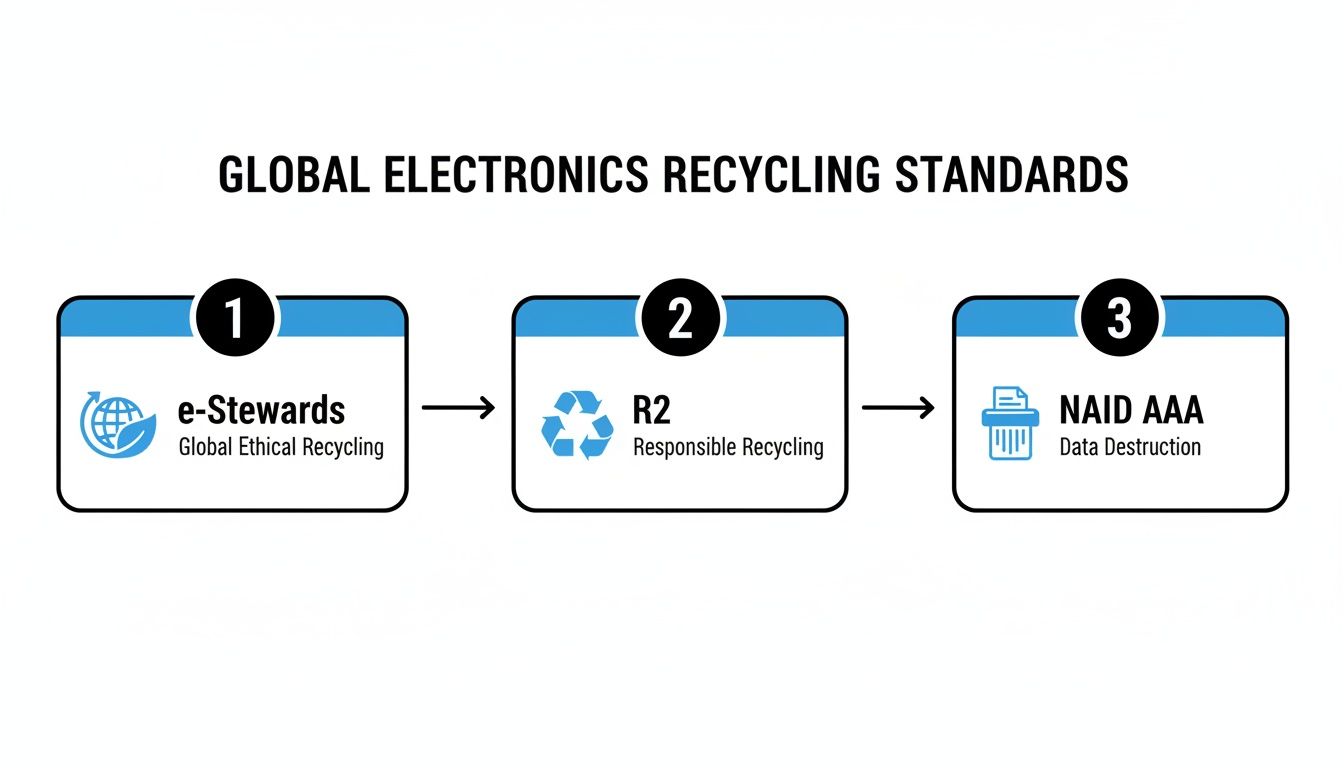
As you can see, top-tier certifications like e-Stewards, R2, and NAID AAA create a solid foundation for trustworthy and secure asset management.
What a Secure Process Looks Like
A robust chain of custody is built on several key operational pillars. When you're vetting a potential partner, you should see these elements in action:
- Serialized Asset Tagging: Before anything leaves your site, each individual device—laptop, server, hard drive—should be scanned and tagged with a unique serial number. This is the first link in the audit trail.
- Secure Logistics: Transportation isn't an afterthought. Assets should be moved in locked, GPS-tracked vehicles operated by screened employees to ensure they are never vulnerable in transit.
- Controlled Facility Access: The recycling facility itself needs to be a fortress. Look for 24/7 video surveillance, restricted access zones for data-bearing devices, and strict visitor protocols.
- Auditable Reporting: Once the job is done, you should receive a detailed, serialized report. This document confirms the final disposition of every single asset, whether it was wiped, destroyed, or resold.
The Certificate of Data Destruction
The final piece of the security puzzle is the Certificate of Data Destruction. This document is far more than just a receipt; it’s a legally binding record that serves as your ultimate proof of compliance. It attests that your data was destroyed according to specific standards and lists the serial numbers of the media that was sanitized or shredded.
This certificate is your definitive answer when auditors, compliance officers, or executives ask, "How do we know the data is really gone?" It officially closes the loop on the chain of custody and transfers liability from your organization to your recycling partner. For a deeper dive, you can learn more about comprehensive security and data destruction services that meet these rigorous standards.
Evaluating True Environmental Stewardship and Reporting
Nearly every computer recycling company calls themselves “green,” but true environmental stewardship is about much more than marketing slogans. For IT leaders responsible for upholding your company's Environmental, Social, and Governance (ESG) goals, you have to look past the promises and evaluate a partner's real-world impact.
Genuine sustainability isn't just about keeping old hardware out of a dumpster. It’s a deliberate, disciplined approach to managing the entire asset lifecycle.
This philosophy is best captured by the recycling hierarchy. Think of it as a priority list, where the most environmentally sound options always come first. The top priority is always reuse—refurbishing a working laptop or server to give it a second life. This is the heart of the circular economy, as it slashes the demand for new manufacturing and the energy that comes with it.
Only when an asset is truly beyond repair should a top-tier vendor move down the list to material recovery. This means responsibly dismantling the device into its core components—plastics, metals, and circuit boards—to be recycled. The absolute last resort, which any certified recycler works hard to avoid, is the landfill.
The Dangers of E-Waste Exporting and Downstream Visibility
One of the biggest risks in our industry is the unethical exporting of hazardous e-waste. Some vendors cut corners by shipping non-working electronics to developing nations that don't have the proper infrastructure to handle toxic materials like lead and mercury.
This practice not only poisons communities abroad but also creates a massive liability that can trace right back to your company.
To avoid this, you must demand transparent downstream reporting. This is the documented paper trail proving where every single component of your retired assets ends up. A reputable partner will provide an auditable chain of custody showing that your equipment was processed by fully vetted and certified downstream partners.
A vendor who can’t provide a clear, documented map of their downstream recycling chain is a major red flag. This lack of transparency often hides irresponsible disposal practices that can directly contradict your company's ESG commitments.
Without this visibility, you’re flying blind and just hoping for the best. You can learn more about the critical need to understand the environmental impact of electronic waste and how to mitigate these risks.
Key Metrics and Questions to Ask
When vetting potential computer recycling partners, push past the generic claims and ask for specific, measurable proof. North America's e-waste recycling market now commands a 37% global share, valued at USD 17,320.66 million, and it's growing because of strong regulations.
With devices like PCs and servers expected to make up 43.85% of all e-waste by 2025, the need for specialized, verifiable services is undeniable. To make sure a vendor truly aligns with your environmental goals, ask these direct questions:
- What is your landfill diversion rate? A high rate (look for over 98%) is a clear indicator of a serious commitment to recycling and reuse.
- Can you provide a sample downstream vendor audit report? This proves they are actively monitoring and vetting their partners.
- How do you prioritize reuse and remarketing over raw material recycling? Their answer will tell you everything you need to know about their commitment to the recycling hierarchy.
Breaking Down Pricing Models and Logistics
Before you can sign on the dotted line, you need a firm grasp of the money and the moving parts. Working with a computer recycling company isn't always a simple per-pound transaction. The pricing can swing from a net cost to your company to a net return on your assets. At the same time, the logistics have to be airtight to avoid throwing a wrench in your day-to-day operations.
Think of it like getting rid of a used car. A 15-year-old clunker with a busted engine will probably cost you money to have it towed away. But a three-year-old sedan with low mileage? That could put a nice check back in your pocket. The same logic applies to your old IT gear. A good partner’s pricing should reflect the real market value of your equipment, not just its weight on a scale.
Common Pricing Structures
When you get a quote, it's going to fall into one of a few common buckets. It’s crucial to understand what each one means for your bottom line. An initial quote is just that—a start. The real value comes from the combination of mitigated risk, potential revenue, and operational peace of mind.
Here’s a quick rundown of what you’ll likely see:
- Cost-Based Services: This is for the old stuff. For equipment that’s non-functional, obsolete, or has no resale value, you’ll pay a fee. This fee covers the secure transportation, certified data destruction, and responsible recycling of all the materials. Think old CRT monitors, ancient printers, and desktops from a decade ago.
- No-Cost Recycling: Sometimes, a vendor will offer to pick up and process your equipment for free. This usually happens when your load has enough desirable assets—like newer laptops or servers—that the value they can recover from those items covers the cost of handling the junk.
- Value Recovery / Revenue Sharing: This is the best-case scenario, especially for big hardware refresh projects. If your retired assets have resale value (like laptops under five years old or recent-model servers), your partner will refurbish and sell them. You then get a share of the profits, which can often wipe out all your recycling costs and even generate a positive return for your IT budget.
Clarifying Logistics and Operations
The most attractive pricing model on earth is worthless if the logistics are a mess. A professional ITAD partner should feel like an extension of your own team, making the entire process smooth and predictable. This is absolutely critical for companies with multiple offices or a remote workforce.
A partner’s logistical capability is a direct reflection of their professionalism. Vague timelines, inflexible scheduling, and surprise fees are red flags. They point to an immature operation that will create business disruptions and hidden costs down the road.
Before you agree to anything, get crystal-clear answers on how they operate. An elite partner should be able to handle complex jobs without breaking a sweat.
Make sure they can cover:
- Nationwide Coordination: Can they schedule pickups from all your locations across the country and consolidate everything under a single, unbroken chain of custody?
- On-Site Services: Do they offer on-site services like hard drive shredding or asset decommissioning for data centers? This provides maximum security before any equipment even leaves your building.
- Detailed Quoting: Your quote needs to be itemized and transparent. Ask pointed questions about potential surcharges for things like palletizing, shrink-wrapping, or handling non-standard equipment. You don't want any nasty surprises on the final invoice.
Building Your RFP and Vetting Vendors Like a Pro
Now that you have a solid grasp of the security, compliance, and environmental standards that matter, it's time to find the right partner. This is where a well-built Request for Proposal (RFP) becomes your most important tool. A strategic RFP does more than just gather price quotes; it’s designed to make potential vendors prove they can meet your organization's specific needs.
Think of your RFP as a detailed interview script, not just a questionnaire. It's your opportunity to cut through the marketing fluff and ask the tough, operational questions that separate a true ITAD professional from a basic scrap hauler. Vague questions will always get you vague answers. Sharp, specific inquiries, on the other hand, demand concrete proof.
Crafting a Strategic Request for Proposal
Your RFP should be structured around the core pillars we’ve covered: security, compliance, logistics, and value recovery. Don't just ask, "Are you certified?"—a question that only gets a simple "yes" or "no." Instead, demand the evidence. Frame your questions to pull out detailed responses that reveal a vendor's actual processes and professionalism.
A strong RFP should require vendors to provide:
- Copies of all current certifications (like R2v3, e-Stewards, and NAID AAA).
- A sample Certificate of Data Destruction and a sample serialized audit report from a recent project similar to yours.
- Proof of insurance, including general liability, pollution liability, and data breach coverage.
- A detailed breakdown of their downstream vendor audit process to prove they handle all materials responsibly.
This level of detail ensures you're comparing apples to apples and making a decision based on mitigating risk, not just on who has the lowest price.
The goal of your RFP is to make it impossible for a subpar vendor to hide behind slick brochures. By demanding specific documentation and detailed process descriptions, you force them to prove their competence and transparency from the very beginning.
This proactive approach puts you in control, allowing you to make an informed and defensible decision for your organization. This is more important than ever, given the market trends.
The e-waste market is seeing explosive growth, particularly in IT and telecom hardware, with a projected 14.55% CAGR fueled by constant data-center upgrades and cloud migrations. As landfill bans tighten, professional recycling is on track to handle 60.88% of all formal e-waste disposal by 2025, making a rigorous vetting process absolutely critical.
The Essential Vendor Vetting Checklist
Once the RFP responses are in, it’s time to vet your finalists. The table below provides a scannable checklist of critical questions to ask potential partners. Use it to guide your conversations and ensure you cover all the crucial bases.
| Category | Question to Ask | Ideal Answer Should Include |
|---|---|---|
| Security & Chain of Custody | "Walk me through your chain-of-custody process, from the moment your truck arrives at our dock to the final certificate of destruction. Where are the specific handover points?" | Details on locked trucks, sealed pallets, GPS tracking, secure facility access, documented handovers, and how each step is recorded. |
| Downstream Accountability | "Can you provide a list of your primary downstream partners? How often are they audited, and can we review a redacted copy of a recent audit report?" | Transparency about their downstream chain, a clear audit schedule (e.g., annually), and a willingness to share audit results to prove compliance. |
| Logistical Capability | "Describe your process for a multi-site national pickup. How do you ensure consistent service levels, security, and reporting across all locations?" | A clear plan for centralized coordination, uniform protocols for all sites, standardized documentation, and experience managing complex logistics. |
| Value Recovery | "What is your process for testing, grading, and remarketing our assets? Please provide a sample report showing the resale value and our net revenue share." | A defined methodology for asset evaluation, transparent reporting that breaks down gross sales, fees, and the final client payout. |
| Problem Resolution | "Describe a time when a client's asset was damaged or lost in transit. What was your process for notifying the client and resolving the issue?" | A straightforward description of their incident response plan, including immediate client notification, investigation protocols, and insurance claims. |
| Compliance & Reporting | "What kind of reporting can we expect? Can you provide a sample serialized asset report that includes make, model, serial number, and final disposition status?" | The ability to provide detailed, serialized reports that are audit-ready and can be customized to meet your specific compliance or inventory needs. |
These questions go far beyond the surface, pushing vendors to provide substantive, evidence-based answers. The best IT asset disposition companies will welcome these questions as an opportunity to showcase their superior processes and build trust from day one.
Your Top Questions About Computer Recycling, Answered
When you're sorting through the details of IT asset disposition, a few key questions always come up. Here are straight, clear answers to the most common concerns we hear from IT leaders, designed to help you move forward with confidence.
What’s the Real Difference Between ITAD and Basic Computer Recycling?
Think of basic computer recycling as just the final step: breaking down old hardware to salvage raw materials like plastic and metal. It's simply a disposal process.
IT Asset Disposition (ITAD), on the other hand, is the whole playbook. It’s a comprehensive security and compliance strategy that covers everything from certified data destruction and serialized asset tracking to potentially remarketing gear to recover value. For any business serious about managing risk, ITAD is the only approach that provides a complete, auditable trail.
Can We Actually Get Money Back for Our Old Computers?
Yes, absolutely. This is what we call value recovery. If your retired assets—like recent-model laptops, servers, or networking gear—still have some life left in them, a qualified ITAD partner can securely refurbish and resell them for you.
You then get a share of the sales revenue. In many cases, this return can offset or even completely cover the cost of recycling your older, zero-value equipment, turning a line-item expense into a positive on the balance sheet.
How Can I Be 100% Sure Our Data Is Gone for Good?
Your proof is a legal document called a Certificate of Data Destruction. Any reputable partner will provide this, and it’s not just a piece of paper—it’s your official record of compliance. This certificate meticulously lists the serial numbers of every single drive or device that was sanitized and details the exact method used, like shredding that meets the NIST 800-88 standard.
For the highest level of assurance, top-tier computer recycling companies offer on-site shredding. This service lets you and your team witness the physical destruction of your hard drives at your own facility before they even leave the building. It doesn't get more secure than that.
What’s the Worst That Can Happen if We Use a Non-Certified Recycler?
Cutting corners with a non-certified recycler is a huge gamble. You’re opening the door to massive risks, including data breaches, crippling environmental fines, and brand damage that’s hard to undo. Without certifications like R2v3 or e-Stewards, you have no third-party proof that their security, environmental practices, or downstream recycling chain are legitimate.
The bottom line is that your company remains liable for any data leaks or improper disposal, even long after the equipment is out of your hands. It’s a risk that’s just not worth taking.
When your organization needs a trusted, nationwide partner for secure and compliant IT asset disposition, Dallas Fortworth Computer Recycling delivers. We provide certified data destruction, transparent reporting, and responsible recycling to protect your data and your reputation. Learn more about our services at https://dallasfortworthcomputerrecycling.com.
