IT Leaders: Select Local Telecom Companies Wisely

A branch office lease gets signed, the project plan says “network ready by go-live,” and suddenly telecom turns into a board-level risk. The circuit order isn’t just a utility request anymore. It affects cutover timing, cloud access, voice continuity, security reviews, and what happens later when that site closes or gets folded into another location.
That’s where many IT teams underestimate local telecom companies. They focus on price and quoted bandwidth, then discover the harder parts later: limited construction visibility, vague support boundaries, awkward carrier handoffs, and unclear responsibility for provider-owned or provider-managed hardware at end of term.
For an IT director, the better approach is to treat telecom as a full lifecycle decision. Selection matters. Contract language matters. Decommissioning matters too. If you only evaluate the front end of the relationship, you leave risk sitting in the rack room at the back end.
The Modern IT Leader’s Telecom Challenge
A lot of telecom decisions start under pressure. You’re opening a location, consolidating infrastructure, replacing MPLS with internet-first transport, or cleaning up a tangle of inherited circuits after an acquisition. Procurement wants a fast answer. Operations wants low disruption. Security wants clean answers about access, logging, and managed equipment.

National carriers can look like the safe choice because they promise broad reach and familiar brands. But in practice, local telecom companies often win on the details that make or break service delivery. They usually know the building, the local loop reality, the municipal construction constraints, and which properties are lit versus merely “near-net” on a sales slide.
Where local providers help
Local providers tend to stand out in a few operational areas:
- Regional knowledge: They often know which business parks have clean fiber paths and which require expensive construction.
- Faster field coordination: Local dispatch and local engineering can reduce back-and-forth during installs and repairs.
- Custom service design: They’re often more willing to shape a solution around a site’s constraints instead of forcing a standard bundle.
- Direct accountability: It’s easier to escalate when the sales team, project manager, and field operations are in the same region.
Where they can create risk
That doesn’t mean local is automatically better.
Practical rule: Never confuse local presence with enterprise maturity.
Some local providers have strong plant but weak documentation. Others sell managed edge equipment without clearly defining patching responsibility, replacement timing, or return obligations. Some rely heavily on third-party last-mile arrangements, which can blur accountability during outages.
The core challenge isn’t picking “local” or “national.” It’s identifying which provider can support your business model, your support expectations, and your asset controls from install through retirement.
Understanding the Local Telecom Landscape
The easiest way to explain the market is this. Choosing among telecom providers is a bit like choosing between a national supermarket and a strong regional grocer. The national chain offers reach and consistency. The regional operator often knows the neighborhood better, stocks what local buyers need, and responds faster when something goes wrong.
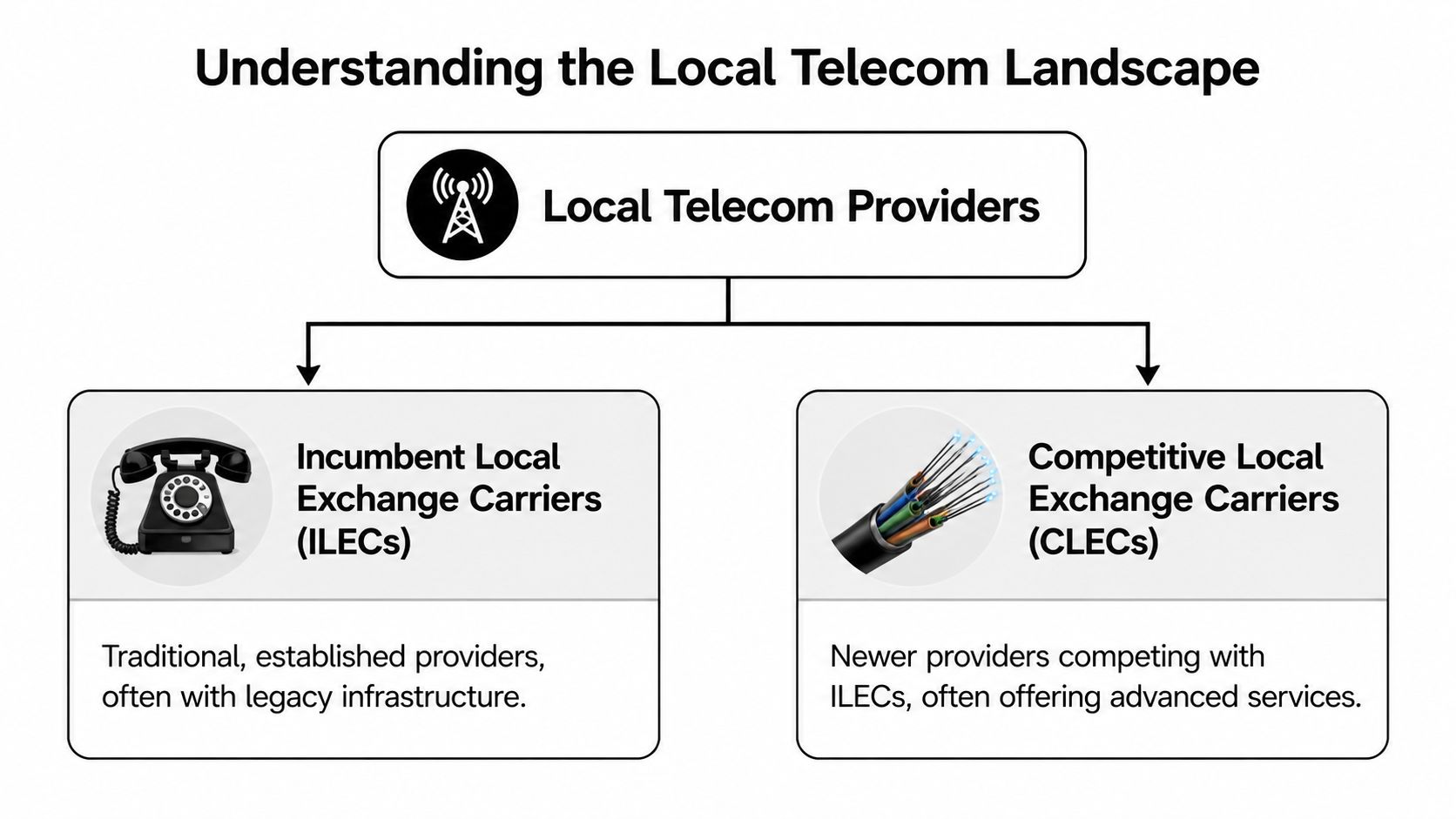
In telecom, that usually means dealing with two broad provider types: incumbent local exchange carriers (ILECs) and competitive local exchange carriers (CLECs). The labels matter less than the operating model behind them.
ILECs and CLECs in practical terms
An ILEC is the traditional established operator in a territory. They often control legacy infrastructure, have long-standing rights of way, and still matter in many buildings where old copper, fiber routes, or local interconnection arrangements shape what’s feasible.
A CLEC is the competitor that entered the market to challenge incumbents. In many metros, CLECs are the ones pushing newer fiber builds, dedicated business services, Ethernet access, SIP, and more flexible commercial packaging.
Here’s the simple distinction IT leaders care about most:
| Provider type | Typical strength | Common concern |
|---|---|---|
| ILEC | Established footprint and existing local plant | Legacy processes and slower change control |
| CLEC | Service flexibility and newer business offerings | Coverage gaps or dependence on leased access |
What local telecom companies actually sell
Too many teams reduce provider evaluation to “internet circuit.” That misses the full service stack.
Most local telecom companies operate across these buckets:
- Data transport: Dedicated fiber internet, broadband, Ethernet, WAN transport, and SD-WAN underlay connectivity.
- Voice services: SIP trunking, hosted PBX, business VoIP, analog line replacement for alarms or elevators where needed.
- Cloud connectivity: Private or more direct access paths into platforms such as AWS and Azure, depending on the provider’s ecosystem and interconnection model.
- Managed edge services: Provider-managed routers, firewalls, session border controllers, and sometimes managed Wi-Fi at branch locations.
- Construction and building entry: Not glamorous, but often a key differentiator if your location needs a new lateral, conduit work, or landlord coordination.
Local telecom development can scale far beyond the “small regional player” stereotype. In the early 2000s, Pakistan Telecommunications Corporation Limited expanded internet access to over 1,707 towns and cities in less than three years, a rollout described as unprecedented in any country’s history, as noted in this PTCL infrastructure expansion reference. That example matters because it shows how local and regional telecom operators can move infrastructure aggressively when policy, market demand, and execution line up.
Why the landscape matters to site planning
If you’re evaluating a building, your telecom options shape the project before the first rack arrives. A site with multiple lit providers is a different risk profile from one with a single incumbent path and unclear construction lead time. That’s why many teams start with a targeted search for a telecommunications company near your location before they finalize facility assumptions.
The provider category matters less than the physical network reality at your address.
How to Find and Verify Telecom Partners in Your Area
Teams often start with a search engine. That’s fine for initial discovery, but it’s a poor way to validate who can serve a site. Telecom sales pages often describe regional capability, not confirmed building serviceability.

A better process starts with the address, the building owner, and the path into the property.
Start with physical availability
Ask each provider four direct questions before you spend time on pricing:
- Is the building on-net, near-net, or off-net?
- Who owns the last mile?
- Does the quoted install require construction or only cross-connect work?
- Can they provide service to the exact suite or only to the building MPOE?
Those answers tell you whether you’re evaluating a real option or a theoretical one.
If you’re building a local provider shortlist, broad discovery tools can still help. A localized search for telecom services near your business sites can surface candidate vendors, but don’t stop there. Validate every claim against building-level facts.
Use people who already know the building
Commercial real estate brokers, landlord facilities managers, and data center operations teams often know more than the provider websites do. They can usually tell you:
- Which carriers are already in the building
- Which providers have struggled with access or install timing
- Whether rooftop, riser, or conduit constraints exist
- Who shows up when there’s a trouble ticket
That kind of intelligence is operationally useful because it comes from installs, outages, and tenant turnover, not marketing.
Verify legitimacy and enterprise readiness
Once a provider looks physically viable, move into verification. I’d check for the basics first, then go deeper during technical review.
| Verification area | What to confirm |
|---|---|
| Legal identity | Registered business details and contract entity name |
| Service model | Whether they operate their own network or resell another carrier |
| Support scope | Business support hours, escalation path, and dispatch model |
| References | Reviews or references from multi-site business customers, not residential users |
If a provider can’t explain where responsibility shifts between their network, their partner’s network, and your handoff, expect friction during outages.
Finally, ask for a sample service order and sample SLA early. You’ll learn more from their paperwork than from the polished discovery call.
Your Evaluation Checklist for Selecting a Provider
Provider comparisons go wrong when teams let sales presentations define the criteria. The cleaner method is to score vendors against a checklist that reflects how your environment runs.
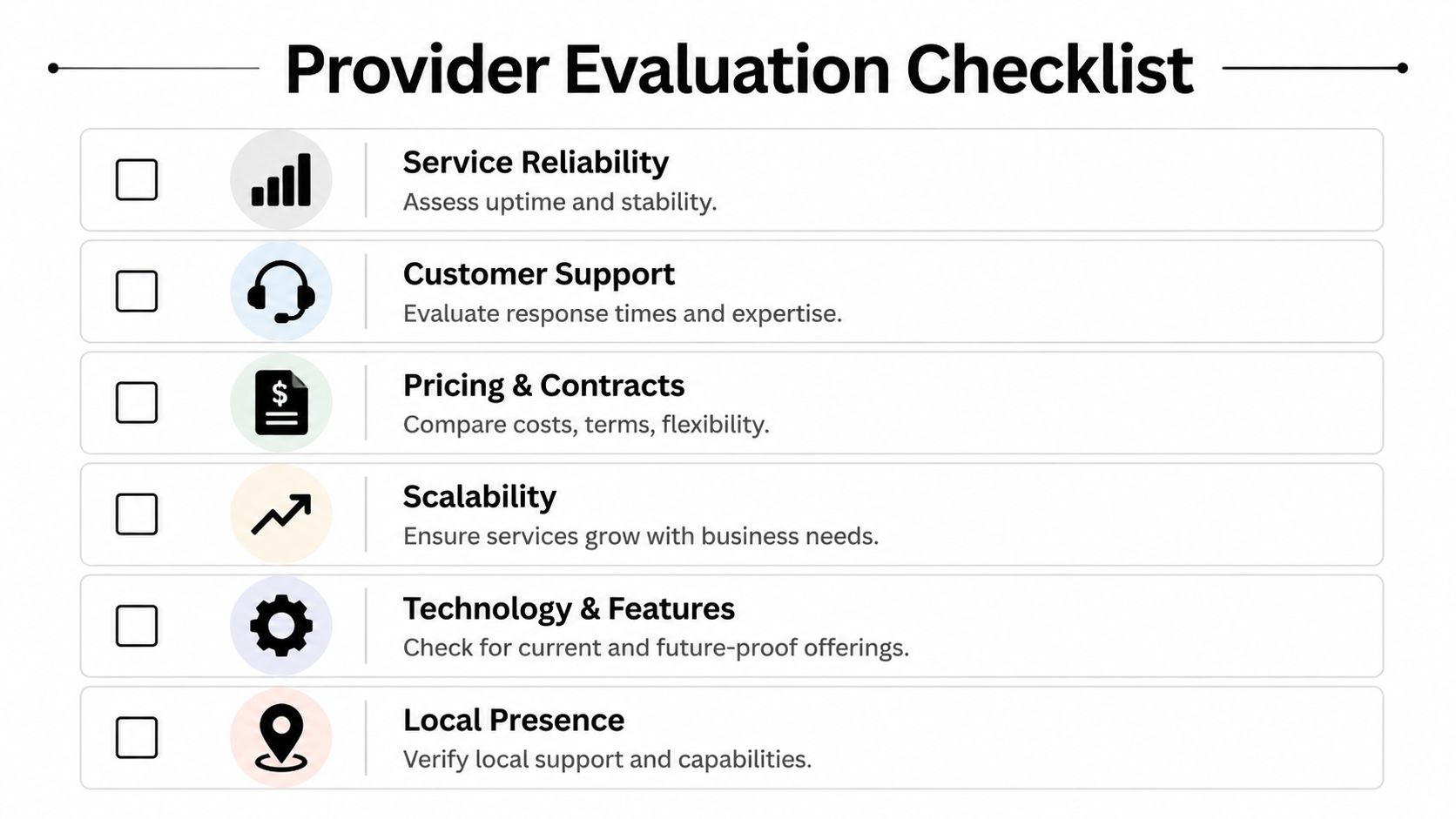
Network quality
Start with performance under normal load and during faults. Ask how they define the service demarc, what monitoring they provide, and how they separate access issues from CPE issues.
Useful questions include:
- Latency path clarity: Is latency measured only on-net, or through the full committed path to the handoff?
- Jitter sensitivity: If you plan to run voice, UC, or real-time apps, how do they troubleshoot jitter versus bandwidth saturation?
- Packet loss handling: What evidence do they provide when you open a performance ticket?
- Maintenance windows: How much notice do they give, and can you request exclusions for critical periods?
If the answers stay vague, the SLA probably will too.
Scalability and service fit
The right provider today can become the wrong one after a merger, cloud migration, or regional expansion. Evaluate how easily they can add bandwidth, turn up additional sites, or shift services without rewriting your architecture.
A few issues matter more than buyers often expect:
- Upgrade path: Can they increase committed capacity without replacing the handoff hardware?
- Multi-site consistency: Can they support branch standards across your footprint, or only at the initial site?
- Cloud alignment: Do they support the connectivity model your network team wants, rather than the one their bundle promotes?
Support and operational maturity
Many local telecom companies differentiate themselves, for better or worse. A highly responsive regional provider can outperform a larger carrier. A thinly staffed one can become a problem fast.
Ask for specifics, not promises:
| Area | Strong answer | Weak answer |
|---|---|---|
| Escalation | Named path from support to engineering | “We’ll take care of it” |
| Local dispatch | Defined process and field coverage | Unclear subcontractor model |
| Change control | Documented maintenance communication | Informal email updates |
| Ticket ownership | Single accountable owner | Repeated handoffs |
Security and asset accountability
Carrier-managed gear often gets the least scrutiny during selection, even though it can create real exposure later. If the provider installs routers, SBCs, wireless controllers, or managed firewalls, ask who patches them, who has administrative access, and who wipes or retrieves them at contract end.
This is also where I’d align telecom review with broader IT asset disposition company requirements. If your organization already enforces chain-of-custody, data destruction, and documented retirement workflows for servers and laptops, telecom gear shouldn’t be exempt just because a carrier installed it.
Don’t evaluate the circuit in isolation. Evaluate the equipment, the support process, and the exit conditions attached to that circuit.
Navigating Telecom Procurement and Contracts
A telecom contract is a risk document disguised as an order form. The install quote gets attention, but the true exposure sits in terms that only matter after there’s a delay, outage, move, or early shutdown.
Clauses that deserve line-by-line review
Start with auto-renewal language. A provider may look flexible during procurement and then lock your team into a renewal window that’s easy to miss. Put a calendar process around notice dates and require procurement to track them alongside lease milestones and infrastructure plans.
Then review termination language with your real estate and infrastructure roadmap in mind. If you’re consolidating sites, planning cloud migrations, or anticipating acquisitions, rigid termination terms can turn a reasonable contract into a stranded-cost problem.
Watch for these issues:
- Auto-renewals: Require explicit review windows and internal reminders.
- Service relocation limits: Some agreements don’t support clean moves to a new site.
- Install contingencies: Clarify what happens if construction cost assumptions change.
- SLA credits: Many look acceptable until you realize the credit process is burdensome and the remedy is narrow.
Negotiate the exit before the install
Experienced buyers protect themselves. Don’t just negotiate recurring rates. Negotiate operational flexibility.
Ask for:
- Clear acceptance criteria before billing starts
- Written definition of demarcation
- Named implementation contacts
- Return and retrieval obligations for provider equipment
- Documented process for disconnect orders and final billing
If your network roadmap includes major relocation or consolidation work, align those terms with your broader data center migration planning. Telecom contracts that ignore migration realities often create duplicate spend, rushed disconnects, or gear left behind in cages and IDFs.
A good telecom deal isn’t the one with the prettiest monthly rate. It’s the one that still works when your environment changes.
Aligning Telecom Contracts with IT Asset Decommissioning
Telecom rarely gets included early enough in decommissioning plans. That’s a mistake. When a branch closes, a cage is vacated, or a provider is replaced, someone has to account for routers, smart hands notes, managed appliances, voice gear, optics, cabling remnants, and whatever was installed without documentation over the life of the circuit.

The risk isn’t just clutter or missed returns. It’s data exposure, chain-of-custody failure, and compliance gaps. Carrier-managed and telecom-adjacent hardware can hold configurations, credentials, call data, routing details, and administrative histories that shouldn’t leave your control untracked.
What gets missed during telecom turn-downs
Teams usually remember the obvious assets. They often miss the small ones.
Common trouble spots include:
- Provider CPE mixed with customer-owned gear
- Old voice appliances left in telecom closets
- Failover routers and LTE backup devices
- Remote management modules embedded in edge equipment
- Disconnected gear staged for “later pickup” that nobody owns
That’s why decommissioning should begin with a joint asset register. Facilities, network engineering, procurement, and the disposition team all need to agree on ownership and removal responsibility before the disconnect date.
Why telecom gear needs specialized retirement
Some telecom hardware carries extra sensitivity because of licensed technology and embedded components. According to this SAMENA Council telecom handling reference, routers and base stations using licensed technology such as Qualcomm should undergo NAID AAA-certified destruction to prevent data leaks. The same source notes that a proper ITAD process supports compliance with R2/RIOS, preserves a clear audit trail, and can maximize reuse value for components.
That has two practical implications for IT leaders.
First, your telecom contract should define who retrieves provider-owned hardware and how that retrieval is documented.
Second, your internal decommissioning process should treat telecom gear like any other regulated or security-relevant asset. If it stores data, credentials, logs, or configuration state, it needs documented handling.
Retired network gear becomes a security problem the moment ownership, custody, or destruction records get fuzzy.
A coordinated workflow that works
The most reliable model ties provider offboarding to your decommission checklist:
| Phase | What the team should do |
|---|---|
| Pre-disconnect | Inventory telecom and edge devices by owner and location |
| Disconnect planning | Confirm removal dates, access rules, and shipping custody |
| Data protection | Route applicable devices into certified destruction or approved ITAD workflows |
| Final reconciliation | Match removed assets to tickets, manifests, and provider closure records |
For larger shutdowns, that process should sit inside the broader data center decommissioning process, not operate as an afterthought. Telecom is part of infrastructure retirement, not a side task for whoever still has the provider rep’s phone number.
Conclusion Building a Strategic Telecom Partnership
The strongest telecom decisions start before procurement and continue after service termination. That’s the mindset shift many IT teams need. Local telecom companies can be excellent partners when they combine local network knowledge with enterprise-grade support, clear contracts, and disciplined asset handling.
A good selection process looks beyond bandwidth and monthly charges. It checks the physical network reality, tests operational maturity, and forces clarity around support, ownership, and end-of-term obligations. That’s how you avoid the common pattern of buying cleanly and exiting poorly.
The overlooked advantage comes from connecting telecom management to asset lifecycle management. When provider selection, contract review, and decommission planning work together, you reduce service risk, tighten security, and keep audits simpler.
Telecom shouldn’t be treated as a one-time service purchase. It’s an infrastructure relationship with operational, contractual, and disposal consequences. Handle it that way, and the partnership becomes far more useful to the business.
Frequently Asked Questions About Local Telecom
Below are the questions IT teams ask most often once they move past the initial quote stage.
| Question | Answer |
|---|---|
| Should I choose a local provider over a national carrier? | Choose the provider that has the best fit for the site, support model, and contract terms. Local providers often do better when regional responsiveness and building familiarity matter. National carriers may fit better for very broad geographic standardization. |
| What’s the first technical question to ask a provider? | Ask whether the site is on-net, near-net, or off-net. That tells you whether the quote reflects existing access or a build that could change cost and timing. |
| How do I verify that a provider really serves my building? | Ask for building-level serviceability, suite-level availability, demarc details, and whether construction is required. Then confirm with the landlord, broker, or facility operator. |
| Are managed routers and firewalls a convenience or a risk? | They can be both. Managed equipment can simplify support, but only if the contract defines patching, access control, replacement, logging responsibility, and end-of-term retrieval. |
| What usually causes telecom projects to slip? | Building access issues, construction surprises, vague demarc assumptions, landlord coordination, and unclear ownership between reseller and underlying carrier. |
| Should procurement own the whole process? | No. Procurement should control commercial terms, but network engineering, security, facilities, and whoever handles asset retirement all need input before signature. |
| What should I document before disconnecting service? | Document asset ownership, device locations, provider retrieval obligations, local contact access, final billing triggers, and the path for data destruction or compliant disposition. |
| When should ITAD planning start for telecom hardware? | Early. If a site closure or provider transition is on the roadmap, include telecom equipment in the decommission plan before disconnect dates are locked. |
If you need a partner to handle the retirement side of network and infrastructure projects, Dallas Fortworth Computer Recycling supports organizations that need secure, compliant IT asset disposition, data destruction, and decommissioning workflows. For IT leaders managing site closures, carrier transitions, and infrastructure refreshes, that kind of documented chain-of-custody can make the final phase of a telecom project as controlled as the first.
