Secure Electronics Recycling Certification

Most IT directors know the scene. A locked room or caged corner near the server area slowly fills with retired laptops, failed drives, switches, access points, monitors, and a few mystery boxes no one wants to touch. The equipment is off the network, so it feels handled. It isn't.
Every one of those assets carries risk. Some still hold data. Some contain hazardous components that can't be tossed into general waste. Some belong to departments that need a documented chain of custody, not a casual pickup and a vague promise. If your team is juggling refresh cycles, lease returns, storage pressure, and compliance reviews at the same time, that pile stops being surplus and starts being exposure.
I've seen organizations treat this as a facilities issue. It rarely is. It's a security issue, a procurement issue, a compliance issue, and sometimes a board-level reputation issue. The danger isn't only what happens inside your building. It's what happens after the truck leaves.
That is why electronics recycling certification matters. Certification is the difference between "they say they recycle responsibly" and "they can prove their process survives audit scrutiny." If you're already reviewing options for electronics destruction services, the certification question should come before pricing, not after it.
The Hidden Risks in Your IT Storage Closet
A storage closet full of decommissioned hardware doesn't look dramatic. It looks annoying. That's why it gets deprioritized.
A few shelves hold old laptops from onboarding changes. A pallet has network gear pulled during a site upgrade. In the corner, there are servers from the last virtualization project, each one removed from production but not fully documented for disposition. Nobody feels urgency because the devices aren't active anymore.
That assumption causes problems.
A retired system can still expose customer records, credentials, cached files, email archives, or protected health information if the drive was never sanitized correctly. A recycler can also create environmental liability if they don't control downstream vendors, don't document handoffs, or can't prove where hazardous material went. The equipment may be gone from your premises and still remain your risk.
Practical rule: If an asset held data in production, treat it like sensitive media until you have documented proof of sanitization or destruction.
The other hidden problem is organizational drift. IT thinks procurement approved the recycler. Procurement thinks legal reviewed the terms. Facilities schedules the pickup. Security assumes certificates will follow. Then an auditor asks for evidence six months later, and the paperwork doesn't line up with the actual serial numbers removed.
What works is a formal disposition path with verified controls. What doesn't work is choosing a vendor because they offered free pickup, same-day loading, or a reassuring sales deck.
Electronics recycling certification gives you a starting framework for control. It doesn't replace due diligence, but it tells you whether the recycler has been evaluated against defined environmental, operational, and security standards. For a risk-conscious IT director, that's the baseline.
Understanding the Certification Landscape
Think of certifications the way you think about building codes. A finished building might look impressive from the street, but what matters is whether the structure was designed, inspected, and maintained to a recognized standard. Recycling vendors are similar. A polished website means very little. The process behind it matters.
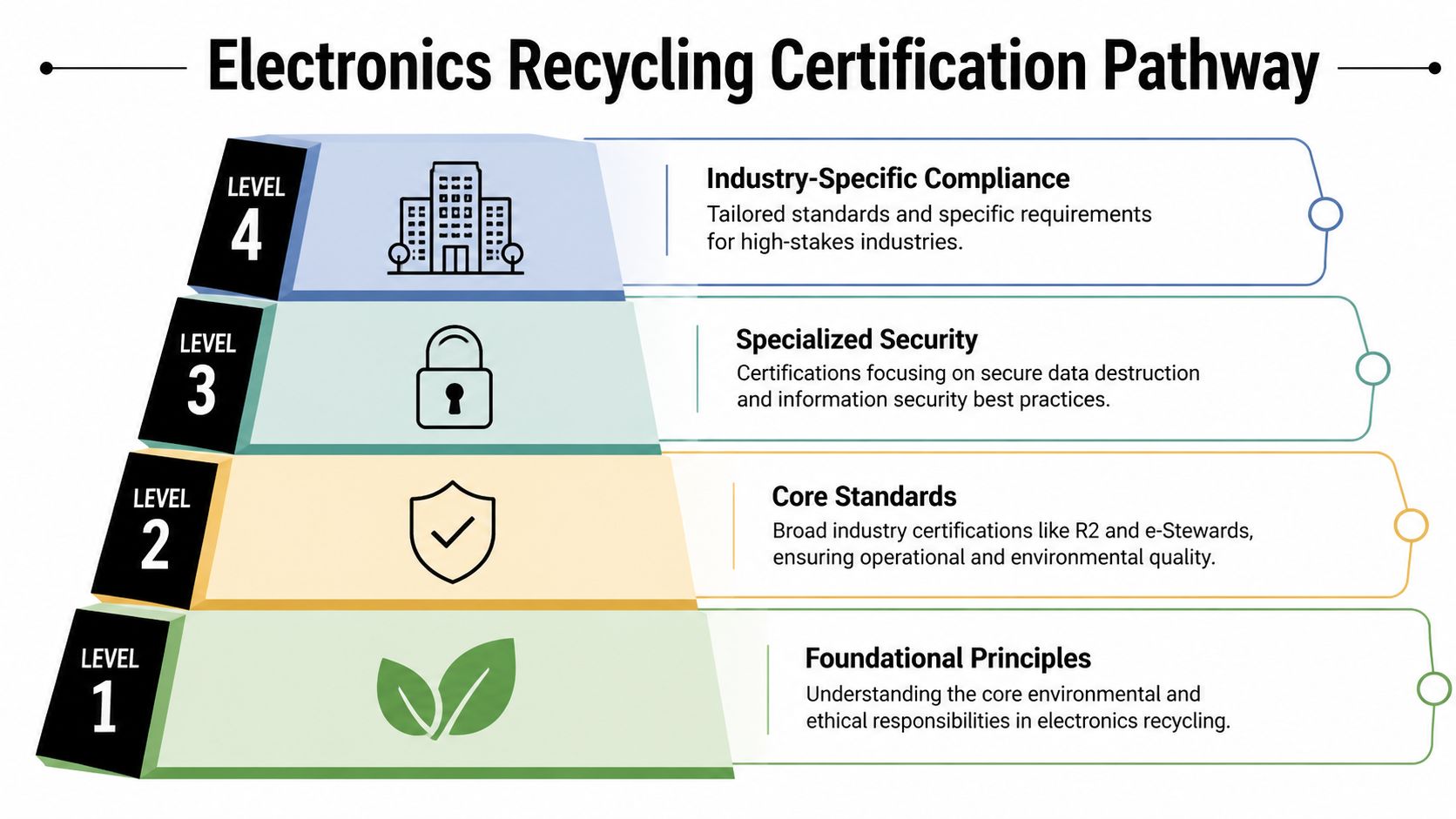
A solid electronics recycling certification framework usually answers three separate questions:
Environmental stewardship
Can the recycler prove they manage hazardous materials responsibly, avoid improper disposal, and control what happens after initial processing? For these reasons, standards such as R2 and e-Stewards matter most. They aren't marketing labels. They are operating disciplines.
If your team is comparing providers, start with an R2 certified electronics recycler and then test whether the certification scope matches the services you're buying.
Data security
Can they protect information from pickup through final disposition? This includes chain of custody, media handling, destruction methods, and records you can defend in an audit. A recycler may be environmentally competent and still weak on data handling. That gap shows up fast when you ask for sample reporting.
Operational integrity
Can they run a controlled process repeatedly, safely, and legally? That means documented workflows, worker protection, downstream oversight, and evidence that audits are part of normal operations, not a once-a-year scramble.
Certifications are useful only when they change behavior on the floor, in the truck, in the warehouse, and in the reporting package you receive afterward.
A common mistake is to ask, "Which certification is best?" The better question is, "Which certification proves the controls my organization can't afford to get wrong?" A data center may focus on serialized chain of custody at scale. A hospital may focus on media destruction tied to regulated records. A government agency may care about documented handling discipline and traceability above all else.
That is the mental model worth keeping. Certifications aren't there to impress procurement. They exist to verify that critical controls are in place before your assets leave your custody.
Core Certifications for Environmental and Operational Excellence
Environmental credentials matter only if they show up in day-to-day controls. An IT director is not buying a logo. You are buying proof that equipment will be received, sorted, stored, processed, and sent downstream under rules that hold up when legal, compliance, or procurement asks for records months later.

Three certifications usually drive that discussion: R2v3, e-Stewards, and ISO 14001. They overlap, but they answer different risk questions. That distinction matters during vendor review because a hospital, colocation operator, and public agency will not weigh the same evidence the same way.
What R2v3 proves
R2v3 is the broad operational standard many ITAD buyers start with because it covers the actual mechanics of running a controlled electronics recycling operation. As noted in Cumulus Sustainability Group's summary of e-waste certifications, R2v3 spans a wide set of performance areas across environmental controls, worker safety, quality practices, data handling, and downstream due diligence.
That breadth is useful if you need one certification to tell you whether the facility runs on documented process instead of tribal knowledge. In practice, good R2v3 operators can explain how material moves from dock intake to final disposition without hand-waving. They can show how they isolate exceptions, how they track nonconforming loads, and how they approve downstream vendors before anything leaves their control.
For a data center or large enterprise refresh, that matters because volume exposes weak process fast. A recycler with R2v3 should be able to show repeatable workflows, not just good intentions.
What e-Stewards proves
e-Stewards tends to matter most when your organization is sensitive to downstream ethics, export exposure, and public scrutiny. Its value is less about broad operational coverage and more about where it draws hard lines.
The clearest example is export control. e-Stewards is known for stricter restrictions on hazardous e-waste exports to developing countries. For organizations with ESG commitments, board visibility, or taxpayer accountability, that narrower tolerance for downstream risk can be the deciding factor.
That does not automatically make e-Stewards "better" than R2v3. It makes it a stronger fit in specific contexts. If reputational risk from downstream handling is high, tighter restrictions may be worth the reduced flexibility.
Where ISO 14001 fits
ISO 14001 serves a different purpose. It is an environmental management system standard, not an ITAD-specific recycling standard.
That means ISO 14001 helps you assess whether a provider runs environmental compliance through documented procedures, corrective action, and periodic review. It does not, by itself, answer the electronics-specific questions an IT director should ask about reuse decisions, downstream qualification, or media-bearing device handling.
I usually treat ISO 14001 as supporting evidence. It strengthens confidence that environmental controls are managed intentionally. It should not be the only credential behind an IT equipment recycling program.
Comparison of Key Electronics Recycling Certifications
| Certification | Primary Focus | Data Security Mandate | Export Rules |
|---|---|---|---|
| R2v3 | Electronics recycling controls across environmental, operational, health, safety, quality, and downstream accountability | Includes documented data security controls and chain of custody requirements | Managed through downstream due diligence and related standard requirements |
| e-Stewards | Ethical downstream management, strict environmental handling, and stronger export restrictions | Includes specific data handling requirements tied to the standard | Absolute ban on exporting hazardous e-waste to developing nations |
| ISO 14001 | Environmental management system discipline | Not an ITAD-specific data destruction standard | Not an e-waste-specific export standard |
What works in vendor review
The practical question is not, "Do they have a certification?" It is, "Does this certification line up with the failure points my organization cares about?"
Use that lens when you review evidence:
- Match the certificate to the site. The certified location should be the facility receiving or processing your assets, not a parent company office or another branch.
- Check the service scope. If the vendor is offering logistics, triage, resale, destruction, or downstream processing, the certification should cover those activities.
- Ask how environmental controls show up on the floor. Good vendors can explain battery segregation, hazardous material handling, and storage rules without reading from a brochure.
- Review downstream discipline. You want a clear answer on who receives material next, how they were qualified, and how performance is reviewed.
- Look for audit maturity. Strong operators can discuss findings, corrective actions, and surveillance audits in plain language because they manage to those standards every week.
A certification logo starts the conversation. The records behind it tell you whether the operation is actually under control.
In real vendor selection, R2v3 often fits buyers who need broad process assurance across mixed asset streams. e-Stewards often fits buyers who need tighter downstream restrictions and stronger protection against reputational fallout. ISO 14001 adds confidence that environmental controls are managed systematically. The right mix depends on the risks your industry cannot afford to explain after the fact.
Specialized Certifications for Data Security and Compliance
A recycler can run a tidy operation and still create a reportable data incident.
That is the dividing line for this part of the review. Environmental certifications tell you whether the company controls waste handling. Data security credentials tell you whether they can take custody of storage media, process it under documented controls, and give your team evidence that stands up in an audit, an investigation, or a board briefing.

Full destruction versus vague sanitization claims
“We wipe everything” is not a security program. It is a sales line until the vendor shows method, decision criteria, exception handling, and records.
For an IT director, the practical question is simple. Which assets are sanitized, which are shredded, and who makes that call? A good provider can explain the difference between reusable media, failed drives, encrypted devices with uncertain key status, and equipment with embedded storage that cannot be reliably sanitized in place. They should also explain what evidence you receive for each outcome.
e-Stewards often comes up here because buyers use it as a signal that downstream controls and data-bearing device handling are taken seriously. The point is not the logo by itself. The point is whether the recycler can show a disciplined process for media destruction, tracking, and release of material after data risk has been addressed.
NAID AAA and SOC 2 in practical review
NAID AAA is useful if your concern is controlled destruction of data-bearing media. It gives procurement and compliance teams a focused way to ask better questions about chain of custody, operator practices, access control, and destruction procedures. In practice, I treat it as one piece of evidence, not the whole answer. If the vendor advertises NAID AAA, ask whether the certified scope covers the devices and service model you are buying, including offsite pickup, onsite destruction, or both.
SOC 2 answers a different question. It is not an electronics recycling standard, and it does not tell you whether the company manages downstream material correctly. What it can show is whether the organization has audited controls around security, availability, and related internal processes. That matters more for providers that give clients portal access, asset reporting, serialized reconciliation, or integration with internal ticketing and disposition systems.
The trade-off is straightforward. NAID AAA is narrower and closer to the destruction event. SOC 2 is broader and often more useful for vendor risk teams reviewing overall control maturity.
HIPAA capability is not a logo
Healthcare buyers often ask whether a recycler is “HIPAA certified.” There is no single certification that settles that question.
Hospitals and clinics need proof that the provider can receive devices containing ePHI, protect them during pickup and processing, and produce records that match the assets removed from service. That usually means Business Associate Agreement readiness, trained handling for devices with embedded storage, and exception procedures for equipment that arrives damaged, locked, or incomplete.
If your team is reviewing secure data destruction services for retired IT assets, ask for sample chain-of-custody forms, serialized destruction records, and a certificate format tied to actual assets or containers. Generic service summaries are not enough for a healthcare audit.
Government and defense-adjacent buyers should push even harder on this point. They need to know whether the vendor can follow contract-specific destruction rules, isolate restricted assets, and document custody by lot, pallet, or serial number, depending on the requirement. Data centers usually care more about throughput and consistency at scale. Hospitals care more about exceptions, mixed device types, and documentation tied to regulated workflows.
The real test is how the vendor handles the assets that do not fit the normal process.
That is where weak controls show up. Failed SSDs. RAID members pulled without labels. Copiers, lab devices, and network gear with storage nobody identified during pickup planning. Strong providers have written decision trees, supervisor review, and records for those cases. Weak providers improvise, and that is where security claims collapse.
How to Verify a Recycler's Certifications and Audit Evidence
The easiest mistake in vendor selection is believing the badge on the website. Verification starts where marketing ends.
A recycler may say they are certified, audited, compliant, secure, and transparent. Fine. Ask them to prove each point with documents that match the facility, service scope, and timeline involved in your project.
Start with the certificate itself
Request the actual certificate, not a screenshot of a logo page. Then review the basics closely:
Legal entity name
The company name on the certificate should match the contracting party.Facility address
Certifications are often site-specific. The pickup team may work under one brand while processing happens at another location.Scope and standard version
Check whether the certified scope covers electronics recycling, data-bearing devices, refurbishing, or specialized handling relevant to your assets.Effective and expiration dates
An expired certificate is not a minor paperwork issue. It means the assurance window has closed.
If you're collecting media disposal evidence already, ask for a sample certificate of destruction for hard drives. It will show you quickly whether the provider's documentation is detailed enough for audit use.
Ask for audit-adjacent evidence
Most recyclers won't hand over full audit files, and that's reasonable. You can still ask for evidence that shows the process is real.
Useful requests include:
- Redacted audit summaries: These can show findings, closure status, and surveillance cadence.
- Sample chain-of-custody forms: You want to see timestamps, signatures, asset counts, and exception notation.
- Downstream due diligence summaries: This tells you whether they vet where material goes after initial processing.
- Data destruction records: Ask how serials, asset tags, and destroyed media are reconciled.
Test the operational story
After reviewing documents, talk through a realistic scenario with the vendor. Don't ask broad questions like "Are you secure?" Ask pointed ones.
Try prompts like these:
- A pallet arrives with mismatched asset counts. What happens next?
- A drive fails sanitization. Do you destroy it automatically, quarantine it, or escalate approval?
- A device contains embedded storage that wasn't disclosed. How is that documented?
- A downstream partner changes. Who approves it, and how do you update customers if needed?
Good vendors answer these questions with process language. Weak vendors answer them with reassurance.
What good looks like
A verified recycler doesn't get irritated when you ask for evidence. They expect it. They can explain the standard they hold, the site where work occurs, the controls attached to your asset type, and the records you will receive after service.
What doesn't work is a procurement process that accepts "R2 certified" or "HIPAA compliant" without checking dates, scope, and documentation flow. Build verification into onboarding. Put it in the vendor file. Review it again when the contract renews.
That approach takes more effort upfront, but it's far cheaper than reconstructing evidence after an incident, an internal audit, or a regulator's request.
A Vetting Checklist for Selecting Your ITAD Partner
Most vendor evaluations fail for a simple reason. They treat IT asset disposition like a hauling service instead of a control-heavy business process.
The right checklist fixes that. It helps IT, procurement, legal, security, and compliance score the same provider against the same expectations.
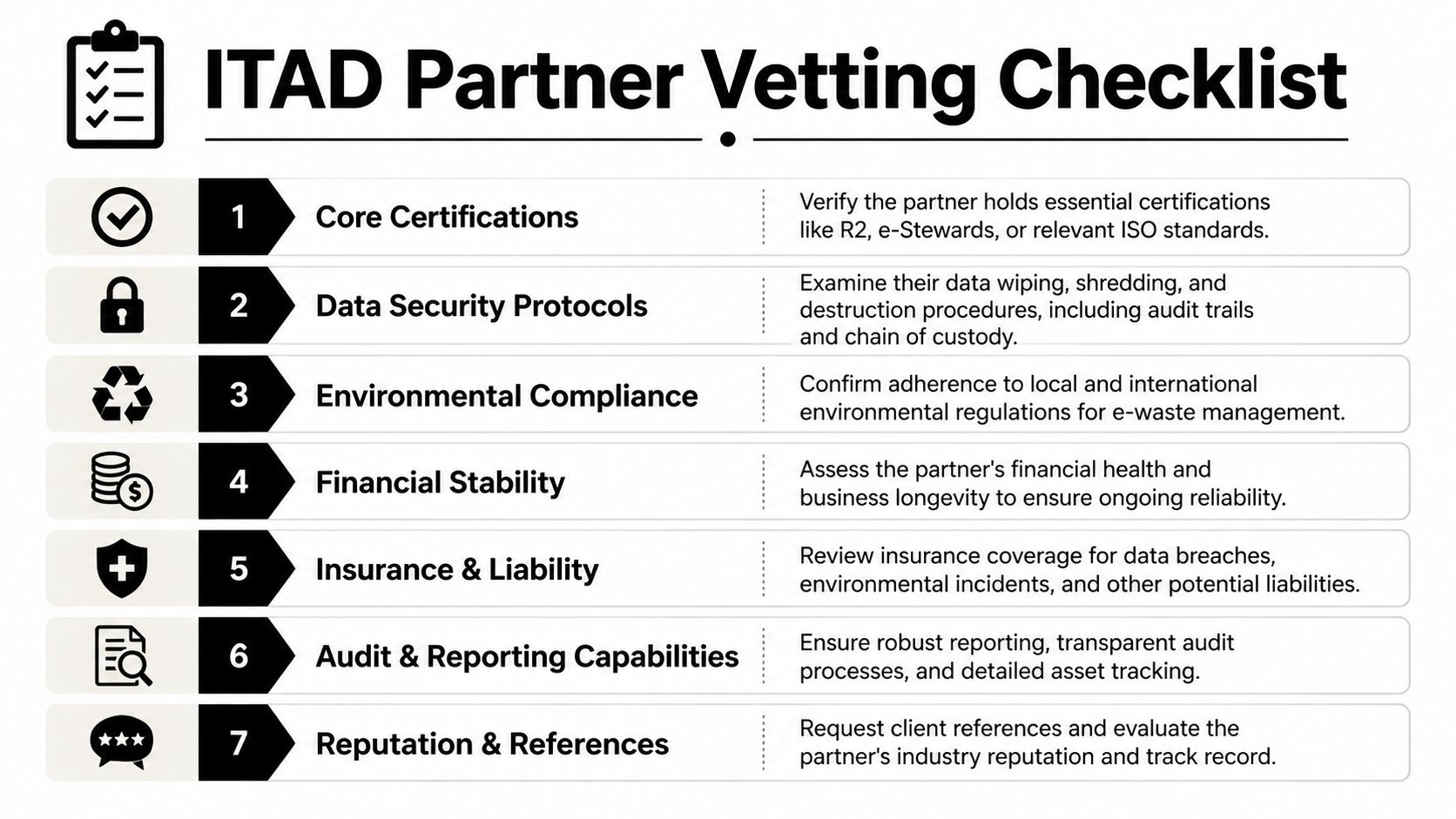
Seven areas to score
Corporate standing
Confirm the legal entity, operating history, facility locations, and permits relevant to the work, as contracts and certificates are only useful if they point to the same operating business.Core certifications
Verify active R2v3, e-Stewards, ISO 14001, or other relevant credentials based on your risk profile, as certification narrows the field to vendors with externally reviewed controls.Data destruction controls
Require clear media handling procedures, NIST 800-88 alignment where sanitization is used, and physical destruction procedures where needed, as "sanitized" is not defensible unless the method and result are documented.Chain of custody
Review how assets are counted, sealed, transported, received, reconciled, and reported, as most disputes come from handoff gaps, not from the final report.Downstream transparency
Ask how subcontractors and downstream processors are approved and monitored, as your liability doesn't end at the first processor.Insurance and liability terms
Review coverage for data incidents, environmental events, and operational losses. Doing so ensures your contract addresses what happens when a control fails.Reporting and audit support
Ask for sample inventory reports, destruction certificates, exception logs, and project closeout packages. The quality of this evidence is essential for the reliability of your internal audit trail.
What to put in the RFP
A useful RFP doesn't ask, "Are you certified?" It asks for proof and operational detail.
Include requirements such as:
- Current certificates with dates and facility scope
- Sample reporting package for a completed project
- Description of failed media handling
- Explanation of downstream due diligence
- Escalation path for discrepancies and incidents
What to avoid
Some warning signs show up early:
- Pricing without process detail
- Generic compliance language copied across proposals
- No sample documentation
- Reluctance to discuss exceptions
- A polished sales team but no operations contact during diligence
A good electronics recycling certification review is never just about whether the vendor has one document. It is about whether the document matches a real, repeatable process you can inspect before your assets move.
Vetting Strategies for Data Centers Healthcare and Government
A recycler can look qualified on paper and still fail your project in ways that are specific to your industry. A data center loses control during a high-volume decommission. A hospital misses embedded storage in a device category nobody tagged as data-bearing. A public agency gets through pickup day, then struggles to defend the records months later under review.

The vetting standard should change with those risks. Good looks different in each environment, and the proof you ask for should reflect that.
Data centers need proof that controls hold under volume
Data center projects fail when process discipline breaks under speed. Hundreds or thousands of assets can move in a narrow maintenance window, often with multiple technicians, staged pallets, partial rack removals, and last-minute scope changes. A vendor that handles office cleanouts well may still lose control in this setting.
Ask for evidence from a comparable decommissioning job, not a generic capability statement. Review sample rack-level or asset-level reconciliation, exception logs, and the procedure for assets that show up without readable labels or with serial numbers that do not match the manifest. If the vendor offers on-site drive destruction, verify who witnesses it, how destroyed media is reconciled back to the source inventory, and what record closes that loop.
R2v3 is often a useful baseline here because it points you toward process control. The audit question is more specific. Can the operator prove consistent custody during a high-throughput project without gaps between removal, transport, destruction, and final reporting?
Healthcare needs device-level awareness, not just media destruction claims
Healthcare environments create a different problem. The risk is often hidden inside mixed asset streams that include carts, imaging systems, analyzers, printers, tablets, nurse station hardware, and specialty equipment with storage that is easy to miss.
I have seen hospital teams focus on laptops and servers while a copier hard drive or diagnostic device creates significant exposure. Vetting should test whether the recycler can identify likely data-bearing equipment before pickup, segregate those assets correctly, and document the sanitization or destruction decision for each category. Ask the operations team, not only sales, how they identify embedded media in biomedical and clinical support devices.
Business Associate Agreement readiness matters, but it is only one checkpoint. The stronger indicator is whether the vendor can show a written intake and triage method for equipment that may contain ePHI, including how uncertain cases are escalated and who signs off on the final handling decision.
e-Stewards can be helpful for healthcare organizations that want a stricter downstream posture, especially if leadership is sensitive to export, landfill, and reputational risk. The practical question is still the same. Ask what that certification changes in day-to-day handling for your asset mix, and request examples from prior healthcare projects.
In healthcare, the riskiest device is often the one nobody recognized as data-bearing until it reached the loading dock.
Government needs records that stand up after the project ends
Government buyers usually need more than clean pickup and a certificate at closeout. They need a file that survives procurement review, inspector scrutiny, legal hold, public records requests, or questions from leadership long after the equipment left the building.
That changes the vetting process. Review whether the vendor's documentation is clear enough for a third party to follow without interpretation. Dates, quantities, serials, locations, custody transfers, exception notes, and destruction outcomes should line up across the entire record set. If they do not, the problem shows up later, when your team has less influence and fewer facts.
Personnel controls also deserve closer review in public-sector work. Ask which facilities will process the material, whether any subcontracted transportation or consolidation is involved, and how those handoffs appear in the documentation. Government agencies often prefer vendors that can produce consistent records across every touchpoint because public accountability is harder to manage after a mistake becomes visible.
What good looks like by sector
| Industry | What to verify | What strong evidence looks like |
|---|---|---|
| Data center | High-volume custody control, reconciliation discipline, exception handling during decommissioning | Sample project file with serialized reconciliation, loadout discrepancies, and documented media disposition tied back to inventory |
| Healthcare | Identification of embedded storage, handling of mixed clinical assets, documented ePHI decision paths | Asset-category handling matrix, written sanitization or destruction methods, BAA readiness, and examples involving medical or lab equipment |
| Government | Inspection-ready records, facility and personnel traceability, defensible subcontractor controls | Complete closeout package with aligned dates and serials, custody transfers, destruction records, and documentation that can withstand formal review |
A generic questionnaire misses these differences. A better vetting approach tests the recycler against the failure pattern your sector is most likely to face, then asks for proof from similar work. That is how an IT director separates a certified vendor from an operator who can protect the organization.
Choosing a Partner Not Just a Processor
The safest ITAD decisions come from a simple shift in mindset. You are not hiring someone to remove old equipment. You are selecting a partner to reduce operational, security, and environmental risk.
That is why electronics recycling certification matters so much. It gives you a structured way to separate disciplined operators from vendors that mainly sell convenience. It also gives your team something concrete to verify: certificate scope, audit evidence, chain-of-custody records, and data destruction documentation.
The strongest programs don't stop at certification. They match the vendor's controls to the organization's actual exposure. A data center needs one level of proof. A hospital needs another. A public agency may need even tighter documentation. The work is not done when you see a logo. It's done when the evidence package supports your internal requirements.
One certification point is worth keeping in view at the close. R2v3 requires an ISO 14001-certified Environmental Management System and prohibits landfilling hazardous e-waste. For IT directors, it also translates into chain-of-custody documentation and NIST 800-88 data destruction methods, with verified sanitization described as reducing breach risks by 99.9%, according to United Electronic Recycling's overview of certifications. That combination captures the broader point. Good certification isn't bureaucracy. It is risk control you can inspect.
Choose the vendor that makes your legal team calmer, your security team more confident, and your audit trail easier to defend. That is a partner. A processor just picks up boxes.
Dallas Fortworth Computer Recycling helps organizations retire technology with the controls risk-conscious IT teams expect. If you need a nationwide ITAD partner for secure pickups, documented chain of custody, certified data destruction, data center decommissioning, or responsible recycling of standard and specialized equipment, visit Dallas Fortworth Computer Recycling to discuss your project.
