A Complete Guide to Secure Data Destruction Services
Secure data destruction services are your guarantee that sensitive information on old hard drives, SSDs, and servers is made completely unrecoverable. It’s the final, and most critical, step in the IT asset lifecycle—the one that ensures retired equipment doesn't come back to haunt you as a future liability. This is worlds away from simply deleting files, a process that often leaves data just beneath the surface, waiting to be retrieved.
Why Secure Data Destruction Is Non-Negotiable

Think about your company's most sensitive paper documents. You wouldn't just toss old contracts or employee records into a public recycling bin. You’d run them through a high-security, cross-cut shredder that turns them into indecipherable confetti. Secure data destruction applies that exact same logic to your digital assets.
This isn’t just a cleanup task; it's a core function of modern risk management. Every retired hard drive, server, or company phone holds a ghost of its former life—customer lists, financial records, proprietary research, and PII. Failing to properly destroy that data is like moving to a new office and leaving the vault door wide open.
The High Stakes of Inaction
The consequences of getting this wrong can be devastating. A single improperly discarded hard drive can trigger a catastrophic data breach, exposing your organization to massive financial and reputational damage. The average cost of a breach just keeps climbing, putting a heavy burden on businesses of all sizes.
Beyond the immediate financial hit, the fallout is severe:
- Crippling Regulatory Fines: Laws like HIPAA, GDPR, and FACTA don't just recommend secure data disposal—they mandate it. Violations can lead to fines stretching into the millions.
- Loss of Customer Trust: A public data breach shatters customer confidence. Rebuilding that trust can take years, if it can be rebuilt at all.
- Competitive Disadvantage: If your trade secrets or proprietary research fall into the hands of a competitor, the damage to your market position could be permanent.
In essence, professional data destruction is an investment in business continuity. It provides a verifiable, auditable process that proves you have taken every necessary step to protect confidential information at the end of its life.
Shifting from Liability to Security
It’s time for a critical mindset shift: see old IT equipment as a potential liability, not just clutter. Each device represents a potential entry point for malicious actors if you don't handle it correctly.
Partnering with professional secure data destruction services transforms this risk into a controlled, documented, and secure final step. It’s a proactive approach that turns a potential vulnerability into a fortified defense—and for any organization handling confidential data, it's absolutely essential.
Choosing Your Method: Onsite vs. Offsite Destruction
One of the first calls you'll have to make when arranging for secure data destruction is deciding where it happens. Will the destruction equipment come to you, or will your assets be transported to a secure facility? This choice between onsite and offsite services is a big one, directly shaping your security posture, logistics, and budget.
Both methods get you to the same end goal—permanent data erasure—but they take different routes. Understanding the workflow for each is key to matching the service with your organization's risk tolerance. The decision really boils down to a simple question: do you need to see it happen with your own eyes, or are you comfortable with a highly documented, audited process managed by a trusted partner?
Onsite Destruction: The Fortress Comes to You
Onsite destruction is exactly what it sounds like. Your vendor brings the destruction equipment—typically a specialized, industrial-grade shredding truck—directly to your office, data center, or warehouse. You're bringing a mobile security operation right to your doorstep.
This approach gives you the ultimate in transparency and control, which is why it's the go-to choice for organizations with the strictest security mandates, like government agencies, banks, and healthcare providers.
- Maximum Oversight: You can physically watch every single hard drive, server, or backup tape get fed into the shredder. There's zero doubt about the outcome.
- Immediate Verification: The job is done on your property, giving you instant peace of mind and making your internal audit trail incredibly simple.
- Reduced Transport Risk: Since data-bearing devices never leave your premises intact, the risk of them getting lost or stolen in transit is completely eliminated.
For many IT leaders, being able to personally verify that their data has been physically destroyed is non-negotiable. If that sounds like you, it’s worth exploring local, high-security onsite shredding services that can meet these tough requirements.
Offsite Destruction: The Secure Courier Model
With offsite destruction, your assets are securely transported to a specialized facility to be destroyed. Think of it as the "secure courier" model. The process starts at your location, where a technician inventories and serializes every asset you're getting rid of.
From there, the devices are locked in tamper-evident containers, loaded onto a secure, GPS-tracked vehicle, and driven to a certified destruction plant. The entire journey is governed by a strict chain of custody—a documented paper trail that tracks your assets from the moment they leave your control until they are finally destroyed.
You don't witness the shredding firsthand, but you receive something just as important: a detailed Certificate of Destruction. This legal document confirms the date, the method used, and provides a full list of serialized assets that were destroyed, giving you the auditable proof you need for compliance.
The trust in certified, offsite processes is a major reason the secure data destruction market is booming. Valued at USD 4.4 billion in 2025, it's expected to more than double to USD 10.3 billion by 2034. That growth is fueled by the unfortunate rise in cybercrime and the stringent enforcement of privacy laws like GDPR and HIPAA.
So, how do you decide which is right for you? This table breaks down the key differences.
Comparing Onsite and Offsite Data Destruction
| Feature | Onsite Destruction | Offsite Destruction |
|---|---|---|
| Location | At your facility; mobile shred truck arrives on-site. | At a secure, specialized vendor facility. |
| Security | Highest level; assets never leave your premises intact. | High level; secured by chain-of-custody protocols. |
| Oversight | Direct visual verification of the entire process. | Verification through documentation (e.g., Certificates of Destruction). |
| Logistics | Requires scheduling and physical space for the truck. | Simpler logistics; vendor handles all transport. |
| Cost | Generally higher due to mobilization and labor costs. | Typically more cost-effective, especially for larger volumes. |
| Best For | Highly regulated industries; maximum risk aversion. | Cost-conscious organizations; routine asset retirement. |
Ultimately, choosing between these two secure data destruction services is a balancing act between direct oversight and logistical efficiency. Onsite gives you absolute visual confirmation, while offsite provides a highly secure, convenient, and cost-effective alternative that is backed by ironclad, auditable documentation.
Understanding Data Destruction Techniques
Once you've decided between on-site or off-site service, the next big question is how the data actually gets destroyed. Not all methods are the same, and the right choice comes down to the type of media you're retiring and what you plan to do with the device afterward. Think of it as choosing the right tool for the job—you wouldn't use a sledgehammer to remove a screw.
Professional secure data destruction services really boil down to three core techniques: software wiping, degaussing, and good old-fashioned physical shredding. Each has a specific purpose and security level, and knowing the difference is the key to making sure your data is gone for good.
This decision tree gives you a simple path for picking a destruction method based on your security needs.
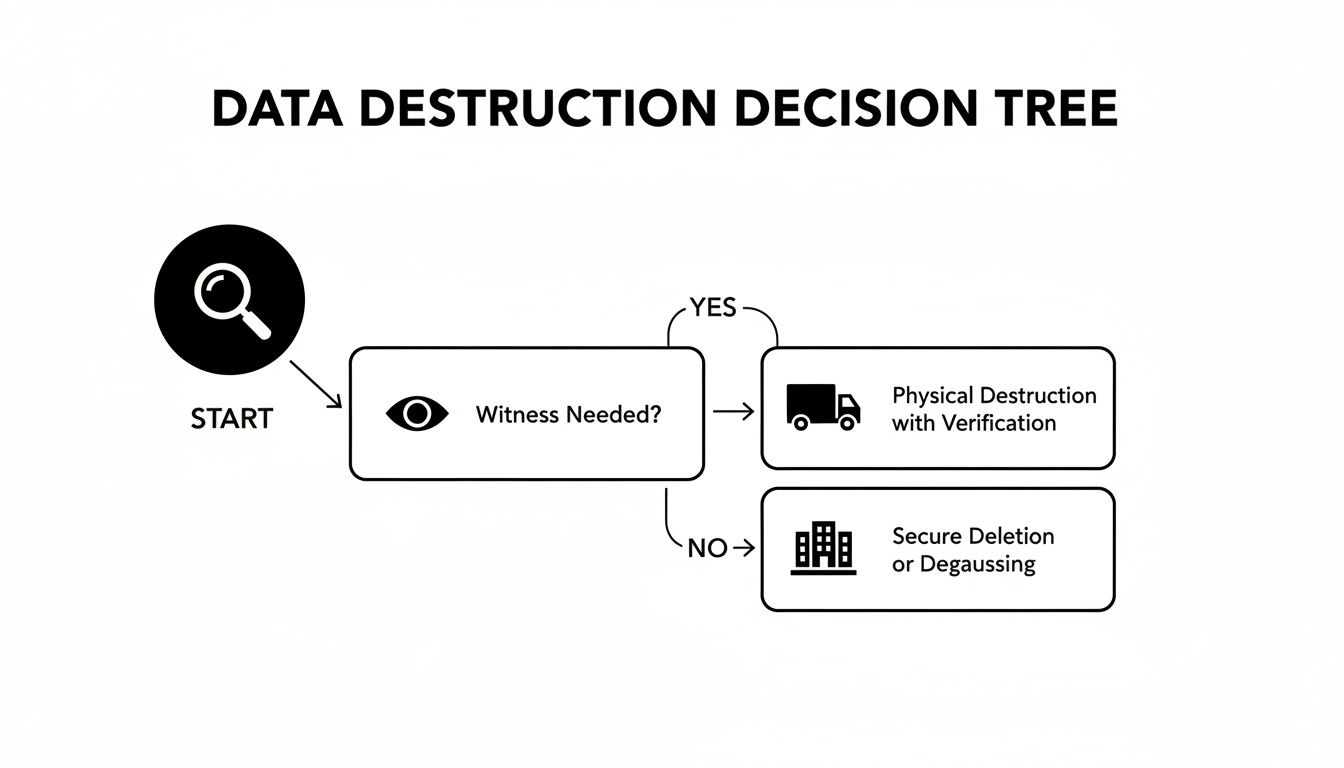
As you can see, the need for direct oversight often points toward on-site solutions, while off-site options provide a secure, fully documented alternative when you don't need to watch it happen.
Software Wiping for Asset Reuse
Software wiping, also called sanitization, uses specialized software to overwrite every bit of existing data on a hard drive with random garbage data. It’s like taking a book and meticulously writing gibberish over every single letter on every page until the original story is completely unreadable.
This is the only method that leaves the physical drive intact and ready for its next life. It’s the perfect solution when you plan to reuse, resell, or donate your hardware. Certified wiping follows strict standards, like those in NIST 800-88, to ensure the data is truly unrecoverable while keeping the asset's value. A multi-pass wipe, for example, just repeats the process several times for an extra layer of security.
Key Takeaway: Software wiping is all about preserving the life of an IT asset. It allows for secure redeployment or remarketing without compromising data security, making it both a sustainable and cost-effective choice.
Degaussing for Magnetic Media
Degaussing is a completely different animal. It uses an incredibly powerful magnetic field to instantly scramble the data on magnetic storage media. Imagine your data is recorded on an old cassette tape. A degausser acts like a giant magnet that instantly wipes that recording clean, leaving behind nothing but static.
This technique is extremely fast and effective for older, traditional hard disk drives (HDDs) and magnetic tapes. But its great strength is also its biggest weakness. Degaussing renders the drive totally inoperable. More importantly, it has zero effect on modern Solid-State Drives (SSDs), which don't store data magnetically. Trying to degauss an SSD is like trying to erase a book by holding a magnet next to it—it just doesn't work. For more on that, check out our guide on the challenges of wiping SSD drives effectively.
Physical Shredding for Ultimate Destruction
When you need absolute, undeniable proof that a device and its data are gone forever, physical shredding is the final answer. This is the most direct and foolproof method there is. It’s the digital equivalent of feeding a top-secret document into an industrial, cross-cut shredder.
The process uses powerful machinery to grind hard drives, SSDs, smartphones, and other devices into tiny, mangled pieces of metal and plastic. At that point, data recovery isn't just difficult; it's a physical impossibility. This is the gold standard for high-security environments and the only universally accepted way to destroy data on SSDs for good.
- Finality: The destruction is absolute and irreversible.
- Verifiability: You can literally see the shredded remains, offering concrete proof.
- Versatility: It works on everything—HDDs, SSDs, backup tapes, and mobile devices.
Choosing the right technique is a critical piece of any secure IT asset disposition strategy. It's all about matching the method to the media and making sure it aligns with your organization’s goals for compliance and reuse.
Navigating Key Compliance and Security Standards
Trying to make sense of the regulations around data disposal can feel like learning a new language. But acronyms like NIST, DoD, HIPAA, and GDPR aren't just bureaucratic alphabet soup; they are the frameworks that define what "secure" actually means in the real world. Following them isn't optional—it's what separates responsible data management from costly negligence.
These standards provide a clear roadmap for how to handle sensitive information when it's time to retire the hardware it lives on. Partnering with secure data destruction services that live and breathe these regulations is your best defense against catastrophic legal, financial, and reputational damage. It ensures your process is not just effective, but completely defensible.
The Gold Standard NIST 800-88
In the world of data sanitization, the National Institute of Standards and Technology (NIST) Special Publication 800-88 is the undisputed gold standard. It provides a practical, risk-based framework that has become the benchmark for both government agencies and private businesses. It moves way beyond just hitting "delete" and outlines three distinct levels of media sanitization.
- Clear: This is a logical wipe of all user-accessible storage areas. It’s effective against simple, non-invasive data recovery attempts and is usually done through standard overwrite commands.
- Purge: This method goes deeper, using physical or logical techniques to make data recovery infeasible even with state-of-the-art lab equipment. Think degaussing, cryptographic erasure, or more advanced overwriting patterns.
- Destroy: This is the most final step. It renders the storage media completely unusable and unrecoverable through physical destruction like shredding, pulverizing, or melting.
NIST 800-88 provides a flexible yet authoritative guide. A certified vendor will help you apply the right method—Clear, Purge, or Destroy—based on your data's sensitivity, ensuring you meet compliance without overspending on unnecessary destruction.
For organizations looking for a partner to meet these stringent requirements, it's vital to work with a provider that understands the nuances of both secure destruction and responsible recycling. You can explore how certifications align with these goals by learning more about what it means to be a certified electronics recycler.
Industry-Specific Mandates HIPAA and GDPR
While NIST provides the technical "how-to," regulations like HIPAA and GDPR dictate the legal "why" for specific industries and regions. They connect the act of data destruction directly to fundamental privacy rights, turning compliance into a non-negotiable part of doing business.
The Health Insurance Portability and Accountability Act (HIPAA) strictly governs how Protected Health Information (PHI) is handled. Its Privacy Rule requires healthcare providers and their partners to safeguard PHI all the way to its final disposal. A single lost or improperly wiped hard drive full of patient records can trigger multi-million-dollar fines and mandatory public breach notifications.
Similarly, the General Data Protection Regulation (GDPR) in the European Union enforces the "right to be forgotten." This gives EU citizens the right to have their personal data erased, forcing companies to have a rock-solid, verifiable process for doing so.
The financial stakes have never been higher. Regulatory pressure is a primary driver behind the explosive growth of the data destruction market, projected to jump from $10.18 billion in 2024 to $11.93 billion in 2025 alone. Since its enforcement, GDPR has led to over 1,200 fines totaling €2.9 billion, while HIPAA breach settlements in the U.S. averaged $6.8 million between 2023 and 2024. The cost of getting it wrong is severe.
While less common now, you might still run into the Department of Defense (DoD) 5220.22-M standard, particularly with older federal contracts. It specifies a 3-pass or 7-pass data overwrite process. Though largely superseded by NIST guidelines, a capable vendor should still be able to perform and certify to this standard when required.
The Importance of Auditable Proof and Chain of Custody
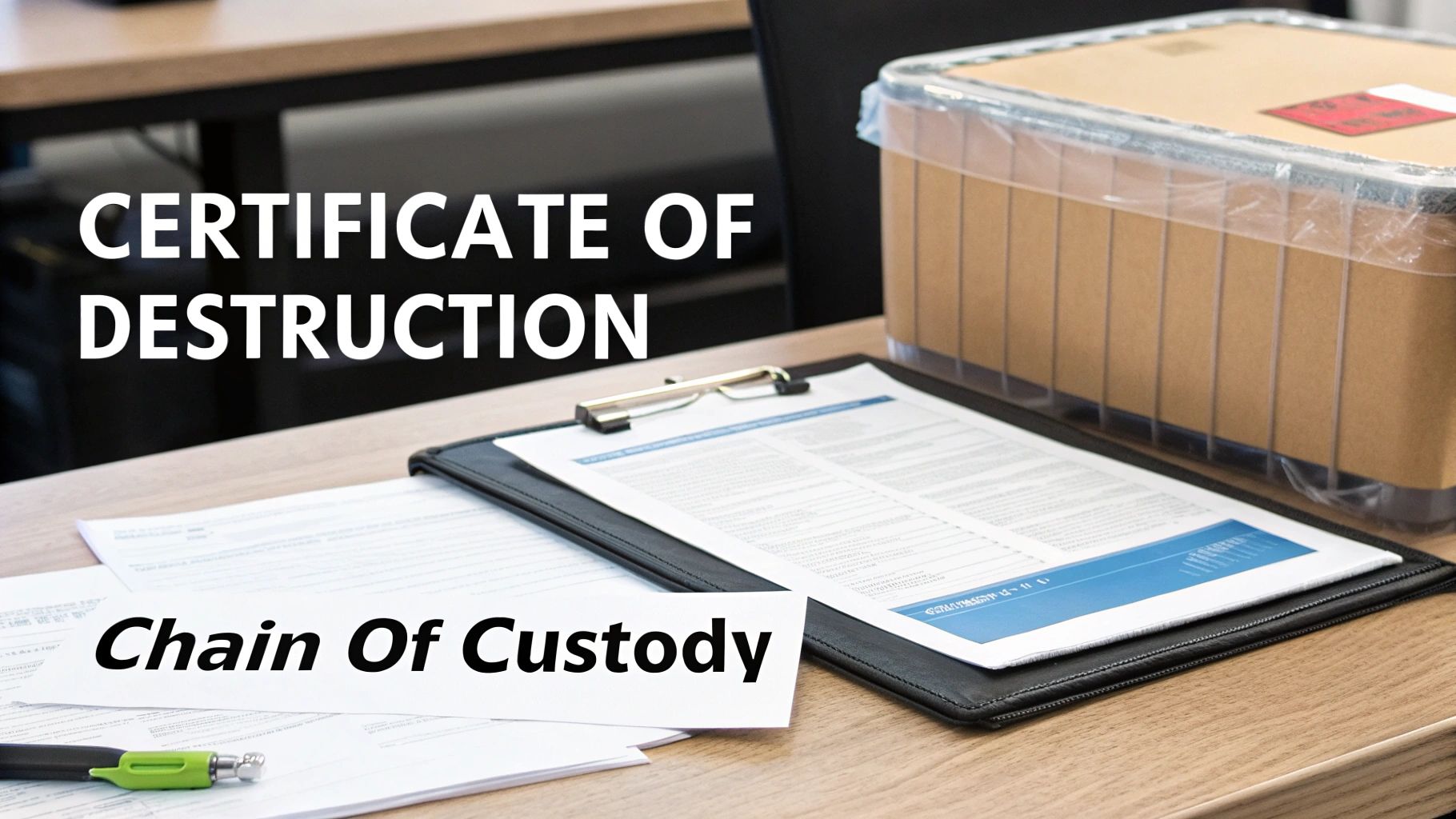
Without tangible proof, data destruction is just a claim. If an auditor comes knocking or you're facing a legal challenge, simply saying you destroyed sensitive data won’t cut it. You need an official, legally defensible record showing you did your due diligence, and that record starts with a solid chain of custody.
Think of it as an unbroken, documented trail of evidence. Much like a forensics team meticulously tracks an item from a crime scene to the lab, a professional IT asset disposal partner tracks your hardware from your facility all the way to its final destruction. This unbroken chain is your first line of defense, proving the integrity of the entire process from start to finish.
This process is what turns abstract security policies into a concrete, observable reality. It’s what assures regulators, stakeholders, and clients that your data was handled securely every step of the way.
Building an Unbreakable Audit Trail
A secure chain of custody isn't a single piece of paper; it's built on several key procedural pillars. Each step is designed to create a verifiable record, eliminating any doubt and ensuring accountability from the moment an asset leaves your control.
This meticulous tracking almost always involves:
- Serialized Asset Tagging: Before anything leaves your premises, every single device—from servers to individual hard drives—gets scanned and tagged with a unique serial number. This creates a detailed inventory that becomes the foundation for all the paperwork that follows.
- Sealed and Secure Transport: Your assets are then placed into locked, tamper-evident containers. Vetted, uniformed technicians transport them in GPS-tracked vehicles, ensuring a secure journey from your door to the destruction facility.
- Secure Facility Access: Certified destruction facilities operate under strict access controls. Think 24/7 video surveillance and logged entry points, guaranteeing only authorized personnel can ever handle your assets.
This systematic approach creates a verifiable timeline, linking each serialized asset to a specific pickup, transport vehicle, and destruction event. It’s this level of detail that makes the process auditable and legally sound.
The Certificate of Destruction: Your Ultimate Proof
The entire chain of custody process culminates in one critical document: the Certificate of Destruction. This is far more than a simple receipt. It's a formal, legal affidavit that serves as your ultimate proof of compliance.
A proper certificate is a detailed record confirming exactly what was destroyed, when, where, and how. It isn’t a generic statement but a specific, factual account of the service. To see what a comprehensive certificate looks like, you can read our guide explaining the importance of a Certificate of Destruction for hard drives.
A compliant Certificate of Destruction should always include:
- Unique Serial Numbers: A complete, cross-referenced list of every asset destroyed, tying directly back to the initial inventory.
- Method of Destruction: A clear statement on the technique used (e.g., shredding, pulverizing) and the compliance standard it met (e.g., NIST 800-88).
- Date and Location: The precise date and location where the destruction took place.
- Transfer of Custody: An official statement transferring all liability for the data from your organization to the destruction partner.
Ultimately, this documentation transforms a procedural task into a powerful liability shield. It provides the irrefutable evidence you need to satisfy auditors, demonstrate compliance with regulations like HIPAA or GDPR, and protect your organization from legal challenges long after the assets are gone.
How to Choose the Right Data Destruction Partner
Picking a partner for secure data destruction is way more than a simple procurement decision—it's a critical choice about managing risk. The right partner acts like an extension of your own security team. The wrong one can leave you wide open to massive liability. Telling the difference between a truly secure, compliant provider and a basic recycler comes down to a sharp eye and asking the right questions.
This isn’t about chasing the lowest bid. It’s about digging into a partner’s certifications, security protocols, and documentation to make sure they can give you the legally defensible proof you need. A top-tier partner provides a shield against downstream risk, not just a simple service.
The demand for these specialized services is exploding. The global secure data disposal market was valued at USD 1.5 billion in 2023 and is on track to hit USD 4.1 billion by 2032. This isn't surprising when you see incidents like a single U.S. breach in 2023 that exposed 422 million records. That’s exactly why IT managers are demanding certified destruction where the odds of data recovery drop to less than 0.001%.
Core Credentials and Certifications
Certifications are your first and most important filter. Think of them as independent proof that a vendor actually meets strict industry standards for security, process, and environmental responsibility. Without them, you’re just taking a company at its word.
Look for these non-negotiable credentials:
- NAID AAA Certification: This is the gold standard for data destruction. It means the vendor has passed unannounced, surprise audits covering everything from employee screening and facility security to their destruction processes and insurance coverage. It's your single best guarantee of a secure chain of custody.
- R2 or e-Stewards Certification: These certifications are all about environmental responsibility and the secure handling of electronics all the way through the recycling chain. They ensure that shredded materials are managed safely and ethically, keeping your e-waste out of a landfill or from being illegally exported.
A vendor that lacks these core certifications should be an immediate red flag. It’s a strong signal they may not have the audited, verifiable processes needed to protect your organization from both data breaches and environmental compliance headaches.
Key Questions for Your Vetting Process
Once you've narrowed your list to certified vendors, it's time to dig deeper. Their answers to these questions will show you the real strength of their operation and separate the pros from the pretenders. The details can get complex, which is why it helps to compare various IT asset disposition companies to find one that truly fits what you need.
Ask any potential partner the following:
- Employee Security: How do you screen your people? Don’t be shy—demand to see proof of background checks, drug screenings, and confidentiality agreements for every single person who might touch your assets.
- Facility Security: Can you walk me through your facility's security measures? You want to hear specifics like 24/7 monitored surveillance, controlled access points, and isolated, secure cages or rooms just for data-bearing devices.
- Chain-of-Custody Procedures: Describe your entire chain-of-custody process from start to finish. A solid answer will cover serialized asset tracking, sealed and GPS-tracked trucks, and a clearly documented transfer of liability at every single step.
- Insurance Coverage: What kind of insurance do you carry, and for how much? A professional partner must have significant general liability and professional liability (also called errors and omissions) insurance that specifically covers data breaches.
- Reporting and Documentation: What, exactly, will our Certificate of Destruction include? Make sure it lists every single asset by serial number, confirms the method of destruction, and is written to serve as a legal affidavit.
By arming yourself with this checklist, you can confidently choose a secure data destruction services partner that doesn’t just check a compliance box, but actively makes your organization's security posture stronger.
Common Questions About Secure Data Destruction
As you start looking into partners and different destruction methods, a few practical questions always seem to pop up. Let's tackle some of the most common ones we hear from IT leaders.
Is Deleting Files And Reformatting A Drive Not Enough?
Not even close. This is one of the most dangerous misconceptions out there. When you delete a file or reformat a hard drive, you're not actually erasing the data—you're just removing the signposts that tell the operating system where to find it.
The actual ones and zeros remain on the drive, and anyone with easily accessible recovery software can pull that information right back. That's precisely why regulations like HIPAA and GDPR explicitly require data to be rendered permanently unrecoverable. To meet that legal standard and eliminate risk, you have to use a certified method like multi-pass wiping or physical shredding.
How Do You Securely Destroy Data On Solid State Drives?
Solid State Drives (SSDs) are a different beast entirely from traditional magnetic hard drives (HDDs). Because they store data on flash memory chips instead of magnetic platters, they are completely immune to degaussing.
The gold standard for destroying data on an SSD is physical destruction. Specifically, shredding the drive into particles of 2mm or smaller obliterates the memory chips, making data recovery a physical impossibility.
While some newer SSDs have a "cryptographic erase" feature, nothing provides the same level of verifiable, foolproof proof as turning the drive into dust. For any high-security environment, physical shredding is the only way to go.
What Happens To The Shredded Materials After Destruction?
A certified, environmentally conscious partner will never let those materials see a landfill. If your vendor holds certifications like R2 or e-Stewards, you can be sure that every last shredded particle enters a secure, fully audited recycling stream.
The mix of shredded metals, plastics, and circuit board fragments is carefully separated and shipped off to specialized downstream processors. From there, the materials are refined back into raw commodities that can be used to build new products. It’s the perfect way to satisfy both your data security requirements and your company’s environmental compliance goals.
Ready to implement a secure, compliant, and auditable data destruction strategy? Dallas Fortworth Computer Recycling offers certified services nationwide, providing the peace of mind that comes from working with an experienced ITAD partner. Get a quote for your project today.
