IT asset disposition McKinney: Secure Data & Compliance for Your Business
For businesses here in McKinney, IT asset disposition (ITAD) is the formal, strategic process for retiring and disposing of outdated technology. It's much more than just getting rid of old equipment. A professional IT asset disposition McKinney program makes sure your company’s sensitive data is completely destroyed, environmental regulations are followed, and any potential value is recovered from those old assets.
Why McKinney Businesses Need a Smart ITAD Strategy

It helps to think of IT asset disposition not as an afterthought, but as a critical stage in your technology's lifecycle. It’s like decommissioning a high-security facility—you wouldn't just walk away and leave the doors open. You would first secure all sensitive information, salvage valuable materials, and make sure the entire process is documented and compliant from start to finish.
For organizations in McKinney's fast-growing economy, a formal ITAD strategy is no longer a "nice-to-have." It's essential. As businesses scale and upgrade their tech, they accumulate a surplus of outdated laptops, servers, and networking gear. If not handled correctly, every single one of those devices is a potential liability.
From Cost Center to Strategic Function
In the past, getting rid of old electronics was often seen as just another operational expense. Today, a modern approach to ITAD reframes this process as a strategic function that protects your business and can even generate a return on investment.
A well-planned strategy accomplishes several critical goals:
- Data Breach Mitigation: Securely and permanently destroys sensitive corporate, customer, and employee data stored on retired hard drives and other devices.
- Regulatory Compliance: Ensures you meet strict industry and government standards for data privacy and environmental responsibility, including regulations like HIPAA and FACTA.
- Value Recovery: Identifies assets with remaining market value that can be refurbished and resold, creating a revenue stream to help offset the costs of new equipment.
- Environmental Stewardship: Guarantees that hazardous electronic components are processed correctly and kept out of landfills. Our guide on e-waste recycling in McKinney covers these environmental responsibilities in greater detail.
To give you a sense of the scale, just look at the local growth. McKinney is a major hub for commercial development, with projects like the 121 Commerce Park adding over 511,000 square feet of new industrial space. All that growth means more companies are setting up shop, expanding, and inevitably upgrading their IT infrastructure—creating a constant flow of retired assets that need professional management.
An effective ITAD program is a pillar of modern corporate governance. It transforms a potential risk into a controlled, documented, and secure business process that safeguards your company’s reputation and bottom line.
A professional ITAD partner helps you manage this entire lifecycle. We provide the expertise to classify assets, sanitize data to government standards, and deliver auditable reports that prove compliance every step of the way. For IT leaders in McKinney’s competitive business, government, and healthcare sectors, this formal process is essential for managing risk in a complex operational world.
Understanding the Growing Demand for Professional ITAD
The need for professional IT asset disposition is no longer just a concern for massive corporations. For businesses of every size in McKinney, it has become a fundamental operational necessity. Several powerful forces are at play, creating an environment where simply tossing out old technology isn't just irresponsible—it's a direct threat to your business.
At the heart of this demand is how quickly technology evolves. The average refresh cycle for business laptops and desktops is now just 3 to 5 years, and critical data center hardware like servers is often replaced even sooner. This rapid turnover means companies are constantly managing a flow of retired assets, each one a potential data security risk if not handled by a professional.
Think of it as a pipeline that never shuts off. As new, more powerful technology comes into your organization, the old equipment has to go somewhere. Without a formal process for IT asset disposition in McKinney, that outflow can quickly become a chaotic, unmanaged flood of liability.
The Forces Driving ITAD Growth
Three key factors are turning ITAD from a back-office task into a boardroom-level conversation. Each one introduces a significant risk that can only be managed with a structured, professional approach.
- Rapid IT Upgrade Cycles: As mentioned, technology moves fast. Businesses must upgrade to stay competitive, efficient, and secure, which creates a constant stream of retired assets that need proper management.
- Expanding Data Center Footprint: The DFW metroplex is a major hub for data centers. This concentration of digital infrastructure means more servers, storage arrays, and networking gear are being decommissioned locally, all holding immense amounts of sensitive information.
- Stricter Data Privacy Laws: Regulations like HIPAA (for healthcare), FACTA (for finance), and GDPR have serious teeth. Non-compliance can lead to severe financial penalties and permanent damage to a company's reputation.
These forces create a perfect storm. For instance, a McKinney-based medical clinic upgrading its patient management system must dispose of old servers. If handled improperly, thousands of patient records could be exposed, resulting in a HIPAA violation with fines that can reach millions of dollars. For an in-depth look at our specialized services that address these exact scenarios, you can explore our comprehensive Dallas-Fort Worth ITAD services.
The question is no longer if a business will need ITAD services, but how it will manage the process to protect itself. Ignoring this reality is a gamble with the company's future.
From Local Trend to Global Imperative
The demand for expert ITAD isn't just a local McKinney phenomenon; it’s part of a massive global shift. The worldwide IT asset disposition market has seen incredible growth, with projections showing its value reaching between $23 billion and $26.46 billion by 2026. This market isn't just growing; it's accelerating, with compound annual growth rates (CAGR) expected to hit as high as 14.0% in the coming years. You can review more details on this expansion in the full market growth report.
This data confirms that investing in professional ITAD is not an isolated cost but a strategic move that aligns with a major industry trend. For IT managers and procurement teams, this information is crucial for building a strong internal case. It shows that adopting a formal IT asset disposition McKinney strategy is no longer just a best practice—it's a standard of modern business and a critical component of risk management.
Protecting Your Data and Ensuring Full Compliance
When you’re retiring old technology, nothing is more important than protecting the sensitive information stored on it. For any McKinney business, a single compromised hard drive can lead to staggering financial penalties, damage to your reputation, and a complete loss of customer trust. Professional IT asset disposition McKinney services go far beyond simple recycling; they build a fortress of security around your data.
Think of it like decommissioning a bank vault. You wouldn't just lock the door and walk away. A proper process involves making sure every single valuable—in this case, your data—is securely neutralized or removed before the vault itself is dismantled. This level of diligence isn't just a good idea; it's a fundamental requirement for modern businesses.
The Science of Permanent Data Destruction
Simply deleting files or reformatting a hard drive isn't enough. These common methods often leave behind data remnants that can easily be recovered with specialized software. Professional ITAD partners use certified, irreversible data destruction techniques to guarantee your information is gone for good.
There are two primary methods for achieving this level of security:
- Physical Shredding: This is the most direct and visually verifiable method. Hard drives, SSDs, and other storage media are fed into industrial shredders that grind them into tiny, unrecognizable fragments. It’s like a high-security paper shredder, but built to destroy dense electronic components, making data recovery physically impossible.
- Cryptographic Erasure: For newer devices, especially SSDs, cryptographic erasure is a highly effective software-based solution. This technique works by destroying the unique encryption key that makes the data readable. Without the key, the encrypted information on the drive becomes a permanent jumble of useless code, effectively locking it forever.
A key takeaway is that professional data destruction is a documented, auditable process. It’s not just about destroying the data; it’s about proving that you did it correctly, which is vital for any compliance audit.
This is where a trusted partner adds immense value. They provide the expertise to choose the right destruction method for each type of asset and the technology to execute it flawlessly.
Navigating McKinney's Regulatory Landscape
For organizations in specific McKinney industries, data security isn't just an internal policy—it's the law. Navigating this complex web of regulations is a core function of a professional ITAD program. A failure to comply can lead to steep fines, legal action, and a significant loss of public trust.
Several key regulations directly impact how local businesses must handle data on retired assets:
- HIPAA (Health Insurance Portability and Accountability Act): For healthcare providers, clinics, and any business handling protected health information (PHI), HIPAA mandates strict security protocols for data on any device, even at disposal.
- FACTA (Fair and Accurate Credit Transactions Act): Financial institutions, auto dealerships, and any company using consumer credit reports must comply with FACTA. The act requires the secure destruction of consumer information to prevent identity theft.
- NIST 800-88: While technically a set of guidelines, the National Institute of Standards and Technology's Special Publication 800-88 is the gold standard for data sanitization. It's required for government agencies and contractors and widely adopted by private companies as a best practice for defensible data destruction. You can learn more about how secure data destruction aligns with these standards.
The Power of Auditable Proof
Ultimately, compliance is about documentation. A professional ITAD process gives you a clear, unbroken paper trail that serves as your proof of due diligence. Two documents are absolutely essential:
- Chain of Custody: This detailed log tracks every single asset from the moment it leaves your McKinney facility until its final disposition. It records serial numbers, asset tags, and every handoff, creating an accountable record of who had your equipment and when.
- Certificate of Destruction: Once your data-bearing devices are destroyed, your ITAD partner issues a formal Certificate of Destruction. This legal document certifies the date, method, and serial numbers of the assets that were sanitized, serving as your official proof of compliance for any future audit.
A Step-By-Step Guide to the ITAD Process
Figuring out what to do with old company electronics can seem like a headache, but a professional ITAD process is actually very straightforward. It’s a transparent, documented system designed to be as undisruptive as possible, ensuring your retired tech is handled securely from the moment it leaves your office.
To show you exactly how it works, let's walk through a typical scenario. We'll follow a fictional McKinney architecture firm, "ArchInnovate," as they retire a batch of older laptops and a few servers.
Stage 1: Initial Consultation and Scoping
It all starts with a simple phone call or a web inquiry. ArchInnovate gets in touch with us to discuss their needs: they have roughly 50 laptops from a recent employee upgrade and three servers coming out of their on-site server closet.
During this first conversation, we’ll ask a few key questions to map out the project:
- What kinds of equipment are being retired, and how many of each?
- Where are the assets located in your McKinney office?
- Do you have any specific data security rules or compliance standards to meet (like NIST 800-88)?
- What’s your ideal timeline for getting the equipment out of your space?
With that information, we put together a clear, detailed proposal. It outlines all the services—secure pickup, certified data destruction, and responsible recycling—and provides a transparent quote with no hidden fees, including any potential value recovery from the assets.
Stage 2: Secure Logistics and On-Site Services
Once ArchInnovate gives the green light, our logistics team gets to work. An insured, professional crew arrives at their McKinney office at the scheduled time. The first thing they do is an on-site inventory, creating a master list by scanning every serial number and asset tag.
This step is the foundation for a secure chain of custody. Think of it as the official start of a documented journey for every single device.
A documented chain of custody is non-negotiable. It's the auditable proof that tracks your assets from the moment they leave your control until their final disposition, ensuring total accountability.
Next, our team securely packs the equipment onto pallets, shrink-wraps them, and loads everything into a locked, GPS-tracked truck for transport to our secure facility. This controlled process guarantees nothing gets lost or compromised along the way. For a deeper dive into prepping your hardware, take a look at our complete server decommissioning checklist.
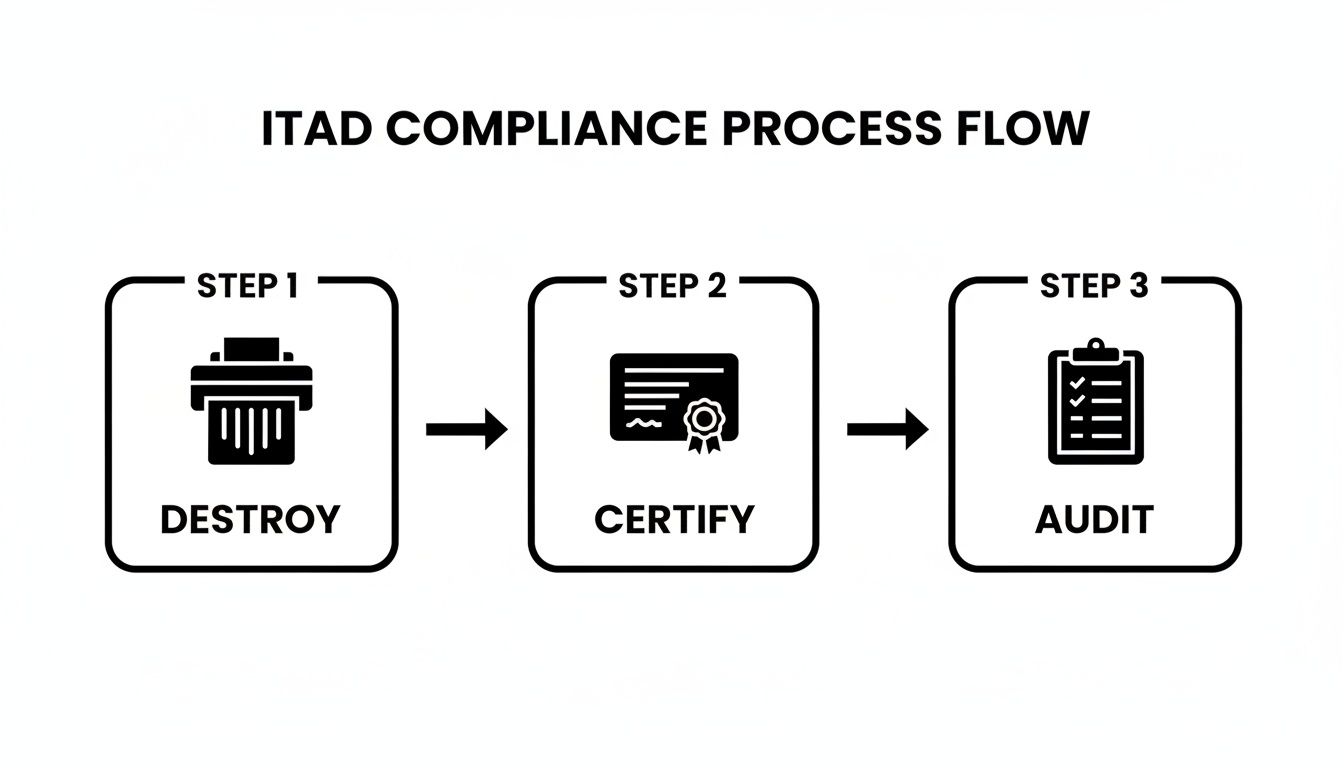
This visual breaks down the core compliance steps—Destroy, Certify, and Audit. These are the pillars of any ITAD program designed to protect your business from risk.
Stage 3: Data Destruction and Final Reporting
When ArchInnovate's assets arrive at our facility, they are checked in and the serial numbers are reconciled against the inventory list created at their office. From there, all the data-bearing devices—the laptop hard drives and server SSDs—are immediately segregated for destruction.
Different data requires different levels of security. Here’s a quick breakdown of the most common methods to help you decide what’s right for your organization.
Choosing Your Data Destruction Method
| Method | Process Description | Best For | Compliance Standard |
|---|---|---|---|
| Data Wiping | Software overwrites all data on a drive with random characters, making the original data unrecoverable. | Reusing or remarketing drives with resale value; meeting basic corporate policies. | NIST 800-88 Purge |
| Degaussing | A powerful magnetic field is used to instantly and permanently erase the magnetic data on hard drives and tapes. | Quickly sanitizing large quantities of magnetic media that will not be reused. | DoD 5220.22-M |
| Physical Shredding | The drive is physically destroyed by an industrial shredder, which grinds it into tiny metal fragments. | Maximum security for highly sensitive data; ensuring data recovery is impossible. | NIST 800-88 Destroy |
Because ArchInnovate’s security policy requires absolute certainty, they chose physical shredding. The drives are fed into an industrial shredder that reduces them to small, unsortable pieces, making data recovery physically impossible.
After destruction comes the final, and most critical, step: reporting. We provide ArchInnovate with two essential documents:
- A Certificate of Destruction: This is a legally binding document that certifies by serial number which assets were destroyed in accordance with industry standards.
- A Final Asset Report: This report gives a complete summary of every item’s final disposition, confirming whether it was recycled, remarkedeted, or destroyed.
With these documents in hand, ArchInnovate has irrefutable, auditable proof that their IT asset disposition in McKinney was handled securely and in full compliance. The entire process was managed by us, freeing up their internal IT team to focus on their core business.
How to Select the Right ITAD Partner in the DFW Area

Choosing an ITAD partner in the crowded DFW market can be tricky. A lot of vendors will promise secure service, but not all of them have the credentials and processes to actually back it up. The right choice goes way beyond comparing price quotes—it's about finding a partner you can trust with your company's most sensitive data and its reputation.
Think of it this way: you wouldn't pick a specialized surgeon based on who offers the cheapest rate. You’d dig into their credentials, check their track record, and make sure they use accredited, proven methods. You need to apply that same level of diligence when selecting a provider for your IT asset disposition in McKinney.
Your goal is to find a partner who operates like a natural extension of your own security team. They should reduce your risk, give you an auditable paper trail, and protect your organization from the massive fallout of a data breach or an environmental fine.
Focus on Foundational Certifications
Before you even get into a sales call, your first filter should always be industry certifications. These aren't just logos for a website; they are hard-earned proof that a vendor has passed rigorous, independent audits of their data security, environmental practices, and worker safety protocols.
In the ITAD industry, two certifications are considered the gold standard. Any credible partner will hold at least one of them:
- R2v3 (Responsible Recycling): This is the latest version of the R2 standard, and it sets an incredibly high bar. An R2v3 certified vendor must prove they have a secure chain of custody and show that all hazardous e-waste is managed correctly through a fully vetted downstream recycling chain.
- e-Stewards: Developed by the Basel Action Network, the e-Stewards standard is famous for its strict, no-exceptions rule against exporting hazardous electronic waste to developing nations. It also has tough requirements for data security and social responsibility.
These certifications give you a baseline of trust. They confirm a provider’s operations for IT asset disposition McKinney aren't just self-proclaimed promises but have been verified by a qualified, objective third party.
Key Questions to Ask Potential Vendors
Once you've confirmed a vendor has the right certifications, it’s time to dig deeper. A professional partner will expect and welcome these questions. Think of this as your due diligence checklist.
Can You Detail Your Chain-of-Custody Process?
Have them walk you through, step-by-step, how they track an asset from your McKinney office to its final destruction or recycling. You want to hear about serialized inventory reports, securely sealed transport, and documented handoffs. A vague answer is a huge red flag.What Data Breach Insurance Do You Carry?
Even with rock-solid processes, you need a safety net. A professional ITAD provider must carry sufficient data breach and liability insurance to protect your organization if the worst should happen. Ask for a copy of their certificate of insurance to verify the coverage limits.Who Are Your Downstream Partners?
No single company handles every single commodity in-house. They all rely on a network of downstream vendors for things like processing crushed monitor glass or refining precious metals. Your potential partner must be transparent about who these vendors are and prove that they are also certified and regularly audited.
A truly secure ITAD partnership is built on transparency. If a vendor is hesitant to share details about their insurance, downstream partners, or security protocols, it’s a clear sign that you should look elsewhere.
This level of scrutiny is non-negotiable. Your liability for improper data handling or disposal doesn't just vanish when the truck drives away. By asking these tough questions, you ensure you’re teaming up with a company that takes accountability as seriously as you do. For an overview of top providers, our guide to IT asset disposition companies can offer more perspective.
By shifting your focus from price to credentials, security, and transparency, you empower your McKinney team to make the right call. The best partner won’t just take your old gear; they’ll deliver genuine peace of mind with a secure, compliant, and fully auditable process.
Common Questions About IT Asset Disposition
Even after deciding to move forward, businesses in McKinney often have a few practical questions about how IT asset disposition really works. Getting clear, straightforward answers is the best way to feel confident about the process. Here are some of the most common questions we hear from local organizations.
What Types of Equipment Do You Handle for IT Asset Disposition?
A professional IT asset disposition McKinney partner should be able to manage just about every piece of technology your company uses. The goal is a single, unified solution, so you aren't stuck juggling different vendors for servers, laptops, and mobile phones. This simplifies your logistics and ensures consistent security from start to finish.
We manage the full spectrum of business technology, from standard office gear to specialized data center hardware. Our process is built to track every single asset from your McKinney facility through its final disposition, giving you a complete, auditable record that everything was handled securely.
This includes, but is not limited to:
- Office Equipment: Desktops, laptops, monitors, printers, and docking stations.
- Data Center Hardware: Servers, storage arrays (SANs/NAS), and networking gear like switches and routers.
- Mobile Devices: Smartphones and tablets that hold sensitive company data.
- Peripherals: Keyboards, mice, cables, and other related accessories.
The entire engagement starts with a detailed on-site inventory, creating a clear record before a single piece of equipment leaves your control.
Will We Get Money Back or Is There a Cost for ITAD Services?
This is one of the first questions most people ask, and the honest answer is: it depends. The final financial outcome hinges entirely on the age, condition, and current market demand for your equipment. An ITAD project can result in a net cost, be cost-neutral, or even generate a return for your company.
When you have newer, functional equipment—like laptops that are just a few years old or in-demand server components—there is often real resale value. In these situations, we refurbish and remarket the assets. The revenue we generate is shared back with you, which can often offset or completely cover the service fees. Sometimes, it even results in a check back to your business.
On the other hand, for older, broken, or obsolete equipment with no secondary market value, a service fee is usually necessary. This fee covers the critical work required for secure and compliant disposal, including:
- Secure transportation and logistics.
- Labor for inventorying and processing.
- Certified data destruction to NIST standards.
- Responsible, environmentally compliant recycling of all materials.
A trustworthy ITAD provider will always provide a transparent, itemized quote before any work begins. This quote should clearly outline all potential costs alongside any projected revenue from asset remarketing, allowing you to make an informed financial decision.
How Do We Schedule an Equipment Pickup in McKinney?
Scheduling a pickup for your retired assets is a simple and straightforward process. Our goal is to work around your business operations, not the other way around, minimizing any disruption to your team.
Just contact us through our website or give us a call to get started. We'll ask for a few key details to understand your project:
- Asset Details: What types of equipment do you have, and what is the rough quantity?
- Location Information: Where are the assets located in your McKinney facility (e.g., a storage closet, data center, or spread across individual offices)?
- Special Requirements: Are there any specific security protocols, compliance needs, or logistical hurdles like stairs or limited loading dock access?
With that information, we’ll coordinate a pickup time that works for your schedule. Our insured logistics team arrives on-site and handles all the physical work—packing, palletizing, and loading everything onto a secure truck. The entire experience is designed to be seamless for you.
Is This a Global Issue or Just a Local Concern?
While your immediate focus is on your McKinney operations, it helps to know that ITAD is part of a much larger global trend. The rapid pace of technology refreshes and stricter data privacy laws aren't just local challenges; they are driving change for businesses everywhere.
For example, the Asia-Pacific region is now the fastest-growing market for IT asset disposition, projected to hit $10.1 billion by 2035 with a 9.9% compound annual growth rate. This boom is fueled by massive data center expansion and tightening regulations, mirroring the same pressures that businesses face right here in North Texas. You can explore additional research on these global ITAD market trends.
Ready to simplify your technology retirement process? With over 13 years of experience, Dallas Fortworth Computer Recycling provides secure, compliant, and transparent IT asset disposition services for businesses across the nation. We handle everything from secure logistics and certified data destruction to responsible recycling, giving you auditable proof and peace of mind.
