Computer Recycling Center Houston TX: Expert Guide
A lot of Houston IT directors are dealing with the same scene right now. A back room fills up with retired laptops, dead monitors, outdated switches, backup tapes, and a few servers nobody wants to touch because they still might contain sensitive data. The equipment looks like clutter, but the problem isn't the space it takes up.
The main problem is exposure. A drive that leaves your building without control can become a breach event. Equipment sent to the wrong downstream vendor can create environmental liability. Hardware with residual value can get scrapped too early, turning a recoverable asset into a write-off. If you're searching for a computer recycling center houston tx businesses can trust, you're not really looking for a drop-off site. You're looking for a disciplined IT asset disposition process.
The Challenge of Retiring Business IT Assets in Houston
A storage room full of retired hardware usually means several projects collided at once. A desktop refresh finished. A team moved offices. A server cluster was replaced. A department held onto old devices "just in case," and now nobody has a clean asset list or a clear chain of custody.

In Houston, that problem scales fast. The city serves energy, healthcare, education, public sector, and technology-heavy operations, all of which cycle through large volumes of equipment. According to Houston Computer Recycling Center, hundreds of computers and other electronics are disposed of into landfills daily in Houston, which creates environmental risk and drives the push to repair, resell, or recycle used electronics. The same source notes that this broader effort is supported by nationwide partners such as Dallas Fortworth Computer Recycling, which has provided compliant IT disposition since 2012.
Why business recycling is really ITAD
For a household, recycling might mean dropping off an old PC. For a business, the process is IT asset disposition, or ITAD. That distinction matters because business equipment carries records, regulated data, software licensing issues, audit obligations, and internal approval requirements.
An effective ITAD program has to answer questions like these:
- Who touched the asset last: You need accountability before anything leaves the building.
- What data was on it: A retired workstation and a decommissioned lab server don't carry the same risk.
- Can any value be recovered: Working assets may be suitable for remarketing, reuse, or donation.
- Where do materials go next: Downstream handling matters as much as pickup day.
Old hardware becomes risky when nobody can document where it was, what was on it, and how it was destroyed.
Houston organizations also have to think beyond convenience. A vendor that can pick up equipment is helpful. A vendor that can support auditability, secure handling, and compliant processing is what reduces liability. That's why many IT teams look at providers that support business-grade disposition workflows across Texas, including Texas electronics recycling services, rather than treating the job like a one-time junk haul.
What doesn't work
Three approaches usually fail.
First, letting equipment sit. Storage isn't a control. It's just delayed risk.
Second, allowing informal disposal through facilities staff, movers, or ad hoc liquidation. That breaks chain of custody.
Third, choosing a recycler based only on proximity. The nearest outlet may be fine for household drop-off, but enterprise retirement requires documented processes, not just a loading dock.
Beyond the Dumpster Core Services of a Houston E-Waste Center
A professional e-waste partner does much more than collect old computers. The useful way to evaluate a computer recycling center houston tx companies rely on is to look at the full operating model. If a vendor can't explain each part of that model clearly, they're probably not ready for regulated or enterprise work.
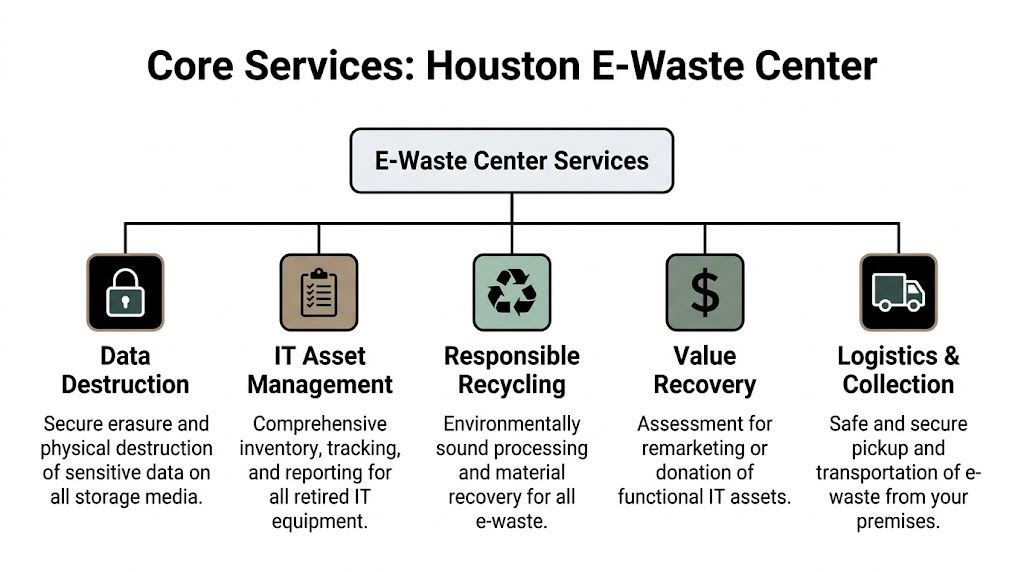
Secure logistics and intake
The process starts before the truck arrives. Good partners define pickup scope, packaging expectations, site access, and who signs transfer paperwork. On collection day, they don't just load loose assets and leave. They maintain control from dock to facility.
For business projects, secure logistics typically include:
- Scheduled pickup windows: Useful when equipment comes from occupied offices, data centers, labs, or clinical areas.
- Controlled handoff: Assets are counted, labeled, or matched to an internal list at pickup.
- Protected transit: The goal is to prevent loss, mix-ups, or untracked stops between your site and the processor.
Houston organizations with recurring retirements often look for broader computer recycling services for business equipment so pickup, transit, and reporting stay consistent across locations.
Inventory and reporting
Weaker vendors often show gaps. They may remove equipment successfully but provide vague summaries later. That doesn't help your audit team, security team, or procurement team.
A proper intake process creates an auditable record. Depending on the project, that can include asset tags, serial numbers, device categories, condition notes, and final disposition status. Reporting should let you answer basic but important questions: what was collected, what was reused, what was destroyed, and what was recycled.
Operational test: If your vendor's final report wouldn't satisfy legal, compliance, and finance in the same meeting, the reporting isn't strong enough.
Data destruction and value recovery
These two services often get treated as separate conversations, but they affect each other.
If the vendor can sanitize eligible assets correctly, some devices may retain resale or reuse value. If sanitization isn't handled properly, the safest option becomes destruction. That may be necessary for certain assets, but a strong ITAD partner helps you make that decision deliberately.
Here are the practical lanes:
- Devices with no reuse case go straight to physical destruction and materials processing.
- Assets with residual value are evaluated for refurbishment or remarketing after approved data sanitization.
- Regulated or high-risk equipment is usually handled under stricter destruction rules, even when hardware still functions.
Responsible recycling
Not everything can be reused. Boards, plastics, metal housings, cables, and failed components need downstream processing that doesn't just move the problem elsewhere.
Houston has mature infrastructure for this. The Houston-Galveston Area Council highlights CompuCycle's capabilities and notes that the company remains the only Texas processor capable of shredding electronics and separating them into raw materials like steel, aluminum, copper, plastics, and circuit boards through its certified operation, as described by the Houston-Galveston Area Council electronics recycling resource. That matters because real recycling depends on actual processing capacity, not just collection.
Navigating the Maze of E-Waste Regulations and Certifications
Certifications only matter if you understand what they control. Too many buyers treat them like logos on a website. In practice, they signal whether a recycler has documented systems for environmental management, quality control, worker safety, and responsible electronics handling.

What the main certifications tell you
The most important starting point in electronics recycling is R2, now commonly referenced in its current framework as R2v3. For a business customer, the value of R2 isn't the badge itself. It's the expectation that the recycler follows defined controls around handling, tracking, downstream management, and environmental practices.
The ISO certifications often tell you something different:
- ISO 9001 points to a formal quality management system.
- ISO 14001 addresses environmental management practices.
- ISO 45001 addresses occupational health and safety.
Those standards don't replace security validation, but they do show whether the operator runs a controlled facility instead of improvising each project.
A Houston benchmark worth understanding
Houston's CompuCycle is a useful local benchmark because it was the city's first recycler to achieve R2, ISO 14001, ISO 9001, and ISO 45001 certifications, which the Houston-Galveston Area Council describes as setting a high bar for compliant e-waste management and supporting secure data destruction and responsible IT asset disposal through the regional Houston electronics recycling guidance. That combination matters because it reflects process maturity across several risk areas, not just one.
If you're comparing vendors, don't stop at "Are you certified?" Ask narrower questions:
- Which facility is certified: Corporate-level claims can hide facility-level gaps.
- What services fall under the certification scope: Pickup, sanitization, storage, and downstream processing may not all be covered the same way.
- Can they produce current documentation: A serious operator won't hesitate.
Certifications are useful when they change behavior on the floor. They aren't useful when they're only part of the sales script.
What works and what doesn't
What works is using certifications as a filter, then validating the operating details behind them. Ask to see how assets are tracked, how exceptions are handled, and how final reports are structured.
What doesn't work is assuming any certified recycler is automatically a fit for your environment. A clinic, public agency, engineering firm, and data center operator don't retire the same assets or carry the same exposure. The right partner is the one whose controls match your risk profile.
A final point matters for Texas buyers. State requirements around covered devices and proper handling aren't theoretical. Vendors that understand compliant electronics processing help your organization avoid preventable mistakes. That's why experienced procurement teams review both certification scope and actual workflow before approving a recycler.
Your Step-by-Step Guide to Engaging a Recycling Partner
Most ITAD projects become manageable once the workflow is visible. The best vendors run the process in a predictable sequence, with clear handoffs and documentation at each stage.
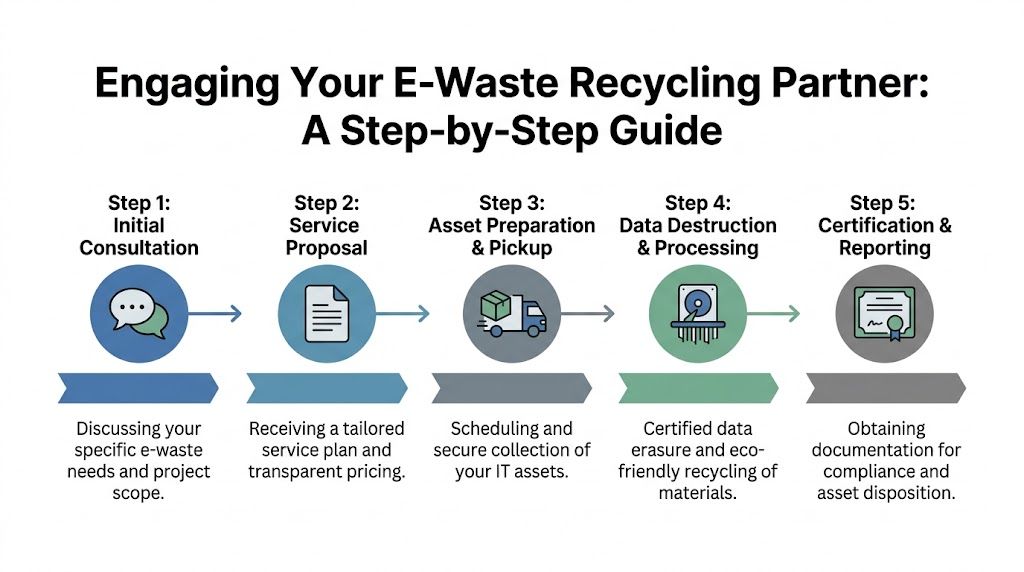
Start with scope, not price
A lot of teams ask for a quote too early. Price matters, but scope matters first. If you don't define what you have, where it sits, and what level of destruction each class of equipment requires, the quote won't be comparable across vendors.
At minimum, prepare:
- Asset categories: Laptops, desktops, servers, network gear, storage, phones, lab devices, peripherals.
- Site conditions: Office pickup, warehouse pull, data center deinstall, loading dock access, elevators, badging, after-hours windows.
- Risk level: Standard office refresh isn't the same as regulated storage media retirement.
If your project is broader than a simple pickup, review how business-focused IT asset disposition companies define scope around logistics, media handling, and reporting.
What happens on pickup day
A disciplined pickup feels controlled, not rushed. The team should know what they're taking, who authorizes release, and how assets are segregated. If equipment still needs onsite counting, labeling, or palletization, that should be part of the plan.
This stage usually includes a few practical checkpoints:
- Handoff confirmation from your designated contact.
- Asset reconciliation against a provided list or onsite count.
- Transfer documentation showing the recycler has taken custody.
Weak pickups are easy to recognize. People start asking basic questions they should've resolved earlier. Assets from different departments get mixed together. Nobody can explain how discrepancies will be reported.
Processing and final closeout
After pickup, the work moves into intake, data destruction, testing where applicable, and final disposition. During these stages, a vendor proves whether their internal controls are real.
A strong closeout package usually gives you:
- Certificates of destruction for media or devices that required destruction
- Disposition reporting showing what was recycled, refurbished, or otherwise processed
- Supporting audit records tied back to the collection event
Ask one question before approving any vendor: "What document will I have in hand at the end, and will it stand up in an audit?"
The reason this matters is simple. Retirement projects often get revisited months later by legal, security, finance, or procurement. When that happens, memory won't protect you. Documentation will.
How Certified Data Destruction Protects Your Business
If you only scrutinize one part of the recycling process, scrutinize data destruction. Everything else is secondary. You can recover from poor resale value. You can fix a delayed pickup. A preventable data exposure tied to retired hardware is far harder to contain.
The methods that matter
The main methods are software sanitization, degaussing, and physical shredding. Each has a valid role, but they aren't interchangeable.
Software sanitization is used when a drive is healthy enough to be overwritten according to policy. This is often the path for reuse-capable devices.
Degaussing applies to magnetic media. It disrupts the magnetic field so the stored information can't be recovered.
Physical shredding destroys the media itself. Think of it as a hard-stop method when reuse isn't appropriate or the risk level is too high.
The benchmark many organizations use is NIST SP 800-88. According to STS Electronic Recycling's Houston facility page, proper data destruction compliant with NIST SP 800-88 is essential because data breach costs can average $9.44M for regulated industries like healthcare, and a zero-landfill policy combined with certified shredding or degaussing makes data forensically irrecoverable.
Why chain of custody is the real control
Methods matter, but chain of custody is what turns a destruction event into a defensible process. If a drive goes missing before destruction, it doesn't matter how good the shredder is.
Look for a workflow that documents:
- Collection custody: Who released the asset and when
- Transit custody: How the load was secured and received
- Processing custody: Which media was sanitized, shredded, or degaussed
- Proof of completion: A certificate tied to the destruction event
For organizations with regulated data, the documentation isn't just administrative. It becomes part of your security record. That's why many buyers specifically request secure data destruction services built around NIST-aligned handling and auditable output.
A certificate of destruction isn't paperwork for its own sake. It's the record that shows your organization acted with control when the data still existed.
Where companies get this wrong
The most common mistake is assuming deletion equals destruction. It doesn't.
The second mistake is applying one destruction standard to every asset. Some equipment can be sanitized and reused. Some must be physically destroyed because of regulation, media type, or internal policy. Mature programs classify before they destroy.
Choosing Your Houston Partner Key Questions to Ask
A recycler should be able to answer hard questions without circling back for basic details. If the responses are vague, the process behind them is usually vague too. That's a serious concern in Houston, especially for healthcare, energy, government, and other operations retiring high-risk equipment.
The need for vetting is stronger than many buyers realize. A 2025 GAO audit found 40% of U.S. recycled electronics were rerouted to illegal landfills abroad despite R2 claims, and the same source notes that Houston's energy sector generates 15% more server e-waste year-over-year, increasing compliance risk, according to the Goodwill Houston partnership discussion.
Vendor Vetting Checklist
| Area of Concern | Question to Ask | Why It Matters |
|---|---|---|
| Certifications | Which certifications does the specific processing facility hold today, and what is the scope? | Facility-level certification tells you more than a corporate logo on a website. |
| Data destruction | Which destruction methods do you use for HDDs, SSDs, backup media, and failed drives? | Different media require different controls. One generic answer isn't enough. |
| Chain of custody | How do you document custody from pickup through final destruction or recycling? | This is what makes your disposition process defensible in an audit. |
| Reporting | Will I receive serialized reporting, certificates of destruction, and disposition summaries? | Final documentation is what legal, compliance, and finance will ask for later. |
| Downstream accountability | Do you process materials directly, and how do you verify downstream vendors? | Downstream opacity is where a lot of risk hides. |
| Regulated assets | How do you handle healthcare, laboratory, public-sector, or other sensitive equipment? | Specialized assets often need tighter workflows and clearer approval paths. |
| Logistics | Can you support office pickups, data center work, and multi-site coordination? | A vendor that can't manage logistics cleanly creates risk before processing even begins. |
| Insurance and incident handling | What happens if an asset is damaged, lost, or found to be out of scope? | Exceptions reveal whether the vendor has mature controls. |
What strong answers sound like
Good vendors speak concretely. They can describe intake, segregation, media handling, and reporting without resorting to buzzwords. They don't hide behind broad phrases like "fully secure" or "environmentally friendly." They explain the operational steps.
Weak vendors usually over-focus on free pickup, generic sustainability language, or convenience. Those points matter, but they shouldn't dominate the conversation when the project involves regulated data or enterprise equipment.
If a vendor can't explain downstream accountability in plain language, treat that as a risk signal, not a minor gap.
A practical buying rule is to compare vendors on documentation quality, not just service menus. Almost every recycler says they handle computers, laptops, and servers. The difference shows up in how they track, destroy, certify, and report.
Making a Strategic Choice for Your IT Asset Disposition
Retiring hardware isn't a cleanup task. It's a risk decision, a compliance decision, and often a value-recovery decision at the same time. That's why the right computer recycling center houston tx partner should be evaluated more like a security and operations vendor than a hauling service.
The strongest approach is simple. Classify assets correctly. Match destruction methods to data risk. Verify certifications at the facility level. Demand chain of custody. Review downstream accountability. Keep final documentation organized enough that security, finance, and procurement can all rely on it later.
That discipline protects your organization in ways a quick pickup never will. It reduces exposure, supports audits, and helps you retire technology without creating a second problem after the refresh is complete.
Frequently Asked Questions About Computer Recycling in Houston
Do Houston recyclers charge for business pickups
Sometimes yes, sometimes no. It depends on asset mix, volume, labor required onsite, location conditions, and whether the project includes specialized handling such as server removal, media destruction, or regulated equipment workflows. Businesses should ask for pricing tied to scope, not a generic pickup promise.
Can a recycler handle servers, network gear, and lab equipment together
They can, but you shouldn't assume the workflow is the same for all three. Servers may require rack deinstallation and stricter serial tracking. Networking equipment may be lower risk unless it contains storage. Laboratory and medical equipment can involve regulated data, specialty components, or internal release procedures. Put each asset category in the scope document before pickup is scheduled.
Is deleting files enough before recycling a computer
No. Deleting files or reformatting a drive isn't the same as certified destruction or NIST-aligned sanitization. If the device came from a business environment, especially one handling employee, customer, patient, or research data, use a documented destruction method and require proof afterward.
What should a small business prepare before pickup
Start with a simple internal list. Separate working devices from dead ones. Identify anything that contains storage media. Remove equipment that isn't approved for release yet. Name one person to authorize the handoff. Those steps prevent confusion and make the vendor's inventory process more accurate.
What if we have equipment spread across multiple Houston locations
Use one project owner and one reporting standard. Multi-site pickups fail when every location follows a different process. Ask the recycler how they reconcile inventory from separate offices and whether final reports can be delivered in a format your team can use.
Should we prioritize resale value or destruction certainty
Start with risk, then consider value. Assets that can be sanitized under your policy may be candidates for remarketing or reuse. Assets with higher sensitivity, failed media, or stricter regulatory requirements should usually move to destruction first. Value recovery is useful, but only after the security decision is settled.
If you're planning a refresh, a data center cleanup, or a regulated equipment retirement, Dallas Fortworth Computer Recycling can help you build a secure, auditable ITAD process that fits your environment. Their team supports B2B and public-sector organizations with nationwide pickup coordination, certified data destruction, responsible electronics recycling, and clear chain-of-custody documentation. Contact them to review your asset mix, define the right disposition path, and get a practical plan for retiring technology without exposing your organization to unnecessary risk.
