A Practical Guide to Data Center Equipment Recycling
Retiring old data center hardware isn't just a cleanup job—it's a critical business operation loaded with risk and opportunity. When you approach data center equipment recycling strategically, what seems like a complex chore can become a secure, compliant, and even profitable process. This guide is your playbook for getting it right.
Beyond Disposal: Why Data Center Recycling Is a Core Strategy

Moving on from legacy data center assets is no longer a simple matter of hauling them away. In a world governed by strict data privacy laws like GDPR and complex environmental regulations, a casual approach is a recipe for disaster. IT leaders I talk to are constantly worried about a data breach from a single misplaced hard drive or the sheer logistical nightmare of a full-scale decommissioning.
Many organizations underestimate just how big this job is. It’s so much more than unplugging servers. A proper decommissioning requires a coordinated effort across security, finance, legal, and facilities management. Every single step, from the initial inventory to the final certificates of destruction, has to be meticulously planned and documented.
The New Rules of IT Asset Disposition
The conversation around technology retirement has completely changed. It’s not just about getting rid of old gear anymore. Modern data center equipment recycling is a strategic function that has to balance several key goals:
- Absolute Data Security: You have to ensure that every byte of sensitive corporate and customer data is verifiably destroyed, with zero chance of recovery.
- Regulatory Compliance: Meeting all local, national, and international standards for both data privacy and environmental protection is non-negotiable.
- Financial Return: You need to identify assets that still have market value and recover that capital through secure remarketing channels.
- Environmental Responsibility: Preventing hazardous e-waste from hitting landfills and supporting a circular economy is now an expectation.
Failing in any one of these areas can lead to massive financial penalties, serious reputational damage, and legal trouble. This is why you have to treat equipment recycling as a core business strategy, not an afterthought.
A successful decommissioning project hinges on treating retired assets with the same level of security and accountability as your active production hardware. The chain of custody must be unbreakable from the moment a server is unplugged to the moment its components are responsibly recycled or destroyed.
Understanding the Global E-Waste Challenge
The sheer volume of electronic waste makes responsible action more critical than ever. The global e-waste problem has reached a staggering scale, with 62 million metric tonnes generated in 2022 alone—that’s an 82% increase from 2010. To put that in perspective, this annual waste would fill about 1.55 million 40-tonne trucks, enough to form a bumper-to-bumper line wrapping around the entire equator. The world is on track to produce 82 million tonnes by 2030.
For IT directors, grasping this scale is critical when evaluating your organization's environmental footprint and choosing a recycling partner. You can learn more about these global e-waste trends in the full report.
Partnering with a certified IT Asset Disposition (ITAD) provider is the most effective way to navigate these complexities. These specialists have the expertise and infrastructure to manage the entire lifecycle of your retired assets securely and sustainably. For organizations looking for a reliable partner, visiting an established electronics recycling center can provide valuable insight into the processes that ensure compliance and protect your brand.
Laying the Groundwork: Your Decommissioning Blueprint
Every successful data center decommissioning starts long before a single server is unplugged. It begins with a meticulous plan. Think of this as the architectural blueprint for the entire project. Without it, you're essentially flying blind through a high-stakes process, opening the door to data breaches, compliance failures, and logistical nightmares. A solid plan ensures every move is deliberate, documented, and secure from start to finish.
The absolute foundation of this blueprint is a comprehensive asset inventory. And I don't mean a simple count of racks and servers—that's not nearly enough. You need granular, serialized detail on every single piece of equipment slated for retirement.
Conduct a Granular Asset Inventory
A vague inventory list like "50 servers, 20 switches" is a recipe for disaster. To properly manage risk and recover asset value, your inventory has to be specific.
For each and every asset, you need to capture:
- Asset Tag and Serial Number: These are the unique identifiers that anchor your entire chain of custody.
- Make, Model, and Configuration: Details like CPU type, RAM amount, and storage capacity are what determine potential resale value.
- Physical Location: Document the specific rack and U-position. This is crucial for a smooth and efficient de-installation process.
- Data Sensitivity Level: Classify each data-bearing device (HDDs, SSDs, etc.) as containing confidential, internal, or public data. This dictates the exact data destruction method required.
This level of detail is non-negotiable. It's what allows your IT Asset Disposition (ITAD) partner to give you an accurate quote, plan the right data destruction services, and maintain an audit trail that will stand up to scrutiny.
Here's the rule of thumb I live by: if you can't track an individual asset by its serial number from its spot in the rack all the way to its final certificate of destruction, you have a security gap. And that gap is exactly where data breaches happen.
Assemble Your Internal Stakeholder Team
A data center decommissioning isn't just an IT project; it's a full-blown business operation. Trying to run it solely out of the IT department is a classic mistake that often leads to getting sandbagged by legal, finance, or security teams later on. The smart move is to assemble a dedicated internal team from day one to get everyone aligned.
Your core team should have a representative from:
- IT Infrastructure: They’ll oversee the technical de-racking and shutdown procedures.
- IT Security: Their job is to sign off on data destruction methods and ensure you're following internal security policies to the letter.
- Finance/Asset Management: They need to track asset depreciation, handle the financial write-offs, and oversee any revenue coming back from resold equipment.
- Legal and Compliance: They’ll make sure the whole process adheres to regulations like GDPR or HIPAA and will review all your vendor contracts.
- Facilities Management: This team coordinates physical access, power-down sequences, and all the on-the-ground logistics within the data center.
Hold a formal kickoff meeting with this group. Aligning on goals, timelines, and responsibilities right from the start prevents those last-minute surprises and ensures everyone knows exactly what their role is in protecting the company.
Vet Your Certified ITAD Partner
Once your inventory is tight and your internal team is in place, it’s time to bring in a certified ITAD partner. This is not a vendor you choose based on the lowest bid. You are literally entrusting them with your company’s sensitive data and its reputation.
When you're vetting potential partners, you need to ask targeted questions to define the project scope and verify their credentials. A qualified partner should be able to clearly walk you through their processes for data destruction, logistics, and reporting.
Critically, look for key industry certifications like R2 or e-Stewards. These aren't just logos; they are third-party proof of a vendor's commitment to environmental responsibility and data security. Understanding the nuances of corporate e-waste solutions is vital, and a true partner will help you navigate compliance while maximizing your asset value.
When you define the project's scope of work, insist on absolute clarity. The formal agreement should detail everything from pickup schedules and on-site procedures to the exact documentation you’ll receive when the job is done. This blueprint—built on a detailed inventory, an aligned internal team, and a thoroughly vetted partner—is what transforms a daunting project into a manageable, secure, and successful one.
Mastering Secure and Verifiable Data Destruction
When it comes to decommissioning data center hardware, this is the stage where your company’s reputation is squarely on the line. A single server or hard drive leaving your control without proper data sanitization can lead to a catastrophic breach.
Successful data destruction isn't just about deleting files; it's about making that data forensically unrecoverable and having the documentation to prove it.
The two main paths are software-based wiping and physical destruction. Neither one is universally better—the right choice depends entirely on the type of media, its data sensitivity, and the asset's end-of-life plan. Getting this distinction right is fundamental to any secure data center equipment recycling strategy.
Choosing Between Wiping and Shredding
Software-based data erasure uses specialized programs to overwrite every single sector of a drive with random data, often in multiple passes. When done according to standards like NIST 800-88, this method completely sanitizes the drive while keeping it physically intact. This makes it a great option for recovering value through reuse or resale.
Physical destruction, on the other hand, is exactly what it sounds like: rendering the media completely inoperable. This is usually done with industrial shredders that grind hard drives, SSDs, and tapes into small, unsortable fragments. For assets that held hyper-sensitive data or for media that can't be reliably wiped (like some damaged drives or older SSDs), shredding is often the only acceptable choice.
This decision tree can help guide that critical choice, showing how a detailed inventory informs your destruction strategy from the very beginning.
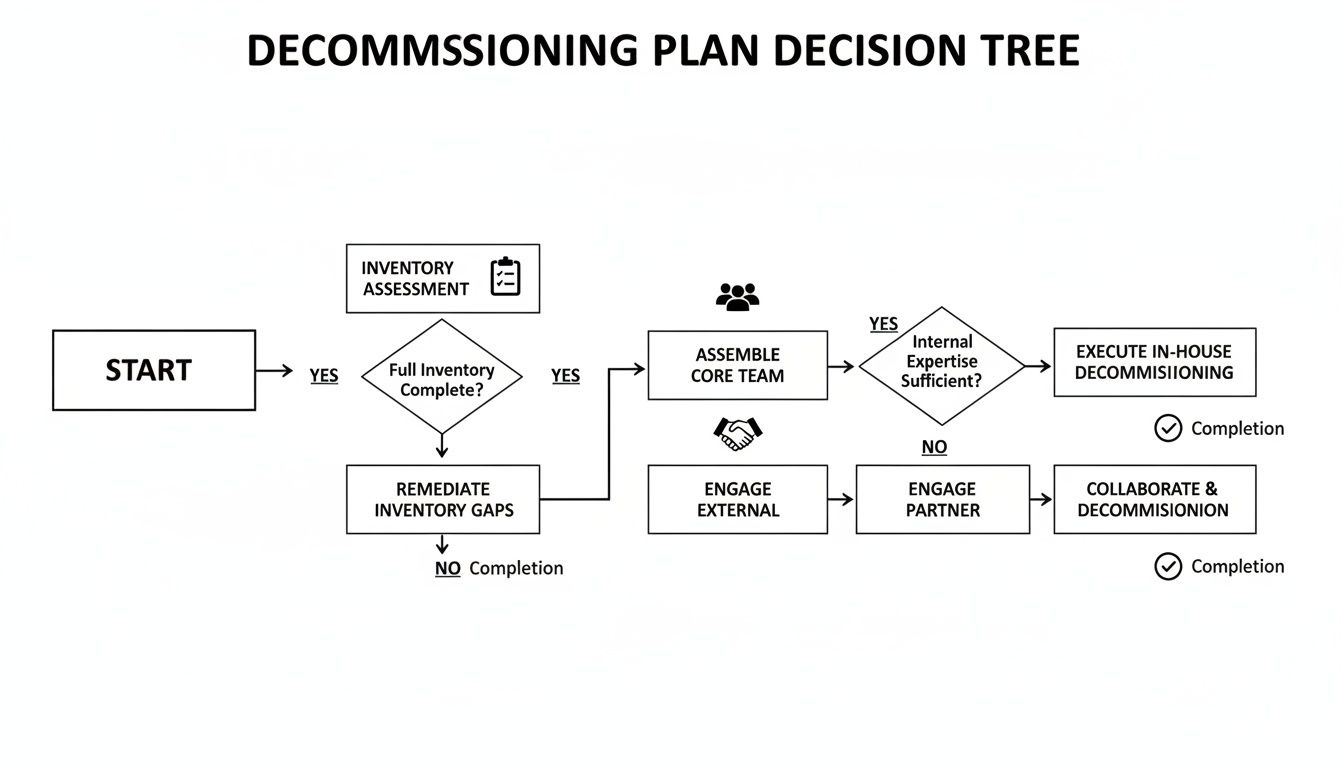
As the visual shows, a successful project is built on three pillars: a thorough inventory, an aligned internal team, and a vetted ITAD partner. Each step informs the next.
Comparing Data Destruction Methods
Deciding between wiping, shredding, or other methods requires a clear understanding of what each technique achieves. This table breaks down the most common options available for enterprise assets.
| Method | How It Works | Best For | Compliance Level | Key Consideration |
|---|---|---|---|---|
| Software Wiping | Overwrites all addressable storage locations with binary patterns (e.g., 0s, 1s, random) | HDDs and some SSDs intended for resale or reuse | High | Must use certified software (e.g., NIST 800-88 compliant) to be effective. |
| Physical Shredding | Grinds media into small, non-reconstructable pieces using industrial machinery | All media types, especially damaged drives, SSDs, and high-security assets | Highest | The only way to be 100% certain data is gone. Destroys all asset value. |
| Degaussing | Exposes magnetic media (HDDs, tapes) to a powerful magnetic field to erase data | HDDs and magnetic tapes | High | Ineffective on flash-based media like SSDs. Renders the drive inoperable. |
| Cryptographic Erase | Deletes the media's encryption key, rendering the encrypted data permanently inaccessible | Self-encrypting drives (SEDs) in both HDDs and SSDs | High | The fastest method, but relies entirely on the drive's encryption implementation. |
Ultimately, the goal is to select the method that aligns with your security policies, compliance needs, and asset value recovery goals. A good ITAD partner will help you apply the right method to the right asset.
Real-World Data Destruction Scenarios
Theory is one thing, but how does this play out in practice? Let's look at a couple of common data center situations.
-
Scenario A: The Leased Server Refresh
A company is retiring 200 servers with HDDs that are only three years old. The drives contain standard corporate financial data. Here, certified software wiping is the perfect fit. It securely erases all data, allowing the ITAD partner to test and resell the drives, generating a financial return that helps offset project costs. For a deeper look at the process, see our complete guide on how to wipe a hard drive for secure data removal. -
Scenario B: The Healthcare Data Migration
A hospital is decommissioning an old storage array that once held patient health information (PHI) on SSDs. Due to strict HIPAA regulations and the technical challenges of wiping SSDs completely, on-site physical destruction is non-negotiable. Witnessing the shredding provides an irrefutable layer of security and compliance assurance that auditors love to see.
The single most critical deliverable from any data destruction process is the Certificate of Destruction. This isn't just a receipt; it's a legally binding document that must list the unique serial number of every single drive that was sanitized or destroyed. Without this serialized proof, your audit trail is broken.
The Unbreakable Audit Trail
At the end of the day, your goal is to create an unbroken and auditable trail of custody and destruction for every single data-bearing asset. Your ITAD partner’s process has to be transparent and verifiable at every stage.
This means their technicians should scan each drive's serial number as it's removed from your facility and then reconcile that list against the final destruction report.
This serialized Certificate of Destruction becomes your ultimate proof of due diligence. It demonstrates to auditors, stakeholders, and regulatory bodies that you took every necessary step to protect sensitive information. If you ever face a legal challenge or an audit, this document is your definitive defense, proving your data center equipment recycling project was executed with the highest standards of security. Anything less introduces an unacceptable level of risk.
Securing the Chain of Custody from Rack to Recycling

Once the data is gone, the physical hardware still exists. And an asset is never more vulnerable than when it's on the move. This is where a rock-solid chain of custody becomes the absolute backbone of a secure data center equipment recycling project.
This isn't just about moving boxes. It’s about creating an unbroken, serialized audit trail for every single piece of gear, from the moment it’s un-racked in your facility to its arrival at the secure processing site. Any gap in that chain is a massive security and compliance risk waiting to happen.
On-Site Coordination and Secure Packing
The process starts right there in your data center aisles. The way equipment is de-installed and packed needs to be just as buttoned-up as any other IT operation. Just piling servers onto a pallet is a recipe for disaster—damaged equipment, lost assets, and a completely broken audit trail.
This is where a professional IT Asset Disposition (ITAD) team brings order to the chaos. Their technicians should be working directly from the serialized inventory list you already created. As each asset is pulled from the rack, it’s scanned, and its removal is logged in real time.
From there, security is all about the packing. And it’s a lot more than just shrink wrap.
- Custom Palletizing: Servers, switches, and storage arrays are methodically stacked to be stable and prevent any shifting during transit. Anti-static materials are a must to protect sensitive components.
- Protective Casing: For high-value or exceptionally fragile gear, you might see locked, hard-sided cases used instead of open pallets.
- Secure Sealing: Once a pallet is wrapped, it gets sealed with serialized, tamper-evident tape. That unique serial number on the tape is logged, making it impossible for the pallet to be opened and resealed without leaving obvious proof.
This disciplined on-site work ensures that what you think is leaving your facility is exactly what is leaving, with a digital record to back it up.
The Journey: A Bulletproof Transit Protocol
With everything packed and sealed, the focus shifts to secure transport. This is not your standard freight shipment. A reputable ITAD partner will use vehicles and protocols designed specifically for high-value, sensitive cargo.
The name of the game here is control. You want to eliminate every possible variable and unsupervised handoff. The industry standard is a dedicated, sealed truck. This means your assets are the only cargo on board, and that truck drives directly from your loading dock to the ITAD facility with no side trips.
Think of it like a sealed evidence bag. The moment that truck door is sealed at your facility, its integrity must be maintained until it's officially broken at the secure destination. This is the core principle of a physical chain of custody.
During transit, you should expect advanced security measures like:
- GPS Tracking: Real-time GPS gives both you and your ITAD partner eyes on the vehicle's exact location from start to finish.
- Dual-Driver Teams: For longer trips, using two drivers keeps the truck moving and ensures it's never left unattended.
- Geofencing Alerts: You can set up automated alerts to notify you if the truck deviates from its planned route for any reason.
These steps provide peace of mind and, just as importantly, a verifiable log of the asset's journey for any internal or external audits.
Reconciliation at the Secure Facility
The final link in the chain is the formal reconciliation at the ITAD partner’s secure receiving dock. When the sealed truck arrives, the very first step is for the receiving team to inspect the seal on the door. They verify its serial number against the one recorded at your facility. Any mismatch is an immediate red flag.
Once that seal is verified and broken, each pallet is unloaded. The serialized, tamper-evident tape on every pallet is also inspected before it’s cut. Technicians then unwrap the assets and scan the serial number of every individual server, switch, and drive.
This new list is meticulously compared against the original inventory list created back at your site. Every single asset must be accounted for. Only after this 100% reconciliation is confirmed does the equipment move on. This multi-point verification process is what makes the chain of custody truly secure. It’s the irrefutable proof you need that every asset you released was received, and it's a critical component of your final certificate of destruction for hard drives and overall project documentation.
Unlocking Asset Value and Ensuring Green Compliance
Once your data is gone for good and the chain of custody is locked down, the final stage of data center equipment recycling shifts to two key goals: clawing back financial value and proving your commitment to environmental responsibility.
This is where a seasoned IT Asset Disposition (ITAD) partner really shows their worth. They're not just about security and logistics; they're your value recovery engine. Not every piece of hardware you retire is scrap—a good portion of it still has a second life and real value on the secondary market.
A professional ITAD vendor works through a clear disposition hierarchy. They'll methodically test and grade every single asset, from servers and storage arrays to networking gear, figuring out what can be resold. This triage separates the valuable from the truly obsolete, setting a clear path for each item.
The ITAD Disposition Hierarchy in Action
Think of it as a strategic funnel for your old hardware. The entire goal is to push as much equipment as possible toward the top, which maximizes both your financial return and your positive environmental impact.
-
Remarketing and Resale: This is the top prize. Your partner will tap into their established sales channels to sell whole systems or valuable components like CPUs, RAM, and enterprise-grade SSDs. A transparent revenue-sharing model is non-negotiable here—it ensures you get a fair cut that can seriously offset your project costs.
-
Component Harvesting: Sometimes a server is too old to sell as a complete unit, but its parts are still in demand. In this case, technicians will harvest those valuable components. A single server might yield parts that are needed for repairs or upgrades on similar systems still in operation elsewhere.
-
Responsible Recycling: Only after every other option is off the table should an asset be sent for recycling. This is the final, responsible end-of-life path for equipment that has no functional or market value left.
This methodical approach is the bedrock of a successful project. For a closer look at how this all works, our guide on IT asset disposition services in Dallas Fort Worth, Texas breaks down the value recovery process in more detail.
The Critical Role of R2 and e-Stewards Certifications
When an asset has no resale value, your focus has to pivot to making sure it’s recycled responsibly. This is where partnering with a recycler holding top-tier certifications like R2 (Responsible Recycling) or e-Stewards is an absolute must.
These aren't just logos for a website; they are your guarantee that the vendor follows the strictest global standards for handling e-waste.
A certified partner ensures that hazardous materials like lead, mercury, and cadmium are managed safely and kept out of landfills. They're also audited regularly to prove that no e-waste is being illegally shipped to developing countries, protecting both the planet and your company's good name.
Choosing a partner without R2 or e-Stewards certification is like navigating the final, most critical stage of your project blindfolded. You lose all visibility and control over where your assets end up, exposing your organization to significant compliance and reputational risks.
The global e-waste problem is staggering. Despite the enormous volume, only 22.3% of e-waste was properly collected and recycled globally in 2022. That means roughly 77.7% of the world's electronic waste—containing an estimated US$62 billion in recoverable natural resources—is being dumped or improperly handled. Research has also shown that 12% of data centers don't do any e-waste recycling at all, while 43% don't have a formal environmental policy.
These numbers highlight why working with certified pros is the only way to ensure you're part of the solution, not the problem. You can find more insights about these data center recycling trends on human-i-t.org.
Demanding the Final, Essential Documentation
The project isn't finished until the paperwork is signed, sealed, and delivered. The final documentation from your ITAD partner is the ultimate proof of a job well done. It provides the auditable trail that your stakeholders, auditors, and compliance officers need to see.
Always insist on a comprehensive reporting package that ties up every loose end. This package should include:
-
A Final Asset Disposition Report: This is the master document. It should be a serialized report that details the final outcome for every single asset on your original inventory list, specifying whether it was resold, parted out, or recycled.
-
A Detailed Financial Settlement: For any gear that was sold, you need a transparent financial statement. It should clearly itemize the gross revenue generated, the agreed-upon revenue-sharing split, and your final net return.
-
Certificates of Recycling: Just like the Certificate of Destruction, this document confirms that all non-reusable assets were processed according to environmental regulations. It’s a key piece of evidence for your company's corporate social responsibility (CSR) efforts.
-
Environmental Impact Reports: The best partners can often provide reports that quantify the positive environmental impact of your project. Metrics like the total weight of materials diverted from landfills can be powerful data points for your company’s annual sustainability reports.
This complete documentation package provides definitive closure, proving that your data center equipment recycling project was secure, profitable, and environmentally sound from start to finish.
Your Data Center Recycling Questions Answered
Even the best playbook can’t cover every single question that pops up during a massive project like a data center decommissioning. IT leaders often run into the same practical questions, so we’ve put together a quick-reference guide to give you direct, no-nonsense answers.
Where Do We Even Begin with a Data Center Recycling Project?
The sheer scale can feel paralyzing. The only place to start is with a detailed, serialized asset inventory. You simply can't plan logistics, security, or value recovery until you know exactly what you have—down to the make, model, and serial number of every single server, switch, and drive.
Once you have that inventory, your very next call should be to a certified IT Asset Disposition (ITAD) partner. A good partner will work with you to build a formal Statement of Work (SOW) that maps out the entire project. This document locks down logistics, specifies data destruction methods for different types of gear, and clarifies what the final reporting will look like. Bringing a partner in early stops you from making expensive assumptions and makes the whole process run smoother.
What Is the Real Difference Between R2 and e-Stewards Certifications?
Both R2 (Responsible Recycling) and e-Stewards are the gold standards in the electronics recycling world. They are the top-tier, third-party audited certifications that prove a vendor is committed to doing things the right way, both ethically and environmentally.
Historically, there were some key distinctions. e-Stewards, founded by the Basel Action Network, has always held a hard line with a strict, absolute ban on exporting hazardous e-waste to developing nations. The R2 standard has evolved significantly and now has its own tough controls on downstream vendor verification and international shipments, bringing the two standards much closer in practice.
While having either certification is a great sign, a vendor that holds both R2 and e-Stewards certifications is making a powerful statement. It shows the highest possible commitment to responsible recycling, as they are voluntarily putting themselves through the toughest audits from both major governing bodies.
Can We Actually Make Money from Our Old Data Center Gear?
Yes, absolutely. For many companies, this is a primary goal of a well-run ITAD program. While your oldest servers or damaged equipment might just be worth their weight in scrap metal, a good chunk of your assets probably has significant value on the secondary market.
Here’s what often has strong resale value:
- Recent-generation enterprise servers: Gear that’s even three to five years old can still be in high demand.
- Networking hardware: High-end switches and routers from brands like Cisco or Juniper hold their value incredibly well.
- Storage systems and components: Enterprise-grade HDDs and SSDs are highly sought after once they've been securely sanitized.
- Individual components: Things like CPUs and high-density RAM modules are often harvested and sold on their own.
An experienced ITAD partner will have established global remarketing channels to get you the best possible return. You should expect a completely transparent revenue-sharing agreement that spells out exactly how the proceeds are split. This return can often offset—or even completely cover—the costs of the entire decommissioning project.
What Final Paperwork Is Absolutely Essential?
Once the last truck drives away, the project isn't truly over. Your final documentation is the auditable proof that you did everything right. For compliance, risk management, and any future internal audits, four documents are non-negotiable.
Your final reporting package must include:
- A serialized Certificate of Data Destruction: This is your proof that all data was wiped or destroyed securely. It has to list the unique serial number for every single data-bearing device.
- A complete chain-of-custody record: This paperwork tracks your assets from the moment they leave your facility to their final destination, proving an unbroken and secure handoff.
- A serialized Certificate of Recycling: This confirms that all non-reusable materials were processed in an environmentally compliant way, according to R2 or e-Stewards standards.
- A final asset disposition report: This is the master document. It reconciles the entire project, detailing the final outcome for every asset from your original inventory—whether it was resold, stripped for parts, or recycled.
This complete documentation package is your ultimate defense in an audit and the definitive record of a secure and responsible project.
Navigating the complexities of data center decommissioning requires a partner with proven experience and certified processes. Dallas Fortworth Computer Recycling provides nationwide, secure IT asset disposition services designed to protect your data, maximize value recovery, and ensure environmental compliance. Learn more about our secure data center services.
