The Ultimate Guide to Secure Shred and Recycle IT Disposal
When it comes to IT asset disposal, the term shred and recycle describes a critical two-step process. First, we physically destroy any device that holds data, making recovery absolutely impossible. Then, we take the remaining fragments and responsibly reclaim the raw materials.
This is the gold standard for securely and sustainably retiring old technology. It guarantees complete data security while preventing hazardous e-waste from ever reaching a landfill.
Decoding the Shred and Recycle Process

Think about how you handle a sensitive corporate document. You wouldn’t just toss it in the recycling bin where anyone could pull it out and read it. The first, non-negotiable step is to run it through a cross-cut shredder, turning it into useless confetti. Only then do the scraps go into the recycling stream.
The shred and recycle process applies that exact logic to your company's retired hard drives, servers, and smartphones. These devices are today's filing cabinets, often holding far more sensitive information than any paper document ever could. Just deleting files or reformatting a drive isn’t enough—that often just removes the pointers to the data, leaving the information itself recoverable with the right tools.
The Shredding Phase: Data Obliteration
The "shred" part is all about physical destruction, and we're not talking about taking a hammer to a hard drive. This involves industrial-grade machinery that grinds, pulverizes, and shears electronics into tiny, unsalvageable pieces. This process utterly destroys the storage platters, memory chips, and internal circuits where your data lives.
This step is your ultimate guarantee for compliance and risk management. For businesses governed by regulations like HIPAA or GDPR, physical destruction offers irrefutable proof that data has been permanently eliminated. It protects your organization from the catastrophic financial and reputational damage of a data breach.
The core principle is simple: data cannot be breached if the medium it was stored on no longer exists in a recoverable form. Physical shredding achieves this with 100% certainty.
The Recycling Phase: Material Recovery
Once we've verifiably destroyed the data, the "recycle" phase begins. The shredded material—a mix of aluminum, steel, plastic, and precious metals—is carefully sorted and processed. This is where environmental responsibility takes center stage.
Instead of ending up as toxic e-waste in a landfill, these valuable commodities are reintroduced into the manufacturing supply chain. This approach not only prevents hazardous materials like lead and mercury from polluting the environment but also reduces the need for new mining operations.
To help visualize this, here's a quick breakdown of how these two pillars work together to protect your business.
Core Components of a Secure Shred and Recycle Program
| Process Component | Primary Goal | Key Outcome for Your Business |
|---|---|---|
| Shredding (Physical Destruction) | Eradicate all data permanently. | Absolute data security, regulatory compliance, and total peace of mind. |
| Recycling (Material Recovery) | Responsibly reclaim raw materials. | Environmental stewardship, support for sustainability goals, and brand protection. |
This circular economy model is a cornerstone of modern corporate sustainability goals. To get a better sense of the complete lifecycle, you can learn more about what IT asset disposition entails and how it fits into your broader corporate strategy.
Ultimately, this integrated process turns a potential liability into a secure, compliant, and environmentally positive outcome for your organization.
Why E-Waste Demands a Shred and Recycle Strategy
Every business today is caught in a constant current of technology upgrades. The relentless pace means servers, laptops, and mobile devices have shorter lifecycles than ever, creating a massive global challenge: electronic waste, or e-waste. This isn't just some far-off environmental problem; it's an operational reality hitting every IT manager and data center operator right where they work.
The numbers are staggering. The world recently generated a massive 62 million tonnes of e-waste in a single year, an 82% increase since 2010. Worse, that figure is projected to climb another 32% to 82 million tonnes by 2030. What's truly alarming is that only 22.3% of this e-waste was properly collected and recycled—a rate that's expected to get even worse. You can get more details on this growing crisis from the Global E-waste Monitor 2024.
This tidal wave of old electronics makes a professional shred and recycle strategy essential. It's time to move beyond just "getting rid of it" to a secure, responsible, and documented process.
The Two-Sided Risk of Improper Disposal
When a company simply discards old electronics, it's walking into two major risks. First, there's the hidden danger of sensitive data left on hard drives and memory chips. Second, there are the hazardous materials locked inside the hardware itself. Both can lead to serious consequences.
Picture an old company server sitting in a dumpster. It's not just a box of metal and plastic. It's a potential goldmine for data thieves and a toxic time bomb for the environment. A professional shred and recycle program tackles both of these threats head-on.
A single discarded server can contain sensitive customer data, proprietary trade secrets, and employee information. At the same time, it may hold toxic substances like lead, mercury, and cadmium that can contaminate soil and water if left in a landfill.
Uncovering Hidden Value and Environmental Dangers
Beyond the risks, it's important to understand that e-waste is a paradox. Your retired IT assets are simultaneously a source of valuable materials and a collection of hazardous contaminants. A well-managed disposal process knows how to separate the good from the bad.
Here’s a look at what’s really inside that old equipment:
- Valuable Materials: Electronics are packed with precious metals like gold, silver, copper, and palladium. A professional recycling process recovers these resources, reducing the need for new mining operations and feeding them back into the circular economy.
- Toxic Elements: Those same devices contain harmful substances. Lead is common in circuit boards, mercury is used in LCD screens, and cadmium can be found in older batteries. These toxins pose serious health and environmental risks if not handled by a certified recycler.
Failing to manage these materials isn't just irresponsible—it's expensive. Environmental regulators can hit you with heavy fines for improper e-waste disposal. Even more damaging is the public backlash and hit to your brand's reputation when your company is tied to environmental contamination.
Adopting a formal shred and recycle program isn't just a compliance checkbox. It’s a core part of modern corporate responsibility that protects your data, your brand, and the planet. For businesses looking to build a secure and compliant process, exploring corporate e-waste solutions is the critical next step. This proactive approach turns a potential liability into a documented, secure, and sustainable business practice.
Ensuring Data Destruction and Verifiable Chain of Custody
When you're dealing with sensitive business data, "good enough" is a recipe for disaster. This is where the shred and recycle process becomes an absolute security mandate, especially for industries like finance, healthcare, and government. The "shred" part is non-negotiable, providing a definitive end to the data lifecycle that software-based solutions just can't guarantee.
Sure, software wiping tools can overwrite data, but they leave the physical drive completely intact. A determined actor could still potentially recover fragments of information. Physical destruction is the only failsafe. It’s the difference between erasing a whiteboard and smashing it into dust—one leaves room for error, while the other offers complete finality.
This level of certainty is precisely why standards like NIST 800-88 recognize physical destruction as the ultimate form of data sanitization. It removes all doubt and gives you concrete, verifiable proof of compliance.
The Unbreakable Chain of Custody
Real security doesn't start at the shredder; it begins the moment an asset leaves your control. This is where the Chain of Custody becomes the central pillar of any secure ITAD program. Think of it as the documented, unbroken trail your hardware follows from your facility to its final destruction.
This isn't just a handshake agreement. It’s a meticulous, auditable record that tracks every single touchpoint.
- Serialized Asset Tagging: Before anything leaves your premises, each device is individually tagged and logged.
- Secure, GPS-Tracked Logistics: Assets travel in locked, sealed vehicles that are monitored from pickup to delivery.
- Controlled Facility Access: The receiving facility must have strict security protocols, including surveillance and restricted access, to prevent unauthorized handling.
- Verified Destruction: The final act of shredding is witnessed, documented, and cross-referenced against the initial inventory list.
This documented process transforms a potential liability into a secure and defensible procedure—exactly the proof you need to satisfy auditors and regulators.
A weak link anywhere in the chain can invalidate the entire process. A verifiable Chain of Custody ensures there are no gaps where an asset could be lost, stolen, or mishandled, providing an unbroken line of accountability from start to finish.
The consequences of getting this wrong are severe. One study of IT professionals found that a staggering 68% of data breaches from discarded hardware stemmed from improper data sanitization. Organizations that merely deleted files were 4.5 times more likely to suffer a breach from retired assets. The study also revealed that 82% of these incidents involved a breakdown in Chain of Custody documentation, proving just how vital this step is. You can discover more insights about these critical IT security trends.
Your Proof of Compliance: The Certificate of Destruction
The final piece of a secure shred and recycle process is the Certificate of Destruction (CoD). This legal document is far more than a simple receipt; it’s your official, auditable proof that your data-bearing assets were destroyed in accordance with industry best practices and regulations like HIPAA, GDPR, and FACTA.
A legitimate CoD must contain specific details that will stand up to scrutiny:
- Unique Serial Numbers: A complete list of every single asset that was destroyed.
- Date and Location of Destruction: Pinpoints exactly when and where the shredding occurred.
- Method of Destruction: Specifies the process used, confirming it meets compliance standards.
- Authorized Signatures: Attestation from the certified vendor that the process was completed as described.
This document is your ultimate defense in an audit, proving you exercised due diligence. It closes the loop on your asset's lifecycle, providing the final piece of the accountability puzzle. If you want to take a deeper dive, you can learn more about what a comprehensive Certificate of Destruction for hard drives should include.
By pairing physical destruction with an ironclad Chain of Custody, you create a fully defensible and secure IT asset disposition strategy.
The Hidden Value in Your Retired Electronics

Once the shredder has done its job and your data is permanently destroyed, the story isn't over. This is where the powerful "recycle" part of the shred and recycle process takes center stage, turning what many see as a liability into a real asset. Too many organizations view IT disposal as a pure cost, but a smart approach uncovers significant financial and environmental returns.
Those shredded fragments of old servers, laptops, and networking gear aren't junk. They're a rich source of raw materials—a collection of plastics, steel, aluminum, and even precious metals. This is where the idea of "urban mining" comes to life. Instead of digging new resources out of the earth, we reclaim them from the technology we've already built.
From E-Waste to Valuable Commodities
The recycling phase is a highly sophisticated sorting operation. Powerful magnets pull out ferrous metals like steel, while eddy currents separate non-ferrous metals such as aluminum and copper. Advanced optical sorters can even identify and segregate different types of plastics. Each material stream is then cleaned, processed, and bundled for sale.
These reclaimed materials are in high demand and are sold directly into global manufacturing supply chains. The aluminum from an old server chassis might become part of a new car. The copper from its wiring could be used in construction. It's a circular flow that powers a more sustainable economy.
By treating retired electronics as a resource instead of waste, your organization directly contributes to a more sustainable supply chain. This process conserves natural resources, reduces energy consumption, and significantly lowers greenhouse gas emissions compared to traditional mining.
This economic engine is growing fast. The global electronics recycling market, driven by secure shredding, is currently valued at USD 43.2 billion. It's projected to skyrocket to USD 147.9 billion by 2035, a clear sign of the massive economic potential in systematic shred and recycle programs. This growth is fueled by enterprises seeking compliant ITAD solutions, especially as unrecycled e-waste has left an estimated $62 billion in valuable metals untapped. You can find more details in this in-depth electronics recycling market report.
Turning a Cost Center into a Revenue Stream
Beyond just recovering raw materials, there's another layer of value to uncover. Not every component that enters an ITAD facility is destined for the shredder. Some assets, or their internal parts, may still hold significant resale value. A certified shred and recycle partner is an expert at identifying these opportunities for remarketing.
This is where your IT disposal program can shift from an expense line to a revenue generator.
- Component Harvesting: Functional parts like RAM, CPUs, and power supplies can be tested, certified, and resold on the secondary market.
- Asset Refurbishment: Entire devices that are not data-bearing or have been securely sanitized can be refurbished and given a second life.
- Revenue Sharing Agreements: Reputable vendors often offer a revenue-sharing model, where your organization receives a percentage of the profits generated from selling these components.
This approach creates a compelling return on investment that resonates with procurement managers and CFOs alike. It reframes the entire disposal process, proving that responsible IT asset management isn't just good for compliance and the environment—it's also good for the bottom line. If your organization wants to get started, it’s wise to learn more about professional computer equipment recycling to maximize these returns.
How to Choose the Right Shred and Recycle Partner
Choosing an ITAD vendor isn't just a procurement task; it’s a critical security and compliance decision. The partner you trust with your retired assets is also trusted with your organization's reputation. One wrong move can lead to a data breach or environmental fines, making a thorough vetting process for any shred and recycle service absolutely essential.
Think of it like hiring an armored car service to transport valuables. You wouldn't pick the cheapest option without first checking their credentials, security protocols, and track record. The same level of diligence is required when your company's sensitive data is the asset being moved and destroyed.
This process ensures your partner isn't a liability but a documented, secure extension of your own operations.
Look for Industry-Leading Certifications
Certifications are the fastest way to sort qualified vendors from potential risks. They act as independent, third-party proof that a company meets the highest industry standards for security, environmental responsibility, and operational excellence. Don’t just take a vendor's word for it; ask for proof of their credentials.
Key certifications to look for include:
- NAID AAA Certification: This is the gold standard for secure data destruction. It confirms a vendor’s hiring practices, operational security, and destruction processes are rigorously audited through unannounced inspections. It’s a non-negotiable for any business serious about data security.
- R2 (Responsible Recycling) Certification: This standard focuses on environmentally sound practices, proper e-waste management, and worker safety. It ensures your assets won’t be illegally exported or dumped in a landfill.
- e-Stewards Certification: Often seen as the most stringent environmental standard, e-Stewards has a zero-tolerance policy for exporting hazardous e-waste to developing countries.
These credentials provide a solid baseline of trust. To learn more, you can explore what it means to be an R2 certified electronics recycler and the strict standards involved.
Scrutinize Security and Reporting Protocols
Beyond certifications, you need to dig into a partner's day-to-day operational security. A truly secure shred and recycle process is built on a foundation of strict controls and transparent documentation, creating an unbreakable chain of custody from the moment assets leave your facility.
A vendor's security is an extension of your own. Gaps in their process become direct risks to your organization, making it crucial to verify everything from employee background checks to facility surveillance.
Your evaluation must include a close look at their reporting capabilities. Vague, summary-level reports are a major red flag. A reliable partner provides detailed, serialized documentation that can stand up to any audit.
Before signing a contract, ask for a practical checklist to help evaluate and select a secure and compliant ITAD partner.
Vendor Vetting Checklist for Shred and Recycle Services
Use this checklist to systematically evaluate potential ITAD vendors. A strong partner will be able to provide clear, confident answers and documentation for each of these points.
| Evaluation Criteria | What to Look For | Why It Matters |
|---|---|---|
| Certifications | NAID AAA, R2, and/or e-Stewards. Ask for current certificates. | Third-party validation of security, environmental, and safety standards. |
| Chain of Custody | Detailed, serialized tracking from pickup to final disposition. | Creates an auditable trail for every asset, proving secure handling. |
| Secure Logistics | Locked, GPS-tracked vehicles; vetted, uniformed drivers. | Prevents in-transit theft or loss, which is a common point of failure. |
| Facility Security | Controlled access, 24/7 video surveillance, and secure storage areas. | Protects your assets from unauthorized access while awaiting processing. |
| Employee Screening | Rigorous background checks and ongoing security training for all staff. | The people handling your data must be trustworthy and properly trained. |
| Reporting & Documentation | Detailed Certificates of Destruction (CoD) linked to serial numbers. | Provides irrefutable proof of data destruction for compliance and audits. |
| Downstream Vendor Audits | A documented process for vetting their own recycling partners. | Ensures your e-waste is handled responsibly throughout the entire recycling chain. |
| Insurance Coverage | Adequate liability and data breach insurance. Ask for their certificate. | Protects your organization financially in the event of an incident. |
A partner who can confidently check all these boxes is one you can trust. They demonstrate a commitment to security and compliance that goes beyond surface-level promises.
Finally, consider their logistical flexibility. Your IT asset retirement needs can range from a few pallets of laptops to a complete data center decommissioning. A capable partner should be able to scale their services for different equipment loads and complex projects without ever compromising security or efficiency. Choosing the right one empowers you to manage risk and protect your organization’s most valuable information.
Putting Your IT Asset Disposal Plan into Action
Taking a well-designed ITAD strategy off the whiteboard and into the real world can feel like a huge undertaking. But with a structured approach, the whole process becomes manageable, secure, and completely transparent. The goal here is to turn your plan into action, ensuring every step protects your organization and gives you total peace of mind.
This process starts internally, long before a truck ever shows up at your door. The first move is to get all the key stakeholders on the same page. Bring together leaders from IT, finance, legal, and facilities management so everyone understands their role and the importance of a secure shred and recycle program. Getting everyone aligned from the start prevents logistical headaches and ensures compliance requirements from every department are covered.
Kicking Off Your Disposal Project
Once your internal team is in sync, it’s time to create a detailed inventory of the assets you’re retiring. This isn't just a simple headcount; it’s a critical step for building your chain-of-custody documentation. Every single device—from servers in a data center to laptops collecting dust in a storage closet—needs to be logged with its serial number, asset tag, and physical location. An accurate inventory is the bedrock of an auditable disposal process.
With your asset list ready, you can now engage your chosen ITAD partner to schedule a secure pickup. They’ll work with you to plan the logistics, making sure their team arrives with the right equipment and personnel to handle your specific needs safely and efficiently. This coordination is key to keeping any disruption to your daily operations at a minimum.
This visualization breaks down the high-level process for vetting a qualified partner who can handle these critical steps.
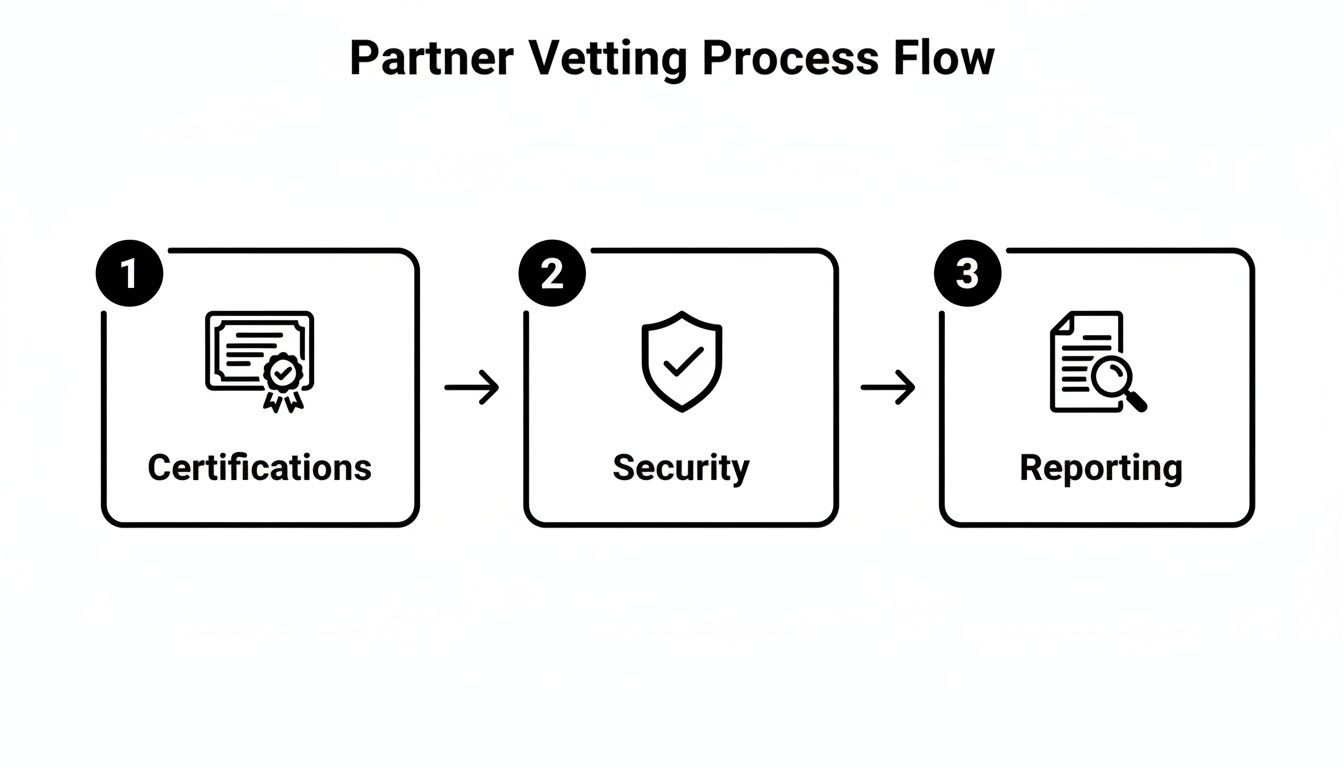
The flow from verifying certifications to confirming security protocols and reporting capabilities is what forms the foundation of a partnership you can actually trust.
From Pickup to Final Certification
On pickup day, the ITAD provider's vetted and uniformed staff will securely pack and transport your assets. They should be using sealed, GPS-tracked vehicles to maintain an unbroken chain of custody from your facility to theirs. This is where all those security measures you verified during the selection process really prove their worth.
As soon as your assets arrive at the processing facility, they are checked and reconciled against the inventory list you provided. Only then does the destruction and recycling begin. Data-bearing devices are physically destroyed according to the agreed-upon standards, and the remaining materials are responsibly recycled, with commodities being sorted and sent back into the manufacturing stream.
The final, and arguably most important, step is receiving the documentation that closes the loop. A detailed Certificate of Destruction, linked to the serial numbers of your specific assets, is your official proof of compliance and secure data elimination.
This final report is much more than a receipt—it's an auditable record that demonstrates your organization’s due diligence. It confirms that your retired IT hardware was managed securely, responsibly, and in full accordance with all relevant regulations. This is the comprehensive documentation that provides definitive assurance that your ITAD plan was successfully executed, protecting both your data and your reputation.
Common Questions About Shred and Recycle Services
Even after you understand the process, a few practical questions always come up when you start planning an IT asset disposition project. Getting clear answers to these common queries helps nail down the details and builds confidence that you're picking the right shred and recycle partner.
We've designed these answers to give IT managers and compliance officers the direct, actionable information they need.
First, people often ask what kinds of equipment we can actually handle. The short answer is: just about anything electronic. A certified ITAD provider processes far more than just old computers and servers. We’re talking about networking gear like routers and switches, all those company mobile phones, printers, and even specialized medical or lab equipment that holds sensitive data. If it has a memory chip or a storage drive, it’s a candidate for secure destruction.
Another big question is always about the logistics of on-site versus off-site shredding.
- On-site Shredding: This is where a mobile shredding truck comes right to your facility. You can literally stand there and watch your assets being destroyed, which offers the ultimate peace of mind. It’s the go-to choice for organizations with highly sensitive data that can’t leave the building intact.
- Off-site Shredding: Your assets are loaded into a locked, GPS-tracked vehicle and securely transported to the vendor’s certified facility for destruction. As long as it’s backed by an unbroken chain of custody, this method is just as secure and is often more practical and cost-effective for larger jobs.
Both options are completely secure. The right choice really just depends on your company's security policies and budget.
Addressing Cost and Value Recovery
Naturally, IT leaders need to know, "What's this going to cost, and can we get any money back?" The price for a shred and recycle service depends on the volume and type of gear, how complex the logistics are, and whether you need on-site or off-site services. But it's important to see this as an investment in risk mitigation, not just a cost. The expense is tiny compared to the multi-million-dollar fines and reputational damage that follow a data breach.
As for getting some value back? The answer is often a resounding yes.
A professional ITAD partner doesn't just destroy things; they assess your retired assets for any remaining market value. Functional components like CPUs, memory, and even entire systems can be harvested and resold. Most reputable vendors offer a revenue-sharing agreement that puts a portion of those proceeds right back in your pocket.
This can seriously offset the program's costs, turning what looks like a disposal liability into a real revenue opportunity. It’s a perfect example of how choosing a partner who’s great at both secure destruction and smart remarketing pays off.
Ready to implement a secure, compliant, and sustainable ITAD program? Dallas Fortworth Computer Recycling offers nationwide services with certified data destruction and a proven chain of custody to protect your organization's most sensitive information. Learn more and schedule your secure electronics disposal at https://dallasfortworthcomputerrecycling.com.
