Data Center ITAD: A Complete Enterprise Guide
A data center decommissioning project rarely starts clean. It usually starts with pressure.
A lease is ending. A cloud migration is finally real. A hardware refresh that looked manageable on a spreadsheet turns into rows of retired servers, storage shelves, loose drives, network gear, and a compliance team asking one question over and over: how do we prove every asset was handled correctly?
That’s where data center itad stops being a back-office disposal task and becomes an operational control. If you’re responsible for a shutdown, consolidation, or phased refresh, you’re not just clearing floor space. You’re closing the last chapter of each asset’s lifecycle without creating a new problem in the form of data exposure, audit gaps, or avoidable asset loss.
The End of the Line A New Beginning
The typical scene is familiar. One part of the facility is still live. Another is half-decommissioned. Pallets are being staged. Engineers are focused on uptime for the environment that remains. Procurement wants updates on recovered value. Legal wants documentation. Security wants certainty.
That’s exactly why data center itad has to be treated as a managed project, not a cleanup exercise.
The market itself reflects that shift. The global Data Center IT Asset Disposition market is projected to grow from approximately USD 14.21 billion in 2026 to USD 25.46 billion by 2035, driven by digital transformation, frequent refresh cycles, and the need for secure, compliant retirement of assets such as servers, HDDs, CPUs, and SSDs, according to Business Research Insights coverage of the data center ITAD market.
What the operator is actually dealing with
A decommissioning project looks physical on the surface, but the hardest parts are usually invisible:
- Hidden data exposure: retired hardware often contains more sensitive data than teams remember
- Documentation risk: if asset tracking breaks, proof breaks with it
- Workflow conflict: facilities, infrastructure, compliance, and finance often want different outcomes
- Timing pressure: production timelines rarely leave room for rework
That’s why smart operators build a formal runbook before the first rack comes apart. A disciplined data center decommissioning process gives structure to what would otherwise become a chain of improvised decisions.
Practical rule: If your team is discussing trucks, pallets, or recycling before it has a serial-level asset plan, the project is already off course.
Why ITAD changes the outcome
Professional ITAD gives you a framework for handling the end of life of technology with the same rigor used to deploy it. Assets are identified, moved under custody controls, sanitized with approved methods, evaluated for remarketing where appropriate, and documented for audit defense.
That’s the new beginning part.
A retired server isn’t just waste. It’s a liability until it’s processed correctly. It may also be a recoverable asset if the right sanitization and testing path is chosen. Good ITAD recognizes both realities at once. It protects the organization while preserving legitimate residual value wherever policy allows.
When operators miss that balance, they usually swing too far in one direction. Some overspend on destruction where secure erasure and resale would have been acceptable. Others chase recovery and weaken controls. Mature programs don’t do either. They decide asset by asset, based on risk, policy, and evidence.
What Data Center ITAD Really Means
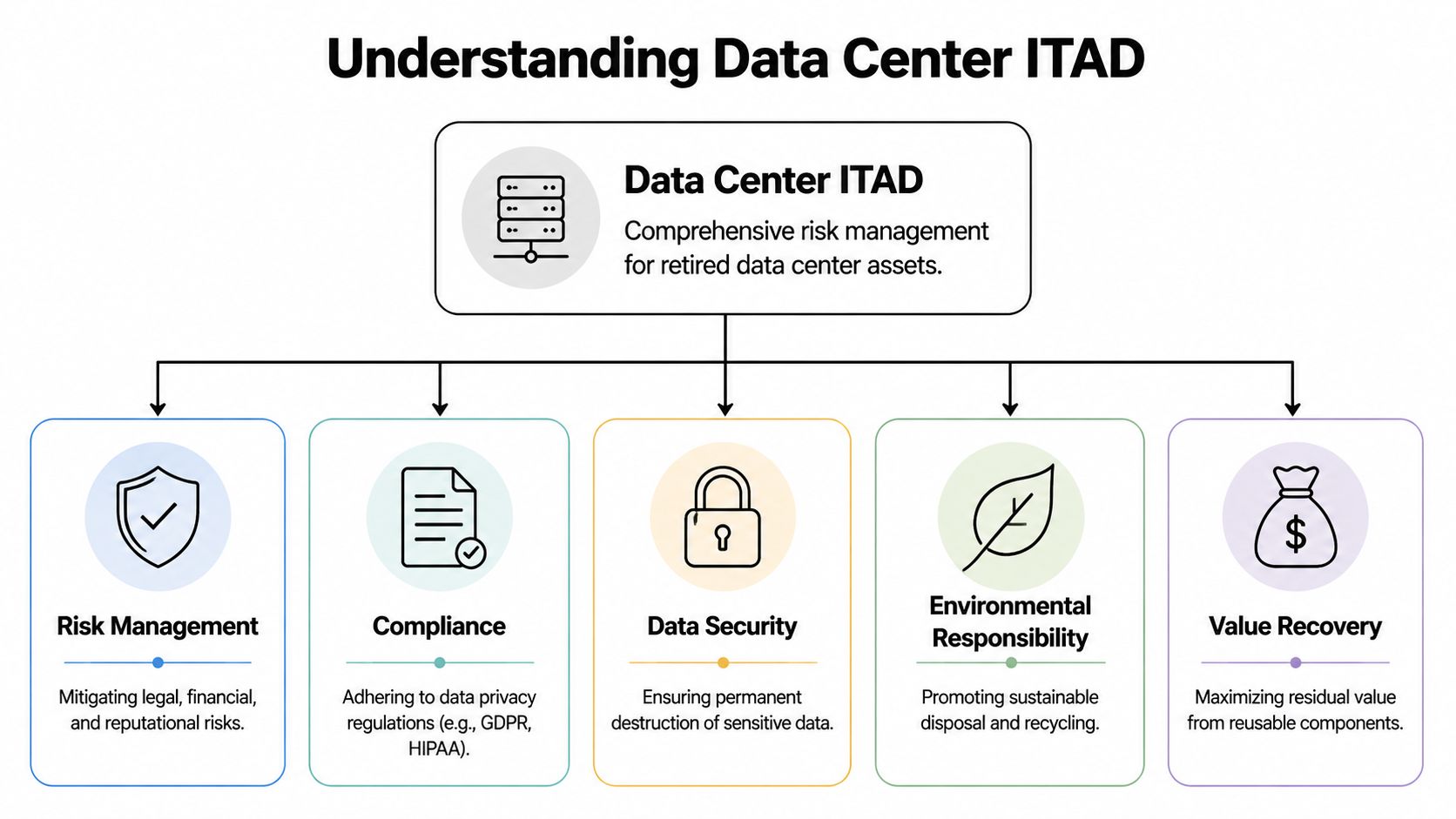
People still use ITAD as if it means “pickup and recycle.” In a data center environment, that definition is far too small.
Data center itad is a control system for retiring technology without losing custody, data security, compliance evidence, or recoverable value. It’s closer to the audited closure of a vault than to ordinary office cleanout work.
The difference between ITAD and basic e-waste pickup
Basic recycling vendors answer one question: how do we remove this equipment?
Enterprise ITAD has to answer a much harder set of questions:
- Who touched each asset
- Where each device was at each handoff
- How data was sanitized or destroyed
- Which assets were fit for reuse or remarketing
- What happened to non-recoverable material downstream
- What evidence can be produced during an audit
That’s why a serious ITAD provider doesn’t just arrive with a truck. The provider arrives with intake controls, manifest discipline, secure logistics, processing standards, and reporting that can survive legal and regulatory scrutiny.
If you need a plain-language baseline, this overview of what IT asset disposition means in practice is a useful starting point.
What enterprise-grade work includes
At minimum, competent data center ITAD should cover these operating functions:
| ITAD function | What good looks like |
|---|---|
| Asset inventory | Serial-level logging, condition capture, and reconciliation |
| Secure removal | Controlled de-racking, packaging, staging, and transport |
| Data handling | Approved sanitization or destruction matched to media type |
| Value recovery | Testing, grading, and remarketing where policy permits |
| Recycling | Responsible processing for non-reusable components |
| Documentation | Complete certificates, disposition reports, and chain-of-custody records |
What works and what fails
What works is a process built around control first, monetization second.
What fails is the scrap mentality. That model usually looks cheaper at the beginning because it skips disciplined inventory, detailed reporting, and media-specific handling. Then the full costs become evident. Missing serial numbers. Mixed lots. Drives separated from their parent assets. No defensible certificate trail. No credible answer when an auditor asks how a specific device was processed.
The easiest way to lose control of a decommissioning project is to let assets turn into bulk material too early.
There’s also a financial misunderstanding that hurts many teams. Remarketing isn’t the opposite of security. Done correctly, it follows security. Assets are sanitized first, verified, then tested for reuse potential. If they don’t qualify, they move to destruction or material recovery. The sequence matters.
The operating mindset that matters
The best data center teams treat ITAD like any other high-impact infrastructure change. They define scope. They assign ownership. They separate live equipment from retired equipment. They control handoffs. They insist on evidence.
That mindset is what turns retired hardware from a loose end into a closed loop.
Navigating the Minefield of Risks and Regulations
The reason data center ITAD gets complicated fast is simple. A decommissioning project combines several kinds of risk in the same event. Data risk, legal risk, environmental risk, and operational risk all sit in the same pile of hardware.
When teams underestimate that, they usually focus on removal speed and leave the difficult questions for later. Later is where most problems become expensive.
Data exposure is the first failure mode
One server with incomplete sanitization can create a problem that extends far beyond the hardware itself. The risk isn’t limited to customer records. Retired systems often contain credentials, internal documentation, backup fragments, API keys, architecture details, and administrative histories that attackers or investigators would find useful.
A failed ITAD event also tends to multiply internally. Security has to investigate. Legal has to assess notification obligations. Compliance has to reconstruct evidence. Infrastructure staff get pulled into a disposal issue long after the migration or shutdown should have been finished.
That’s why mature operators decide early which assets can be sanitized for reuse and which require irreversible destruction. They don’t let that call happen ad hoc at the dock door.
Compliance gets stricter as the environment gets more sensitive
Healthcare, finance, and public-sector teams already know that retired hardware remains a compliance concern until final disposition is documented. The difficult part is that requirements are rarely satisfied by a generic “destroyed” statement. Auditors want traceability, method, dates, custody continuity, and proof that the process matched policy.
This becomes much tighter in defense-related environments. Defense-sector ITAD engagements require mandatory compliance with ITAR and DFARS standards, necessitating vendors to maintain physically segregated workflows and documentation streams to prevent cross-contamination of export-controlled data, as described in Securis guidance on government ITAD compliance requirements.
That single requirement changes facility design, transport planning, handling procedures, and documentation discipline. A vendor that’s fine for ordinary commercial retirements may be completely unsuitable for defense-adjacent work.
Environmental liability is real, even when the data risk is managed
A common mistake is to think the project is complete once media has been destroyed. It isn’t.
You still need responsible downstream handling for boards, metals, plastics, batteries, cabling, and unusable components. If a vendor is vague about where material goes after primary processing, that’s a procurement problem, not a minor detail.
A useful way to think about risk categories is this:
- Security risk: data remains accessible or sanitization can’t be proven
- Regulatory risk: records don’t satisfy the standards your auditors expect
- Environmental risk: downstream material handling isn’t transparent or responsible
- Operational risk: project delays, mixed inventories, and custody breaks disrupt the shutdown
If your vendor can explain destruction equipment in detail but gets fuzzy about documentation or downstream flows, keep looking.
Where operators usually go wrong
Most failed decommissioning projects don’t fail because the team didn’t care. They fail because control points were too loose.
Common examples include:
Bulk packing before reconciliation
Once assets are mixed before serial confirmation, proving completeness becomes harder.Separating drives from asset records
Media may be destroyed correctly, but if the record trail breaks, compliance still suffers.Using one rule for every asset
Not every device needs the same treatment. Some warrant shred-only handling. Others can move through secure erasure and resale.Treating ITAD as a facilities handoff
Facilities matters, but infrastructure, security, and compliance all need signoff points.
The practical response
Build a decommissioning workflow that assumes scrutiny later. That means approved methods, restricted access, documented exceptions, and clear authority over every handoff.
Good ITAD doesn’t remove risk entirely. It makes risk visible, controlled, and defensible.
A Guide to Secure Data Destruction Methods
Data destruction is where many decommissioning projects become binary in people’s minds. Wipe it or shred it. In practice, the choice is more nuanced than that.
The right method depends on the media type, your internal policy, the sensitivity of the data, reuse goals, and how much verification you need. If the method doesn’t fit the device, you either create unnecessary cost or false confidence.
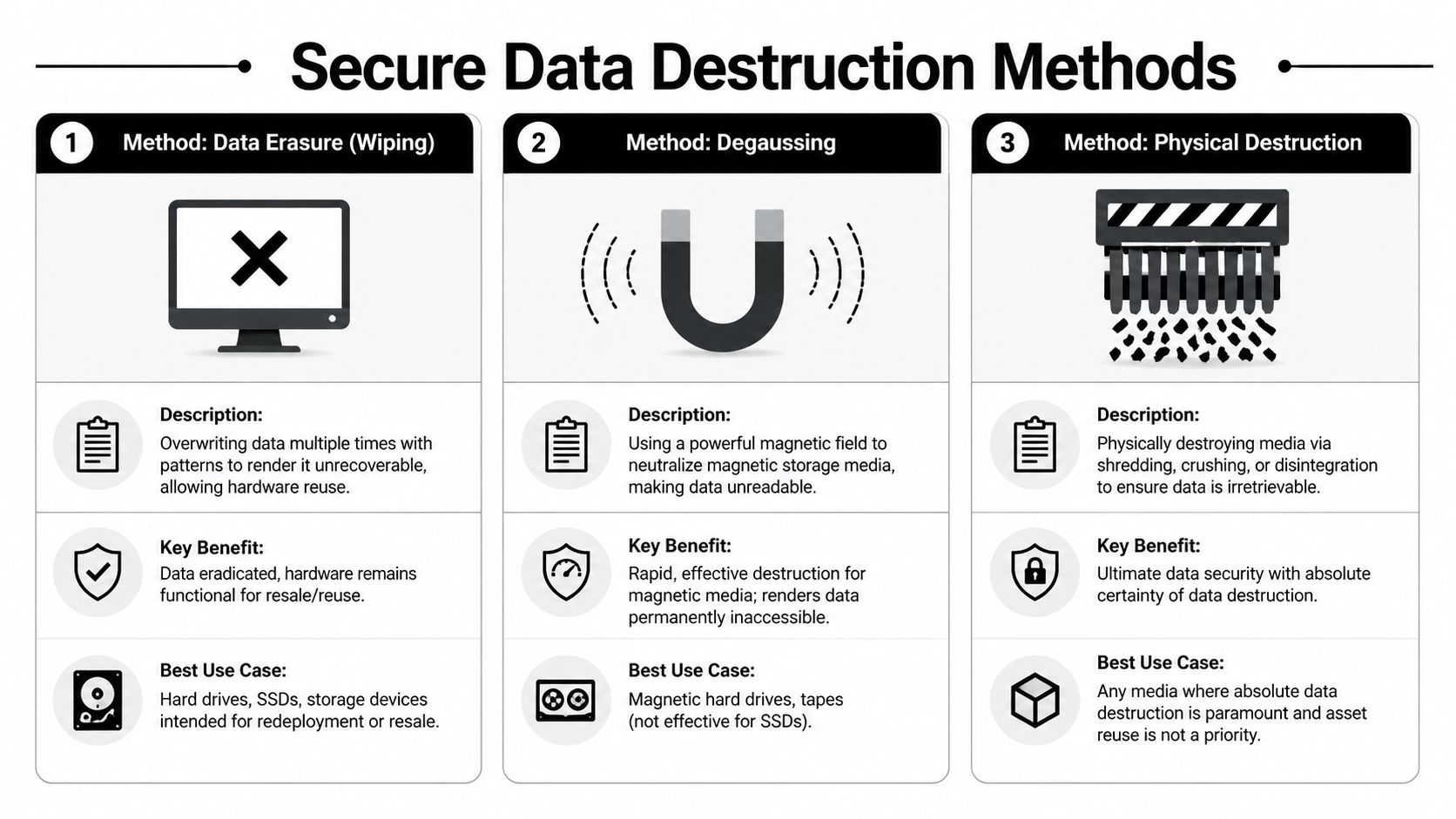
The three methods and when they fit
Here’s the working decision framework most operators need.
| Method | Security Level | Asset Reusability | Best For | Verification |
|---|---|---|---|---|
| Data erasure | High when properly validated | High | Reuse or resale candidates, including storage intended for remarketing | Software reports and device-level documentation |
| Degaussing | High for magnetic media | None | Magnetic hard drives and tapes where reuse isn't needed | Process records tied to the media handled |
| Physical destruction | Highest practical finality | None | Damaged media, highly sensitive assets, or policy-mandated destruction | Destruction logs and per-device certificates |
A provider offering secure data destruction services should be able to explain this matrix clearly, not push one method for every scenario.
Data erasure
Erasure is the best option when policy allows hardware reuse. It preserves asset value and supports remarketing or redeployment.
That said, teams make two mistakes with wiping. First, they assume every device can be handled the same way. Second, they accept vague pass/fail summaries instead of device-level evidence. In a data center environment, neither is acceptable.
Use erasure when you want to keep the hardware functional and can support the method with verification records tied to the exact device processed.
Degaussing
Degaussing still has a place, but only for magnetic media. It is not the answer for SSDs or other non-magnetic storage.
Its value is speed and irreversible impact on magnetic data-bearing devices. Its limitation is just as important. Once degaussed, the media isn’t a reuse candidate. So if a project’s financial model depends on recovering value from magnetic drives, degaussing removes that possibility.
For highly sensitive environments, degaussing is often paired with later physical destruction as part of a layered control model.
Physical destruction
Shredding, crushing, or similar destruction methods are the right choice when the organization requires maximum certainty or the media is damaged and can’t be reliably erased.
This is often mandatory for some classes of devices and some regulated projects. It is also the cleanest answer when chain-of-custody concerns are high and reuse isn’t a goal.
Field advice: Don’t choose shredding by habit. Choose it because policy, sensitivity, or device condition makes it the right endpoint.
How to choose without overpaying
A practical selection model looks like this:
- Use erasure for devices with resale or redeployment potential, provided the device type and policy support validated sanitization.
- Use degaussing for magnetic media where fast neutralization matters and reuse does not.
- Use physical destruction for failed media, high-sensitivity workloads, or assets covered by stricter internal or contractual requirements.
A better decision question
Don’t ask, “What is the most secure method in theory?”
Ask, “What is the most appropriate method for this media, this policy, and this audit burden?”
That question usually produces better outcomes. It protects the organization without destroying value unnecessarily.
The Power of an Audit-Proof Chain of Custody
Most organizations spend too much time debating destruction methods and not enough time on the evidence layer that makes those methods defensible.
Without chain of custody, a correct technical process can still fail an audit. You may know the drives were handled properly. Your compliance team still has to prove it to someone who wasn’t in the room.

What audit-proof actually looks like
Enterprise-grade documentation isn’t a summary PDF that says a batch was destroyed. It’s a record structure that ties each data-bearing device to a specific processing outcome.
Enterprise-grade compliance demands multi-device, serial-level destruction certification aligned with NIST SP 800-88 Rev. 2. Top-tier NAID AAA certification validates this through rigorous unannounced audits, including support for advanced hardware categories such as GPU-dense systems and NVMe drives, according to STS Electronic Recycling guidance on data center ITAD compliance.
That standard matters because modern data center retirements don’t just involve generic hard drives. They involve mixed storage types, accelerators, blade environments, and dense assemblies where one missing serial number can create a documentation hole.
The certificate is not a formality
A valid certificate of destruction for hard drives should support an auditor’s questions without requiring guesswork.
Look for these fields at a minimum:
- Device identification: serial number or equivalent unique identifier
- Method used: erasure, degaussing, shredding, or another documented process
- Processing details: date, facility location, and responsible technician or processing authority
- Disposition status: whether the asset was destroyed, sanitized for reuse, or routed to recycling after handling
If a vendor issues one certificate for an entire truckload with no device-level detail, that isn’t enough for many enterprise environments.
Documentation is what turns “we handled it” into “we can prove it.”
Certifications matter because promises aren't controls
NAID AAA and related audited standards matter for one reason. They provide third-party validation that a vendor’s process has controls behind it.
That doesn’t eliminate the need for due diligence. You should still ask for sample reporting, intake workflows, exception handling procedures, and custody escalation protocols. But certification filters out many weak operators quickly because it shows the vendor has submitted to external scrutiny rather than relying on marketing language.
Choosing Your ITAD Partner A Vendor Selection Checklist
Vendor selection is where many organizations accidentally reintroduce risk they worked hard to remove from the project plan. Price pressure does that. So does schedule pressure.
A weak ITAD partner often looks acceptable during procurement because the proposal sounds complete. The differences show up later, when you ask for exception handling, witness options, detailed certificates, or asset-level reconciliation.
The checklist that matters
Use this list when comparing providers:
- Verify certifications: Confirm NAID AAA, R2v3, and any other standards relevant to your environment. Ask for current documentation, not a verbal assurance.
- Inspect chain-of-custody detail: Request sample manifests, sample certificates, and example exception reports.
- Test service scope: Ask whether the team handles de-racking, packaging, onsite segregation, and media-specific processing.
- Review facility controls: You need to know who can access assets, how intake is logged, and how mixed customer inventories are prevented.
- Check downstream accountability: The vendor should explain what happens to assets that cannot be remarketed and how end-of-life materials are managed.
- Assess reporting quality: Reports should help your audit team, not create more work for them.
Questions worth asking in the first call
Some of the best screening questions are direct:
| Question | Why it matters |
|---|---|
| How do you track assets from pickup through final processing? | Reveals whether custody is real or mostly manual |
| Can you produce serial-level destruction records? | Tests audit readiness immediately |
| Which media types do you erase, degauss, or shred? | Exposes whether they understand device-specific handling |
| How do you handle exceptions or unreadable assets? | Shows process maturity |
| Can your facility support segregated workflows if needed? | Critical for regulated or defense-adjacent environments |
One option in the market is Dallas Fortworth Computer Recycling's IT asset disposition company services, which include secure collection and transportation, data sanitization, certified destruction, inventory tracking, refurbishment, remarketing, and responsible recycling for organizations with nationwide needs. That service mix is the kind of scope you should compare across vendors, rather than reducing the decision to haul-away cost.
Red flags that should stop the process
Watch for these:
- Vague language about documentation
- No sample reporting available
- One-size-fits-all destruction answers
- Unclear downstream partners
- No discussion of witness procedures or exception handling
- A quote that arrives faster than a scoping conversation
A serious ITAD partner wants to understand your asset mix, risk profile, and documentation burden before finalizing the disposal path.
If procurement treats this as commodity hauling, the organization usually pays for that mistake later.
The Strategic Balance Cost Sustainability and Value Recovery
A decommissioning project can look successful on paper and still lose money. The racks are cleared, drives are destroyed, and the recycler issues a certificate. Then finance reviews the write-off, sustainability asks what was actually reused, and operations realizes recoverable equipment was scrapped because nobody sorted it early enough.
That outcome is avoidable. A sound data center ITAD strategy sets asset disposition rules that protect data, preserve resale where policy allows, and document environmental outcomes in a way finance and compliance can both use.

The primary trade-off is asset certainty versus asset value
Physical destruction removes reuse from the table. For some media and some regulatory environments, that is the right call. It reduces residual risk, simplifies policy enforcement, and gives legal and security teams a clear record.
Secure erasure creates more financial upside and supports reuse, but only if the organization can defend that path with written policy, device-level tracking, and validation records. Recycling serves a different purpose. It is the correct downstream path for equipment that has no resale market, no internal redeployment value, or no compliant route to reuse.
Market demand keeps growing as operators retire dense compute, refresh for AI workloads, and close older facilities, as noted in Resource Recycling reporting on data centers and AI as an ITAD growth engine. That growth increases the value of disciplined triage. It also increases the cost of getting the triage wrong.
Where operators give away value
Value is usually lost before the first truck leaves the site.
I see it happen when decommissioning is handed off as a removal job instead of a recovery project. Assets get unpowered, unmounted, palletized, and mixed by hardware class with no separation between shred-only media, resale candidates, and equipment better suited for parts harvesting. Once that happens, serial attribution gets weaker, cosmetic condition gets worse, and resale options narrow fast.
The same pattern hurts sustainability reporting. If reusable assets are merged into scrap flows too early, the organization may still recycle responsibly, but it loses the stronger outcome of extending equipment life through redeployment or secondary market resale.
A stronger operating model
The better model is not complicated. It is disciplined.
Set destruction rules before shutdown
Identify which assets are policy-bound to shred, which can be sanitized and resold, and which should go straight to material recovery.Protect resale condition during removal
Recoverable servers, networking gear, and components lose value when they are stacked carelessly, stripped without documentation, or stored in mixed lots.Separate financial recovery from scrap accounting
Scrap weight is not the same as value recovery. Track resale, parts harvesting, and commodity recycling as different outcomes.Report to each stakeholder in their language
Security needs proof of sanitization or destruction. Finance needs net recovery and fee transparency. Sustainability teams need documented reuse and recycling outcomes.
Strong ITAD programs do not force security, finance, and sustainability into the same answer for every asset. They assign the right disposition path to each class of equipment, then document why.
What strategic operators do differently
They bring ITAD into the project while migration and shutdown plans are still being written. They decide early which equipment is governed by risk policy and which equipment should be preserved for remarketing. They treat chain of custody as both a compliance control and a value protection tool, because intact records support both audit defense and resale.
That is the shift. ITAD is not just a cost center at the end of the hardware lifecycle. Handled correctly, it reduces exposure, improves reporting quality, and returns value that would otherwise be lost in a rushed teardown.
If you are planning a shutdown, migration, or refresh, Dallas Fortworth Computer Recycling provides nationwide ITAD support for secure pickup, certified data destruction, decommissioning workflows, inventory tracking, remarketing, and responsible recycling. Evaluate that kind of scope based on process control, documentation quality, and recovery discipline, not just the haul-away quote.
