Texas Recycling: A Guide to Secure IT Asset Disposal
The request usually lands on IT with a vague label: “clean out the old equipment.”
What that often means in practice is a storage closet with retired laptops, a row of decommissioned switches, a few servers nobody wants to touch, and a stack of loose drives that may still hold employee, patient, customer, or financial data. The equipment is out of production, but the risk is still live.
Most Texas recycling advice loses utility at this point. General recycling guidance helps with cardboard, bottles, and municipal waste. It does not tell an IT director how to document custody of data-bearing assets, decide whether a drive should be wiped or shredded, or prove to an auditor that devices were handled correctly from pickup through final disposition.
Texas has strong recycling momentum, but there is still a gap around B2B electronics recycling. Public recycling coverage often focuses on municipal solid waste, while business concerns such as secure IT asset disposition, certified data destruction, and audit-ready reporting get far less attention. That gap matters most in healthcare, finance, government, and any environment where one forgotten drive can create a legal problem long after the hardware leaves your building.
The Hidden Risks in Your IT Storage Closet
A crowded IT storage room looks like an operations nuisance. It is usually a compliance problem first.
One shelf may hold laptops from a refresh project. Another may hold failed drives removed from servers. A corner may have network gear waiting for resale review. If those assets are mixed together, nobody can answer basic questions quickly: Which devices still store data? Which belong to a regulated business unit? Which are approved for remarketing? Which require destruction?
Why generic recycling advice breaks down
For households, recycling usually means convenience. For businesses, it means security, documentation, and defensibility.
A municipal drop-off model does not give an IT director what they need. It does not establish who handled the asset, whether the serial number was captured, whether storage media was sanitized correctly, or whether downstream processing matched internal policy.
Texas recycling coverage also leaves a real blind spot here. General municipal recycling reporting showed 9.2 million tons recycled in 2015, but there is still minimal guidance on secure IT asset disposition, certified data destruction, and chain-of-custody controls for businesses, as noted by the Texas Commission on Environmental Quality recycling study page.
The risks are not only environmental
The storage closet creates several kinds of exposure at once:
- Data exposure: Old desktops, laptops, copiers, servers, and removable media may still contain regulated information.
- Process failure: If equipment sits too long, labels fall off, ownership becomes unclear, and asset records drift away from reality.
- Financial loss: Devices with resale potential lose value while they sit untouched.
- Audit weakness: If a business cannot produce records for retirement and destruction, “we believe it was recycled” is not a defensible answer.
Practical rule: If a device ever touched sensitive data, treat retirement as a controlled disposition project, not a cleanup task.
That is why many IT teams separate hard drive disposal from general electronics handling. If you need a reference point for that part of the process, this overview of secure hard drive disposal reflects the level of specificity businesses should expect.
What regulated teams need instead
Healthcare, finance, public sector, and multi-site enterprises need a repeatable process with named controls:
- inventory before pickup
- segregation of data-bearing assets
- documented handoff
- approved destruction method
- final reporting tied back to asset records
Texas recycling is not just a sustainability issue for these teams. It is part of governance.
Navigating Texas E-Waste Regulations
Texas businesses need to think about electronics disposition in two layers. The first layer is environmental handling. The second is data and privacy compliance. If either layer fails, the whole project fails.
Texas recycling rules are part of a longer state pattern
Texas did not arrive at recycling policy recently. The state has a long record of building recycling programs at scale. In 1994, TxDOT launched a statewide recycling program for road construction. By 2001, TxDOT was investing $200 million annually in recycled products and had diverted nearly 2.6 million tons of waste from landfills since the program began, according to the Federal Highway Administration account of the Texas roadway recycling program.
That matters because it shows a longstanding Texas approach: remove specification barriers, create practical pathways, and build systems that keep material out of landfills. Electronics require the same mindset, but with much tighter controls around data.
Green does not automatically mean compliant
An electronics recycler can sound environmentally responsible and still leave you exposed if their data handling is weak.
The key distinction:
- Environmental compliance asks whether equipment and components are managed responsibly.
- Data compliance asks whether information on these devices was secured, destroyed, and documented properly.
For an IT director, these are inseparable. You are not just recycling hardware. You are retiring an information asset.
What IT leaders need to map internally
You do not need to become an attorney to manage texas recycling correctly. You do need to know which obligations attach to your devices and your data.
Focus on these categories:
Data privacy requirements
If your organization handles patient data, consumer financial records, employee records, or regulated public-sector information, retired devices can fall under internal and external obligations tied to privacy and record protection. HIPAA, GLBA, FACTA, contractual security requirements, and internal retention policies all shape what “proper disposal” means.
A server with a failed RAID set is not low risk because it is broken. A broken drive is often the asset that creates the most confusion in a rushed cleanup.
Environmental handling rules
Electronics are not ordinary trash. Batteries, certain display components, and other materials require controlled downstream processing. A vendor should be able to explain where material goes, how it is sorted, and how they prevent landfill leakage.
Documentation requirements
Many projects fail unobserved at this stage. If you cannot connect an internal asset record to a pickup record, to a destruction event, and then to final reporting, you have a weak chain.
Ask one simple question: If an auditor asks for proof on a single serial-numbered device six months from now, can your team produce it without rebuilding the story from emails?
The vendor conversation should be operational
The strongest IT leaders do not ask broad questions like “Are you compliant?” They ask operational ones:
- How do you identify data-bearing devices on intake?
- What happens when assets arrive without tags?
- How do you separate reuse candidates from destruction inventory?
- What record do you issue after destruction?
- Who signs custody at pickup?
That is the standard to apply when reviewing providers for enterprise IT equipment recycling in Texas.
Your Internal IT Asset Disposition Checklist
The smoothest disposition projects are usually won before the truck arrives.
If your team sends a recycler a vague list like “old computers, some servers, maybe monitors,” you invite pricing confusion, custody mistakes, and delay. If you send a clean inventory with clear handling instructions, the job becomes faster, safer, and easier to audit.
Sort first, then schedule
Texas municipal recycling offers a useful warning sign here. The Texas Recycling Data Initiative found an average 13% residual contamination rate in single-stream recycling programs, according to the TRDI report. In business electronics, contamination looks different, but the operational problem is similar. If teams mix data-bearing and non-data-bearing assets, secure destruction and reporting get harder immediately.
That is why internal sorting matters.
Build three categories
Create simple handling lanes before pickup:
Assets for data destruction
Laptops, desktops, servers, storage arrays, copiers, mobile devices, and loose media should go in this group if they may hold data.Assets for reuse or resale review
Newer business equipment with remaining market life belongs in a separate lane. Mixing these with scrap equipment slows evaluation and can reduce recovery.Assets for commodity recycling
Monitors, damaged peripherals, cables, and obsolete gear that no longer justify refurbishment can go here.
Use a short-form internal log
Do not wait for the recycler’s intake process to become your first real record. Start your own.
A basic internal log should capture:
- Asset identifier: serial number, asset tag, or internal ID
- Device type: laptop, server, switch, SAN, monitor, printer
- Location: closet, branch office, rack row, department
- Data status: confirmed data-bearing, likely data-bearing, no storage present
- Disposition instruction: destroy, remarket, recycle
- Custody owner: person releasing the asset
That log does not need to be elaborate. It needs to be consistent.
Keep failed drives separate
Loose hard drives, SSDs, backup tapes, and removable media deserve their own container and count. They are the easiest items to lose track of during office cleanouts and server refreshes.
Tip: If a device was removed from a chassis, log the media separately. Do not assume the host server record is enough.
Consolidate the project physically
A clean pickup area reduces errors. Whenever possible, move approved assets into one secure staging zone instead of leaving them scattered across offices, labs, and closets.
That gives you operational benefits:
- pickup crews scan faster
- internal signoff is easier
- fewer items get missed
- chain-of-custody starts in a controlled location
Brief the people involved
Not every project fails because of policy. Many fail because one local office manager, lab supervisor, or facilities lead adds an unlisted pile of electronics at the last minute.
Send a short instruction note before the pickup date. State what is in scope, what is out of scope, who can authorize additions, and how sealed media should be handled.
If your team is preparing for infrastructure retirement, a detailed server decommissioning checklist is the kind of operational reference that keeps this stage disciplined.
How to Select a Compliant Recycling Partner in Texas
Most ITAD failures are vendor selection failures.
A provider can promise sustainability, offer a low pickup price, and speak confidently about recycling. None of that proves they can protect your organization when the project involves data-bearing devices, audit obligations, or multi-site logistics.
Texas has been pushing broader recycling market development for years. In 2019, the state recycled 12.9 million tons of MSW and reported a $4.8 billion economic impact, as summarized in the Texas Recycling Market Development Plan coverage from ECOS. For IT teams, the practical takeaway is straightforward: certified electronics processing helps keep high-value materials in productive circulation instead of treating everything like waste.
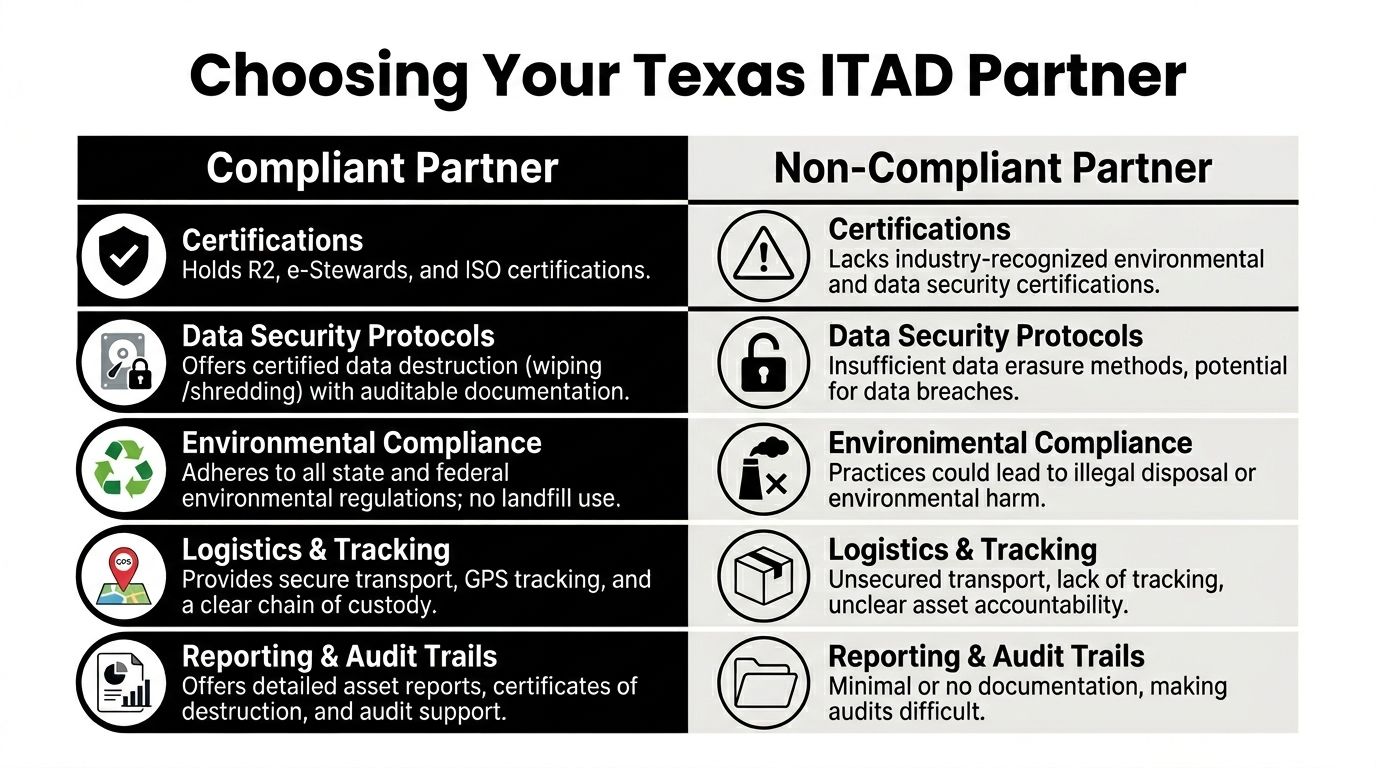
What a serious vendor should prove
Do not evaluate a recycler only on convenience or price. Evaluate them on whether they can create a defensible record.
A strong vendor should be able to show:
- recognized certifications
- documented data destruction methods
- secure transportation procedures
- facility security controls
- downstream environmental accountability
- itemized reporting after the project
If any of those answers come back vague, keep looking.
Key ITAD Vendor Certifications Explained
| Certification | What It Guarantees | Why It Matters for Your Business |
|---|---|---|
| R2 | The provider follows a recognized framework for responsible electronics reuse and recycling operations | It helps you screen for process discipline, downstream control, and documented handling |
| e-Stewards | The provider operates under a certification model focused on responsible electronics management | It gives another signal that environmental handling is being managed under a structured program |
| ISO-based quality or security certifications | The provider maintains formal management systems for operational consistency or information security | It matters when you need repeatable workflows, audit support, and fewer custody gaps |
If certification status matters to your procurement process, review the standards behind an R2 certified electronics recycler.
Ask about methods, not slogans
“Data destruction” is too broad to be useful in an RFP. You need method-level clarity.
Software wiping
This can make sense for devices that are eligible for reuse and can be processed under a recognized sanitization workflow. It only works when the device is functional enough for the process and when the vendor can document completion clearly.
Degaussing
This applies to certain magnetic media. It can be appropriate in some environments, but it also affects whether equipment can be reused. Teams should understand that trade-off before approving it as the default.
Physical shredding
This is often the right answer when risk tolerance is low, the media is damaged, the device is from a highly regulated environment, or the organization desires finality. It usually reduces or eliminates remarketing potential for the media itself, which is sometimes exactly the point.
Rule of thumb: Pick the destruction method based on data risk first, value recovery second.
Visit the weak points in the workflow
The best questions focus on where errors happen.
Transportation
How are assets secured in transit? Who signs custody? Are containers sealed? Is there a documented transfer record?
Intake
What happens when a pallet arrives with mixed equipment and loose drives? How are serials captured? What happens if a tag is missing?
Exceptions
How does the vendor handle damaged devices, failed drives, or inventory that does not match the original list? If they do not have an exception process, the chain breaks when reality stops matching the quote.
Price usually hides the wrong question
A low quote may mean the vendor excluded the difficult parts: serial capture, onsite services, secure packing, audit reporting, or media-specific destruction.
That quote is not “efficient.” It is incomplete.
A better comparison framework is:
- What level of documentation do we receive?
- Which destruction methods are included?
- What controls exist from pickup to final processing?
- How are exceptions reported?
- Can this vendor support legal, internal audit, and procurement if questions arise later?
Red flags that deserve immediate attention
- no clear answer on downstream processing
- no sample certificate of destruction
- no explanation of how data-bearing devices are identified
- no distinction between recycling and reuse streams
- unclear insurance or liability language
- pricing that depends on broad assumptions but no inventory review
A compliant Texas recycling partner should make your internal risk smaller, not force your team to fill in the blanks after pickup.
Managing Secure Logistics and Chain of Custody
Once the vendor is selected, execution becomes the priority. Strong plans either hold or fail at this juncture.
The physical movement of retired technology is not a side detail. It is the control point that links your internal inventory to the final proof of destruction or recycling. If the chain is loose here, every later document becomes less reliable.

Start with a real scope document
A good pickup begins with a Statement of Work that matches reality.
That document should identify pickup locations, asset types, access constraints, packaging expectations, whether onsite work is required, and how data-bearing assets will be handled. If your team is retiring a cage of servers at a data center, the workflow should not resemble a small office electronics pickup.
What a controlled pickup looks like
When logistics are done correctly, the process is boring in the best way.
Typical checkpoints include:
- Arrival control: pickup crew verifies the site contact and scope
- Asset review: staged inventory is checked against what was expected
- Scanning or logging: serial-numbered assets are captured where required
- Secure packing: equipment is placed in controlled containers, pallets, or wrapped loads
- Transfer record: the handoff document starts the external chain of custody
That handoff record matters because it establishes when responsibility moved from your organization to the service provider.
Multi-site and rural Texas create different problems
Texas geography complicates ITAD projects. One office in Dallas is easy. A healthcare group with satellite clinics, a county agency, or a manufacturer with remote locations has a much harder logistics problem.
Rural businesses in particular face fewer local recycling options. Keep Texas Recycling supported 50 partners in 2024, diverting 5,000 tons with 300 truckloads valued at $600,000, and added $180,000 in infrastructure grants, according to the case study on expanding rural recycling access. But electronics are often still outside that support structure, which is why IT teams with dispersed operations usually need a partner that can serve every location under one custody and reporting model.
Do not let exceptions go undocumented
Real projects always contain surprises.
You may find:
- unlisted loose drives in a cabinet
- medical or lab devices that need separate handling
- monitors mixed into server pallets
- equipment with missing tags
- branch offices that packed extra devices after the inventory freeze
The answer is not to “just take it.” The answer is to document the exception, assign the proper disposition path, and update the record.
Best practice: If an item appears on pickup day that was not approved in advance, require explicit signoff before it joins the load.
Final documents are your proof
The project is not complete when the truck leaves. It is complete when your records are closed and supportable.
You should expect post-project documentation that may include:
| Document | What it should show | Why it matters |
|—|—|
| Pickup record or bill of lading | Date, location, releasing party, receiving party, scope of transferred assets | Confirms the start of external custody |
| Asset report | Device identifiers, counts, categories, and final disposition status | Helps reconcile internal inventory to vendor processing |
| Certificate of destruction | Confirmation that approved data-bearing media was destroyed or sanitized per the agreed method | Supports audit and compliance review |
| Settlement or disposition summary | Reuse, recycling, and residual handling outcomes | Closes the project operationally and financially |
For teams that need to validate their reporting expectations, this guide to a certificate of destruction for hard drives reflects the kind of proof you should request.
Costs, Value Recovery, and Community Impact Programs
IT directors often get pushed into a false choice. Either recycle responsibly and treat the project as a pure expense, or chase resale value and accept more risk.
That is the wrong frame. A well-run disposition program can pursue security first, then recover value where policy allows, then extend useful equipment life through approved reuse or donation channels.
What drives cost
Pricing in Texas recycling for business electronics usually turns on project complexity, not just volume.
Common cost drivers include:
- whether the assets contain data
- whether work happens onsite or offsite
- how much inventory detail exists before pickup
- the mix of reusable equipment versus scrap material
- the number of locations involved
- special handling for healthcare, lab, or infrastructure gear
A pallet of tested laptops ready for remarketing is a different project from a room full of unsorted towers, printers, failed drives, and specialty devices.
Value recovery works when you preserve optionality
The assets most likely to retain value are usually the ones that are handled cleanly from the start.
That means:
- devices are inventoried early
- cosmetic condition is preserved
- chargers, rails, caddies, and accessories stay with the equipment where relevant
- data-bearing devices are routed through an approved sanitization process that still supports resale when policy permits
If your team waits until equipment is piled together for months, parts get separated, labels disappear, and resale review becomes harder. Recovery drops because process quality dropped.
Not every device should be remarketed
Not every device should be remarketed. Mature IT teams make better decisions in this area than bargain-focused buyers.
Some assets belong in a reuse stream. Others should go directly to destruction and commodity recycling because the data risk, condition, age, or regulatory context makes remarketing a poor fit.
Examples that often require stricter handling include:
- failed storage media
- retired devices from regulated healthcare workflows
- systems with uncertain ownership history
- specialty equipment where internal policy requires physical destruction
That is not lost value. That is controlled risk.
Smart policy: Write down in advance which asset classes are eligible for resale review and which are mandatory destruction items. Do not improvise that decision at pickup time.
Community impact is strongest when it is structured
There is also a meaningful social side to business electronics disposition. Equipment that is still useful can sometimes support schools, nonprofits, and other organizations through structured reuse and donation programs.
The point is not to “give away old stuff.” The point is to extend useful life responsibly after data protection requirements have been met and equipment has been evaluated for suitability.
That can align three goals:
| Goal | Practical outcome |
|---|---|
| Operational efficiency | IT clears space and closes asset records cleanly |
| Environmental responsibility | More equipment is reused or recycled instead of discarded |
| Community benefit | Qualified organizations may gain access to technology they could not otherwise justify buying |
Programs built around reuse can also support broader circular-economy thinking in Texas. The state’s recycling planning has emphasized market development and keeping useful materials in circulation. For IT leaders, that principle is most valuable when it is paired with auditable data destruction and clear eligibility rules for reuse.
When teams approach disposition strategically, cost, recovery, and community benefit stop competing with each other. They become separate outputs of the same disciplined process.
Your Final Texas IT Recycling Action Plan
If you are responsible for retiring business technology in Texas, keep the plan simple and strict.
Confirm the rules that apply to your environment
Map the project to your actual obligations. That includes privacy requirements, internal retention policy, procurement rules, and any environmental handling expectations tied to the equipment involved.
Do not let “recycling” become a catchall term that hides data risk.
Build an inventory before vendor pickup
Capture the assets, locations, and likely data status. Separate destruction items from reuse candidates. Keep loose media on its own log.
If your inventory is weak, every later document will be weaker too.
Select the vendor like a risk decision
Review certifications, destruction methods, transport controls, reporting samples, and exception handling. Ask how they manage missing tags, failed drives, and mixed loads.
A vendor that cannot explain its process clearly will not protect you when the project gets messy.
Lock down logistics
Use a defined scope of work. Stage assets in a controlled area where possible. Make sure someone inside your organization owns release approval at every site.
For multi-location organizations, insist on one reporting model across all sites.
Do not close the project without final proof
Require pickup records, asset reports, and destruction documentation that can be tied back to your internal records. Review exceptions before filing the project complete.
The right Texas recycling process should leave you with fewer open questions at the end than you had at the start.
If your team needs a B2B-focused partner for secure, auditable electronics disposition, Dallas Fortworth Computer Recycling provides nationwide IT asset disposition, certified data destruction, data center decommissioning, and responsible electronics recycling for organizations that cannot afford compliance gaps.
