Computer Recycling Services: Secure ITAD & Eco-Friendly E-Waste Solutions
Computer recycling services are specialized solutions designed to help businesses securely and responsibly dispose of obsolete IT equipment. This process, better known in the industry as IT Asset Disposition (ITAD), is much more than just hauling away old hardware. It's a critical function for protecting sensitive data, staying compliant with environmental laws, and even recovering financial value from retired technology.
Why Computer Recycling Is a Critical Business Strategy

For IT directors and compliance officers, managing the end-of-life for technology has shifted from a simple disposal task into a strategic imperative. Think of it as giving your company’s hardware a secure ‘digital retirement.’ Just like you would carefully plan a key employee's departure, your technology needs a formal, secure process to exit the organization without creating new risks.
The stakes have never been higher. Technology upgrade cycles are faster than ever, meaning businesses are retiring assets more frequently. At the same time, data privacy regulations like GDPR and CCPA impose severe penalties for mishandling sensitive information, even on devices you plan to scrap. A single improperly discarded hard drive can trigger a devastating data breach, leading to steep fines and irreversible damage to your brand.
The Three Pillars of a Professional ITAD Program
Professional computer recycling services are built on three foundational pillars that address these modern business challenges. If you neglect any one of these areas, you're exposing your organization to significant operational, financial, and reputational risks.
A successful program always integrates:
- Ironclad Data Security: This is the absolute non-negotiable core of any ITAD strategy. It involves certified data destruction methods that guarantee all sensitive corporate and customer information is permanently wiped clean before an asset is remarketed or recycled.
- Environmental Stewardship: When electronics are dumped in a landfill, they can leach toxic materials like lead and mercury into the environment. A compliant program ensures every component is recycled according to strict environmental standards, helping you meet corporate social responsibility goals. You can learn more about proper computer equipment recycling and its environmental impact in our detailed guide.
- Maximum Value Recovery: Not all of your retired equipment is worthless. Many devices, like recent-model servers, laptops, and networking gear, still have significant residual value. A strategic partner will identify these assets, refurbish them, and sell them on the secondary market, returning a portion of the proceeds directly to your bottom line.
When you view IT asset disposition through this lens, it stops being a cost center and becomes a risk management function. A formal program protects the company, ensures compliance, and can even generate revenue, making it an essential part of the modern IT asset lifecycle. It turns a potential liability into a verified, secure, and responsible process.
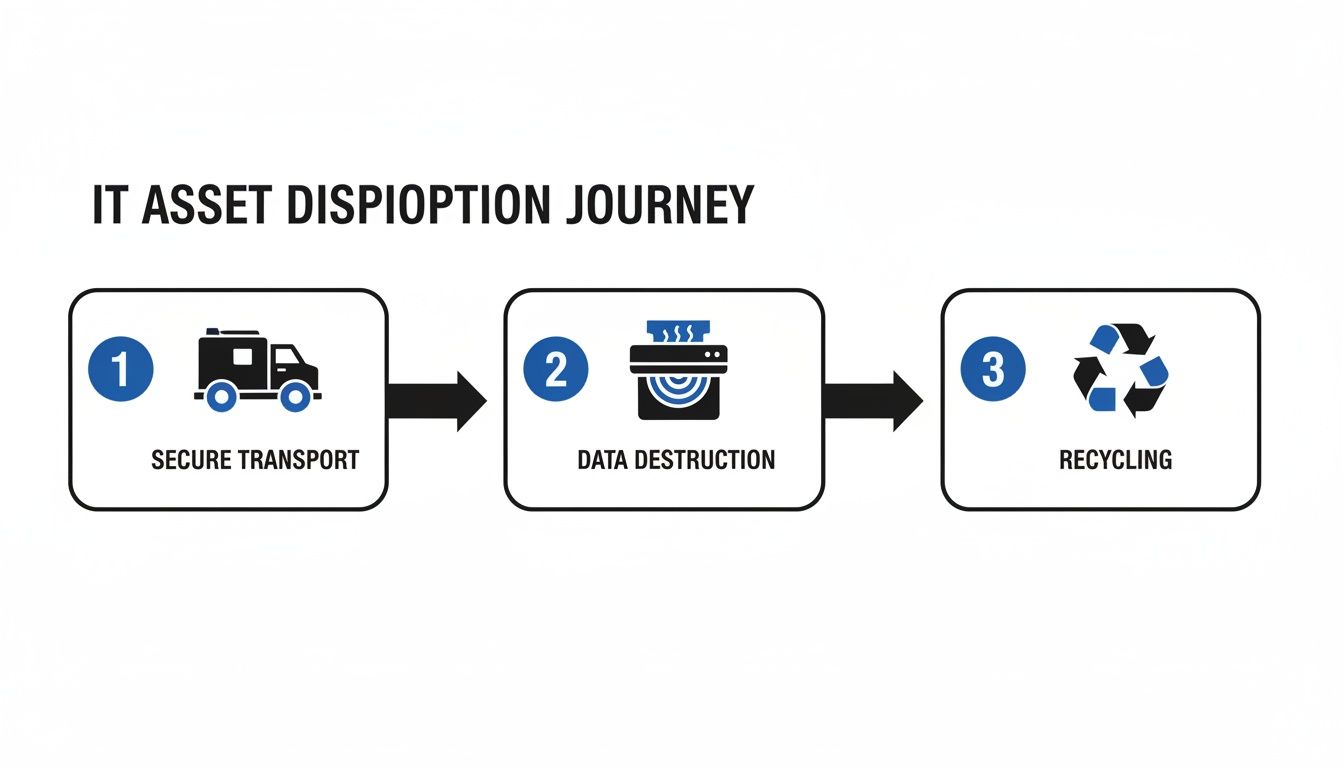
The Secure Journey of Your Retired IT Assets
When a computer, server, or hard drive is decommissioned, its journey is far from over. For IT managers, the time between an asset leaving your loading dock and its final disposition is filled with potential risks. A professional computer recycling services provider transforms this uncertain path into a secure, transparent, and auditable process.
This journey isn't just about disposal; it's a meticulously managed lifecycle designed to protect your data, comply with regulations, and preserve your company's reputation at every turn. Let's walk through the path a retired asset takes from your office to its final, responsible end.
Stage 1: Onsite Logistics and Secure Transport
It all starts at your facility. A reputable ITAD partner never expects you to just leave pallets of sensitive equipment on a curb. Instead, their trained and background-checked technicians arrive on-site to professionally inventory, pack, and prepare your assets for transit.
This first step is absolutely critical for establishing the chain of custody—the unbroken, documented trail of your equipment. Assets are then loaded into secure, GPS-tracked vehicles, ensuring that from the moment they leave your control, they are under constant surveillance until they reach the secure processing facility.
Stage 2: Chain of Custody and Detailed Auditing
Upon arrival at the ITAD facility, every single asset is meticulously audited. Technicians scan serial numbers and asset tags, creating a detailed inventory that’s reconciled against the initial on-site pickup list. This confirms that every device you handed over has been accounted for.
This isn't just a simple head count. The audit captures key details for each item, including:
- Asset Type: Server, laptop, desktop, networking gear, etc.
- Manufacturer and Model: For example, a Dell PowerEdge R740 or HP EliteBook 840.
- Serial Number: The unique identifier for precise tracking and reporting.
- Asset Tag Number: Your internal tracking number for seamless record-keeping.
This detailed report is your first piece of essential documentation, giving you a transparent record of what was received before any data destruction or recycling even begins.
The table below summarizes the key stages and their importance in a secure ITAD process.
| Process Stage | Key Activities | Core Business Benefit |
|---|---|---|
| Logistics & Transport | On-site inventory, professional packing, and secure, GPS-tracked transit. | Establishes an unbroken chain of custody and minimizes the risk of asset loss or theft during transit. |
| Receiving & Audit | Scanning all serial numbers and asset tags, reconciling against the initial pickup list. | Provides a transparent, auditable record confirming every asset has arrived safely at the facility. |
| Data Destruction | Segregating data-bearing devices for certified wiping (NIST 800-88) or physical shredding. | Guarantees complete data erasure, protecting against data breaches and ensuring regulatory compliance. |
| Value Recovery & Refurbishment | Testing, grading, and refurbishing functional equipment for resale in secondary markets. | Offsets disposition costs by generating revenue from remarketed assets and promotes a circular economy. |
| Responsible Recycling | De-manufacturing end-of-life assets into commodities and safely managing hazardous materials. | Ensures environmental compliance, prevents e-waste from entering landfills, and supports sustainability. |
Each step is designed to build on the last, creating a comprehensive, documented trail that protects your business from start to finish.
Stage 3: Certified Data Destruction
This is arguably the most critical stage in the entire process. Here, all data-bearing devices are segregated for certified data destruction, adhering to rigorous standards like those found in NIST 800-88. Your ITAD partner will use one of two primary methods to guarantee your data is gone for good.
- Data Sanitization (Wiping): Specialized software overwrites every single sector of a hard drive with random data, often in multiple passes. This method preserves the drive's functionality, making it suitable for refurbishment and resale.
- Physical Destruction (Shredding): For devices that are end-of-life or when sanitization isn't an option, physical destruction is the definitive solution. Hard drives and other media are fed into industrial shredders that grind them into small, irrecoverable fragments.
Upon completion, you receive a Certificate of Data Destruction. This legal document lists the serial numbers of every sanitized or destroyed drive, serving as your official proof of compliance and due diligence.
Stage 4: Maximizing Value Through Refurbishment
Not all retired IT equipment is waste. A key part of a strategic ITAD program is identifying assets that still have market value. After data has been securely wiped, functional equipment like laptops, servers, and networking components are tested, graded, and refurbished for resale. You can get a deeper explanation of the full ITAD lifecycle and its benefits by reading our guide on what is IT asset disposition.
This value recovery process is a win-win. It extends the useful life of technology—the most sustainable outcome possible—and it generates revenue that can be shared back with your organization, directly offsetting the costs of the recycling service.
Stage 5: Responsible Materials Recycling
For assets that have no resale value or have failed testing, the final stage is responsible recycling. This is where the commitment to environmental stewardship becomes tangible. Devices are de-manufactured, and their components are separated into base commodities.
This process involves breaking down electronics into their core materials:
- Precious Metals: Gold, silver, copper, and palladium are recovered from circuit boards.
- Base Metals: Steel, aluminum, and plastics are separated for processing.
- Hazardous Materials: Components containing mercury, lead, and cadmium are safely removed and handled by specialized downstream partners.
Every material is sent to a certified facility for smelting or reprocessing, ensuring nothing ends up in a landfill. A final Certificate of Recycling completes your documentation, confirming your assets were handled in an environmentally compliant manner from start to finish.
Understanding Data Security and Compliance Mandates
When you hand over retired IT assets, you're not just getting rid of old hardware. You're entrusting a partner with your company's most sensitive information. The legal and regulatory landscape around this process is complex and, frankly, unforgiving. A misstep here isn't just a mistake—it's a direct threat to your organization's bottom line and hard-earned reputation.
For businesses in regulated industries, the rules are especially tight. Regulations like the Health Insurance Portability and Accountability Act (HIPAA) for healthcare or the Fair and Accurate Credit Transactions Act (FACTA) for finance don't offer suggestions; they impose strict mandates on how data is managed, even at the end of its life. A single discarded hard drive with patient records or financial data can trigger staggering penalties and painful legal battles.
This is why professional computer recycling services are a core part of any solid risk management strategy. It's about ensuring every last byte of data is properly accounted for and destroyed in a way that stands up to scrutiny.
The journey your assets take is a documented, secure process designed to ensure compliance at every single stage.
As you can see, a compliant process isn’t a single event. It’s a series of interconnected, secure steps that build on each other to create a verifiable audit trail from start to finish.
Demystifying the Chain of Custody
The "chain of custody" is the absolute backbone of compliant asset disposal. Think of it as the documented life story of your retired equipment. It's an unbroken, chronological paper trail that follows each asset from the moment it leaves your facility to its final destruction.
This documentation is your proof of due diligence. If an auditor ever asks what happened to a specific server or laptop, a strong chain of custody report provides an immediate, verifiable answer, complete with serial numbers, dates, and confirmation of data destruction. This is exactly why you need a detailed certificate of destruction for hard drives to close the loop on every single asset.
Without this proof, your organization is left exposed. It’s one thing to say you properly disposed of your assets; it’s another to prove it with meticulous, legally-sound documentation.
The Gold Standard of Industry Certifications
So, how can you be sure a potential partner actually meets these high standards? The answer is third-party certifications. These aren't just logos on a website—they are rigorous standards that a vendor must earn through intense, ongoing audits of their security, processes, and environmental practices.
The two premier certifications to look for are:
- R2v3 (Responsible Recycling): This standard covers the entire lifecycle, ensuring practices that protect the environment, worker health and safety, and data security. An R2v3 certified facility has proven its commitment to responsible electronics management.
- e-Stewards: Developed by the Basel Action Network, this certification is known for its incredibly strict standards, especially its absolute ban on exporting hazardous e-waste to developing nations. It’s often considered the gold standard for environmental and social responsibility.
Choosing a vendor with R2v3 or e-Stewards certification is the single most effective way to vet their capabilities. It confirms they have the systems, security, and downstream accountability required to handle your assets without putting your organization at risk.
The global electronic waste recycling market has seen incredible growth, valued at USD 70.1 billion in one recent year and projected to hit USD 80.8 billion the next. This growth highlights how much businesses now rely on professional services as technology lifecycles get shorter. North America leads this market with about 37% of the share, driven by strict regulations and a sophisticated recycling infrastructure.
How to Choose the Right Computer Recycling Partner
Picking a partner for your computer recycling services isn’t like choosing a shipping company. It's more like vetting a financial auditor. Both demand absolute trust, transparent processes, and meticulous documentation to shield your organization from serious risk.
The right partner acts as an extension of your compliance and security teams. The wrong one can leave you with liabilities that surface years down the road. You aren't just getting rid of old hardware; you're handing over your company's reputation and its most sensitive data. A low-cost quote might look good on paper, but if that vendor cuts corners on certifications or data security, the potential cost of a breach or environmental fine will dwarf any initial savings.
Core Vendor Evaluation Criteria
To properly evaluate potential partners, you need to dig into four critical areas. These are the pillars of a trustworthy IT asset disposition program that separate the real professionals from the simple scrap haulers. A solid vendor won’t just meet these criteria—they’ll be eager to prove it.
- Industry Certifications: This is your first and most important filter. Look for either R2v3 (Responsible Recycling) or e-Stewards. These certifications are non-negotiable. They confirm that an independent, third-party auditor has rigorously inspected the vendor’s processes for data security, environmental safety, and employee health.
- Data Destruction Methodology: Get specific about how they destroy data. Do they follow NIST 800-88 guidelines? Do they use multi-pass software wiping, physical shredding, or both? A top-tier provider offers both options and issues a serialized Certificate of Data Destruction for every single device that holds data.
- Downstream Transparency: A vendor's responsibility doesn't stop when your equipment leaves their facility. You need to know exactly where your assets go next. Ask for a complete map of their downstream recycling chain. Certified partners are required to vet every one of their downstream partners, ensuring nothing is illegally exported and all hazardous materials are handled correctly.
- Reporting and Logistics: The entire process must be backed by solid documentation and secure logistics. This means detailed inventory reports, secure GPS-tracked trucks, and a clear chain-of-custody record from the moment your assets are picked up to their final disposition. If a vendor is vague about their process, that’s a major red flag.
Key Questions to Ask During Vetting
Once you have a shortlist, it's time to ask some direct questions. How they answer will tell you everything you need to know about their professionalism and transparency. A reliable partner will have clear, confident answers ready.
- Can you provide a complete, auditable downstream trail for all recycled materials? This is a direct test of their commitment to environmental compliance.
- What are your insurance limits for data breach liability and errors and omissions? This shows they are financially prepared to stand behind their work and protect you from worst-case scenarios.
- How do you document and verify the chain of custody from our facility to yours? The answer should include serialized tracking, secure transport, and reconciliation reporting once the assets arrive.
- Are your employees background-checked and trained in data security protocols? The people handling your equipment are a critical link in the security chain.
- Can we tour your facility to observe your processes firsthand? A transparent vendor will welcome a visit. Any hesitation is a significant warning sign.
Before selecting a vendor, it's helpful to organize your evaluation. The checklist below provides a structured way to compare potential partners on the criteria that matter most.
Vendor Evaluation Checklist
| Evaluation Criteria | What to Look For | Why It Matters |
|---|---|---|
| Certifications | R2v3 or e-Stewards certification. Ask for their certificate number and verify it online. | Independent, third-party validation that their processes meet the highest industry standards for security and environmental safety. |
| Data Destruction | Adherence to NIST 800-88. Offers both software wiping and physical shredding. Provides serialized Certificates of Destruction. | Guarantees that your data is permanently and verifiably destroyed, eliminating the risk of a breach from discarded assets. |
| Chain of Custody | Secure, locked transport with GPS tracking. Detailed inventory reports. Clear documentation from pickup to final disposition. | Creates an unbroken, auditable trail for every asset, which is critical for compliance and proving due diligence. |
| Downstream Accountability | A fully vetted and mapped downstream recycling chain. No export of hazardous e-waste. | Ensures your company is not inadvertently contributing to environmental damage or illegal e-waste dumping. |
| Insurance & Liability | Substantial coverage for data breach liability, pollution, and errors & omissions. Ask for a Certificate of Insurance. | Provides a financial backstop and shows the vendor is serious about risk management and protecting their clients. |
| Facility Security | Secure facility with controlled access, surveillance, and employee background checks. | Protects your assets from theft or unauthorized access while they are being processed. |
Using a checklist like this ensures you perform the same level of due diligence on every potential partner, making your final decision objective and defensible.
Vetting a computer recycling services provider is all about verifying trust. You need a partner whose processes are as secure and auditable as your own internal financial controls. Any vendor who can't provide clear, documented answers to these questions introduces an unacceptable level of risk to your business. A partner with a robust certification, like being an R2 certified electronics recycler, has already passed rigorous third-party audits that confirm their commitment to these high standards. This independent verification is your best assurance of their capabilities and reliability.
The Link Between E-Waste and Corporate Responsibility
Working with professional computer recycling services is about much more than just compliance. It’s a powerful statement about your company’s commitment to Corporate Social Responsibility (CSR). Today, customers and stakeholders look closely at how a business operates, and the way you handle old technology has become a clear indicator of your environmental values.
When outdated electronics end up in landfills, they don't just sit there. They leach hazardous materials like lead, cadmium, and mercury into the soil and groundwater, causing long-term ecological damage. This growing mountain of electronic waste, or e-waste, is a significant threat that responsible businesses can no longer afford to ignore.
The Scale of the Global E-Waste Challenge
The sheer volume of discarded electronics is almost hard to imagine. In a single recent year, the world generated a staggering 62 billion kilograms of e-waste—an 82% increase from 2010. What’s truly shocking is that only 22.3% of it was properly collected and recycled.
That means countless tons of toxic materials and valuable resources were simply thrown away. This mismanagement leads to the release of an estimated 58,000 kilograms of mercury and 45 million kilograms of plastics containing harmful flame retardants into the environment each year, underscoring the urgent need for ethical disposal solutions.
Embracing the Circular Economy
A forward-thinking approach to this problem is the circular economy. Unlike the old "take-make-dispose" model, a circular economy keeps resources in use for as long as possible. Professional ITAD services are a direct and practical way to put this principle into action.
By partnering with a certified recycler, your business directly participates in the circular economy. Instead of creating waste, you are creating a resource stream that conserves energy, protects ecosystems, and reduces the need for new mining.
This process works in two key ways:
- Refurbishment and Reuse: Functional devices are given a second life, which is by far the most sustainable option. This extends a product’s value and shrinks the carbon footprint tied to manufacturing new equipment.
- Materials Recovery: For devices at the end of their life, valuable raw materials like gold, copper, and aluminum are carefully extracted and returned to the supply chain, reducing the environmental damage caused by mining for virgin materials.
Aligning with ESG Goals and Building Brand Trust
For modern businesses, Environmental, Social, and Governance (ESG) goals aren't just a talking point—they are key indicators of a company’s long-term health and ethical standing. Choosing certified computer recycling services gives you a tangible, measurable way to advance your ESG initiatives.
It sends a clear signal to investors, customers, and employees that your organization takes its environmental duties seriously. This commitment builds a positive brand reputation and sets you apart from competitors who might overlook this critical part of corporate citizenship. Ultimately, responsible e-waste management is about demonstrating leadership and contributing to a more sustainable future.
Explore our corporate e-waste solutions to see how we can help you meet your CSR objectives.
Common Questions About Computer Recycling Services
When it comes to IT asset disposition, IT and operations managers have a lot on their plates. Making smart decisions about your company’s retired technology means getting clear, direct answers to the right questions. This section cuts through the noise to address the most common inquiries we hear, giving you the practical information you need to manage your computer recycling process with confidence.
What Actually Happens to the Data on Our Old Computers?
This is—and should be—the number one concern. Professional computer recycling services don’t just wipe your data; they ensure it is permanently and verifiably destroyed using certified methods that meet strict standards like NIST 800-88.
A reputable partner will use one of two primary techniques. The first, and most absolute, is physical destruction. Your hard drives, solid-state drives, and other storage media are run through industrial shredders that grind them into tiny, irrecoverable pieces. It’s impossible to recover data from something that no longer physically exists.
The second method is data sanitization, which uses specialized software to overwrite every sector of a drive with random characters, often in multiple passes. This completely erases the information while keeping the drive intact, allowing it to be safely reused. After either process, you must receive a serialized Certificate of Data Destruction. This isn't just a piece of paper; it's your legal proof that the data is gone for good, protecting you from breaches and satisfying compliance auditors.
Can We Recover Any Financial Value from Our Old IT Gear?
Absolutely. Value recovery is one of the biggest benefits of working with a professional ITAD service. Just because a piece of equipment is retired doesn't mean it's worthless. A key part of the process is auditing your assets to see what still has life left in it.
Your provider will sort through your old equipment to separate items with resale potential from those that truly need to be recycled.
Items that often hold their value include:
- Recent-model laptops and desktops that can be refurbished for business or consumer use.
- Enterprise-grade servers and networking equipment like switches and routers, which are always in demand on the secondary market.
- Components like RAM, CPUs, and high-capacity hard drives that can be harvested and sold individually.
After all data is securely destroyed, these assets are tested, refurbished, and sold. The vendor then shares a portion of the revenue with you, which can help offset—or even exceed—the cost of the service. It's a smart financial move that also supports the circular economy by giving useful technology a second life.
What Kind of Documentation Should We Demand?
Comprehensive documentation isn't a "nice-to-have"—it's an absolute must for your audit trails and compliance records. A professional computer recycling partner must provide a complete set of documents that creates an unbroken, verifiable chain of custody for every single asset.
Think of this documentation as your legal shield. It's the definitive proof that your organization did its due diligence in handling sensitive data and managing e-waste responsibly. Without it, you're exposed to serious liability.
Your paperwork should always include these three essential reports:
- A Detailed Inventory Report: This lists every asset collected, identified by make, model, and unique serial number. It’s your proof of what left your facility.
- A Certificate of Data Destruction: This report legally certifies that all data on your hard drives and media has been destroyed, and it should list the serial numbers of the destroyed devices.
- A Certificate of Recycling: This final document confirms that all non-reusable materials were processed in an environmentally compliant manner, meeting all local, state, and federal regulations.
This complete paper trail gives you the transparency and accountability required to satisfy internal audits, regulatory inquiries, and corporate governance standards.
How Does the Pickup and Transportation Process Work?
A full-service ITAD partner handles all the logistics, making the process secure, efficient, and completely hands-off for your team. It all starts with scheduling a pickup at your facility at a time that minimizes disruption to your operations.
On the scheduled day, a team of trained, insured, and background-checked technicians will arrive to professionally pack, palletize, and load your equipment. This ensures your assets are protected from damage and handled securely from the moment they leave your control.
For transport, all assets are moved in locked, GPS-tracked vehicles. This is a critical security measure that maintains a secure chain of custody from your door to the processing facility. For larger projects, like a full data center decommissioning, the vendor manages the entire process—from on-site de-installation to final reporting. This allows your IT team to stay focused on their core responsibilities while the experts handle the complexities of asset retirement.
At Dallas Fortworth Computer Recycling, we provide secure, compliant, and transparent ITAD solutions tailored to the needs of modern businesses. Our certified processes ensure your data is destroyed, your environmental obligations are met, and your brand is protected. To learn more about our nationwide computer recycling services, visit us at https://dallasfortworthcomputerrecycling.com.
