A Guide to ITAD Services Frisco for IT Leaders
For businesses in Frisco, IT Asset Disposition (ITAD) is more than just getting rid of old computers. It’s the formal, strategic process for retiring technology securely, responsibly, and in a way that protects your organization from very real risks. This involves everything from certified data destruction and responsible electronics recycling to recovering value from equipment that still has life left in it.
Why Frisco Businesses Need a Strategic ITAD Partner

Frisco’s explosive growth as a business hub means the tech lifecycle here is moving faster than ever. To stay competitive, local companies are constantly upgrading servers, laptops, and networking hardware. But this rapid turnover creates a critical challenge: what do you do with all the old equipment?
Leaving retired assets in a storage closet or handing them to an unvetted recycler isn't just inefficient—it's a significant security and compliance gamble. That's where a formal ITAD strategy becomes indispensable. It’s not about disposal; it’s a vital business function that safeguards your company’s most sensitive data. Every retired hard drive, server, and company phone contains information that, if it fell into the wrong hands, could result in devastating breaches, regulatory fines, and lasting damage to your reputation.
Navigating Compliance and Recovering Value
A professional approach to ITAD services in Frisco directly addresses three core business needs:
- Data Security: Ensuring every last bit of confidential data is permanently destroyed using certified methods like those outlined in NIST 800-88.
- Environmental Compliance: Following all federal and state e-waste regulations to prevent hazardous materials from polluting landfills and creating liability for your company.
- Value Recovery: Finding assets that still have market value and remarketing them to generate a return that can offset your disposition costs.
This process is so critical that the global ITAD market, valued at USD 26.46 billion in 2026, is projected to hit USD 39.66 billion by 2031. This growth is fueled by increasing digital transformation and much stricter data privacy laws.
For IT leaders, the right ITAD partner isn't just another vendor—they are a risk management consultant. Their expertise is your first line of defense against a future data breach or compliance penalty.
Ignoring this essential function is no longer a viable option in today's business climate. To help you get started, this quick reference table summarizes what to look for when evaluating potential partners in the Frisco area.
Key Considerations for Selecting an ITAD Provider in Frisco
| Evaluation Criteria | What to Look For | Why It Matters for Frisco Businesses |
|---|---|---|
| Certifications | R2, e-Stewards, NAID AAA | These certifications prove the vendor adheres to the highest industry standards for data security and environmental responsibility. |
| Data Destruction Methods | Certified wiping, degaussing, physical shredding | A reputable partner offers multiple methods and provides Certificates of Data Destruction for your compliance records. |
| Chain of Custody | Secure logistics, asset tagging, detailed reporting | You need a documented, auditable trail from the moment assets leave your facility to their final disposition. |
| Value Recovery & Resale | Transparent process for testing, grading, and remarketing assets | A good partner helps you recoup value from viable equipment, lowering your total cost of ownership. |
| Local Presence & Logistics | DFW-based operations, on-site services | A local provider understands the North Texas business landscape and can provide fast, flexible, and secure pickups. |
Choosing a partner who checks all these boxes ensures your ITAD program is secure, compliant, and efficient.
As your trusted local partner since 2012, Dallas Fort Worth Computer Recycling has been helping Frisco businesses navigate these complexities for over a decade. We deliver a structured, secure, and fully transparent process for managing your end-of-life technology. For a closer look at best practices, our guide on Frisco electronics recycling offers more detailed insights. This guide will walk you through the essential steps to build your own effective ITAD program from the ground up.
How to Vet ITAD Vendors Like a Pro
Choosing an ITAD partner in Frisco isn't about finding the lowest bidder. It’s about doing the detailed homework required to shield your company from some pretty staggering financial and reputational blows. A slick website and a friendly sales pitch mean absolutely nothing without verifiable proof of security and compliance. Your vetting process should feel less like a vendor interview and more like an audit.
The conversation has to get beyond the surface-level stuff. Don't ask if they handle data securely. Ask them to show you the documented proof of how they do it. This is where the real evaluation starts.
Verify Key Industry Certifications
Your first line of defense is making sure any potential partner holds current, legitimate industry certifications. These aren’t just nice-to-haves; they are the gold standard for proving a provider has invested in proper security and environmental controls.
Never, ever take a vendor's word for it. You need to ask for the actual certificate copies and then go to the issuing body's website to check their online directory. Make sure the certification is active and in good standing.
- R2 (Responsible Recycling): This certification tells you the vendor follows established best practices for electronics recycling, with a focus on environmental safety, worker health, and data security.
- e-Stewards: Often considered the most rigorous standard in the industry, e-Stewards provides a guarantee that hazardous e-waste isn't being exported to developing nations and that all your data is handled securely.
- NAID AAA: This is the big one for data destruction. It verifies that a vendor’s methods for shredding, wiping, and degaussing meet the highest industry benchmarks for secure data sanitization.
A provider operating without these certifications is a massive red flag. It’s a clear signal they haven't put in the resources or work to build the infrastructure needed to protect their clients.
Scrutinize Their Security and Insurance Policies
Certifications are the starting point, but you also need to dig into the operational nitty-gritty. That means asking for the documentation that proves they’re ready to handle the risks that come with managing your sensitive equipment.
Ask for proof of their insurance coverage. Any legitimate ITAD company will carry policies designed specifically for this work. You're looking for Data Breach Insurance and Pollution Liability Insurance. These policies are what protect your organization if something goes wrong during the disposition process.
The single most important question you can ask a potential ITAD partner is this: “Can you describe your downstream vendor auditing process and provide a recent audit report?” This question cuts right to the chase and reveals whether they actually know where your assets end up or if their chain of custody breaks down the second your gear leaves their building.
You should also be asking about their internal security. Do they run background checks on every employee who might touch client assets? What kind of physical security do they have at their processing facility? A great way to get a feel for their operation is to schedule a facility tour. A transparent partner will be more than happy to show you around. As you evaluate your options, it helps to learn more about the leading IT asset disposition companies and what truly sets them apart.
Mastering Data Destruction and Compliance
Once your assets leave your facility, the real work begins. You've handed them over to a partner, but your responsibility for the data on those devices doesn't end. For any business in Frisco, especially if you're in a regulated field like healthcare or finance, this next step is non-negotiable. It’s all about ensuring every last bit of data is completely and permanently destroyed.
This isn’t just about deleting files. It's about meeting strict compliance standards and avoiding the massive risks—and fines—that come with a data breach. There's no one-size-fits-all method for this; the right approach depends entirely on the type of media and your organization's security policies.
Choosing the Right Destruction Method
Your ITAD partner should walk you through a few core options, matching the right technique to each asset. The three main methods you'll encounter are software wiping, degaussing, and good old-fashioned physical shredding.
Software Wiping (NIST 800-88 Standard): Think of this as the digital equivalent of scrubbing a surface clean. Specialized software overwrites the entire drive with random data, making the original information unrecoverable. This is the go-to for newer, working hard drives (HDDs) and solid-state drives (SSDs) that still have resale value.
Degaussing: This method uses an incredibly powerful magnet to scramble the magnetic field on traditional hard drives and tape media, effectively wiping them instantly. It's fast and thorough for HDDs, but it’s completely useless for SSDs, which store data electronically, not magnetically.
Physical Shredding: When a drive is too old, broken, or held data so sensitive that no chances can be taken, physical destruction is the final answer. The drive is fed into an industrial shredder that grinds it into small, mangled pieces of metal. There's no coming back from that.
Getting these methods right is fundamental to protecting your data. You can see how we implement these techniques by reading our guide to secure data destruction services.
A Frisco Healthcare Scenario
Let’s put this into a real-world context. Imagine a Frisco healthcare clinic is decommissioning a server room. Those servers are loaded with protected health information (PHI), putting HIPAA compliance at the forefront. A single mistake here could lead to millions in fines and a public relations nightmare.
In this situation, we would recommend a blended strategy. Newer server drives with market value would be sanitized using NIST 800-88 compliant software, allowing the clinic to recoup some of their initial investment. But for any older or failed drives, we'd degauss them and then send them straight to the shredder. This guarantees total data destruction and creates a clear audit trail.
Your most important piece of legal proof in this process is the Certificate of Data Destruction. This document, provided by your ITAD vendor, lists each asset by serial number and confirms the exact method used to destroy its data. It's your formal record of due diligence.
Beyond Data: Environmental Compliance
Compliance isn't just about data security. Getting rid of electronics the wrong way can put you in hot water with the EPA. A certified ITAD provider ensures that any materials that can't be reused are recycled responsibly, keeping toxic e-waste out of landfills. This protects the environment and shields your business from future liability.
The need for professional ITAD is growing fast. The data center ITAD market is projected to jump from USD 13.18 billion in 2026 to an incredible USD 28.76 billion by 2034. As you can see in these market growth projections, this isn't a niche service anymore—it's a critical business function.
By partnering with a certified expert like Dallas Fort Worth Computer Recycling, businesses across Frisco can confidently handle both data security and environmental regulations without a second thought.
Securing Your Assets with Flawless Logistics
A secure ITAD program is only as strong as its chain of custody. After you've vetted a partner and signed off on their data destruction methods, the focus shifts to the physical logistics—getting those assets from your Frisco office to their facility. This is where a professional ITAD service truly shows its value.
The entire process should feel controlled and organized, not like a chaotic scramble. It all starts with scheduling a pickup that works for you and causes the least disruption, whether that’s after hours or over a weekend. Before a single piece of equipment is moved, a thorough on-site inventory is absolutely critical.
On-Site Inventory and Secure Transport
A professional ITAD team doesn't just show up with a truck and start loading. They arrive ready to catalog every asset you’re handing over. This means scanning the serial number of each server, laptop, hard drive, and switch. That serialized inventory list is the foundation of your entire chain of custody.
Once everything is inventoried, the assets are carefully packed into secure, sealed containers right there on your premises. From that point forward, the journey of your equipment is completely transparent and trackable. Here’s what secure logistics looks like:
- GPS-Tracked Vehicles: Every truck is equipped with GPS, providing real-time monitoring from your location all the way to the processing facility.
- Sealed Containers: Your assets travel in locked, tamper-evident containers, ensuring nothing can be touched or removed in transit.
- Documented Handoffs: Every time custody changes hands—from your team to the logistics crew, and from the crew to the facility—it's documented with signatures.
This infographic shows the core methods we apply once your assets arrive securely for processing.
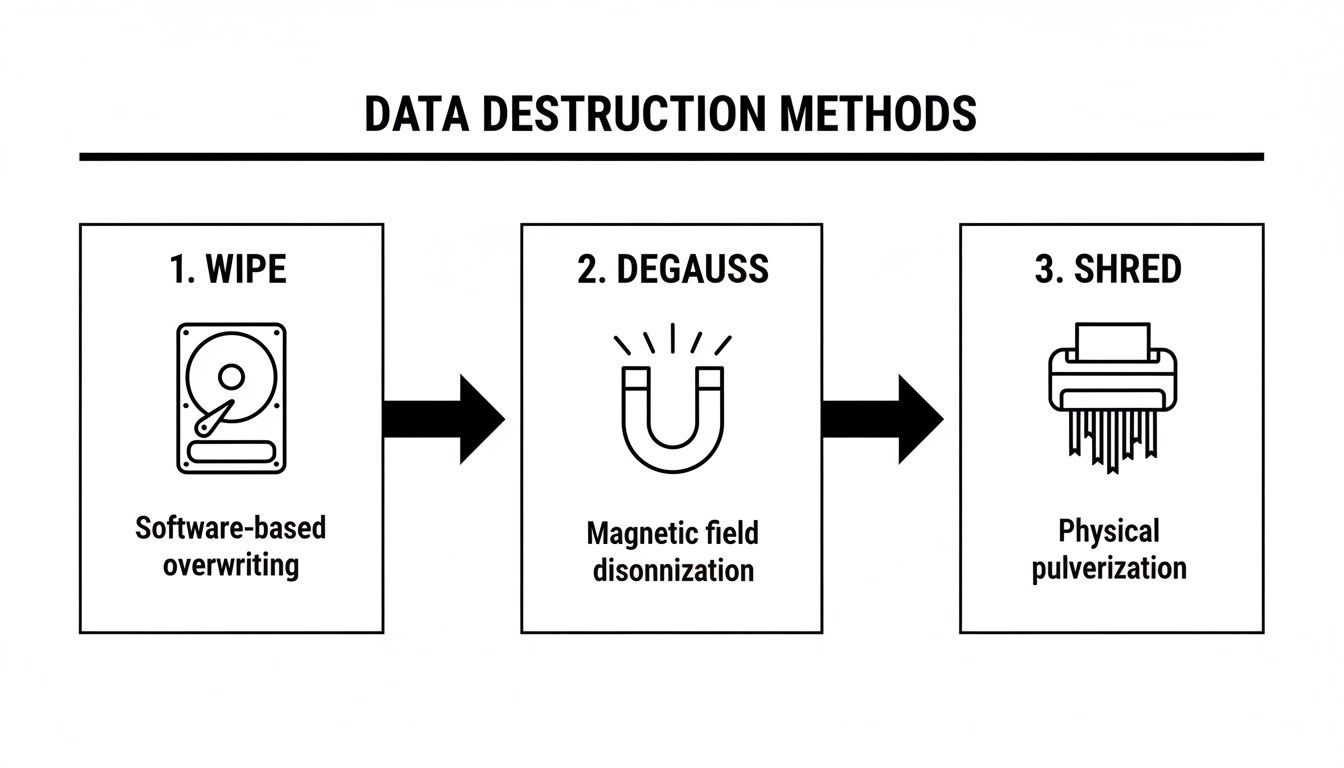
This illustrates how data is permanently eliminated through software wiping, magnetic degaussing, or physical shredding, depending on the asset type and your security requirements.
Peace of Mind Through an Auditable Trail
Let’s put this into a real-world context. A financial services firm in Frisco is decommissioning 500 laptops after an employee hardware refresh. The data on those devices is extremely sensitive. The IT director’s biggest concern isn't just that the data gets destroyed—it's having proof that all 500 devices were accounted for and properly sanitized.
For a project of this scale, the serialized audit trail is everything. It provides the documented proof needed to satisfy both internal risk managers and external auditors that no asset went missing or was improperly handled.
A qualified ITAD partner will provide a final report that reconciles the initial on-site inventory with the final disposition records. This report details what happened to each individual asset: which ones were wiped and remarketed, and which were physically destroyed. This level of detail gives you undeniable peace of mind.
For assets that require immediate destruction on-premises, you can learn more about how we facilitate onsite shredding near you for maximum security. Knowing what to expect and what to demand from your ITAD partner ensures no asset ever falls through the cracks.
Maximizing Value from Retired IT Assets

While security and compliance are non-negotiable, the financial side of IT asset disposition is just as important. A well-run ITAD program shouldn't just be a line item expense; it's a real opportunity to recover value from your retired hardware. Understanding how this process works helps Frisco businesses improve their project’s ROI.
Professional ITAD partners usually offer a couple of common pricing models. Some might charge a simple per-unit fee for recycling and data destruction, which makes sense for older or low-value gear. But for assets that still have life left in them, a value-sharing agreement is often the smarter financial move.
In this model, the ITAD provider tests, refurbishes, and remarkets your viable equipment. Once the hardware is sold, the revenue gets split between your company and the provider based on a pre-agreed percentage. This approach turns old assets into a revenue stream that can significantly offset your disposition costs.
Identifying Remarketable Assets
The key to maximizing your return is knowing which assets actually have resale potential. Not everything is destined for the shredder. A good ITAD partner will help you sort your inventory to pinpoint the high-value items.
Generally, the best candidates for resale include:
- Recent-Generation Servers: Enterprise servers less than five years old are often in high demand on the secondary market.
- Business-Class Laptops: Laptops from major brands that are only a few generations old can be refurbished and find new homes.
- Networking Gear: Enterprise switches, routers, and firewalls from brands like Cisco often hold their value surprisingly well.
- Bulk Monitors and Peripherals: While a single unit isn’t worth much, a large lot of matching monitors can be sold together.
On the other hand, older desktops, broken equipment, and outdated accessories are typically best slated for responsible recycling. It’s a crucial distinction, and if you have specific components you're curious about, check out our guide on where to sell used computer parts for cash.
The Pitfall of the Cheapest Option
It’s always tempting to go with the vendor offering the lowest upfront cost, but this is often a costly mistake in the long run. “Bargain-basement” providers frequently cut corners on security, compliance, and environmental standards. The potential cost of a data breach or a non-compliance fine can easily dwarf any initial savings.
A reputable partner for ITAD services Frisco provides transparent pricing that reflects the true cost of secure, responsible processing.
The smartest financial decision isn't finding the cheapest disposal service. It's partnering with a provider who can maximize your value recovery while guaranteeing compliance. The hidden costs of getting it wrong are simply too high.
This focus on responsible asset management is a cornerstone of the North American ITAD market, which was valued at USD 6.4 billion in 2025 and is driven by strong regulations and corporate sustainability goals. As detailed in these industry growth findings, certified ITAD is now standard business practice, not an optional extra.
Finally, responsible ITAD is a powerful tool for your corporate social responsibility (CSR) goals. By prioritizing reuse through programs like our 'Beyond Surplus' initiatives, you not only recover value but also support local nonprofits and reduce your environmental footprint—a win for your budget and your brand.
Your Questions About ITAD Services in Frisco Answered
When it comes to IT Asset Disposition, we know IT directors and procurement teams in Frisco have practical questions that need straight answers. Here’s a breakdown of the common inquiries we handle, giving you the clarity needed to manage your end-of-life technology with confidence.
What Types of Equipment Do You Accept?
A common concern is whether a single partner can handle every type of asset you need to retire. When evaluating ITAD services Frisco businesses depend on, you need a provider who can manage your entire inventory, not just the easy stuff.
We accept a comprehensive range of B2B technology. This, of course, includes all the standard office equipment you’d expect us to handle:
- Computers and laptops
- Monitors and docking stations
- Printers, scanners, and copiers
- Servers and networking switches
Beyond that, we specialize in the more complex hardware found in data centers and regulated environments. We’re equipped to manage server racks, UPS systems, storage arrays, and specialized medical and lab equipment, ensuring every item is processed securely and in full compliance with industry standards.
The goal of a true ITAD partner is to be a single point of contact for all your retired technology. You shouldn't have to find separate vendors for your laptops, your data center gear, and your old phone systems.
If you have unusual or highly specialized assets, we can address them directly during our initial consultation. Our process is designed to handle nearly any electronic equipment your organization needs to retire.
How Do We Start the Process of Scheduling a Pickup?
We've designed our process to be simple and efficient for busy IT departments. To get started, you can either call us directly or fill out the form on our website.
We’ll have a brief, straightforward discussion to understand the scope of your project—what you have and how much of it there is. Based on that information, we'll provide a service quote and coordinate a pickup time at your Frisco facility that works for your team and causes minimal disruption.
Our logistics team handles all the planning from there. You won't have to worry about the details; we manage the entire on-site process to ensure a smooth, professional, and efficient pickup.
Is It Possible to Recover Value from Our Old IT Equipment?
Yes, and this should be a key part of any strategic ITAD program. We don't just see old hardware; we see an opportunity to generate a return for your organization and improve the ROI on your initial investment.
Our team evaluates your entire inventory to identify assets with remaining market value. This often includes newer-model laptops, enterprise-grade servers, and networking equipment that can be refurbished and resold.
For these assets, we offer transparent value-sharing agreements. After the devices are securely sanitized, tested, and sold on the secondary market, we return a portion of the proceeds directly to you. This financial return helps offset disposition costs and can turn a necessary expense into a budget-positive project.
What Documentation Will We Receive for Compliance?
Solid documentation is the bedrock of a compliant ITAD process. It’s your proof of due diligence and the official record that protects your organization.
After every project, we provide a complete documentation package for your compliance and audit records. This includes:
- A serialized inventory list that accounts for every asset we processed.
- A formal Certificate of Data Destruction that specifies the sanitization method used for each data-bearing device.
- A Certificate of Recycling confirming that all non-reusable materials were processed in an environmentally responsible manner.
This documentation provides a clear and unbroken chain of custody, giving you an auditable trail that demonstrates your commitment to data security and regulatory compliance.
Ready to implement a secure and compliant ITAD strategy for your Frisco business? The team at Dallas Fortworth Computer Recycling has been the trusted partner for organizations across North Texas for over a decade. We provide the certified processes, secure logistics, and detailed documentation you need to retire your IT assets with complete confidence. Learn more and schedule your consultation today.
