Secure & Compliant IT Asset Disposition Arlington

For any business in the Arlington area, figuring out what to do with old technology is more than just a cleanup task. A formal IT asset disposition plan is a crucial business process for preventing data breaches, staying compliant with regulations, and even recovering money from your outdated hardware.
What Is IT Asset Disposition and Why Is It Essential?
IT Asset Disposition (ITAD) is the formal, secure process for retiring and disposing of a company’s technology assets. This includes everything from computers and servers to network gear and mobile devices.
Simply tossing an old hard drive or server is a huge risk for Arlington businesses. A single device that isn't handled correctly can lead to a disastrous data breach, causing serious damage to your brand and resulting in steep fines. A professional ITAD program turns this risk into a secure, sustainable, and well-managed part of your IT operations.
The Core Pillars of ITAD
A professional ITAD process is built on a few key pillars. Each one is essential for retiring your technology the right way, making sure no detail is overlooked. Any comprehensive approach to IT asset disposition in Arlington must balance these components to be effective.
Here’s a quick look at the main components of a professional ITAD program.
IT Asset Disposition At a Glance
| Core Pillar | Objective | Key Action |
|---|---|---|
| Data Security | Eradicate all sensitive data from devices. | Perform certified data wiping, degaussing, or physical shredding. |
| Value Recovery | Maximize financial return on retired assets. | Test, refurbish, and remarket functional equipment through certified channels. |
| Environmental Compliance | Ensure responsible, eco-friendly disposal. | Recycle non-reusable materials according to R2 and EPA standards. |
These three pillars work together to provide a complete, end-to-end solution.
Data Security: The absolute top priority is ensuring that every bit of sensitive information on your old devices is completely and verifiably destroyed. This eliminates any chance of a data breach from retired equipment.
Value Recovery: Many retired IT assets still have significant financial value. An important goal is to identify this equipment, refurbish it for reuse, and sell it to recoup some of your original investment.
Environmental Compliance: Throwing electronics in the trash is illegal and harms the environment. ITAD ensures that all non-working materials are recycled according to strict environmental standards, keeping e-waste out of landfills.
The global IT asset disposition market isn't just growing—it's accelerating. Valued at about USD 18.61 billion in 2025, it's projected to hit USD 38.22 billion by 2034. This rapid growth shows that businesses in tech-focused hubs like Arlington are moving away from simple disposal. Instead, they’re adopting strategic end-of-life management that turns old hardware from a liability into a secure asset.
This disciplined process protects your business from multiple angles. When you implement a formal ITAD strategy, you're not just clearing out an old storage room—you're securing your company's data, finances, and reputation.
The Complete ITAD Process for Arlington Businesses
When it's time to retire old IT equipment, Arlington businesses need a clear, secure process. A professional IT asset disposition (ITAD) partner follows a strict roadmap designed for total security and accountability, ensuring nothing is lost or exposed from the moment equipment leaves your office until its final certified disposal.
This process starts with a plan to identify and catalog every asset slated for retirement—from servers and laptops to printers and networking gear. This initial inventory is the foundation for a secure and auditable project.
Establishing the Chain of Custody
The most critical step is establishing an unbreakable chain of custody. Think of this as a documented paper trail that tracks every single asset. A reputable ITAD provider creates a detailed inventory, assigning a unique serial number or asset tag to each device before it’s moved.
This is a non-negotiable part of the process. It guarantees that every hard drive and server is accounted for, from your Arlington facility to our secure processing center. This serialized tracking is your first and best defense against asset loss and potential data breaches.
Once everything is cataloged, trained and background-checked technicians securely pack and transport your assets in locked, GPS-tracked vehicles. This isn't a job for a standard moving company; it demands specialized logistics built entirely around security.
The Secure Data Destruction Phase
Once your assets arrive at our certified facility, the top priority becomes permanent data destruction. This goes far beyond simply deleting files. Professional ITAD services follow strict standards, primarily the NIST 800-88 Guidelines for Media Sanitization, which details three methods for destroying data.
- Data Wiping (Clear & Purge): This software-based approach overwrites the entire storage device with random data, often in multiple passes. The process makes the original data completely unrecoverable but keeps the physical drive intact for potential reuse, which helps recover value.
- Degaussing (Purge): Using a powerful magnetic field, this method instantly destroys the magnetic signature on hard drives and tapes where data is stored. While incredibly fast and effective, it also renders the drive unusable, eliminating any resale value.
- Physical Shredding (Destroy): For the highest level of security or for devices that are already dead, physical destruction is the final answer. We feed assets into industrial shredders that grind them into tiny, unrecognizable fragments, making data recovery impossible.
A key takeaway is that you, the data owner, decide which method aligns with your company's security policy and budget. Certified data wiping is often sufficient for most business needs and maximizes the potential for financial returns.
The infographic below shows how our secure ITAD program works, highlighting the relationship between security, recycling, and value recovery.
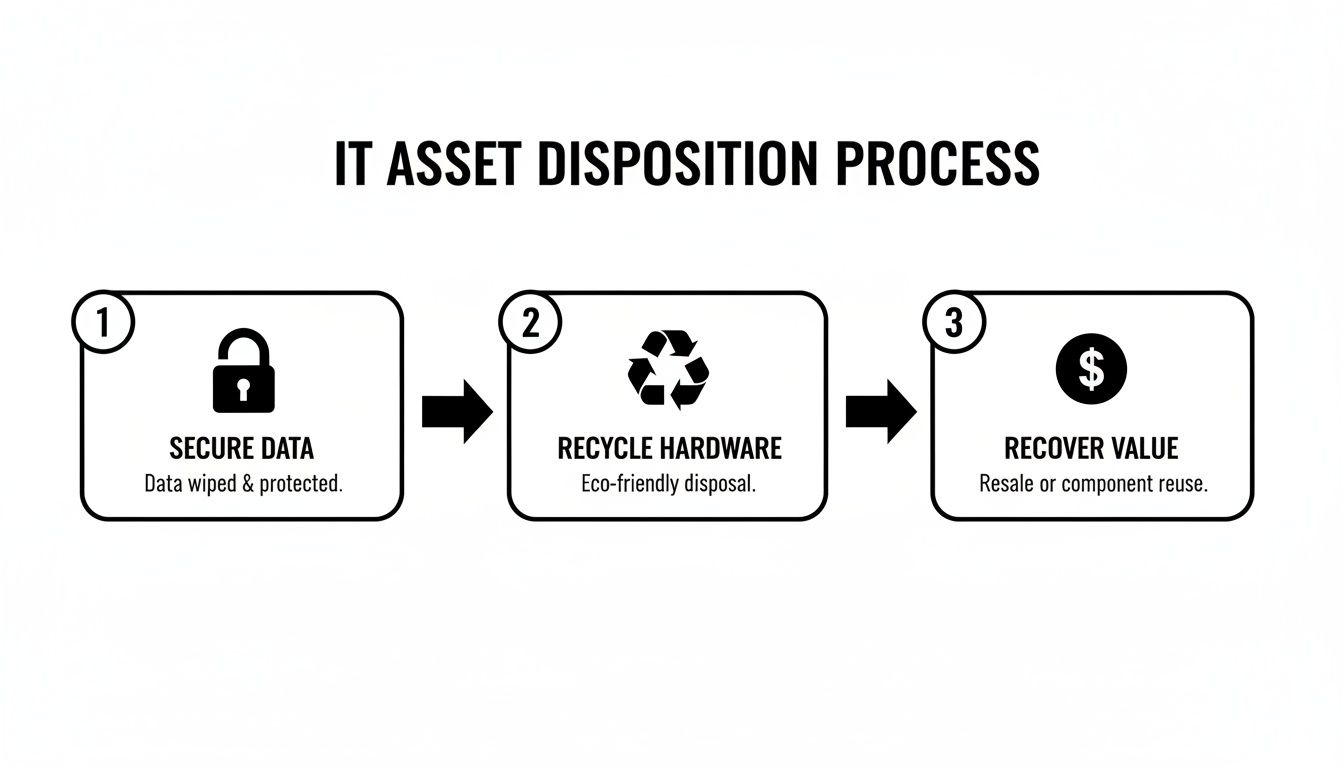
This proven process ensures every retired asset is handled with a clear purpose, whether that’s securing data, recycling materials responsibly, or recovering money for your organization.
Remarketing and Responsible Recycling
After all data is securely destroyed, our focus shifts to processing the physical assets. Technicians test each piece of equipment to assess its condition and functionality. This sorting step is a crucial part of the IT asset disposition Arlington lifecycle, as it determines the best path forward for every device.
Functional, late-model equipment is refurbished and prepared for resale. This value recovery process can generate a significant financial return for your company, helping turn a disposal cost into a revenue stream. Items that can't be reused but have working components may be disassembled for spare parts.
For any equipment that is non-functional, obsolete, or has no resale value, responsible recycling is the final step. To learn more, check out our guide on IT equipment recycling in Arlington. This ensures all materials are broken down in an environmentally compliant manner, preventing hazardous e-waste from ever reaching a landfill.
Once the job is done, you receive two critical documents: a Certificate of Data Destruction and a Certificate of Recycling. These auditable reports provide serialized proof that your data was destroyed and your hardware was handled in compliance with all environmental regulations, officially closing the loop on your ITAD project.
Navigating Data Security and Environmental Regulations
When your Arlington business retires old IT assets, simply ignoring compliance isn't an option. There's a complex web of data security and environmental laws that govern this process. One misstep can lead to serious financial penalties and damage the reputation you've worked hard to build.
A professional IT asset disposition Arlington provider isn't just a mover; they are compliance experts who shield your business from these risks. They understand that when you handle retired technology, you're responsible for two critical things: securing the sensitive data on those devices and disposing of the electronic waste correctly.
Understanding Key Data Privacy Laws
Data privacy regulations exist to protect consumer information, and the penalties for getting it wrong are steep. Depending on your industry, several federal laws directly impact your ITAD process. Think of these as a non-negotiable rulebook for protecting the data you've been entrusted with.
- HIPAA (Health Insurance Portability and Accountability Act): If you're in healthcare in Arlington—from a major hospital to a private practice—HIPAA is your top priority. It demands that all patient health information (PHI) on any device, whether it's a server, laptop, or medical cart, is made completely unrecoverable before disposal.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions like banks, investment firms, and insurance companies must follow GLBA. This law requires protecting consumers' private financial information, making certified data destruction an absolute must for any retired IT gear.
- FACTA (Fair and Accurate Credit Transactions Act): This act touches nearly every business that handles consumer information. Its Disposal Rule requires the secure and permanent destruction of any data pulled from consumer credit reports.
Failure to comply with these laws can bring fines in the millions of dollars for a single incident. A certified ITAD partner ensures every single device is sanitized according to these strict legal standards, giving you a clear audit trail to prove you did your due diligence. If you work with patient data, you can learn more in our guide to HIPAA-compliant electronics recycling in Texas.
Environmental Regulations for E-Waste
Beyond securing data, federal and state environmental laws tell you exactly how you must dispose of electronic waste, or e-waste. Your old electronics are filled with hazardous materials like lead, mercury, and cadmium, which can easily contaminate soil and groundwater if they end up in a landfill.
The Environmental Protection Agency (EPA) regulates e-waste nationally, and Texas has its own specific rules managed by the Texas Commission on Environmental Quality (TCEQ). These regulations make it illegal to just toss IT equipment in the trash. Responsible disposal isn't just good practice—it's the law.
A professional ITAD provider makes sure all non-working equipment is properly dismantled and recycled in full compliance with all EPA and TCEQ regulations. This protects your organization from environmental liability and shows a real commitment to corporate sustainability.
This is where industry certifications become your most valuable tool for vetting a vendor. They act as a guarantee that a company's processes have been independently audited and verified.
The Power of R2v3 and e-Stewards Certifications
So, how can you be sure an ITAD vendor actually follows all these complex rules? The answer is third-party certifications. These aren't just fancy logos for a website; they are your proof that a partner is committed to the highest industry standards.
The two premier certifications to look for are:
- R2v3 (Responsible Recycling): The R2v3 standard is the gold standard, covering data security, environmental protection, and worker health and safety. An R2v3-certified facility has passed tough audits confirming its processes for secure data destruction, materials tracking, and responsible downstream recycling.
- e-Stewards: This is another leading global certification that is laser-focused on preventing the illegal export of hazardous e-waste to developing nations. It also has very strict requirements for data security and environmental performance.
Choosing an R2v3 or e-Stewards certified partner for your IT asset disposition Arlington needs is the single best way to guarantee compliance. It means you're working with a true professional who is regularly audited and held accountable, setting them miles apart from uncertified operators who might cut corners and put your business at risk.
Choosing The Right ITAD Partner In Arlington

When it comes to IT asset disposition Arlington businesses can trust, selecting your vendor is the most critical step. It’s easy to focus on the price tag, but a bargain-basement quote often signals major risks to your data security and compliance. Think of it this way: you’re not just hiring a moving company, you're hiring a security firm for your data.
A professional ITAD partner is your first line of defense. They provide the certified processes and auditable paper trail that prove you’ve done your due diligence. That documentation is what protects you from the staggering financial and reputational fallout of a data breach. The right partner turns a complex liability into a secure, managed process.
Vendor Vetting Checklist for Secure ITAD
Vetting potential partners requires a clear-eyed look at their credentials, processes, and transparency. A premier partner will welcome detailed questions and provide clear documentation, while a risky operator will often be vague or evasive. This checklist helps you tell the difference.
| Evaluation Criterion | Premier Partner (What to Look For) | Risky Operator (What to Avoid) |
|---|---|---|
| Certifications | Proudly displays R2v3 or e-Stewards certifications, validated by third-party audits. | Lacks industry certifications or uses vague, self-made "eco-friendly" claims. |
| Data Destruction | Offers NIST 800-88 compliant methods and provides detailed, serialized Certificates of Data Destruction. | Cannot provide sample documentation or offers non-compliant "wiping" with no proof. |
| Chain of Custody | Provides secure, GPS-tracked transport, serialized asset tracking, and access-controlled facilities. | Uses unmarked vans, offers no asset tracking, and has a disorganized warehouse. |
| Downstream Vetting | Maintains a fully audited and certified downstream vendor chain for all recycled materials. | Cannot tell you where your e-waste actually ends up or if it’s exported illegally. |
| Transparency | Eagerly answers questions, provides facility tours, and offers clear, detailed quotes. | Hesitates on specifics, avoids direct questions, and offers quotes that seem too good to be true. |
By using this framework, you can confidently evaluate whether a potential vendor will be a true security partner or a liability waiting to happen. A thorough vetting process is your best defense against the risks of improper IT asset disposal.
Key Questions To Ask Your Potential Partner
Once you have a shortlist, it's time to dig into the operational details. A professional, transparent partner will have ready answers for these questions—a hesitant or vague response is a major red flag.
- "Can you provide a sample Certificate of Data Destruction and Certificate of Recycling?" These documents are your proof of compliance. Make sure they include serial numbers for each asset.
- "How do you maintain chain of custody from our office to your facility?" Look for specifics like locked, GPS-tracked vehicles, uniformed employees, and serialized inventory lists created on-site.
- "Are your downstream recycling partners also certified?" An R2v3 certified partner is required to vet their entire downstream, ensuring your e-waste is never dumped or illegally exported.
- "Do you offer on-site data destruction?" For assets with the most sensitive data, having the option to witness destruction at your own facility provides ultimate peace of mind.
A vendor who has built their business on security and accountability won't just have these answers; they'll be proud to share them.
Finding A Partner Who Fits Your Needs
Beyond the non-negotiables, the right partner for IT asset disposition Arlington businesses need is one who understands your specific project. Refreshing 50 laptops for a sales team is a completely different logistical challenge than decommissioning an entire data center with hundreds of servers.
A flexible partner can scale their services to fit your scope, security needs, and budget. They should work with you to choose the right data destruction methods and have established remarketing channels to maximize the financial return on your reusable equipment. For a closer look at what these credentials mean, you can learn more about being an R2 certified electronics recycler.
Real-World Scenarios of Secure ITAD
It's one thing to read about ITAD processes, but it’s another to see how they work in the real world. Let’s walk through a couple of common situations we handle for Arlington-area businesses every day.
These stories show how a professional IT asset disposition program isn't just a service—it’s a practical solution that secures your data and recovers asset value. First, a local healthcare provider retiring patient devices, then a tech company refreshing its data center.
Scenario 1: A Healthcare Clinic Retiring Patient Kiosks
An urgent care clinic in Arlington decided to upgrade its entire check-in system. This meant retiring 25 patient-facing kiosks and 40 older staff laptops, all loaded with protected health information (PHI). For the clinic’s IT director, HIPAA compliance was non-negotiable, as any mistake could result in massive fines and a devastating loss of patient trust.
They needed a partner they could count on, so they chose an R2v3-certified specialist in IT asset disposition in Arlington. Here’s how the process played out.
On-Site Inventory and Secure Transport: Our team arrived at the clinic to create a serialized inventory, tagging every single kiosk and laptop. The devices were then loaded into a locked, GPS-tracked truck, establishing a solid chain of custody right from the start.
Certified Data Destruction: The data was extremely sensitive, so the clinic opted for a dual approach. We performed NIST 800-88 compliant data wiping for the newer laptops that had resale value and physical shredding for the older, obsolete kiosks.
Auditable Reporting: In just a few days, the clinic received a serialized Certificate of Data Destruction. This document is a legal record, listing every device by its serial number and confirming the exact method and date of destruction. It provided them with an airtight audit trail for HIPAA.
In this case, the ITAD partner acted as a compliance shield. By providing certified destruction and meticulous documentation, they allowed the healthcare provider to upgrade its technology without risking a data breach or violating complex federal regulations.
This is a perfect example of why professional ITAD is crucial for any organization handling regulated data. It’s not just about disposal; it’s about complete risk mitigation.
Scenario 2: An Enterprise Refreshing Its Data Center
A growing Arlington technology firm needed to expand its on-premise data center. The project involved decommissioning 30 servers, 15 network switches, and a full storage area network (SAN) array. Their goals were clear: guarantee 100% data destruction and recover as much money as possible to help fund the new hardware.
This kind of project requires specialized expertise. If you're facing a similar challenge, our guide on the data center decommissioning process offers more in-depth insights.
The ITAD vendor they selected tackled the project with a dual focus on security and value recovery.
- Systematic Decommissioning: The team coordinated with the company's IT staff to safely power down and disconnect all equipment, carefully labeling every component to maintain the chain of custody.
- On-Site and Off-Site Destruction: The SAN array held the company’s most sensitive R&D data, so we performed on-site shredding of the hard drives right at their facility. The server drives, which had less critical data, were securely moved to our facility for multi-pass data wiping.
- Value Recovery and Remarketing: Once sanitized, the functional servers, switches, and other components were tested, graded, and refurbished. Using an established resale network, the ITAD partner sold the equipment, recovering over $15,000 for the client.
The tech firm got detailed settlement reports showing exactly what sold and for how much, plus certificates for all destroyed media. They were able to securely upgrade their infrastructure and turn retired assets into a significant budget boost. These scenarios prove that a strategic IT asset disposition Arlington plan is more than just an operational task—it's a smart business move.
Common Questions About IT Asset Disposition in Arlington
Even when you understand the ITAD process, practical questions about cost, timelines, and paperwork always come up. For IT managers in the Arlington area, getting clear answers is key to moving forward. Here are the direct answers to the questions we hear most often, so you have the confidence to build a secure and compliant IT asset disposition strategy.
What Does IT Asset Disposition Cost in Arlington?
There’s no flat rate for an IT asset disposition Arlington project. The cost is quoted for each job because it depends entirely on the work involved.
Think of it less like a single price tag and more like a scope of work. The final cost comes down to a few key variables:
- Volume and Type of Equipment: A small office refresh of 20 laptops has a very different cost profile than decommissioning a data center full of servers and networking gear.
- Data Destruction Method: On-site physical shredding is the most secure but also the most intensive option. Software-based wiping that follows NIST 800-88 standards is often more cost-effective and allows the drives to be reused, which can increase their resale value.
- Logistics: The complexity of the pickup matters. Removing equipment from a high-rise office building or a secure data center requires more planning and labor than a simple ground-floor collection.
- Value Recovery Potential: This is the biggest factor. If your equipment is recent and has high market value, the revenue from remarketing can significantly offset or even eliminate your costs. In many cases, these pickups can be free.
Be wary of quotes that seem unusually low. Rock-bottom pricing can be a red flag for cutting corners on data security, environmental compliance, or proper certification. A professional partner will always provide a transparent, itemized quote that breaks down all fees for logistics, data destruction, and recycling.
How Long Does the ITAD Process Take?
The project timeline is tied directly to the size and complexity of the job. A standard office pickup is typically fast, while a major decommissioning requires more coordination.
For a common office cleanout of 50 to 100 devices, the entire process can often be completed within 1-2 weeks from your initial call to receiving your final reports. This allows for proper scheduling, secure transport, and thorough processing.
On the other hand, a multi-phase data center decommissioning could take several weeks. These projects involve more detailed steps like on-site auditing, carefully de-racking servers, and coordinating with your IT team to prevent any disruption to your operations.
A professional ITAD partner will give you a clear, projected timeline upfront. You should expect consistent communication and chain-of-custody updates throughout the process, so you're never left wondering about the status of your assets.
This ensures you have full visibility from the moment your equipment leaves your facility until you have the final certificates in hand.
What Documentation Will I Receive?
The paperwork you receive isn't just a receipt—it's your proof of compliance. These documents are your official record for internal audits and legal protection, demonstrating that you followed all regulations like HIPAA or GLBA.
When your project is complete, you should expect two critical documents:
- A Certificate of Data Destruction: This is your most important piece of documentation. It should be a serialized report that lists every single hard drive or storage device by serial number, confirming the exact method of destruction (e.g., NIST 800-88 Purge) and the date it was performed.
- A Certificate of Recycling: This document confirms that all non-reusable materials were processed and recycled in an environmentally responsible manner, adhering to R2v3 and EPA standards.
If any of your assets were sold, you will also receive detailed settlement reports. These reports transparently show what was sold, where it was sold, and the net revenue returned to your company, closing the loop on the value recovery process.
Can You Handle Specialized Equipment?
Yes, a full-service IT asset disposition Arlington provider should be well-equipped to manage specialized IT assets beyond standard office computers. This is especially important for organizations in healthcare, manufacturing, and R&D.
Medical devices, industrial control systems, and lab equipment often have embedded storage that holds sensitive patient data or proprietary information. They can also contain materials that require special handling under environmental laws.
A certified ITAD vendor must have specific protocols to:
- Identify and sanitize data from proprietary and embedded systems.
- Ensure full compliance with regulations like HIPAA for medical equipment.
- Responsibly manage the recycling of all components, including any hazardous materials.
Before you partner with a vendor, always confirm they have direct experience with your specific types of equipment. This ensures they have the technical expertise and processes to handle your assets securely and correctly.
Ready to implement a secure, compliant, and cost-effective ITAD strategy? Dallas Fortworth Computer Recycling offers certified, nationwide services tailored to your organization's needs. Schedule your free assessment and let our experts handle the rest.
