Telecommunications Company Near Me: IT Leader’s Guide
Typing telecommunications company near me into Google is fine if you need home internet, a store locator, or a quick check on local coverage. It’s weak procurement practice for an enterprise circuit, a data center uplink, a healthcare voice platform, or a multi-site WAN. Search results skew toward consumer listings, speed-test pages, and tower maps. They rarely tell you whether a carrier has real route diversity into your building, competent implementation teams, or a clean process for retiring the hardware you’re replacing.
That gap matters more than most buying teams admit. The telecom side of the decision gets all the attention. The displaced routers, firewalls, switches, PBX gear, and edge appliances get handled later, usually under deadline pressure and with thin documentation. That’s how avoidable risk shows up. You don’t want your procurement process to end at install day.
Why 'Near Me' Fails for Enterprise Telecom Needs
A local office isn’t the same thing as local network presence. For business telecom, that distinction decides whether you get a clean turn-up or a fragile service with too many dependencies hidden behind a glossy quote.
The public web doesn’t help much. Search results for this phrase are dominated by residential provider pages and coverage tools, while the business problem is usually about carrier design, implementation discipline, and hardware retirement. One of the more useful facts in this space is that a 2025 Gartner report on ITAD trends noted only 15% of businesses report having an audited chain-of-custody for surplus equipment created by network upgrades, as summarized in this analysis of the content gap around telecommunications company near me. That’s the part most “near me” guides miss entirely.
What consumer search results get wrong
Residential advice usually answers the wrong questions:
- Availability over architecture. It tells you who can sell service at an address, not how that service reaches the address.
- Price over resilience. It compares monthly plans but skips conduit paths, failover design, and escalation processes.
- Installation over lifecycle. It treats cutover as the finish line, when enterprise teams still have to decommission and document retired gear.
If your environment supports revenue systems, regulated workflows, or public services, location-based shortlists can create false confidence. A provider can have a nearby sales branch and still depend on leased infrastructure, overloaded local handoffs, or messy subcontractor coordination.
Practical rule: If the vendor’s strongest proof point is “we serve your area,” keep digging. Enterprise telecom is about engineered delivery, not ZIP-code marketing.
What an IT team should search for instead
Use the phrase telecommunications company near me only as a starting signal. Then move fast into due diligence that tests network reach, implementation quality, and disposition planning. The retirement of replaced hardware should sit in the same workstream as circuit procurement, especially if old equipment still holds configs, credentials, call records, or topology details.
Teams that need to address the disposal side of the project can use resources focused on computer recycling options for business equipment to frame internal requirements before the rollout starts.
Redefining Your Search From Proximity to Presence
The better question isn’t “who’s near me?” It’s “who is already present where my business operates, and how much of that presence do they control directly?”
In the U.S., scale alone tells you why local office proximity is a weak filter. The telecommunications sector is forecasted to reach 336 billion USD in 2024, and the market supports over 390 million mobile subscriptions, which shows how much value sits in nationwide infrastructure reach rather than storefront location, according to Statista’s U.S. telecom market overview.
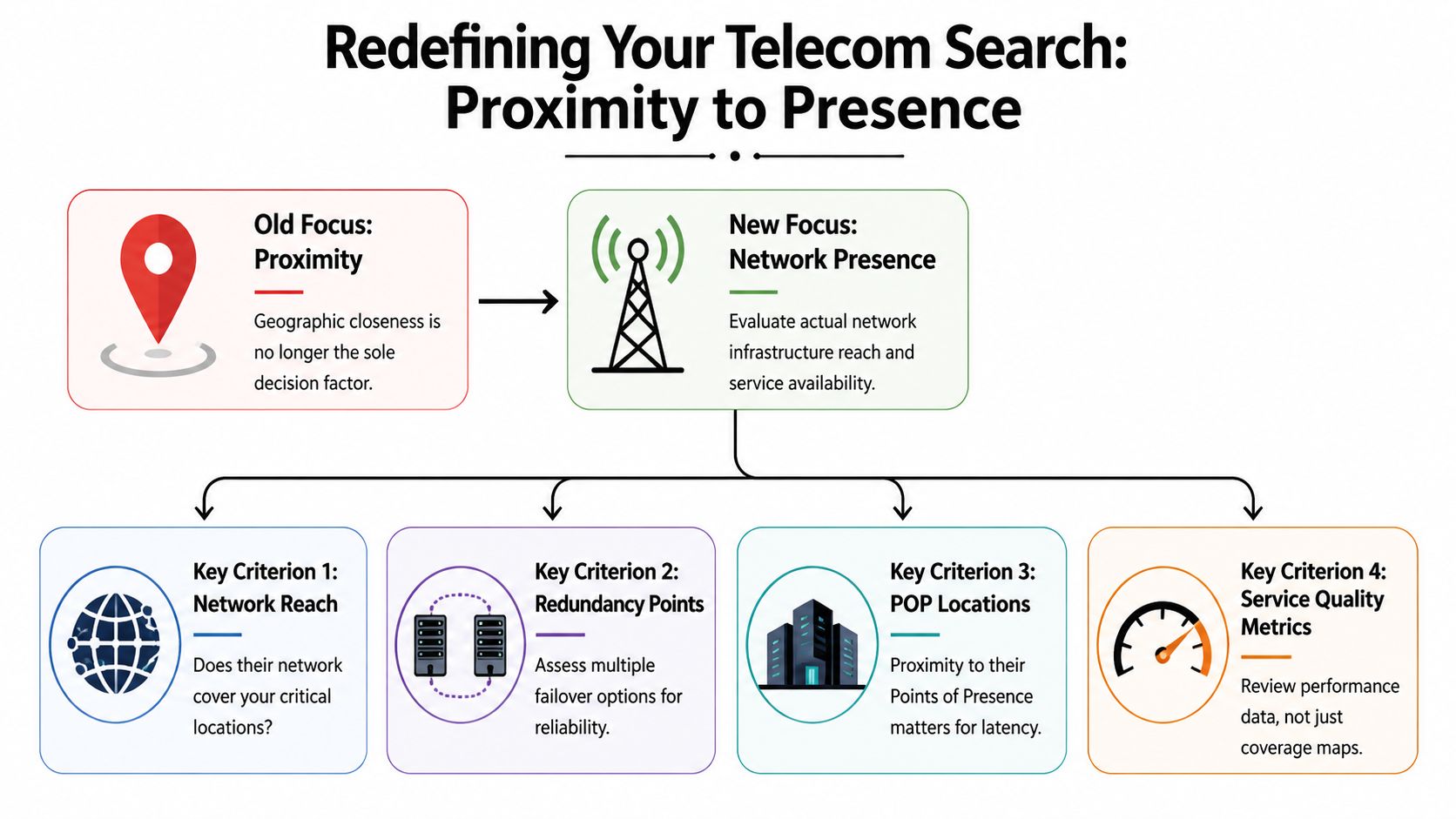
What presence actually means
A provider’s presence includes several things procurement teams should separate clearly:
- On-net building status. If the carrier is already in your building, install risk is usually lower than a fresh construction scenario.
- Points of Presence. A nearby PoP often matters more than a nearby office because it affects handoff options and latency.
- Control of the last mile. Providers that own or tightly manage access paths usually resolve issues faster than those layering multiple third parties.
- Cloud and data center adjacency. If your workloads live in colocation or public cloud, interconnection strategy matters as much as branch connectivity.
Don’t accept “we service that area” as an answer. Ask whether the provider is on-net, near-net, or fully dependent on another carrier for the final segment. Those are different risk profiles, even if the monthly recurring price looks similar.
A better search workflow
Replace broad local search with a tighter sourcing sequence:
- Start with your addresses, not the vendor list. Include headquarters, branches, call centers, clinics, warehouses, and data centers.
- Map business criticality to each site. A site with voice, payment, dispatch, or EHR dependence needs stricter carrier scrutiny.
- Check building connectivity posture. Determine whether each site is already lit by one or more enterprise carriers.
- Ask for route narratives. Not just maps. Written descriptions reveal whether the seller understands the path.
- Compare implementation ownership. Who surveys, who builds, who coordinates building entry, who tests, who documents?
That workflow sounds basic, but it immediately filters out a lot of weak-fit vendors.
What to look for in vendor responses
Good carrier responses are specific. Weak responses are promotional.
| Response quality | What you’ll hear |
|---|---|
| Strong | Clear on-net status, handoff options, install dependencies, escalation process |
| Weak | Broad coverage claims, generic uptime language, little detail on last-mile ownership |
| Risky | “We’ll confirm after order acceptance,” vague implementation milestones, no disposition guidance |
A related procurement blind spot is vendor sprawl during retirement work. If the telecom partner installs new equipment while a separate, loosely managed recycler handles old assets, chain-of-custody gets harder to defend. Teams evaluating providers alongside lifecycle vendors often review business-focused computer recycle companies at the same time so the transition doesn’t split into disconnected projects.
Presence beats proximity because outages are solved by network design and operational control, not by whoever leases office space closest to your building.
How to Vet Network Topology and Redundancy
Most telecom sales decks flatten complexity into a coverage map and an uptime promise. That’s not enough. You need to know how traffic enters the building, what happens when a segment fails, and whether the backup path is independent or just differently labeled.

Start with the physical layer
A surprising number of “redundant” designs share the same weak point. The provider may present two services, two invoices, and two circuit IDs. Then you find both paths enter through the same vault, same riser, or same exterior wall penetration.
That’s why I push teams to ask for plain-language path descriptions. If the seller can’t explain route diversity without hiding behind marketing terms, assume the resilience story isn’t mature.
Physical quality matters too. In structured cabling work aligned with TIA/EIA-568, fiber testing with OTDR aims for insertion loss under 0.3 dB/km, and improper bend radius can cause attenuation spikes of 15 to 20%, according to Nor Cal Communications. Those details matter because “carrier-grade” service still depends on disciplined installation at the edge, in risers, and inside your facility.
The questions that expose weak designs
Use these in technical review calls:
- Primary and backup entry. Do the circuits enter the property through separate paths?
- Last-mile ownership. Which segments do you own directly, and which are leased?
- Carrier hotel or building MPOE dependence. Is there a single shared handoff point that defeats the redundancy claim?
- Maintenance coordination. If the route owner and reseller are different, who drives the incident bridge?
- Failure domain clarity. What single event could interrupt both services?
Ask the provider to describe the route as if you’re standing outside the building and walking the cable in. That answer is usually more honest than the slide deck.
Match topology to the use case
Different architectures fit different operating models:
Dark fiber
Best when you need high control and have internal capability to manage optics and scale paths over time. It isn’t automatically better if your team lacks the staff to support it.
WDM services
Useful when you need high-capacity transport with fewer moving parts under your control. Good fit for data center interconnect where deterministic performance matters.
Carrier Ethernet
Often the practical middle ground for multi-site business environments. It can simplify operations, but you still need clarity on access loops and handoff design.
SD-WAN over mixed underlays
A smart choice when your sites have inconsistent access options and you need policy-based failover. It does not replace the need for sound physical diversity. It only makes better decisions on top of what you’ve bought.
Don’t separate resilience from recovery
Procurement teams often evaluate redundancy and disaster recovery as separate workstreams. That creates handoff problems later. If your failover design depends on network gear that’s being replaced during the project, include decommissioning and contingency handling in the same governance thread. This is especially important in sites with dense rack environments or staged cutovers. Teams reviewing outage planning often align telecom selection with data center disaster recovery considerations so route diversity and recovery operations don’t drift apart.
A quick red-flag table
| Claim from provider | What to verify |
|---|---|
| “Fully redundant service” | Separate building entry, separate conduit, separate upstream path |
| “Enterprise-grade fiber” | Testing standards, handoff documentation, install ownership |
| “Rapid failover” | Trigger conditions, routing behavior, support process during partial failure |
| “Managed end to end” | Which parts are leased, who controls field dispatch, who owns escalation |
Your SLA and Security Diligence Checklist
A contract can say “enterprise” and still leave you exposed. The weak points usually hide in definitions, exclusions, credit language, and security answers that sound polished but aren’t auditable.
Use a checklist. Not because procurement likes paperwork, but because sales teams are trained to move past details that affect accountability later.
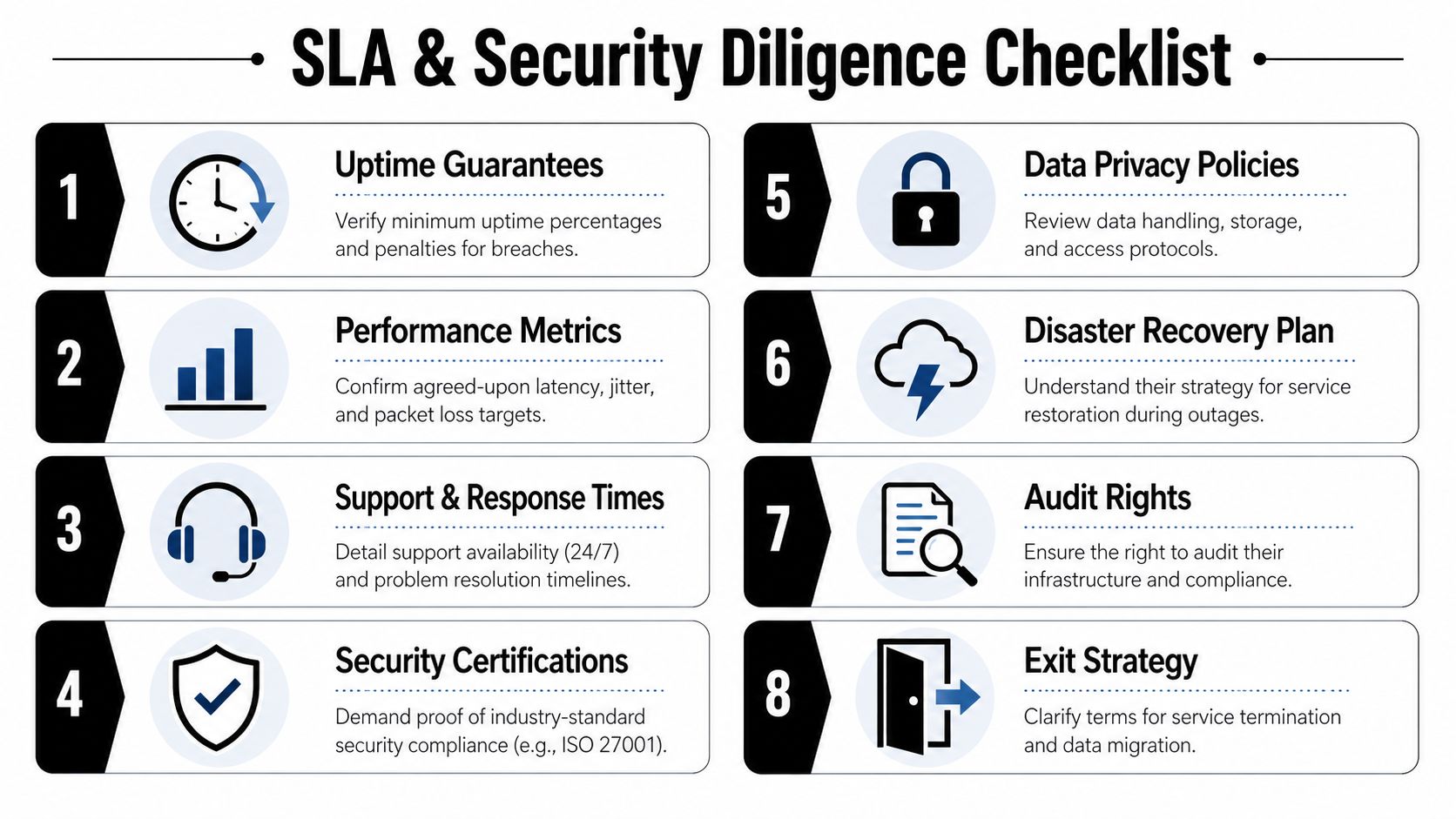
SLA review points that matter
Read the SLA with operations and security in the room. Legal alone won’t catch the practical traps.
- Uptime definitions. Check what counts as downtime, what’s excluded, and when the measurement window starts.
- Latency, jitter, and packet loss terms. A generic uptime promise doesn’t protect voice, video, or transactional applications.
- Repair timelines. Ask how severity is assigned and who can trigger escalation.
- Service credit mechanics. Credits rarely offset business damage. Their value is influence, not reimbursement.
- Chronic failure language. You want a path to terminate or remediate if service repeatedly underperforms.
A provider can miss your business need while still staying technically within a weak SLA. That’s why negotiated wording matters more than the logo on the MSA.
Security diligence questions to put in writing
Ask for direct responses. Avoid verbal assurances.
Governance and controls
Request their current security certifications, audit summaries if available, and a description of how access to network facilities is controlled. If they host or manage edge equipment, ask how admin access is granted, reviewed, and revoked.
DDoS and edge protection
If the service supports public-facing applications or critical remote access, ask whether mitigation is included, optional, or dependent on another service layer. Clarify who owns communication during an attack.
Data handling
Providers touching managed voice, logs, support artifacts, or hosted edge infrastructure should explain what they store, where they store it, and who can access it. If they can’t describe retention and access plainly, expect headaches during audit season.
Incident response
Ask who notifies you, how quickly they escalate, and whether your team gets direct access to incident coordinators during a live event.
What works: written operational commitments tied to named services.
What doesn’t: broad promises buried under exclusions and “commercially reasonable efforts” language.
Include exit and asset security in the diligence process
One of the most overlooked security questions is what happens when the relationship ends. If the vendor installed customer premises equipment, hosted edge devices, or managed telephony endpoints, your team needs a documented exit process for config removal, credential cleanup, and physical recovery.
That’s also where secure disposition enters the picture. Replaced telecom hardware can hold call metadata, network configs, VPN details, and management credentials. Procurement teams should tie carrier exit terms to internal secure data destruction services requirements so disposal is controlled, documented, and auditable.
Simple checklist for side-by-side review
| Area | What to confirm |
|---|---|
| SLA precision | Definitions, exclusions, performance metrics, chronic failure terms |
| Support model | Named escalation path, incident communication, after-hours coverage |
| Security posture | Certifications, facility controls, access governance |
| Operational transparency | Incident reporting, maintenance notices, change management |
| Exit discipline | Equipment return, config removal, credential handling, disposition records |
Navigating Contracts and Uncovering Hidden Costs
The monthly price is rarely the whole price. The contract turns a service quote into an operating reality, and that’s where finance teams get surprised.
A provider can look inexpensive on paper and still become the costliest option after implementation charges, handoff fees, support add-ons, construction dependencies, and renewal terms kick in.

The quote scenario procurement teams keep underestimating
Two providers quote a similar managed voice and network refresh. One looks cheaper because the monthly recurring charge is lower. Then the actual costs appear.
You learn the quote assumes existing building access that hasn’t been verified. Cross-connects inside the data center are billed separately. Move-add-change requests sit outside the managed scope. The backup path depends on shared switching capacity, and if those switches are oversubscribed, performance suffers long before the outage becomes obvious.
That’s why planning matters. In enterprise telecom systems, providers such as ATC Telecom report a 92% reduction in TCO over 5 years when moving from legacy systems, while also noting that oversubscribed switches can cause 25% packet loss, a hidden performance cost that may not be visible in the initial quote, according to ATC Telecom.
Terms that deserve line-by-line review
MRC and NRC
Separate recurring charges from non-recurring charges and insist that both are fully itemized. If install assumptions change after survey, you need a process for approval before costs move.
Auto-renewals
Check notice periods and renewal duration. Procurement teams miss these constantly, especially when telecom agreements live outside normal software renewal tracking.
Early termination language
Read the formula, not the heading. Some contracts make exits expensive enough to trap you in underperforming service.
Best-effort wording
If a feature or timeline matters to operations, don’t leave it under soft language. Put it in the order form, SOW, or SLA attachment where accountability is clearer.
Hidden cost checklist
- Construction dependencies. Ask what happens if new fiber build or entrance work is required.
- Inside-the-building charges. Clarify riser work, cross-connects, smart hands, and demarc extension costs.
- Support scope. Confirm whether managed service includes changes, testing, and after-hours coordination.
- Hardware handling. Determine who removes old equipment and who documents the transfer.
- Renewal and exit. Track notice deadlines and obligations tied to service cancellation.
Cheap telecom often becomes expensive in labor, delay, and rework. The invoice doesn’t always show the real cost. Your operations team will.
Integrating Your Telecom Upgrade with IT Asset Disposition
Every telecom upgrade is also an asset retirement project. Treating those as separate efforts creates avoidable security and compliance gaps.
When circuits move, voice platforms change, or network edge equipment gets refreshed, old hardware doesn’t become harmless. It often still holds saved credentials, routing details, VLAN data, firewall rules, phone system records, and management history. That material belongs in your risk register until it’s properly destroyed, sanitized, or documented for reuse.

Why this problem is growing
The disposal issue isn’t niche. It’s tied to the pace of connectivity growth and hardware turnover. Global internet usage is projected to reach 6 billion users by 2025, or 74% of the world’s population, with 1.3 billion new users coming online since 2020, according to the International Telecommunication Union. More connectivity means more edge equipment, more refresh cycles, and more retired electronics that need controlled disposition.
That growth pushes telecom procurement and ITAD closer together than many teams realize. If you buy new transport, UC, wireless, or access infrastructure without planning for the outgoing assets, you leave the project half-governed.
What to put into the project plan on day one
Build these requirements into the rollout packet, not as an afterthought:
- Asset inventory before cutover. Identify every device leaving service, including spares and branch edge gear.
- Chain-of-custody documentation. Record who removed each asset, when it moved, and where it went next.
- Data destruction standards. Align sanitization or destruction to internal security policy and recognized standards such as NIST 800-88 when applicable.
- Environmental handling. Require responsible recycling and documented downstream processing.
- Reuse decisions. Separate equipment that can be retained for lab, DR, or controlled redeployment from equipment that should be retired permanently.
Where projects usually go wrong
The failures are mundane. A field team swaps a firewall and leaves the old unit in a closet. A voice gateway gets stacked with miscellaneous surplus because nobody owns pickup. A branch router is shipped back without adequate logging. None of those sound dramatic until audit, breach review, or a location closure forces reconstruction of the chain.
Retired telecom hardware is still part of your security perimeter until you can prove otherwise.
For larger refreshes, especially in colocation rooms, MDF/IDF cleanouts, or multi-site carrier transitions, it helps to tie the network project directly to a documented data center decommissioning process. That keeps removal, transport, sanitization, and reporting under one accountable plan.
Sample RFP Questions and Decision Criteria
Most telecom RFPs ask too little about operations and almost nothing about retirement. That leads to polished answers and weak comparability. A good RFP forces providers to show how they deliver service, how they support it, and how they help you close the loop on replaced equipment.
Sample questions for providers
Network design and delivery
- Describe whether each requested site is on-net, near-net, or dependent on third-party last-mile access.
- Explain the primary and backup path into the facility in plain language.
- Identify any shared physical dependencies that could affect both primary and backup services.
- State who performs site survey, installation, testing, and final documentation.
Performance and support
- Provide the service metrics you will contractually stand behind for the requested service.
- Describe the escalation path for a major outage, including after-hours support.
- Explain how maintenance windows are communicated and how emergency maintenance is handled.
- Identify which issues require third-party coordination and who owns the customer communication.
Security and governance
- List current security certifications and summarize facility access controls for network locations relevant to service delivery.
- Describe how administrative access to managed equipment is controlled and reviewed.
- Explain your incident notification process for security events affecting customer services.
- State what logs, configs, or customer data you retain, and for how long.
Transition and end of life
- Describe your process for cutover, rollback, and failed implementation recovery.
- State whether customer premises equipment is included, leased, or optional.
- Explain how replaced telecom hardware is handled at project close, including custody transfer points.
- Confirm what documentation you provide for equipment removal, return, sanitization, or disposal coordination.
Telecom Provider RFP Decision Matrix
| Decision Criterion | Sample RFP Question(s) | Weighting (1-5) |
|---|---|---|
| Network presence | Are our sites on-net, near-net, or third-party dependent? | 5 |
| Route diversity | Are primary and backup paths physically independent into the building? | 5 |
| Last-mile control | Which service segments do you own and which are leased? | 5 |
| Implementation discipline | Who handles survey, install, testing, and as-built documentation? | 4 |
| SLA quality | What performance terms are contractual, and what exclusions apply? | 5 |
| Support operations | What is the escalation path for critical incidents and after-hours issues? | 4 |
| Security posture | What certifications, facility controls, and admin access controls are in place? | 5 |
| Contract flexibility | What are the renewal, exit, and change-order terms? | 4 |
| Total cost of ownership | What charges sit outside MRC, including install and support add-ons? | 5 |
| Hardware disposition | How are removed telecom assets tracked, transferred, and documented? | 5 |
How to score the answers
Don’t score based on presentation quality. Score on verifiability.
A concise answer with route detail, named responsibilities, and written commitments should beat a polished answer full of broad claims. If a provider can’t explain building entry, leased dependencies, support ownership, or asset handling without “we’ll confirm after signature,” lower the score. That uncertainty usually becomes your project burden later.
The best RFP process also includes one final check: can the provider operate cleanly inside your internal governance model? If your security, facilities, network, legal, and asset-disposition teams all need evidence, choose the vendor who can produce usable documentation, not just the one with the lowest headline rate.
If your telecom upgrade is creating a backlog of retired routers, switches, PBX systems, servers, or other network gear, Dallas Fortworth Computer Recycling can help you close the project properly. Their team supports nationwide B2B IT asset disposition, secure data destruction, electronics recycling, and data center decommissioning with the documentation procurement and infrastructure teams need for chain-of-custody, compliance, and responsible downstream handling.
