Secure Electronics Destruction Near Me: Vetted ITAD
The search usually starts the same way. An IT director looks at a locked closet, a cage in the data center, or a back room at a branch office and sees stacked laptops, dead switches, retired servers, and a banker’s box full of loose hard drives. None of it is in production. All of it still carries risk.
That pile isn’t just clutter. It’s retained data, chain-of-custody exposure, environmental liability, and an audit problem waiting for the wrong moment. A local search for electronics destruction near me feels like a quick fix, but for a business with regulated data, multiple locations, or decommissioning projects, “near me” is often the wrong frame. The critical question is whether the vendor can prove secure handling, documented destruction, and compliant downstream processing at scale.
The Hidden Risk in Your IT Storage Closet
An IT director signs off on a refresh project, but the retired gear does not leave the building that week. It ends up in a closet, a cage, or a branch back room because finance wants final asset counts, operations wants a pickup window that will not disrupt staff, and someone still hopes a portion of the equipment can be reused. That delay is where exposure builds.
The weakest point in electronics destruction is often the period before any destruction happens. Retired laptops, failed servers, network gear, backup media, and loose drives still sit under your control. If they contain data, they still belong in your risk register. If they contain batteries, boards, or regulated materials, they still belong in a documented disposition process.
The scale of the disposal problem is not small. The United Nations Global E-waste Monitor 2020 reported 53.6 million metric tons of e-waste generated worldwide in 2019, with only 17.4% formally collected and recycled. For enterprise teams, that matters because informal handling is still common. A vendor being local does not make the downstream process compliant.
Why Local Search Overlooks the Core Problem
Search results for electronics destruction near me usually optimize for convenience. They highlight drop-off service, consumer recycling, and quick pickups. That is useful for a household clearing out old devices. It does not answer the questions an IT, security, or procurement team has to answer before release.
A business project usually requires a provider that can control intake, separate reuse from destruction, document every custody transfer, and produce records your auditors will accept. If you are managing multiple offices, mergers, relocations, or data center cleanouts, the selection criteria shift fast. Local proximity becomes one factor among many, and often not the deciding one.
What matters in practice is whether the provider can handle:
- Business-grade intake that separates reusable assets from destruction candidates
- Documented chain of custody from pickup through final processing
- Data-bearing media controls for loose drives, backup devices, and embedded storage
- Audit-ready reporting that procurement, security, and compliance can all use
I have seen organizations treat a closet cleanout like a one-time junk haul, then discover halfway through the project that half the assets need serial capture, several devices contain embedded storage, and the certificate format does not meet internal policy. Teams planning a larger retirement project often start with a broader computer equipment disposal program because the actual scope usually extends well beyond destroying a few obsolete items.
The highest-risk assets are often the ones nobody logged properly. A failed SAN drive on a shelf, a loaner laptop in a drawer, or a lab device sent to storage without classification creates more exposure than the pallet everyone remembers.
What That Closet Usually Contains
A typical IT storage area holds several asset classes, each with different handling requirements.
- Remarketable equipment such as newer laptops or desktops that can be sanitized and reused
- End-of-life hardware that should go directly to physical destruction and compliant recycling
- Peripheral equipment with low resale value but possible embedded storage
- Specialized devices that may fall under stricter internal or regulatory controls
The mistake is treating all of it as scrap, or treating all of it as reusable. Good ITAD programs sort assets by data sensitivity, reuse value, chain-of-custody requirements, and reporting needs before a truck is ever scheduled. That is the difference between a local disposal transaction and a controlled disposition strategy that works across sites.
Decoding Destruction Methods What Secure Really Means
“Secure destruction” gets used loosely in this industry. That’s a problem, because the right method depends on the asset, the data classification, and whether the device has reuse value left.
Some media should be sanitized and remarketed. Some should be degaussed. Some should be shredded without debate. If a vendor can’t explain when each method applies, they’re selling a slogan, not a control.
Right below is a useful visual summary.
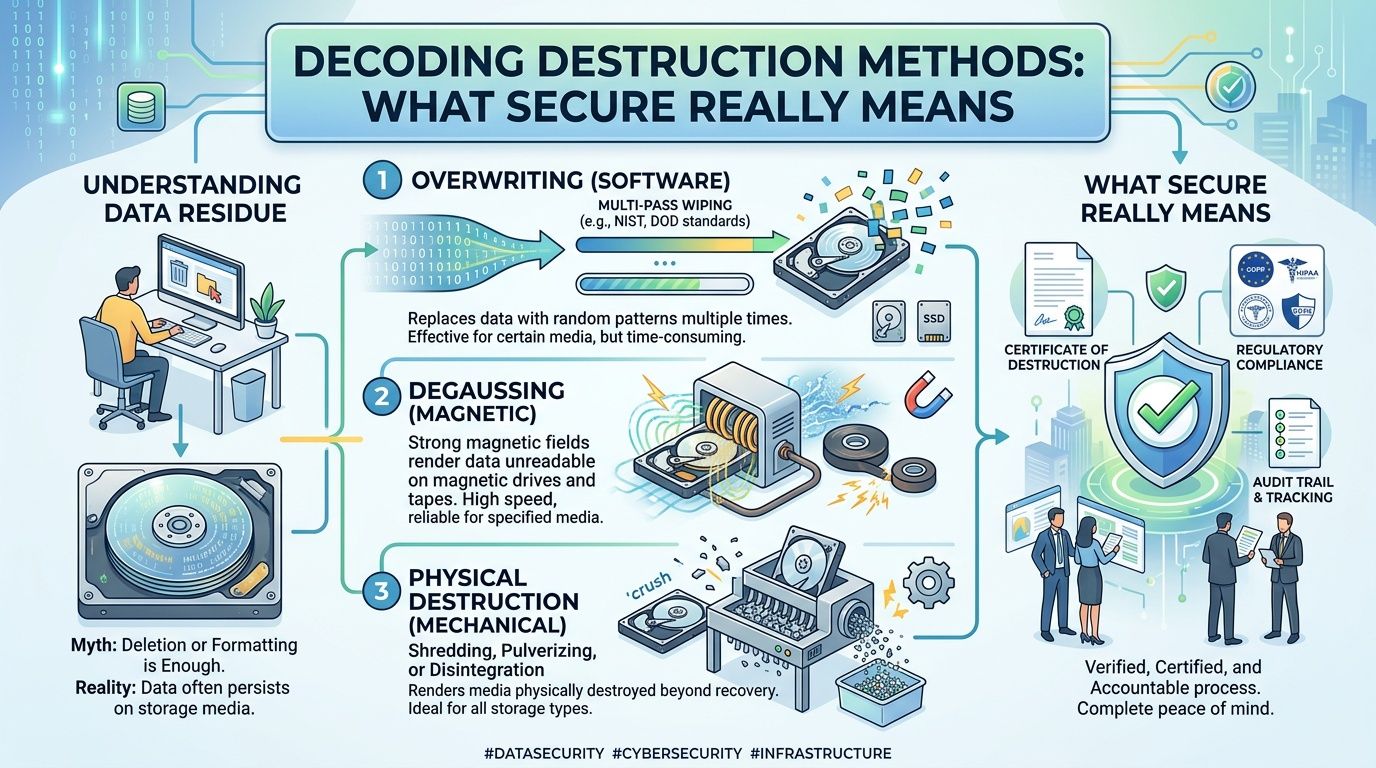
Data wiping for reusable assets
Data wiping works when the device still has operational value and the goal is secure reuse. The process overwrites stored data so the original information can’t be recovered through normal means.
This is the right fit for working laptops, desktops, and some storage devices that can be redeployed or remarketed. For an IT director, wiping is often the most financially sensible path when the hardware still holds value. But it only works if the process is controlled, validated, and documented.
What doesn’t work is informal wiping. A technician reimaging a machine or deleting partitions is not the same as a governed sanitization workflow. If the vendor can’t show how they verify the result, don’t count it as destruction.
Degaussing for magnetic media
Degaussing uses a strong magnetic field to disrupt the recorded data on magnetic storage media. It’s useful in environments that want to render certain drives unreadable without relying on software-based overwrite.
Its limitation is practical. After degaussing, the media is generally no longer reusable in any meaningful business sense, and the organization still needs documented handling for the physical device itself. In many programs, degaussing is paired with later physical destruction so there’s no ambiguity.
For many buyers, degaussing sounds more secure than it really is in procurement terms. It’s not a substitute for chain of custody, and it doesn’t remove the need for final disposition documentation.
Physical destruction for end-of-life media
Shredding is the clearest answer for drives that are damaged, obsolete, high-risk, or not worth recovering. In certified workflows, physical destruction eliminates the business question of whether the media should ever be reused.
According to this certified ITAD process overview, industrial shredding reduces hard drives to particle sizes typically under 2mm, per NIST guidance for high-security clearance, and can achieve up to 95% material recovery rates in R2v3 certified facilities. That combination matters. The same process that makes recovery virtually impossible also supports responsible downstream recycling.
Organizations looking for a dedicated certified hard drive destruction process should focus less on the marketing phrase and more on the evidence package: serialized intake, witnessed handling where needed, and clear destruction reporting.
Practical rule: If the asset has little reuse value and high data sensitivity, physical destruction is usually the simplest and strongest control.
What people do that feels secure but isn’t
A surprising amount of bad practice still comes from improvised methods. Drilling a hole through a drive, hitting it with a hammer, or removing a single platter may make the owner feel better. It doesn’t create a reliable, auditable destruction event.
Here’s why those methods fail procurement and compliance review:
- They aren’t standardized. Results depend on who performed the work.
- They aren’t easy to document. You can record that someone tried, but not that the process met a defined standard.
- They complicate recycling. Damaged partial components still need proper downstream handling.
- They don’t scale. What seems acceptable for one drive breaks down fast across sites and departments.
A mature ITAD program uses the method that matches the asset’s security need and residual value. Secure doesn’t mean dramatic. It means repeatable, documented, and defensible.
The Compliance Gauntlet: Understanding Regulations and Certifications
A disposal project can look clean on paper and still fail audit review six months later. The usual breakdown is not the shredder. It is weak documentation, unclear downstream handling, or a vendor whose certifications do not apply to the site and service you bought.
Compliance in electronics destruction is a stack of requirements that sit on top of each other. Environmental handling rules apply to the material. Privacy and records rules apply to the data. Procurement standards apply to the vendor. If your team is operating across multiple offices or business units, a simple "electronics destruction near me" search rarely gives enough confidence. Mid-size and enterprise organizations need a provider that can deliver the same controls, reporting, and chain-of-custody discipline across locations.
The visual below captures the basic decision path most organizations need to follow.
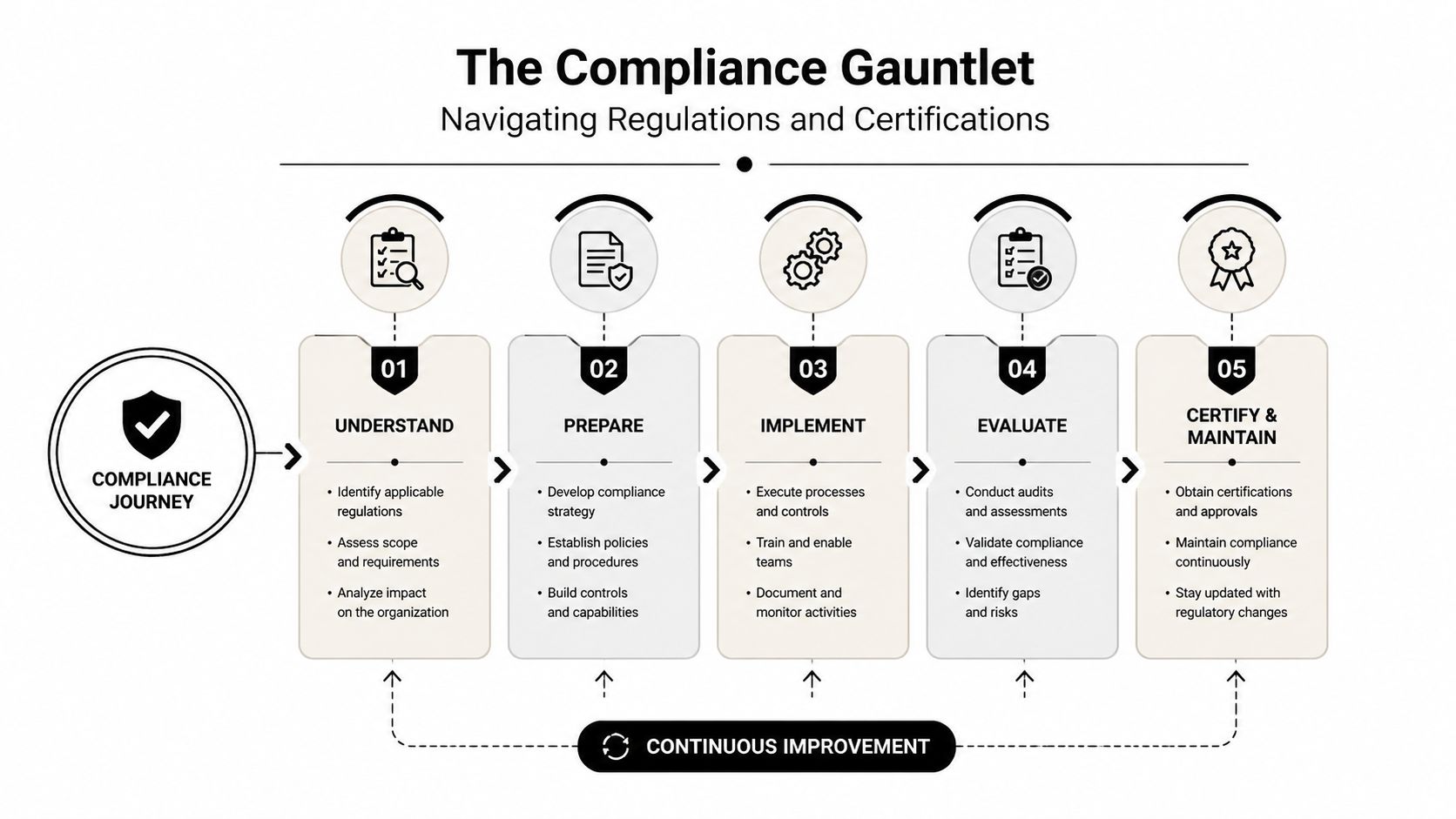
RCRA and environmental liability
The Resource Conservation and Recovery Act (RCRA) matters because retired electronics can contain components that require controlled handling and disposition. Once equipment leaves active service, your risk does not disappear. It shifts to how the material is stored, transported, processed, and documented.
For IT leaders, the practical question is simple. Can the vendor explain where material goes after pickup, who processes it, and what records they keep if a regulator, customer, or internal auditor asks later?
A Texas IT asset disposition provider with statewide service coverage or any national partner should be able to show downstream controls, material segregation practices, and records retention procedures. If the answer stops at "we recycle everything," the review is incomplete.
WEEE and global operating standards
Organizations with international operations often inherit WEEE-aligned expectations through customer contracts, internal environmental policy, or reporting requirements tied to foreign subsidiaries. Even for a U.S.-only destruction event, those standards shape how procurement teams write vendor requirements and how compliance teams assess recyclers.
This matters in practice. A vendor that understands global recovery standards usually has stronger documentation discipline, clearer downstream oversight, and fewer blind spots in mixed asset streams. That becomes important when one program needs to satisfy legal, ESG, and customer assurance requirements at the same time.
NIST 800-88 and defensible data sanitization
For data-bearing devices, NIST 800-88 is the standard security teams usually want referenced in the statement of work. It gives procurement and audit teams a common language for deciding whether media should be cleared, purged, or physically destroyed.
The true measure is not whether a salesperson says 'we follow NIST.' It lies in whether the vendor can map the method to the media type, explain when sanitization is acceptable versus when destruction is required, and produce evidence that the process was completed as designed.
I look for three things during vendor review:
- A written process that ties sanitization or destruction choices to device type and risk level
- Validation records that show the method worked, not just that equipment was handled
- Asset-level reporting that procurement, security, and audit can all use without rework
If a vendor claims NIST alignment but cannot produce a process map, audit trail, and destruction evidence, the claim is incomplete.
HIPAA, FACTA, and sector-specific exposure
Healthcare, financial services, laboratories, education, and government environments carry tighter handling obligations because retired devices can still contain regulated information. A workstation that no longer boots can still create legal exposure if it leaves your control without proper sanitization or destruction.
Local convenience often loses to program design. A nearby recycler may be able to collect equipment quickly. That does not mean they can support business associate requirements, regulated records handling, or enterprise reporting standards across multiple sites.
Ask whether the vendor can support:
- Certificates of destruction tied to serial numbers or other asset identifiers
- Chain-of-custody records from pickup through final processing
- Exception handling for untagged or unexpectedly data-bearing equipment
- Documented procedures for medical, laboratory, or specialized devices
Certifications that matter in vendor selection
Certifications are a filter, not a substitute for diligence. They help identify providers that have subjected their process to outside review, but only if the certification is current and applies to the service you are buying.
Focus on these categories:
- NAID AAA for secure destruction controls, employee screening, and documented handling practices
- R2v3 for electronics recycling controls, downstream accountability, and environmental management
- ISO-aligned management systems if your procurement team requires formal quality, security, or environmental governance
Then verify the scope. Ask for the certificate, the covered locations, the expiration date, and whether mobile or on-site services are included. That step matters more than the logo on the website.
On-Site Versus Off-Site Destruction A Risk-Based Decision
This choice gets framed emotionally more than it should. Some teams assume on-site destruction is automatically safer because they can watch it happen. Others assume off-site destruction is better because the plant has heavier equipment and a more controlled processing line. Both can be right. Both can also be wrong.
The correct decision comes down to asset sensitivity, operational constraints, witness requirements, and how much you trust the custody process between pickup and final destruction.
The side-by-side decision view
| Factor | On-Site Destruction | Off-Site Destruction |
|---|---|---|
| Security visibility | Your team can witness destruction at your location | Relies on sealed transport, intake controls, and documented custody |
| Chain of custody | Shorter physical journey, but still needs logging and supervision | Strong if the vendor uses serialized intake and controlled receiving |
| Operational disruption | Mobile trucks, access coordination, and staging can affect the site | Less disruption at your facility once assets are loaded and released |
| Best fit | High-sensitivity projects, strict internal witness rules, limited-release environments | Large refreshes, multi-site programs, data center decommissioning, mixed asset streams |
| Processing capability | Useful for immediate destruction needs | Usually better for broader sorting, remarketing, recycling, and material recovery |
| Verification | Visual witness plus post-event documentation | Audit trail, serialized records, and plant-issued destruction reporting |
When on-site makes sense
On-site destruction is strongest when the organization has a policy or customer expectation that media should not leave the premises intact. It also helps in environments where internal stakeholders want direct observation as part of sign-off.
That said, witness visibility shouldn’t replace process quality. A mobile shred event still needs asset reconciliation, operator controls, and final reporting. Watching a truck destroy drives is reassuring. It isn’t enough by itself.
If your policy requires witnessed destruction, a provider offering on-site shredding services may fit the requirement better than a standard plant-based pickup.
When off-site is the better operational decision
Off-site destruction often wins for scale. If you’re retiring mixed equipment across several offices, coordinating a data center move, or handling both reusable and scrap assets, a processing facility can manage sorting more efficiently.
It also supports better decision-making when not every asset should be shredded. Some equipment needs data destruction and resale evaluation. Some needs dismantling and compliant recycling. A good off-site workflow handles those branches cleanly.
Choose the model that gives your organization the strongest evidence trail with the least operational friction. The “best” method is the one your auditors and security team will both accept.
The mistake to avoid
Don’t buy on-site just because it feels more secure, and don’t buy off-site just because it looks cheaper. Match the service model to the risk classification of the project. That’s the procurement standard that holds up.
How to Qualify Your Electronics Destruction Partner
A strong vendor interview sounds less like facilities management and more like a security review. That’s how it should sound. You’re not hiring a hauler. You’re appointing an outside party to take custody of devices that may still contain regulated or confidential information.
The weakest proposals usually look polished. They promise secure recycling, free pickup, and easy scheduling, but they stay vague on who touches the assets, what gets recorded, and how the destruction is proven. That vagueness is the risk.
According to this review of local recycling gaps, many “free” local recycling services lack NAID certification and proper chain of custody, and improper asset disposal is linked to 18% of data breach incidents. That’s why vendor qualification needs to focus on evidence, not convenience.
The checklist below is a good starting point for procurement and IT working together.

Start with the custody model
If the vendor can’t explain custody clearly, stop there. Everything else depends on it.
Ask them to walk you through the asset path from pickup to final disposition. Not the marketing version. The operational version. Who arrives on site, how assets are packaged, when serials are captured, how exceptions are handled, and when your team receives final documents.
Look for answers that include:
- Locked transport procedures and controlled loading practices
- Serialized intake for devices and loose media where applicable
- Custody handoffs documented by role, date, and location
- Exception handling for missing tags, damaged drives, or unmanifested items
A provider with credible controls can describe the process without hesitation.
Build your RFP around proof, not promises
The RFP should force concrete answers. If you ask broad questions, you’ll get broad claims.
Use prompts like these:
- Describe your chain-of-custody workflow from pickup through destruction or resale.
- List the certifications currently held and identify which facilities and service lines they cover.
- Explain when you wipe, degauss, or shred media.
- Provide a sample certificate of destruction and sample serialized report.
- Describe downstream recycling controls and audit requirements for subcontractors.
- State whether destruction can be witnessed and how witness events are documented.
- Identify insurance coverages relevant to data handling and transport risk.
- Explain employee screening and access controls for staff handling client assets.
These questions separate actual ITAD operators from scrap-forward vendors quickly.
Read the certificate of destruction like an auditor
A weak certificate says little more than “items destroyed.” That’s not enough for regulated environments or internal audit.
A useful certificate should answer basic accountability questions:
- Which customer and site the material came from
- When custody changed hands
- What was destroyed, ideally tied to serial numbers or asset identifiers
- Which method was used
- When final processing occurred
- Who authorized or performed the destruction event
If the certificate is generic, ask what supporting report accompanies it. In a stronger program, the certificate is the summary document, not the only document.
Audit lens: If your security team had to reconstruct the history of one specific drive six months later, could the vendor’s records support that review?
Verify certifications and scope
Many buyers stop at “they’re certified.” Don’t. Certifications have scope, facility coverage, and renewal cycles.
A prudent review includes:
- Current status check against the certifying body or supplied documentation
- Facility match to ensure the actual processing location is covered
- Service match to confirm the certification applies to destruction, recycling, or both
- Subcontractor clarity if another company handles transport or downstream processing
This is also where an R2 certified electronics recycler differs from a general junk removal provider. Certification doesn’t guarantee perfection, but it does signal a more mature operating discipline.
Test how they handle edge cases
The safest vendor often reveals itself in the awkward scenarios.
Ask what happens if your team hands over an unlisted hard drive during pickup. Ask what they do with embedded storage in copiers, lab devices, or networking equipment. Ask how they handle assets that arrive damaged, unlabeled, or mixed with nonstandard items.
Good answers are specific. Weak answers become fuzzy right where the risk rises.
Procurement red flags that should slow the deal
These are the warning signs I’d treat seriously:
- “Free” as the main value proposition. Free isn’t impossible, but if the economics aren’t explained, the custody controls may be thin.
- No sample reporting. If they won’t show documents before award, expect disappointment later.
- Vague destruction language. “We destroy everything securely” isn’t an operating procedure.
- No downstream transparency. If they won’t name process steps, they may not control them.
- Consumer-oriented workflow. A drop-off model adapted for enterprises usually creates documentation gaps.
What strong partners consistently do
Reliable electronics destruction partners tend to share a few traits regardless of company size:
- They classify assets before processing instead of treating everything as scrap.
- They document every handoff that matters.
- They separate sanitization from destruction decisions based on policy and value.
- They issue records your auditor can use.
- They speak comfortably with IT, procurement, security, and compliance in the same meeting.
That’s the standard to hold in any search for electronics destruction near me. Geography helps with logistics. It doesn’t prove competence.
Beyond the Price Tag Cost Scheduling and Total Value
At 4:30 p.m. on a Friday, the low-bid vendor pushes your pickup to next week. The gear stays in a branch office conference room all weekend, including laptops waiting for disposition and a box of loose drives no one wants to own. The quote looked efficient. The operating model was not.
That is the problem with treating electronics destruction as a local hauling decision instead of a controlled ITAD service. For organizations managing multiple sites, cost only makes sense when it is tied to custody, scheduling reliability, reporting quality, and the ability to sort assets correctly before anything is destroyed or recycled.
Pricing models vary for good reasons. Some vendors charge by item, some by pallet, some by truck, and some build a project fee around labor, logistics, data-bearing media handling, and final reporting. The model matters less than the fit. A simple warehouse clear-out should not be priced like a serialized media destruction project. A nationwide refresh with site coordination, badged crews, and audit-ready documentation should not be priced like a residential drop-off service.
Cheap quotes usually cut somewhere. Common pressure points include:
- Reporting depth that leaves your team reconciling serial numbers by hand
- Poor asset segregation that sends reusable equipment into the shred stream
- Loose scheduling controls that create missed pickups, repeat site visits, and more staff coordination
- Exception handling gaps for damaged assets, loose media, or equipment that was never listed on the manifest
The better buying question is simple. What result is this vendor contract delivering?
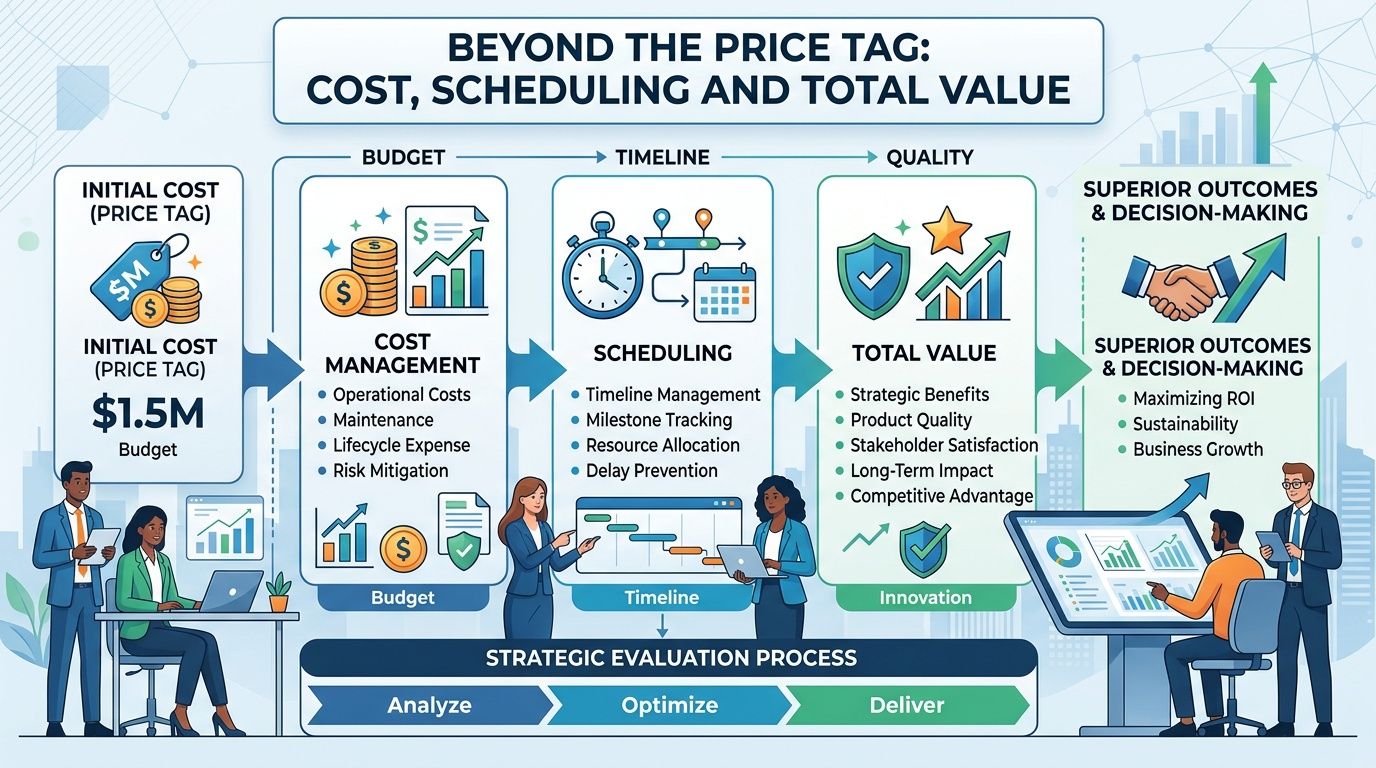
Cost should match the service model
If your scope includes witnessed destruction, serialized inventory, chain-of-custody documentation, after-hours pickup, or coordination across several offices, the price should reflect that work. If it does not, ask what was left out.
I look closely at scheduling language in statements of work because that is where hidden cost shows up. Site access rules, loading dock windows, freight elevator reservations, certificate turnaround times, and no-show policies all affect labor on both sides. A vendor that can serve ten states under one operating standard often creates more value than a nearby provider that handles each pickup like a custom event.
Total value includes resale, recycling yield, and avoided internal labor
Strong ITAD programs do not treat every retired device as scrap. They identify what can be sanitized and remarketed, what needs physical destruction, and what should move straight to commodity recycling. That triage improves financial recovery and keeps your destruction stream focused on assets that require it.
Industry guidance from the Sustainable Electronics Recycling International knowledge base supports this approach by emphasizing reuse before recycling when data security and device condition allow. In practice, recovery rates vary by asset age, configuration, and market demand. The larger point is operational. A vendor that can separate value-bearing assets from true end-of-life material can reduce net program cost without weakening controls.
A qualified ITAD partner does more than remove equipment. The partner reduces audit risk, shortens project timelines, and preserves recoverable value where policy allows.
Scheduling is part of the security model
Retired equipment sitting on-site creates exposure. It also creates noise for local teams who now have to store it, watch it, and answer for it.
For a single office, that may be an annoyance. For a distributed organization, it becomes a pattern of small failures that consume security, facilities, and IT time. Predictable pickup windows, defined escalation paths, and clear exception handling reduce that drag. That is why the best procurement decisions in this category are rarely driven by the nearest truck route alone. They are driven by who can execute the same controlled process across every location you need to clear.
Transforming Disposal into a Strategic Asset
Electronics destruction looks tactical until something goes wrong. Then it becomes a board-level issue, a legal issue, or an audit issue.
That’s why a search for electronics destruction near me shouldn’t end with the closest vendor or the cheapest truck route. For mid-size and enterprise organizations, the better path is a deliberate ITAD decision based on custody controls, destruction method, certifications, reporting quality, and the vendor’s ability to operate across sites without improvising.
The storage closet, branch office back room, or decommissioned rack row doesn’t need a quick cleanup. It needs a controlled release process. When you classify assets correctly, demand proof instead of promises, and choose a partner that can support both compliance and operational efficiency, disposal stops being an afterthought. It becomes part of your security program.
That shift changes procurement behavior in a useful way. The question stops being “Who can take this stuff?” and becomes “Who can help us retire technology without creating new risk?”
If you need a partner for secure, compliant nationwide IT asset disposition, Dallas Fortworth Computer Recycling works with IT teams, data centers, healthcare organizations, government agencies, and nonprofits that need documented chain of custody, certified data destruction, and reliable pickup coordination. They can also help you build a repeatable disposition workflow instead of treating each retirement event as a one-off project.
