Texas Port Recycling A Guide for E-Waste & ITAD
Your infrastructure team is retiring racks of servers, network gear, laptops, and storage. Procurement wants the floor space back. Security wants documented destruction. Legal wants to know whether anything is leaving the country. Operations wants it gone this quarter.
That’s when “texas port recycling” starts sounding simpler than it is.
In practice, Texas ports sit at the intersection of logistics, commodity recycling, export controls, environmental rules, and data security. If you’re handling enterprise electronics, that combination creates one hard truth: a company that is excellent at scrap metal processing is not automatically qualified to manage secure IT asset disposition. For IT leaders, mixing those categories can turn a routine decommissioning project into a compliance problem.
Understanding the Landscape of Texas Port Recycling
The phrase texas port recycling often gets used as if it describes one industry. It doesn’t.
At the port level, you’re dealing with multiple material streams moving through the same geographic corridor. Steel, copper, aluminum, vehicles, industrial equipment, and electronics may all pass through Houston-area and other Texas logistics networks. But the controls required for each stream are very different.

What general scrap operations actually do
Texas Port Recycling is a good example of why this distinction matters. It was formed in February 2006, operates four scrap metal facilities in Texas, and houses Houston’s largest automobile shredder, according to the company’s fast facts page. That same page states that it is a subsidiary of The David J. Joseph Company, founded in 1885, and part of Nucor since 2008. Its business focus is ferrous and nonferrous metal processing.
That matters because those capabilities are real, but they solve a different problem.
A high-volume scrap operator is built to receive metal-bearing material, inspect it for prohibited contaminants, process it efficiently, and move commodities into downstream industrial markets. That’s appropriate for structural steel, auto hulks, mixed metal scrap, and many industrial streams.
It is not, by itself, proof of secure handling for retired laptops, servers, SSDs, network appliances, medical devices, or storage media.
For enterprise teams managing a refresh, this difference becomes obvious the minute someone asks basic questions:
- Which assets were serialized at pickup
- Who had custody during transport
- How was each drive sanitized or destroyed
- What certificate ties destruction back to the original asset list
- What happens if a device contains regulated data
- Which items are eligible for reuse instead of commodity shredding
A commodity recycler may handle the metal value. A proper ITAD workflow handles the legal, security, and audit burden around the device.
Why ports increase both opportunity and risk
Texas ports are powerful logistics hubs. That helps when you need large-scale movement, coordinated pickups, and access to downstream recycling markets. It also increases exposure.
Once equipment enters a port-oriented flow, mistakes become harder to unwind. Misclassified material can move quickly. Incomplete paperwork can follow the load instead of stopping it. And if a vendor’s process is optimized for weight recovery instead of controlled disposition, your internal controls may effectively end at the loading dock.
Practical rule: If your project involves storage media, regulated records, or export-sensitive equipment, treat the port as a high-control zone, not just a shipping convenience.
That’s why mature organizations separate two decisions that often get bundled together:
- Who is qualified to process the material
- Who is qualified to handle the data and compliance risk
Those aren’t always the same vendor.
The right frame for IT leaders
If you’re retiring enterprise hardware, don’t ask only, “Can this company recycle it?” Ask, “Can this company defend every handoff, every serial number, and every data-bearing asset if we get audited?”
That’s the standard that matters.
For teams looking at enterprise-scale retirement projects across Texas, this broader operational lens is the useful one: enterprise IT equipment recycling in Texas. The port may be part of the logistics chain, but it should never define the compliance model.
Navigating Regulatory and Export Restrictions
Most IT leaders don’t need to become environmental lawyers. They do need to know where the obvious traps are.
The first trap is assuming e-waste is just “used equipment.” Sometimes it is. Sometimes it’s a regulated waste stream. Sometimes it’s a mixed load with components that trigger special handling before anything can move through a Texas port.
Start with the hazardous components
The practical way to manage this is to screen for components that create environmental or transport risk before the load leaves your site.
Texas Port Recycling’s published specifications offer a useful example of how serious conditional acceptance can be. The company requires transformers to be fully drained and accompanied by an analytical report confirming PCB concentrations below 2 ppm, according to its Houston port specifications. That requirement exists because PCBs are persistent pollutants and create major liability when they enter the wrong disposal path.
For IT teams, the lesson is broader than transformers.
Electronics disposition often involves embedded parts that people overlook during decommissioning:
- Power distribution gear with capacitors or oil-filled components
- Legacy lab or medical equipment with regulated materials
- Battery-backed systems that need separate handling
- Compressed gas components from specialty equipment
- Mixed loads where scrap metal, electronics, and accessories are packed together without screening
If your outbound lot contains any of those, a recycler’s intake standards become a risk control, not a paperwork annoyance.
The vendors worth keeping are usually the ones that reject unclear material. A permissive intake process may feel easier on pickup day, but it often means your risk screening never happened.
Port movement adds export questions
Once equipment is routed toward a port, you also have to think about transboundary movement. Even when your organization is not intentionally exporting waste, downstream vendors may sell, broker, consolidate, or remarket material into international channels.
That means your review should cover more than the pickup vendor. It should cover downstream handling.
Ask these questions early:
- Is the equipment being sold for reuse, dismantled for parts, or processed as scrap
- Who decides that classification
- What documentation supports that decision
- Which downstream entities may receive the material
- What happens when a shipment contains nonconforming items
If a vendor can’t answer those plainly, the problem isn’t just transparency. It’s control.
What acceptance criteria tell you
A published prohibited-items sheet or conditional acceptance policy can reveal how disciplined an operation is. It shows whether the facility is built around controlled inbound screening or around speed.
That distinction matters in Texas port recycling because ports reward throughput. Throughput is valuable. It is also where bad loads get normalized if nobody wants to stop the trailer.
From an IT risk perspective, useful controls include:
- Pre-shipment review: Assets are categorized before pickup, not after arrival.
- Exception handling: Devices with unknown contents are quarantined instead of blended into a load.
- Documented rejection rules: The vendor can explain what it won’t take and why.
- Site-specific guidance: Different material categories have different receiving paths.
If your current process doesn’t enforce those checks, revisit it before your next move through Texas electronics recycling operations. The cleanup cost from one bad outbound load can outweigh the convenience of a fast pickup.
The operational mindset that works
The best internal teams treat decommissioning like controlled release management.
They don’t send a mixed pallet of equipment to a recycler and hope intake figures it out. They build a manifest, identify exceptions, isolate devices with special handling needs, and make the vendor confirm acceptance before transportation is scheduled.
That approach slows the front end a little. It prevents much larger problems later.
Scrap Recyclers vs Certified ITAD Partners The Critical Difference
This is the confusion point that causes most of the damage.
A general scrap recycler and a certified ITAD partner may both take possession of old technology. They are not performing the same service. The overlap is physical material. The difference is everything else.
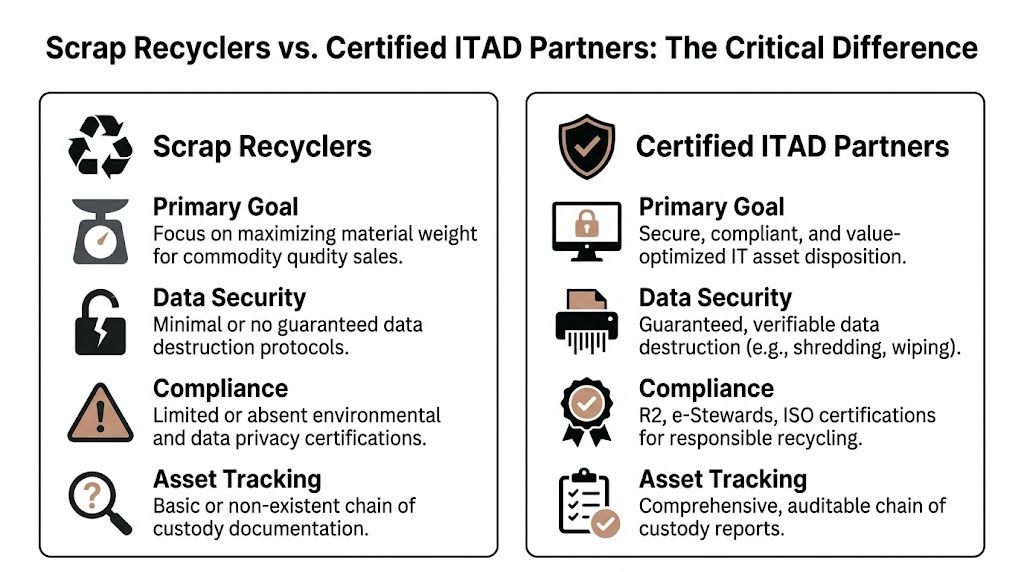
Where the models diverge
A scrap recycler is generally organized around commodity recovery. Material comes in, prohibited contaminants are screened out, metals are separated and processed, and value is tied largely to commodity output.
A certified ITAD partner is organized around asset-level control. Material still gets recycled when necessary, but the workflow starts with device identity, data risk, reuse potential, documentation, and downstream accountability.
That difference becomes critical the moment a retired asset still contains one of the following:
- Employee data
- Customer records
- Protected health information
- Financial information
- Configuration files
- Encryption keys
- Access credentials
- Internal intellectual property
A metal shredder solves none of those issues unless the process around it is controlled, documented, and defensible.
The public information gap is the warning sign
Texas Port Recycling’s published materials illustrate the divide well. Publicly available information does not detail specific e-waste acceptance protocols, data destruction certifications, or auditable chain-of-custody processes for electronics, based on the company’s prohibited and conditional materials sheet. For regulated industries, that gap is a major concern.
That doesn’t mean the company is doing something improper in its core scrap business. It means you should not infer ITAD controls that are not publicly demonstrated or contractually defined.
If a vendor’s literature talks in detail about metal grades, shredders, balers, shears, and inbound scrap conditions, but says little about serialized tracking, certificates of destruction, or data-bearing devices, believe the business model it’s showing you.
Side-by-side comparison
| Feature | General Scrap Recycler | Certified ITAD Partner |
|---|---|---|
| Primary objective | Maximize commodity recovery from material streams | Secure, compliant, documented disposition of IT assets |
| Unit of control | Load, pallet, or material category | Individual serialized asset |
| Data destruction | Often not publicly defined for enterprise devices | Documented wiping or physical destruction procedures |
| Chain of custody | May be limited to receiving and scale records | End-to-end auditable custody from pickup through final disposition |
| Reuse focus | Usually secondary to material processing | Typically central to value recovery and circularity strategy |
| Regulated-industry fit | Risky unless controls are specifically proven | Appropriate when certifications and documentation are in place |
| Vendor evaluation standard | Material acceptance and pricing | Security, compliance, reporting, downstream accountability |
The easiest way to avoid category error is to use a stricter benchmark for electronics vendors, such as an R2 certified electronics recycler. Certification doesn’t remove the need for due diligence, but it gives you a more relevant starting point than a generic scrap profile.
What works and what fails
What works is separating assets by risk and routing them accordingly.
For example, bare racks, empty metal enclosures, and clearly non-data-bearing ferrous scrap may belong in one channel. Laptops, servers, phones, drives, switches, and multifunction devices belong in another. Mixed handling saves time only on paper.
What fails is the common shortcut: one trailer, one vendor, one weight ticket, one invoice.
That approach might clear a warehouse. It won’t satisfy an auditor asking which exact storage arrays were destroyed, how the data was handled, and where the residual materials ultimately went.
Ensuring End-to-End Data Security and Chain of Custody
The words secure recycling get used too loosely. Security isn’t a marketing adjective. It’s a sequence of controls that survives scrutiny after the assets are gone.
If you can’t reconstruct who touched a device, where it moved, how it was sanitized, and when final disposition occurred, you don’t have a defensible process. You have trust-based disposal.

What a defensible process looks like
Strong ITAD security starts before pickup.
Your internal team should identify which assets are data-bearing, which are peripheral, and which require physical destruction rather than software sanitization. That classification should be documented in the asset manifest, not improvised on the dock.
Then the vendor process should show clear controls:
- Serialized inventory capture before or at pickup
- Sealed transport procedures with named custody handoffs
- Restricted facility access for inbound electronics
- Defined destruction methods matched to media type
- Exception documentation for missing, damaged, or unmatched assets
- Final reporting tied back to the original list
A recycler that says “we destroy everything securely” but can’t produce asset-level records is asking you to accept operational blind spots you may not be able to defend later.
Data destruction has to match the media
Not every device should be handled the same way.
Software wiping may be appropriate for some reusable drives and endpoints when the process is verified and documented. Physical shredding may be the only acceptable option for failed drives, damaged media, or highly sensitive assets. Some organizations also require on-site destruction for selected classes of equipment.
The control question isn’t which method sounds toughest. It’s whether the method chosen is appropriate, documented, and consistently applied.
Audit mindset: If counsel asks six months later how a specific drive from a specific server was destroyed, your vendor should be able to answer without rebuilding the entire job from email threads.
Chain of custody is more than a receipt
A bill of lading or receiving receipt is not the same thing as true chain of custody.
Real chain of custody documents movement by asset or by tightly controlled lot from the point of release through processing. It records who released the equipment, who transported it, who received it, where it was held, and what final action occurred.
That’s especially important when assets move through complex logistics environments or port-adjacent operations, where consolidation can blur boundaries between lots unless the process is designed to prevent it.
A useful review framework includes:
Pickup controls
Look for badging, vehicle identification, sealed containers where appropriate, and a signed transfer from your authorized staff. Informal handoffs create avoidable ambiguity.
Facility controls
Ask how inbound assets are segregated, where media is stored before destruction, and how unauthorized access is prevented. The answer should describe a process, not a promise.
Reporting controls
The output should include more than a generic certificate. You want documentation that maps the result back to the original asset population. For many teams, security data destruction workflows are easier to evaluate when the vendor can show sample documentation in advance.
The practical standard is simple. If a device disappears between your dock and final processing, the chain of custody should show where the failure happened. If it can’t, the chain was never strong enough.
How to Select a Compliant E-Waste Recycling Partner
Vendor selection usually breaks down when teams overvalue pickup speed and undervalue downstream accountability.
The partner you want is not the one who says yes to every item in the first call. The partner you want is the one whose controls still make sense after legal, security, sustainability, and procurement all review the program.

Certifications are a floor, not the whole answer
For electronics, recognized certifications matter because they force discipline around environmental practices, downstream controls, and process consistency. They aren’t a substitute for vendor review, but they’re better screening tools than generic claims about being green or secure.
If a vendor cannot clearly explain its certifications, audit scope, and downstream management approach, move on.
A reliable evaluation should cover:
- Scope clarity: Does the certification apply to the facility and services you will use?
- Downstream accountability: Can the vendor explain where materials go after primary processing?
- Data handling alignment: Do the destruction and reporting processes fit your internal requirements?
- Industry fit: Can the vendor support healthcare, government, finance, education, or other regulated environments if that applies to you?
Many organizations realize they need an electronics-focused facility review, not just a recycling quote from an electronic recycling center.
Ask for sustainability data that means something
Broad recycling programs can show real value at the state level. Keep Texas Recycling reports $12.3 million in revenue and 550,000 cubic yards of landfill space saved over its program history on the Keep Texas Recycling page. Those figures are useful context for Texas recycling as a whole.
They do not tell you what your vendor achieved with enterprise electronics.
That’s the gap ESG-focused organizations should pay attention to. If your board, customers, or procurement policy expects environmental reporting, ask for vendor-specific output, not broad industry language.
Useful questions include:
What percentage of equipment is reused versus shredded
A partner committed to circularity should be able to explain how it prioritizes reuse, refurbishment, harvesting, and material recovery. If everything goes straight to destruction, you may be leaving both value and sustainability gains on the table.
What reporting can be tied to our program
You’re looking for reports that reflect your own outbound assets and outcomes, not generalized environmental messaging. The stronger vendors can show how your organization’s disposition translated into documented recycling and reuse outcomes.
How are downstream vendors managed
If material leaves the primary facility, you need to know how those downstream relationships are qualified and monitored. That’s where strong environmental claims often fall apart.
Good sustainability reporting is specific enough to survive procurement review. If the numbers can’t be tied back to your own shipments and outcomes, they’re branding, not reporting.
The selection habits that save trouble
The best buyers do a site review, ask for sample documentation, and pressure-test exception handling before the first pickup.
The risky buyers compare only price per pound, truck availability, and generic assurances.
When texas port recycling enters the conversation, keep the standard high. Ports amplify scale. They also amplify the cost of weak vendor controls.
Your Action Plan for Secure IT Asset Disposition
If your current process still treats retired electronics like surplus scrap, fix that before the next refresh cycle.
The most effective changes are usually operational, not theoretical. You don’t need a massive policy rewrite to improve control. You need a cleaner decision path.
Start with an internal audit
Review what your organization is sending out.
Separate data-bearing assets from non-data-bearing equipment. Identify any legacy devices, specialty equipment, batteries, embedded components, and mixed pallets that create intake ambiguity. If your internal inventory is weak, strengthen that first.
Classify by risk, not convenience
Don’t build disposition lots around what’s easiest to load.
Build them around what must be controlled differently. Servers, laptops, network gear, storage media, medical systems, and industrial electronics often require distinct handling. A mixed trailer may reduce scheduling friction, but it increases the chance of custody and documentation failure.
Review your vendor file like an auditor would
Pull the current contract, statements of work, certificates, and sample reports.
Then ask direct questions:
- Can the vendor document asset-level chain of custody
- Are data destruction methods defined
- Do reports map back to your inventory
- Are downstream processors identified and governed
- Can the vendor explain exception handling without improvising
If the answers are vague, your exposure is larger than the relationship suggests.
Standardize your pre-shipment controls
A workable release checklist should include internal approval, serialized inventory where appropriate, lot segregation, packaging standards, and explicit identification of exceptions.
It should also define who in your organization is authorized to release equipment. Too many chain-of-custody failures start with an informal pickup arranged by facilities or a local manager who was just trying to clear space.
Treat every outbound load as if you may need to explain it later to security, legal, procurement, and an external auditor at the same time.
Vet your next partner before the project starts
Don’t wait until the loading dock is full.
Schedule a process review before the next major decommissioning. Ask to see example manifests, certificates of destruction, and downstream reporting. Make the vendor explain how it handles reusable assets, damaged drives, unmatched serials, and prohibited material found after pickup.
That conversation tells you more than a polished proposal ever will.
Secure IT asset disposition through Texas logistics and port networks can be done well. But it only works when the partner is selected for data security, chain of custody, and environmental accountability, not just recycling capacity.
Dallas Fortworth Computer Recycling helps organizations manage secure, compliant IT asset disposition with documented data destruction, electronics recycling, and nationwide logistics support. If your team needs a partner that treats retired technology as a security and compliance workflow, not just a commodity stream, visit Dallas Fortworth Computer Recycling to review services and start a conversation.
