Corporate e waste solutions: A Complete Guide
Every business eventually ends up with a pile of retired servers, old laptops, and outdated phones. It's a constant stream—a kind of 'digital tsunami' of e-waste. But this isn't just about making space in a storage closet; it's a serious corporate risk that needs a real strategy. Having professional corporate e waste solutions in place isn't optional anymore. It's a core part of modern risk management, data security, and operational health.
Confronting the Digital Tsunami of E-Waste
Think of your company's old electronics less like junk and more like dormant liabilities. Every discarded server, laptop, and smartphone is a container potentially holding sensitive corporate data, customer information, or trade secrets. Just stacking them in a back room or handing them off to a standard recycler leaves your organization wide open to risk.
This isn't some far-off problem. It’s a massive global issue that's getting bigger every year. In 2022, the world generated a staggering 62 million tonnes of e-waste, which is an 82% increase from 2010. That number is projected to hit 82 million tonnes by 2030, with e-waste growing five times faster than our documented recycling efforts can keep up.
Beyond Disposal: A Matter of Risk Management
Today’s business environment demands a shift in thinking. Managing e-waste isn't just an environmental nice-to-have or a task for the facilities team. It's a critical function of IT security and corporate compliance. The consequences of getting it wrong are severe and can ripple through every part of the business.
These risks generally fall into three big categories:
- Catastrophic Data Breaches: A single hard drive that isn't properly wiped can leak data, costing millions in remediation, customer notifications, and credit monitoring services.
- Hefty Compliance Fines: Regulations like HIPAA, GDPR, and FACTA have strict rules for data protection. Failing to follow proper disposal requirements can lead to crippling financial penalties.
- Lasting Brand Damage: A public data breach or an environmental scandal tied to improper e-waste disposal can destroy customer trust and do long-term damage to your company's reputation.
An effective corporate e-waste solution is, at its heart, a security protocol. It ensures the chain of custody for every retired asset is secure, audited, and compliant from the moment it leaves your building until its final destruction or recycling.
The Urgency for a Formal Strategy
Without a formal plan, companies often fall into dangerous habits, like stockpiling old equipment in a closet indefinitely or using the cheapest, unvetted disposal service they can find. These shortcuts create vulnerabilities that often go unnoticed until it's far too late. You can learn more by reading about the broader environmental impact of electronic waste.
This is precisely why a structured e-waste program is so essential. It gives you a clear, defensible process for handling retired technology, protecting your data, and meeting your legal and ethical obligations. It’s all about creating a secure final chapter for every piece of technology that powers your business.
The Anatomy of a Secure E-Waste Solution
A real corporate e-waste solution isn’t just a pickup service—it's a tightly controlled, fully auditable process built to shield your company from risk. Think of it as a secure "reverse supply chain" for your old tech. From the moment a device leaves your office to its final recycling or resale, every single step has to be tracked, documented, and secured. This creates an unbroken chain of custody.
Why is this so critical? Because the second an asset is retired, it stops being a tool and becomes a potential liability. Without a structured process, you’re wide open to data breaches, compliance violations, and steep environmental fines.
Each retired device sits at the intersection of data security, regulations, and your brand's reputation.
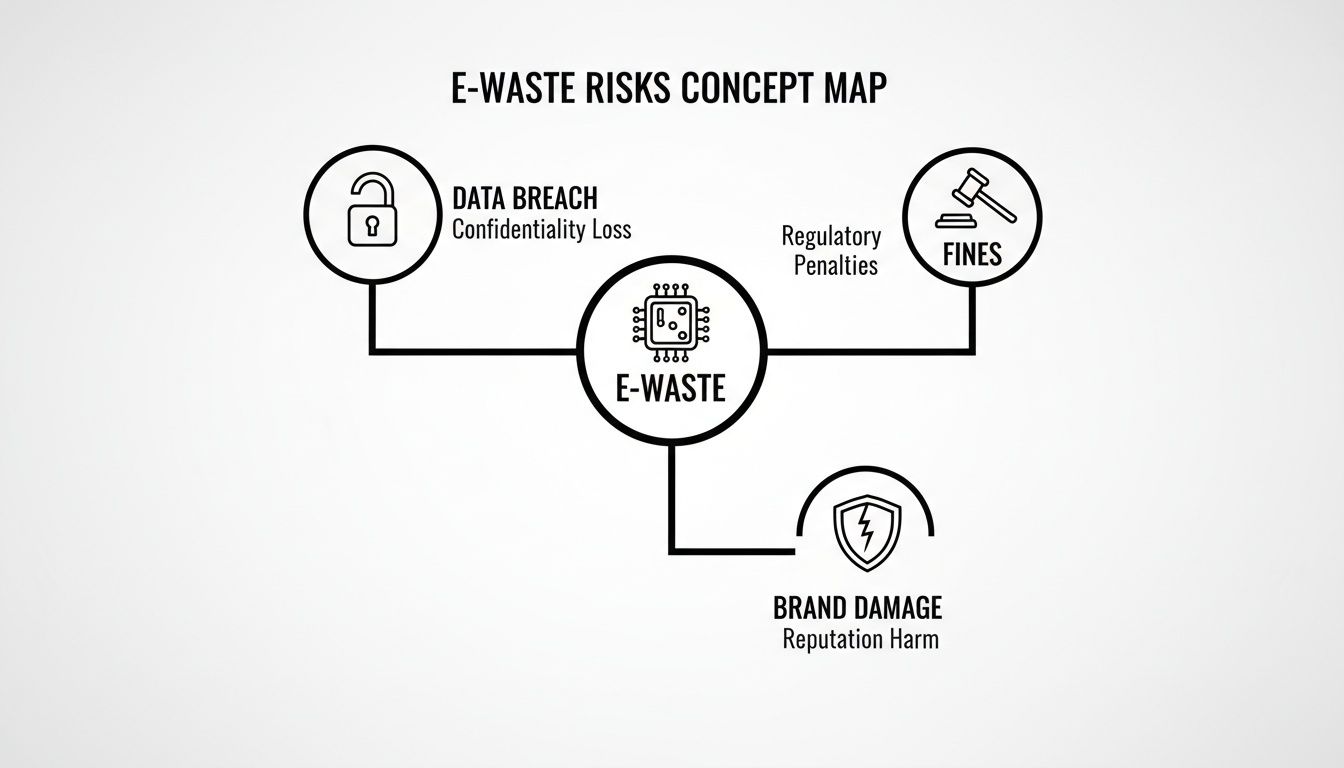
As you can see, mishandling old equipment can trigger a cascade of problems. A professional, secure process is simply non-negotiable.
Core Components of a Secure Program
A solid e-waste program is built on several key services that work together. Each one tackles a specific risk, ensuring your assets are managed the right way from beginning to end.
These core services always include:
- Secure On-Site Logistics: This is where it all starts. Trained, background-checked technicians arrive in sealed, GPS-tracked vehicles to collect assets directly from your facility. This secures the chain of custody from the very first step.
- Certified Data Destruction: This is arguably the most important piece. It guarantees that all sensitive data is permanently destroyed using methods that comply with standards like NIST 800-88. To learn more, see our guide on the importance of secure data destruction services.
- Responsible Recycling and Materials Recovery: For equipment that can’t be reused, this process makes sure hazardous materials are handled safely. It also recovers valuable commodities like gold and copper, returning them to the manufacturing supply chain and minimizing environmental harm.
- IT Asset Remarketing (ITAD): Some retired equipment still has market value. A professional IT Asset Disposition (ITAD) partner can test, refurbish, and resell these assets, generating a financial return that helps offset the program's costs.
The need for these services is growing fast. The global e-waste market is projected to hit $48.41 billion in 2024 and climb to $66.33 billion by 2029. This growth is fueled by staggering volumes, expected to exceed 65.3 million tonnes in 2025.
Even so, a shocking 347 million metric tonnes of unrecycled e-waste is expected to have piled up worldwide by 2025 because proper collection can't keep up. This gap underscores the urgent need for professional corporate solutions.
To get a sense of what a comprehensive service looks like, here’s a quick breakdown of the different components.
E-Waste Service Models At a Glance
The table below outlines the primary services you'll find in a corporate e-waste solution, explaining what each one does and why it matters to your business.
| Service Component | Primary Function | Key Business Benefit |
|---|---|---|
| On-Site Logistics | Secure collection and transportation of retired assets from your facility. | Establishes a documented chain of custody from the very beginning. |
| Data Destruction | Irreversible sanitization of data from hard drives and storage media. | Protects against data breaches and ensures regulatory compliance. |
| Asset Remarketing (ITAD) | Refurbishing and reselling equipment that still holds functional value. | Recovers financial value from retired assets, reducing total cost. |
| Responsible Recycling | Safe dismantling and recovery of raw materials from end-of-life electronics. | Prevents environmental liability and supports sustainability goals. |
Each of these components plays a distinct role in creating a defensible, responsible, and often financially beneficial asset retirement program.
What Do Those Certifications Actually Mean for You?
Certifications aren't just fancy acronyms for a vendor's website; they are your proof that a partner follows the highest industry standards. They provide an essential layer of third-party validation, protecting your company from liability long after your equipment is gone.
A vendor's certifications are a direct reflection of their operational maturity and commitment to risk mitigation. They are the easiest way to differentiate between a simple scrapper and a true security partner.
Here are the critical certifications you should look for and what they guarantee for your business:
| Certification | What It Guarantees | Your Business Benefit |
|---|---|---|
| R2v3 | Responsible recycling, robust data security, and worker safety protocols. | Protects you from environmental liability and ensures ethical processing. |
| e-Stewards | The strictest standard prohibiting the export of hazardous e-waste. | Guarantees your old tech won't cause a brand-damaging scandal overseas. |
| NAID AAA | The gold standard for secure data destruction, covering processes and facility security. | Provides verifiable proof of data sanitization, crucial for HIPAA or GDPR compliance. |
When you choose a vendor holding these certifications, you’re not just hiring a recycler. You’re bringing on a verified compliance and security expert to manage the final stage of your IT asset lifecycle.
Choosing the Right E-Waste Partner for Your Business

Picking a vendor for your corporate e-waste is easily the most important decision you'll make in this entire process. You need to think of it less like hiring a disposal service and more like bringing on a security contractor.
A great partner becomes an extension of your own IT and compliance teams, protecting your data and your reputation. The wrong one, however, can expose your business to devastating data breaches, regulatory fines, and brand damage.
This isn't a choice you should ever make based on price alone. The cheapest quote often means corners are being cut where you can't see them—like with data security or their environmental practices. To make a smart decision, you have to get past the sales pitch and start asking the tough questions. It's about digging into their processes, verifying their certifications, and making sure they can deliver true end-to-end security.
Non-Negotiable Vendor Criteria
As you start vetting potential partners, there are a few foundational requirements that are simply non-negotiable. These are the things that separate the professional, risk-focused providers from the basic recyclers.
Your evaluation checklist must include:
- Verifiable Certifications: Your vendor absolutely must hold current R2v3 and NAID AAA certifications. R2v3 guarantees responsible recycling practices, while NAID AAA is the gold standard for secure data destruction, covering everything from employee background checks to facility security.
- Secure Chain of Custody: Ask them to walk you through their entire process. This should start with an on-site pickup using GPS-tracked vehicles and uniformed staff and end with secure processing at their facility. Every single touchpoint needs to be documented.
- Transparent Downstream Auditing: A reputable partner can prove exactly where your materials go after they leave their facility. They should provide clear documentation showing that all hazardous materials are sent only to certified downstream partners for final disposition.
If a vendor gets cagey about providing proof for any of these items, consider it a major red flag. True security partners are proud of their processes and are more than happy to show you how they keep you compliant.
Critical Questions to Ask Potential Partners
Once you have a shortlist of certified vendors, it’s time to dig deeper. Their answers to these questions will reveal their operational maturity and their real commitment to protecting your business. Think of this as an interview for a critical role on your security team.
Here are a few essential questions to guide your conversations:
- How do you document and prove data destruction?
- You’re looking for serialized reporting. The report must link the specific serial number of each device to a certificate of data destruction. A generic, bulk certificate is simply not good enough.
- Can you describe your process for asset tracking and reporting?
- They should offer a client portal or detailed reports that give you real-time visibility into the status of your assets, from pickup all the way to final disposition.
- What is your policy on employee background checks and security training?
- Anyone who handles your sensitive equipment must undergo rigorous background checks and receive ongoing security training. No exceptions.
- How do you handle assets with potential resale value?
- A good IT Asset Disposition (ITAD) partner will have a clear, transparent process for testing, grading, and remarketing assets, along with a defined revenue-sharing model.
- Can we tour your facility?
- A flat-out refusal to allow a site visit is a huge warning sign. A professional vendor will be eager to show off their secure, well-managed facility.
The quality of a vendor's reporting is a direct indicator of the quality of their service. Vague, non-serialized reports often hide a disorganized and insecure process. Demand detail and accountability.
By asking these tough questions, you move beyond marketing claims and get to the heart of what really matters: verifiable security and compliance. Taking the time to thoroughly vet potential partners is the single best investment you can make in your e-waste program. For a deeper dive into this topic, you can explore our guide on how to evaluate IT asset disposition companies. Making an informed choice here protects your organization from unnecessary risk down the road.
Implementing Your Corporate E-Waste Program

A real corporate e-waste program is much more than just calling for a pickup. It’s about building secure, compliant disposal practices right into the DNA of your company’s operations. This takes a clear blueprint, buy-in from the right people, and a solid way to measure success.
Without that structure, even the best intentions can lead to sloppy practices and gaping security holes. The mission is to create a repeatable, auditable process that every employee gets, turning asset retirement from a random chore into a core business function. This is the bedrock of any strong corporate e-waste solution.
Building Your Internal Foundation
Before you can even think about rolling out a program, you need to get the key departments on board. E-waste is not just an IT problem—it’s a legal, finance, and operations issue, too. Each of these teams has skin in the game and needs a seat at the table from day one.
- IT Department: They're on the front lines, managing the asset lifecycle, flagging equipment for retirement, and making sure data is handled securely before it ever leaves your building.
- Legal & Compliance: This team’s job is to ensure the program follows all data privacy laws like HIPAA or GDPR and shields the company from the legal fallout of a disposal mistake.
- Finance Department: Finance is tracking asset depreciation, managing the budget for disposition, and accounting for any money made from selling refurbished equipment.
Getting this alignment from the start means your program is built on solid ground with shared ownership and clear communication. It keeps the whole process from getting dumped on IT and makes it a true company-wide effort.
Developing a Clear Asset Retirement Policy
With your internal team aligned, the next move is creating a formal Asset Retirement Policy. Think of this document as the official rulebook for your program. It needs to be simple, clear, and easy for everyone to find, laying out exactly how and when to retire company-owned electronics.
A strong policy has to define a few key things:
- Retirement Triggers: What makes an asset ready for disposal? Is it age, poor performance, or the end of a lease? Be specific.
- Request Process: How does a department or an employee officially kick off the retirement process for a device?
- Data Handling Protocols: What are employees responsible for before they hand over a device, like backing up their own data?
- Chain of Custody: Who is responsible for the asset at every step, from an employee's desk to the secure IT storage area?
This policy gets rid of the guesswork. It ensures every device is handled the same way, every time, closing the security loopholes that always pop up with informal disposal methods.
An Asset Retirement Policy isn’t just paperwork; it’s a powerful security control. It creates a predictable and defensible process that protects your business from data loss and non-compliance when an asset's life is over.
The Asset Retirement Workflow in Action
Let’s follow a single company laptop from retirement to final disposition to see how a structured program really works. The process turns a simple request into a secure, fully documented event.
- Request Submission: An employee opens a ticket through the IT service portal to retire their laptop, giving a clear reason like "device is four years old and failing."
- IT Validation & Prep: IT confirms the request, backs up critical data if needed, and logs the device in the asset management system. Our article on the best IT asset management software can be a big help here.
- Secure Staging: The laptop is moved to a locked, designated holding area, waiting for pickup by your certified e-waste partner.
- Scheduled Pickup: The vendor shows up, scans the asset’s serial number into their system, and loads it into a secure, GPS-tracked vehicle. At this point, the chain of custody officially transfers.
- Final Disposition & Reporting: Back at the vendor's facility, the laptop's hard drive is destroyed, and the machine is either recycled or prepared for resale. A serialized Certificate of Data Destruction is generated and uploaded to your client portal.
This systematic workflow makes sure nothing slips through the cracks. It gives you a complete audit trail for every single asset, proving you’ve done your due diligence and met your compliance duties.
Navigating Industry-Specific Compliance Challenges
E-waste disposal is never a one-size-fits-all problem, and this is especially true when different industries face their own unique sets of rules and risks. A general recycling plan might be fine for office furniture, but it falls dangerously short for electronics loaded with sensitive data. The right corporate e-waste solutions are built to meet the strict compliance demands of your specific sector.
What works for a software startup won’t pass an audit for a hospital. The operational and regulatory hurdles vary wildly, meaning your e-waste partner must understand the specific world you operate in. From healthcare to government, each industry has non-negotiable requirements that dictate how every single asset must be handled.
Healthcare and HIPAA Compliance
For any healthcare provider—from a major hospital system to a private clinic—the Health Insurance Portability and Accountability Act (HIPAA) is the single most important factor in asset disposition. Every retired device, from a nurse's workstation to a diagnostic imaging machine, is a potential container for Protected Health Information (PHI). A single data breach from an improperly wiped hard drive can trigger mandatory patient notifications, government investigations, and fines that can easily reach into the millions.
This makes certified data destruction the most critical component of any healthcare e-waste program. It’s not just about wiping a drive; it's about creating an auditable, legally defensible record that proves PHI was irretrievably destroyed.
- Serialized Reporting is Mandatory: Each device's serial number must be tied directly to a Certificate of Data Destruction. A generic certificate for a "pallet of computers" is worthless in a HIPAA audit.
- Physical Destruction is Often Preferred: To eliminate all doubt, many healthcare organizations opt for on-site hard drive shredding. This allows them to witness the destruction of data-bearing media before it ever leaves their facility.
- Business Associate Agreements (BAAs): Your e-waste vendor must be willing to sign a BAA, legally obligating them to protect your PHI with the same rigor you do.
Under HIPAA, your responsibility for protecting patient data doesn't end when a device is retired. Your organization remains liable until you can produce irrefutable proof that the data has been permanently destroyed according to NIST 800-88 guidelines.
Data Centers and Large-Scale Decommissioning
Data centers face a challenge of sheer scale. Decommissioning hundreds or even thousands of servers at once is a massive logistical and security undertaking. Each server contains multiple hard drives, and every single one must be sanitized with 100% certainty. A single missed drive in a decommissioned rack could lead to a catastrophic data breach.
The focus here is on process efficiency without sacrificing an ounce of security. A specialized e-waste partner must be able to manage these high-volume projects with military-like precision.
Key requirements for data center e-waste solutions include:
- On-Site Project Management: A dedicated team to manage the entire decommissioning process, from de-racking servers to securely packing and transporting them.
- High-Volume Data Destruction: The capability to perform on-site shredding or wiping of thousands of drives within a tight project timeline.
- Complete Asset Reconciliation: Every single asset tag and serial number must be scanned, tracked, and reconciled against a master project list to ensure nothing is lost.
Government and Public Sector Security
For government agencies—whether federal, state, or local—the primary concerns are an unbroken chain of custody and absolute security. The data on government devices can range from sensitive citizen information to classified national security data. As a result, the protocols for asset disposal are incredibly strict and often require a higher level of clearance and process verification.
Vendors serving this sector must demonstrate an unwavering commitment to security protocols. This often means providing services that go above and beyond standard commercial offerings.
- Cleared Personnel: Technicians handling the equipment have often undergone extensive background checks.
- Secure, GPS-Tracked Logistics: All vehicles used for transport must be sealed, locked, and monitored in real-time from the point of pickup to the secure facility.
- Restricted Facility Access: The processing facility itself must have robust security measures, including 24/7 surveillance, strict access controls, and isolated cages for processing sensitive assets.
By understanding these industry-specific needs, you can see how a truly effective e-waste partner customizes their approach. They don't just offer a service; they provide a solution built to withstand the intense scrutiny of your industry's regulators and auditors, ensuring you remain compliant and secure.
Common E-Waste Pitfalls and How to Avoid Them
Even with the best intentions, a corporate e-waste program can fail spectacularly due to a few common, yet critical, mistakes. These pitfalls often lead directly to the exact outcomes you’re trying to prevent: data breaches, compliance fines, and surprise costs. Understanding these traps is the first step to building a truly secure and resilient program.
The most frequent mistake is choosing a vendor based on price alone. A quote that seems too good to be true almost always is. It's a huge red flag that a vendor is cutting corners on essential security protocols, data destruction verification, or responsible recycling—shifting all the liability right back onto your company.
The Pitfall of Generic Reporting
Another major issue is accepting vague, non-serialized reports from your vendor. You might get a "Certificate of Recycling" that simply lists "one pallet of mixed electronics." For any audit, that document is practically useless. It offers zero real proof of what happened to your specific assets.
Without serialized tracking, you have no way to prove that the hard drive from a specific executive's laptop was actually destroyed. This documentation gap creates a massive risk, especially if you're ever facing a compliance audit or a data breach investigation.
Key Takeaway: If your e-waste report doesn't link the unique serial number of each asset to a specific outcome—like certified data destruction or resale—then it’s not a true compliance document. It’s just a receipt.
To sidestep this, demand detailed, serialized reports as a non-negotiable part of your service agreement. A professional partner will give you access to a portal where you can see the documented final disposition for every single asset you hand over.
Neglecting Employee Training
Finally, one of the most overlooked weak spots is the failure to train employees on your disposal procedures. Your asset retirement policy is only effective if your team actually knows it exists and understands how to follow it. When employees are left in the dark, they often resort to insecure, makeshift methods. For more on this, check out our guide on how to dispose of old computers safely.
This can lead to serious mistakes, including:
- Stockpiling: Old devices get stashed in unsecured closets or under desks, where they are eventually forgotten or stolen.
- Improper Disposal: Staff might toss old keyboards, mice, or even company phones into the regular trash, which can violate local disposal laws.
- Using Unvetted Services: A well-meaning employee might try to be helpful by dropping off old equipment at a local, uncertified collection event, completely breaking the chain of custody.
The fix is straightforward: integrate your e-waste policy into new employee onboarding and hold annual refresher training sessions. Make the process clear, simple, and easy to follow. By tackling these common pitfalls head-on—prioritizing security over cost, demanding detailed reporting, and training your staff—you can ensure your e-waste program is not just implemented, but truly effective.
Frequently Asked Questions About Corporate E-Waste
When it comes to corporate e-waste, IT, compliance, and facilities managers often run into the same practical questions. Here are some straightforward answers to the questions we hear most often.
What Is the Difference Between a Recycler and an ITAD Vendor?
Think of it this way: a basic recycler is like a junk hauler. Their main job is to take old electronics and break them down for raw materials like copper and plastic. Their focus is on recovering those materials, not necessarily on protecting your data or giving you a detailed audit trail.
An IT Asset Disposition (ITAD) vendor, on the other hand, is a full-service security partner. They manage the entire end-of-life process, from secure logistics and certified data destruction to finding ways to remarket usable equipment to recover value. While recycling is part of what they do, an ITAD vendor’s primary mission is to eliminate risk and ensure your business stays compliant.
The real difference comes down to risk management. A certified ITAD partner provides a documented, legally defensible process that a standard recycler simply can't match, making them the only safe choice for handling corporate e-waste.
Can We Just Wipe Hard Drives Ourselves?
Handling data destruction internally might seem like a good way to save money, but it opens your business up to some serious risks. Without the right software, validation tools, and a documented process that meets NIST 800-88 standards, you have no way to prove the data was actually destroyed.
If a data breach ever gets traced back to a device you thought was clean, the liability falls squarely on your company. Partnering with a NAID AAA certified vendor transfers that risk. They provide an official Certificate of Data Destruction for every single drive, giving you a rock-solid audit trail to stand behind.
How Much Does a Professional E-Waste Service Cost?
The cost for professional e-waste services really depends on the specifics of the job. A few key factors come into play:
- Volume and Type of Equipment: A full data center decommissioning project will have very different logistics costs compared to a routine office cleanout.
- Data Destruction Method: On-site hard drive shredding, for instance, is typically priced differently than off-site data wiping services.
- Asset Value: If your retired equipment still has resale value, the money generated from remarketing can significantly reduce or even cover the cost of the service.
A good partner will always give you transparent, itemized pricing that clearly explains all the fees involved.
Ready to put a secure, compliant e-waste program in place? Dallas Fortworth Computer Recycling offers nationwide, end-to-end ITAD services designed to protect your data and your brand. Schedule your secure pickup today.
