Arlington Electronics Recycling – arlington electronics recycling guide for 2026
For businesses in Arlington, secure electronics recycling is a critical security and compliance task, not just a disposal chore. It’s all about protecting your sensitive data, meeting strict regulations, and safeguarding your company’s reputation by working with a certified IT asset disposition (ITAD) expert.
Why Secure E-Waste Management Matters in Arlington

Every Arlington organization, sooner or later, needs to retire old technology. From servers and laptops to networking gear, this equipment often holds a company’s most valuable asset: its data. If they're not handled correctly, these devices aren't just junk—they are serious security liabilities waiting to be exploited.
The Real Risks of Improper Disposal
The risk goes far beyond a cluttered storage room. A single old hard drive, improperly discarded, can become a gateway for a devastating data breach, exposing customer records, trade secrets, or financial information.
The fallout from a breach like that is severe and hits from all sides. Your business could be looking at:
- Hefty Financial Penalties: Failing to comply with data privacy laws and environmental regulations like the Resource Conservation and Recovery Act (RCRA) can lead to major fines.
- Reputational Damage: A data breach shatters customer trust, which is incredibly difficult and expensive to win back. News of a security failure can permanently tarnish your brand.
- Operational Disruption: Cleaning up after a breach drains significant time and resources, pulling focus away from your actual business operations.
The real problem is that many businesses see old equipment as a disposal issue when they should be treating it as a security challenge. Reframing IT asset disposition (ITAD) as a risk-mitigation strategy is the first step toward protecting your organization.
Turning Liability into a Secure Process
This is where a strategic approach to Arlington electronics recycling becomes invaluable. Partnering with a certified ITAD provider transforms what feels like a chore into a streamlined, secure, and fully compliant process. It guarantees every device is managed correctly, from data sanitization to responsible recycling.
The United States generates more e-waste per person than any other country, and e-waste is the fastest-growing waste stream in the world. This puts immense pressure on businesses to adopt responsible practices.
Instead of trying to navigate these complexities on your own, a professional partner provides the expertise to manage every step. By working with an expert, you can learn more about the environmental impact of electronic waste and ensure your company is part of the solution, not the problem.
Building Your IT Asset Disposition Plan
Before you schedule a pickup for your Arlington electronics recycling project, you need a solid internal plan. A formal IT Asset Disposition (ITAD) strategy acts as your playbook, ensuring every step is secure, compliant, and serves your business goals. Jumping into disposal without this groundwork often leads to security gaps and logistical headaches.
The first step, before anything else, is a comprehensive asset inventory. This isn't just counting old computers in a storage room; it’s about creating a detailed catalog that prepares you for the security and compliance challenges ahead.
Cataloging Your Retiring Assets
Your inventory, whether it's a spreadsheet or an asset management database, needs to capture key details for every single piece of equipment slated for retirement. Think of it as creating a profile for each device. This process tells you exactly what you have and, more importantly, what level of risk it carries.
Use this template to categorize your business assets for recycling, ensuring no critical details are missed during your initial audit.
IT Asset Inventory Checklist for Arlington Businesses
| Asset Category | Key Information to Document | Data-Bearing (Yes/No) | Special Handling Notes |
|---|---|---|---|
| Computers & Laptops | Serial Number, Model, CPU, RAM, Storage Size | Yes | Note if SSD or HDD for destruction method. |
| Servers | Serial Number, Model, # of Drives, Location (Rack/Row) | Yes | Critical priority. Document RAID configuration if known. |
| Network Gear | Model (Switch, Router, Firewall), Port Count | Yes | May contain network configurations, IP info, and credentials. |
| Storage Media | Type (HDD, SSD, Tape), Serial Number, Capacity | Yes | Highest risk. Track individually, never as a bulk lot. |
| Monitors & Peripherals | Model, Size (for monitors), Type (Keyboard, Mouse) | No | Generally low risk; can be bulk-processed. |
| Mobile Devices | IMEI/Serial Number, Model, User (if known) | Yes | Often contains sensitive company and personal data. |
By documenting these details, you create the foundation for a secure and efficient disposal process that can be audited and verified.
The most critical piece of this audit is identifying whether an asset contains data. A server that held customer records requires a completely different disposal process than a pallet of monitors. Separating your assets into "data" and "non-data" piles from the very start is the bedrock of a secure plan. For a deeper look at this framework, you can review the essentials of IT asset disposition and its core components.
We often see businesses make the mistake of treating all electronics the same. Applying the same process to a high-risk server and a basic office phone either creates unnecessary security risks or inflates your costs. A detailed inventory prevents that.
Aligning Your Team and Setting Goals
A successful ITAD project isn't just an IT task—it requires input from across the organization. Getting the right people involved early on prevents internal friction and ensures all requirements are met.
Your planning team should include people from:
- IT: To oversee the technical inventory and specify data destruction requirements.
- Finance: To manage asset depreciation, track costs, and evaluate potential value recovery.
- Legal/Compliance: To ensure the plan adheres to all data privacy and environmental regulations like HIPAA or PCI-DSS.
With your team in place, define your primary goals. Is ironclad data security the absolute top priority? Are you focused on maximizing financial return from newer equipment? Or is demonstrating the highest standard of environmental compliance your main objective?
The answers will directly influence the services you need. For instance, a healthcare organization will prioritize NAID AAA certified data destruction above everything else. This clarity ensures your final ITAD plan is built specifically for your organization's unique risk profile and business needs.
Understanding Data Destruction and Compliance
With your inventory list in hand, the next step is tackling the most critical part of any Arlington electronics recycling project: data. Just deleting files or reformatting a hard drive isn't nearly enough. That data can often be pulled back with simple tools, creating a huge liability for your business.
True data security requires a deliberate, documented sanitization process. This really comes down to two paths: software-based wiping or complete physical destruction. The right choice depends on what you plan to do with the equipment and just how sensitive the data is.
Software Wipes for Asset Remarketing
If you have equipment that still holds some value—like a batch of three-year-old laptops—you'll want to consider software wiping. This process uses specialized programs to overwrite every sector of a drive with random data, making the original information completely unrecoverable.
We follow the DoD 5220.22-M standard, which involves multiple overwriting passes to ensure total data sanitization. This is the perfect strategy when you want to refurbish and resell assets to recoup some of your initial investment. The hardware stays functional, but the data is gone for good.
Think of software wiping as a value-recovery tool. It cleanses the data without harming the asset, making it ideal for functional equipment you want to give a second life.
Physical Destruction for Maximum Security
For some assets, there's just no room for risk. When a device has no resale value or held your most sensitive information—think intellectual property, financial records, or R&D data—physical destruction is the only answer.
This isn't just taking a hammer to a hard drive. It means ensuring the storage media is obliterated and unusable. The most common and effective methods are:
- Shredding: The drive is fed into an industrial shredder that tears it into small, unrecognizable metal fragments. It's the most secure method and provides clear visual proof of destruction.
- Degaussing: A powerful magnetic field is used to instantly scramble the magnetic data on a hard drive or tape, rendering it useless forever.
A decommissioned server that once stored your company's core financial data should always be physically shredded. The potential risk tied to that data is infinitely greater than any tiny value the hardware might have.
This decision-making process is something we help Arlington businesses navigate every day. Here’s a simple flowchart that shows how we approach it.
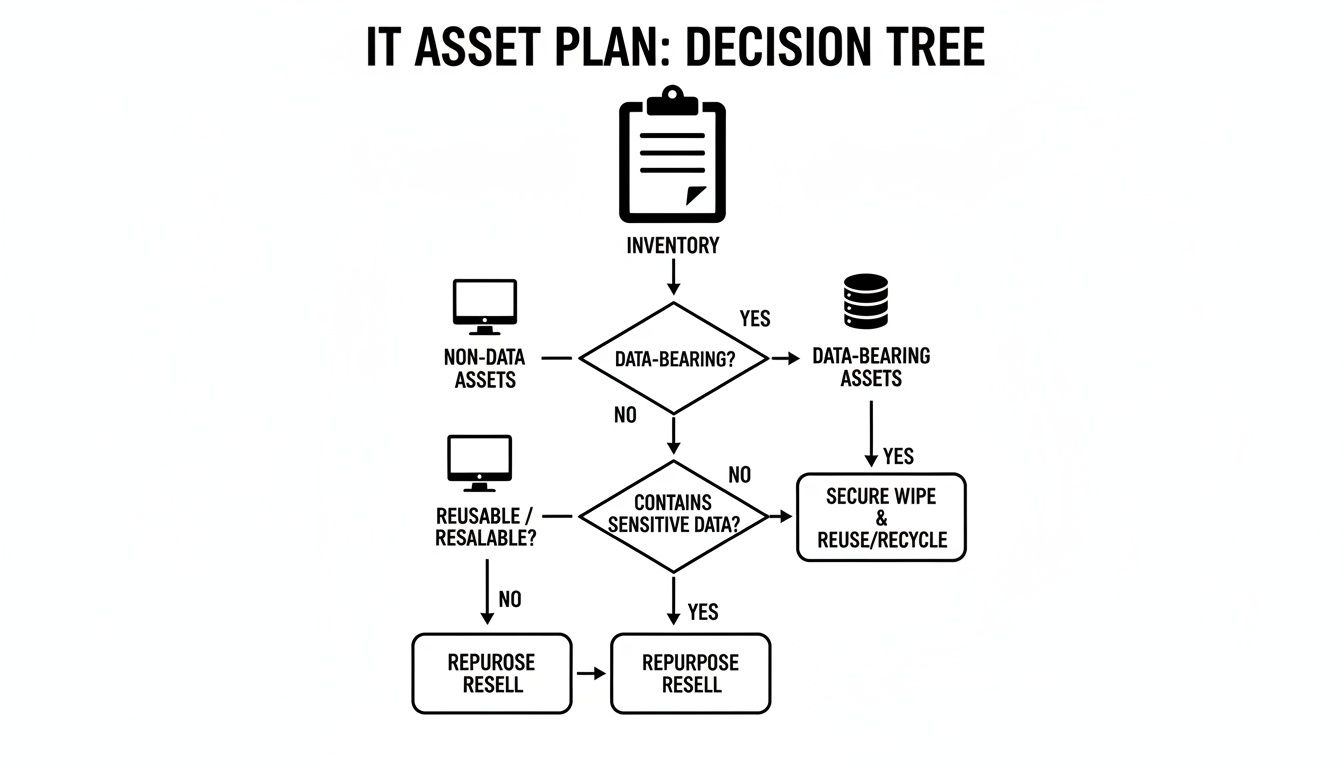
As you can see, the first question is always whether an asset holds data. That single factor dictates the entire security workflow that follows.
The Role of Certifications and Documentation
Working with a certified recycler is not optional—it’s your proof of due diligence. Certifications like R2 (Responsible Recycling), e-Stewards, and NAID AAA Certification aren't just for show. They are your guarantee that your partner follows the highest industry standards for security and environmental practices.
Once the job is done, you must receive a Certificate of Data Destruction. This document is your official, auditable record proving your data was properly destroyed in line with compliance rules. It details what was destroyed, how, and when, giving you a legal safeguard and completing the chain of custody. You can learn more about why this matters in our guide to certified and secure data destruction.
Securing Your Logistics and Chain of Custody

After you've sorted your inventory and decided on data destruction, the next step is often the most underestimated: getting the equipment from your Arlington facility to a recycling partner. This physical journey is one of the riskiest points in the entire process. A single security gap during transit can completely undo all your internal data protection efforts.
That’s why a documented chain of custody is non-negotiable. It’s the formal, auditable paper trail that follows your assets from the moment they leave your control, creating a clear line of accountability from your door to ours. This isn't just about a truck showing up; it’s about a managed, secure transfer of responsibility.
What Secure Transport Really Looks Like
Professional logistics for Arlington electronics recycling are built from the ground up to eliminate risk. For example, once you have your equipment ready, we take over to ensure it stays protected. Our process begins by securely palletizing and shrink-wrapping all assets right there at your location, before anything is even loaded onto a truck.
This is followed by several key steps:
- Vetted Personnel: Every member of our logistics team is background-checked and fully trained in handling sensitive IT equipment.
- Locked and Tracked Vehicles: Our trucks are always locked and equipped with GPS tracking, giving us a real-time log of your assets' location from start to finish.
- Serialized Documentation: The chain of custody form, which lists serial numbers for high-value or high-risk assets, is signed at your facility to officially confirm the transfer.
This systematic approach seals off any opportunity for assets to be misplaced, accessed, or compromised while on the move.
The moment your equipment leaves your building, it enters a critical "in-between" phase. A weak link here—like an unvetted driver or an unsecured vehicle—creates an unacceptable security risk. The chain of custody is your assurance that this link is strong.
Documenting the Entire Asset Journey
The chain of custody paperwork is the backbone of any compliant and secure electronics recycling project. It's the physical proof you need to show you did your due diligence in protecting your organization's data. Once the shipment arrives at our secure facility, each pallet is immediately checked against the initial paperwork and every serialized asset is verified.
This detailed tracking doesn’t stop until the very end. The final step is issuing a Certificate of Destruction, which serves as the official capstone of the chain of custody. You can learn more about how this provides legal and auditable proof in our guide on the importance of a Certificate of Destruction.
This level of detail is possible because of the mature recycling ecosystem here in Texas. State-level programs have processed incredible volumes of electronics, proving the infrastructure for secure handling is well-established. In fact, Texas programs have collected a cumulative total of 441,898,491 pounds of computers and televisions, with the vast majority recycled. You can see the scale of these efforts by reviewing the state-wide electronics collection data. This proven framework gives Arlington businesses real confidence in the logistics supporting their IT asset disposition needs.
What Electronics Can Your Business Recycle
It’s one of the first questions we hear from businesses planning an Arlington electronics recycling project: "So, what can we actually give you?"
Knowing the difference between standard IT gear and items that need special handling is the key to a smooth and efficient process. Getting it wrong from the start can lead to project delays, unexpected costs, and logistical headaches.
The good news is that the vast majority of your office technology falls into a set of standard categories we handle every day.
Standard Business Equipment We Accept
For most companies, the list of recyclable electronics covers just about everything in your IT closet and on your employees' desks. We’ve built our entire process around securely managing these common assets, from the moment we arrive for pickup to their final, documented disposition.
We regularly handle:
- Computers and Laptops: Desktops, all-in-ones, towers, and laptops of any brand, age, or condition.
- Servers and Data Center Gear: Rack-mounted servers, blade servers, and storage area networks (SANs).
- Networking Equipment: The switches, routers, firewalls, and modems that form the backbone of your network.
- Peripherals and Accessories: Keyboards, mice, docking stations, and external hard drives.
- Monitors: LCD, LED, and older CRT displays.
- Mobile Devices: All company-issued cell phones and tablets.
The core principle is simple: if it plugged into your IT network or stored company data, it needs a secure recycling path. We often see businesses make the mistake of treating a server full of sensitive information with the same care as an old keyboard. Our certified process helps you avoid that risk.
Handling Specialty and Unacceptable Items
Beyond typical office tech, many Arlington businesses rely on specialized equipment. This can include industrial control panels, medical diagnostic machines, or proprietary lab instruments. These assets often contain highly sensitive data or even potential contaminants that require a specific disposal plan. We work with you to create custom solutions for these items, ensuring both data security and environmental safety standards are met.
It’s just as important to know what doesn't belong with your IT assets. These items need to go into different waste streams and should be separated out before your pickup:
- Large appliances like refrigerators or HVAC units.
- Loose batteries not integrated into a device (e.g., car or forklift batteries).
- Light bulbs, especially fluorescent tubes.
- Items containing liquids, such as standalone ink or toner cartridges.
The City of Arlington runs a great residential program, which shows a strong local commitment to keeping e-waste out of landfills. You can learn more about the city's residential program and see how our local infrastructure supports proper disposal for everyone.
By separating your standard IT assets from specialty gear and other materials, you make the entire process faster and more compliant. For an even more detailed breakdown, you can check out our guide on recycling different types of computer equipment.
Common Questions About Business E-Waste Recycling
When it comes to electronics recycling, we find Arlington businesses often have the same core questions. Getting these answers right is the first step toward building a secure and compliant IT asset disposition (ITAD) plan. We've addressed the most common concerns we hear from organizations just like yours.
What Is the True Cost of Electronics Recycling?
The cost for any Arlington business will depend on a few key factors: the volume and type of equipment you have, and the level of data destruction you need. In some cases, newer equipment with resale value can help offset recycling fees or even generate a small return.
But the real cost isn't what you pay for recycling—it's the potential cost of doing nothing. The financial fallout from a single data breach or fines for environmental non-compliance can be catastrophic. A professional partner provides a transparent quote, allowing you to weigh the manageable cost of certified recycling against the immense liability of improper disposal.
How Can I Be Certain My Company's Data Is Destroyed?
This is, without a doubt, the most important question for any Arlington electronics recycling project. Absolute certainty doesn't come from a simple promise; it comes from a certified, fully documented process that leaves zero room for error.
You gain that assurance through a few critical layers of security:
- Standardized Destruction Methods: We align our processes with rigorous government and industry standards, including those outlined in NIST 800-88.
- Unbroken Chain of Custody: A strict, documented trail tracks every single asset from your facility to its final disposition. Nothing gets lost or overlooked.
- Formal Certification: Upon completion, you receive a serialized Certificate of Data Destruction.
This certificate is more than just a piece of paper. It's your legally auditable proof that every data-bearing device was properly sanitized, protecting your business from future liability.
Is It Worth Using a Professional Service for Only a Few Items?
Absolutely. Data security isn't about the quantity of devices; it's about the sensitivity of the information they hold. A single executive's laptop, if improperly discarded, could contain enough strategic plans, client data, or financial records to trigger a major security incident.
While there are residential drop-off sites, they simply aren't equipped to provide the certified data destruction, serialized tracking, and auditable proof that businesses require for compliance. Professional services are built to be scalable, offering a secure and compliant ITAD solution for every Arlington organization, no matter the size.
What Happens to Our Equipment After You Pick It Up?
Once your assets leave your facility, they enter a structured process guided by a "reuse, recover, recycle" hierarchy. Our first priority is always to find opportunities for reuse.
Viable devices are thoroughly tested, completely sanitized of all data, and refurbished for resale. This is the most environmentally responsible approach and helps recover maximum value from your assets.
Items that can't be reused are carefully de-manufactured. They are broken down into their core commodity streams—plastics, precious metals, glass, and circuit boards. These raw materials are then sent to our network of vetted downstream partners to be reintroduced into the manufacturing supply chain. Our strict zero-landfill policy ensures every component is handled with complete environmental responsibility.
When you're ready to implement a secure, compliant, and environmentally responsible plan for your organization's retired IT assets, Dallas Fortworth Computer Recycling is here to help. We provide the expertise and certified processes that Arlington businesses trust. Visit us online to learn how we can support your ITAD needs at https://dallasfortworthcomputerrecycling.com.
