Data destruction Irving: Secure & Compliant Solutions for 2026

For businesses in Irving, hitting 'delete' on old hardware offers a false sense of security. Every retired server, laptop, and hard drive holds the potential for a massive data breach, making professional data destruction Irving services an essential part of your IT security strategy. It's the only way to ensure your company's sensitive information is permanently and verifiably destroyed.
Why Secure Data Destruction Is Non-Negotiable in Irving
Every outdated piece of IT equipment in your Irving office contains data that can be recovered. When you delete a file, you’re not actually erasing the information; you're simply removing the system's pointer to it. The data itself often remains on the hard drive, easily retrievable with the right software.
This isn't a theoretical risk. This lingering data can expose your most sensitive information, from financial records and customer lists to proprietary trade secrets. For any organization, a single improperly discarded hard drive can become a ticking time bomb, leading to costly breaches, regulatory fines, and irreparable damage to your reputation.
The Escalating Risk of Dormant Data
The amount of data we create is staggering, and this amplifies the risk. By 2025, the world is projected to store over 200 zettabytes of data, with associated cybercrime costs expected to hit $10.5 trillion annually. This data explosion has contributed to a 68% spike in data breaches, making outdated hardware a prime target for criminals. You can explore the full scope of these projections at Cybersecurity Ventures.
Think of a retired server like an old filing cabinet. Simply throwing it out without shredding the documents inside would be unthinkable. Failing to professionally destroy the data on that server is the digital equivalent—an open invitation for disaster.
This is where a professional approach to data destruction transforms a liability into a secure, documented, and compliant process. It moves your business from a position of risk to one of complete control.
Turning Liability into a Secure Asset
Engaging a certified partner for data destruction in Irving is about much more than just breaking old hard drives. It’s about implementing a verifiable process that protects your organization from the ground up. This structured approach includes:
- Inventory Management: Identifying every single device that holds data, from servers and laptops to printers and USB drives.
- Secure Logistics: Ensuring a documented chain of custody from the moment an asset leaves your facility.
- Certified Destruction: Using approved methods like physical shredding or degaussing to render data completely unrecoverable.
- Auditable Proof: Providing a Certificate of Destruction as legal proof that your compliance obligations have been met.
By following these steps, you defuse the ticking time bomb of old IT assets. A comprehensive IT asset disposition (ITAD) strategy ensures your data lifecycle ends with total security. You can learn more about how a full-service ITAD program in Irving can protect your business. This proactive stance is the cornerstone of modern data security and corporate responsibility.
The Difference Between Deleting and Destroying Data
It’s a common mistake to think that hitting “delete” or dragging a file to the recycling bin makes it disappear for good. For businesses, this misunderstanding creates a massive security gap. In reality, deleting a file is like tossing a sensitive memo into an office trash can—it’s out of sight, but it’s far from gone.
Anyone with basic data recovery software can easily "dumpster dive" into your old hard drives and pull back files you thought were erased. The operating system just marks the space as available for new data. Until that space gets overwritten, the original information is still there, perfectly intact and ready to be recovered.
True data destruction, on the other hand, is an irreversible process that makes data completely unrecoverable. It’s the only way to be certain that your company's proprietary information, customer records, and financial details don't end up in the wrong hands after your IT assets are retired.
Comparing Data Destruction Methods
To achieve permanent erasure, professionals use specific, verifiable techniques. Each method has a distinct purpose and works best for different types of media. The three primary methods used for professional data destruction in Irving are data wiping, degaussing, and physical shredding.
This flowchart shows how retired hardware, if not handled properly, can lead to significant business risks from these lingering "digital ghosts."
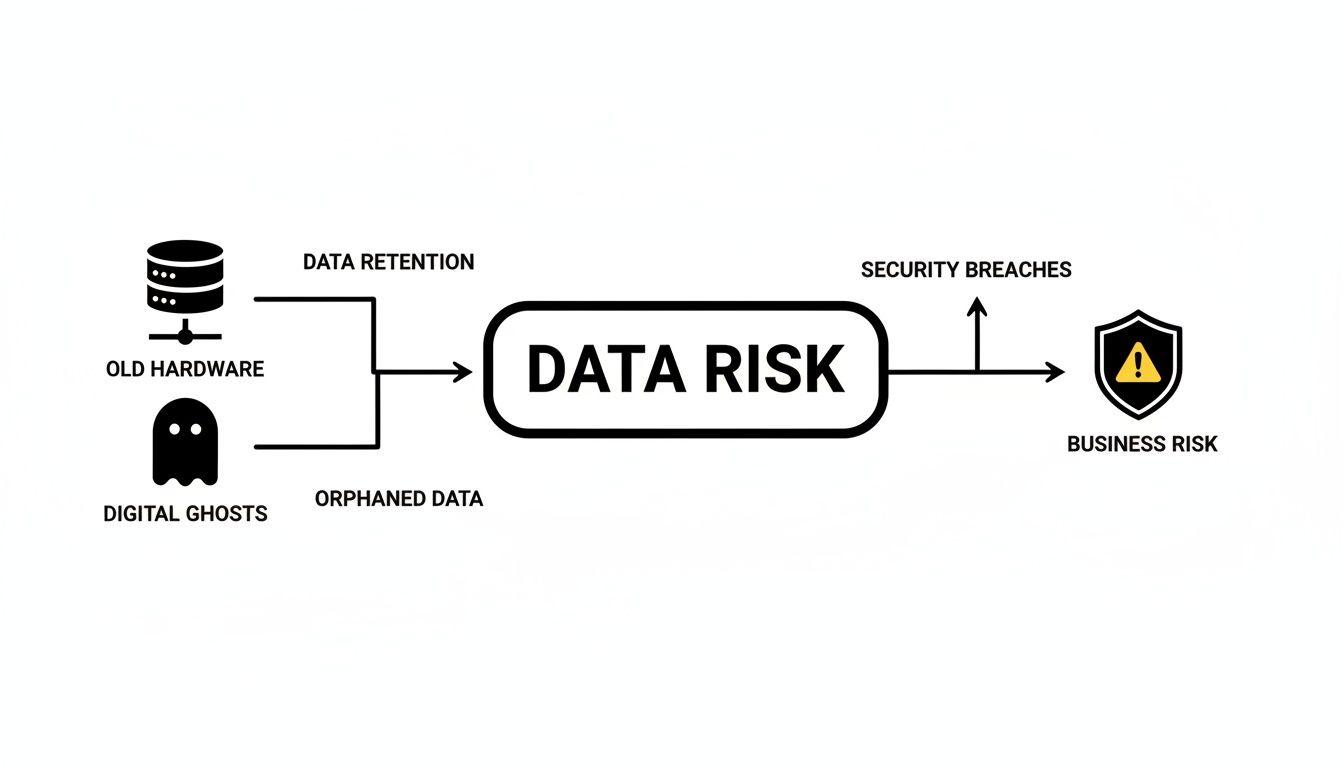
As you can see, there’s a direct line from old equipment to potential security breaches, highlighting why just storing or improperly disposing of hardware is a direct threat.
Data Wiping: Overwriting Information
Data wiping, also called overwriting or clearing, is a software-based approach. Think of it like taking a thick, permanent marker and scribbling over every single word on a document until the original text is completely unreadable.
Specialized software writes patterns of ones and zeros across the entire drive—often multiple times—to overwrite the original data. This process sanitizes the drive, making data recovery practically impossible.
- Best For: Hard Disk Drives (HDDs) that are still working and might be reused or resold.
- Key Advantage: It allows the physical drive to be repurposed, which is both cost-effective and good for the environment.
It's important to know, however, that wiping isn't a silver bullet for Solid-State Drives (SSDs) because of the way they scatter data across non-linear blocks. For those, you need a more definitive method. For a deeper dive into the technical side, check out our guide on how to completely wipe a hard drive.
Degaussing: Erasing with Magnetism
Degaussing is a powerful and highly effective method for magnetic media like HDDs and backup tapes. It’s like using an industrial-strength magnet to instantly vaporize all the ink from a document, leaving it totally blank.
A degausser creates an intense magnetic field that completely neutralizes the magnetic domains on a hard drive's platters where data is stored. This process instantly and permanently erases everything, and it also renders the drive inoperable.
This method is incredibly fast and thorough for the right kind of media. But it doesn't work on non-magnetic storage like SSDs, and since it destroys the drive, reuse is out of the question.
Physical Destruction: The Ultimate Guarantee
When data absolutely must be destroyed beyond any doubt, nothing beats physical destruction. This is the equivalent of feeding a sensitive document into an industrial cross-cut shredder that turns it into tiny, unreadable pieces of confetti.
During this process, hard drives, SSDs, and other media are fed into powerful shredders that grind them into small, irregular fragments. This method is the gold standard for security and is often required to comply with regulations like HIPAA or FACTA.
Advantages of Physical Destruction:
- Universal Effectiveness: It works on all media types, including HDDs, SSDs, flash drives, and CDs/DVDs.
- Absolute Security: It provides a visible, undeniable guarantee that the data and the device are destroyed for good.
- Compliance Peace of Mind: It meets the highest standards for data sanitization, ensuring you're ready for any audit.
Choosing the right method comes down to your security needs, compliance requirements, and whether you plan to reuse the hardware. For the highest level of assurance, a professional data destruction Irving service offering certified shredding provides the ultimate protection.
Staying Compliant with Data Privacy Laws in Texas
For any business in Irving, especially those in healthcare, finance, or legal services, data privacy isn't just a best practice—it's a strict legal requirement. Juggling regulations like HIPAA, FACTA, and Texas's own privacy laws can seem overwhelming, but their core message is straightforward: you are legally on the hook for protecting sensitive data from the moment it's created to the moment it's destroyed.
Picture this: a North Texas medical clinic upgrades its servers. The old equipment, still loaded with thousands of patient records, gets tossed in with a general recycler and eventually finds its way to a landfill. If that data is ever recovered, the clinic faces a nightmare scenario of staggering fines, drawn-out legal battles, and a complete collapse of patient trust. This isn't just a "what-if"; it's a real-world risk that highlights why compliant disposal is so critical.
Professional data destruction in Irving turns this legal headache into a simple, manageable process. It ensures your organization meets every obligation and is shielded from the devastating fallout of a breach.
The Major Regulations Affecting Irving Businesses
A few key federal and state laws dictate exactly how your business must handle data. While each law has a slightly different focus, they all share a common demand: you must securely and permanently destroy personally identifiable information (PII) and protected health information (PHI) once it's no longer needed.
Understanding these rules is the first step in building a compliant data destruction plan. To make it easier, we've created a quick reference table.
Compliance at a Glance Key Data Destruction Regulations
| Regulation | Who It Affects | Key Data Disposal Requirement |
|---|---|---|
| HIPAA | Healthcare providers, clinics, insurers, and their business associates. | Must render Protected Health Information (PHI) "unreadable, indecipherable, and otherwise unable to be reconstructed." |
| FACTA | Virtually any business that handles consumer credit information. | Requires the proper disposal of consumer information through methods like burning, pulverizing, or shredding. |
| Texas ITEPA | All Texas businesses that possess sensitive personal information. | Includes a "Disposal Rule" similar to FACTA, mandating secure destruction of personal data to prevent misuse. |
Breaking these rules can lead to fines that stretch into the millions of dollars for a single incident. This is why it’s so important to partner with a destruction provider who knows these regulations inside and out. For healthcare providers, our guide on HIPAA-compliant electronics recycling in Texas provides more specific details.
The core principle is simple: your responsibility doesn't end when a device is unplugged. Your organization is accountable for the data's entire lifecycle, and having proof of proper destruction is your ultimate safeguard.
This intense focus on compliance is fueling major industry growth. The secure data destruction market, valued at $4.4 billion in 2025, is expected to more than double to $10.3 billion by 2034, driven by strict adherence to laws like HIPAA. With North America commanding a 38% market share, the demand for professional, compliant services has never been higher.
Turning Legal Requirements into a Simple Process
Compliance doesn't have to be a burden. A certified data destruction partner translates these dense legal statutes into a clear, actionable plan for your business. They ensure the methods used—whether it’s physical shredding, degaussing, or data wiping—meet or exceed the specific standards set by HIPAA, FACTA, and other relevant laws.
This partnership gives you more than just a service; it provides documented proof and peace of mind. By issuing a formal Certificate of Destruction after every job, your Irving business gets the auditable, legal evidence needed to prove due diligence. This single document confirms you took all the necessary steps to protect sensitive information, effectively closing the loop on your compliance duties and protecting your brand from the consequences of a data breach.
Choosing Between On-Site and Off-Site Destruction
So, you've decided to bring in the pros for data destruction. Smart move. Now comes the next big question: where should the destruction actually happen?
For businesses here in Irving, it really boils down to two choices. We can bring the shredder to you (on-site destruction), or we can securely transport your assets to our facility for destruction (off-site). Both get the job done right, but the process, verification, and logistics are different.
Think of it like choosing between a mobile paper shredding truck that visits your office versus sending locked document bins to a secure plant. Both result in shredded paper, but how you get there—and the oversight you have along the way—is what sets them apart. Figuring out which path fits your company's security policies and operational needs is key to building the right data destruction Irving strategy.

On-Site Destruction: Ultimate Transparency and Control
On-site destruction is exactly what it sounds like. We roll up to your Irving facility with a specialized truck carrying industrial-grade shredders, and the entire process happens right there while you watch.
This gives you the absolute highest level of security and assurance. Your team can physically witness every single hard drive, SSD, or tape get turned into tiny, irrecoverable pieces. There's no gray area.
It’s the go-to method for organizations with zero tolerance for risk. If you're a healthcare provider managing PHI, a law firm with sensitive case files, or a government contractor, the ability to visually confirm destruction provides unmatched peace of mind.
Here’s why it's the gold standard for high-security environments:
- Maximum Security: Your devices never leave your property intact. This completely eliminates any risk during transit and creates an immediate, airtight chain of custody.
- Direct Verification: You and your staff can watch the entire shredding process from start to finish. It’s undeniable proof that the job was done.
- Compliance Peace of Mind: For regulations like HIPAA or GLBA that demand strict oversight, on-site destruction is the most direct way to prove you’ve met your obligations.
This immediate, witnessed destruction is the most straightforward way to ensure total compliance. You can see more on how this service works by checking out our options for on-site shredding near you.
Off-Site Destruction: Efficiency and Scalability
Off-site destruction is a secure, highly efficient, and often more cost-effective option, especially when you're dealing with a large volume of IT assets.
With this approach, our certified team comes to your Irving office to collect and securely containerize all your old devices. We use locked, tamper-evident bins to ensure nothing can be accessed after it leaves your hands.
From there, the sealed containers are transported in a GPS-tracked, secure vehicle to our specialized destruction facility. The entire plant is under 24/7 video surveillance with strictly controlled access. Once your assets arrive, they are destroyed under these controlled conditions, with the whole process meticulously documented.
The integrity of off-site destruction hinges on an unbroken chain of custody. This documented trail—from secure collection at your site to final destruction—is your guarantee that every asset is accounted for and handled with the highest level of security.
This process is perfect for businesses managing large-scale projects like an office-wide IT refresh, a data center decommissioning, or simply routine disposals where cost and logistics are big factors.
How to Make the Right Choice for Your Business
There’s no single "best" answer here. The right choice is the one that best aligns with your company's specific risk tolerance, budget, and operational workflow.
Use this simple table to help guide your decision:
| Factor | On-Site Destruction is Better if… | Off-Site Destruction is Better if… |
|---|---|---|
| Security Protocol | Your internal policies demand direct, visual confirmation of destruction. | A fully documented, secure chain of custody meets your security needs. |
| Data Sensitivity | You're handling classified government data, top-tier IP, or other extremely sensitive information. | You have large volumes of standard business data that require certified, but not witnessed, destruction. |
| Logistics | You have the physical space at your Irving facility for a large shredding truck to park and operate. | Your site has logistical constraints (like a downtown high-rise) or you're disposing of a very large quantity of assets. |
| Cost | The premium for absolute, witnessed security is a worthwhile investment for your risk profile. | You're looking for a highly efficient and budget-friendly solution for bulk destruction projects. |
Ultimately, both on-site and off-site methods, when performed by a certified and trusted provider, deliver secure and compliant data destruction in Irving. No matter which option you choose, we will provide a detailed Certificate of Destruction, giving you the official documentation you need to satisfy any audit.
Why a Certificate of Destruction Is Your Proof of Compliance
When it comes to secure data disposal, the job isn’t done until the paperwork is. While the physical destruction of a hard drive is essential, the documentation that follows is what proves you’ve met your compliance obligations. This audit trail is your defense against legal challenges and heavy fines for your Irving business.
Think of it like tracking a valuable shipment. You don't just send it off and hope for the best; you get a tracking number and follow its journey. In data destruction, this process involves two critical documents: the Chain of Custody and the Certificate of Destruction. Together, they form an unbreakable record of secure handling.

The Chain of Custody Your Step-by-Step Tracking History
The Chain of Custody document is the live, detailed log for your data-bearing assets. It starts the moment our team arrives at your Irving office, recording every laptop, server, and hard drive by its unique serial number.
This document records every single touchpoint:
- Collection: Who collected the assets and when.
- Transport: Details of the secure, GPS-tracked vehicle used.
- Receipt: Confirmation of arrival at our secure destruction facility.
- Final Disposition: The exact method and date of destruction for each asset.
Every handoff is documented, creating a transparent timeline. This meticulous process proves that your sensitive assets were securely managed from your door to their final destruction, leaving no room for questions.
The Certificate of Destruction Your Delivery Confirmation
If the Chain of Custody is the tracking history, the Certificate of Destruction is the official "delivery confirmed" notice. This legally binding document is your absolute proof that all your data was destroyed according to industry standards and government regulations.
This certificate is more than a simple receipt. It’s your primary defense in a compliance audit and formally transfers liability for the destroyed assets from your organization to us, your certified destruction partner.
A valid certificate must be specific. Our guide on the Certificate of Destruction for hard drives details exactly what information it needs, including individual serial numbers and the specific destruction methods used.
Verifying Your Partner’s Credentials
Your documentation is only as reliable as the partner who issues it. With the data destruction market projected to grow from $12 billion in 2025 to $39.3 billion by 2035, it's crucial to choose a partner with verifiable credentials. This explosive growth, detailed in a cybersecurity analysis, highlights the need for trusted experts.
To ensure your data destruction Irving provider is qualified, always check for key industry certifications. These credentials confirm that a company operates at the highest standards for security and environmental responsibility.
Key Certifications to Verify:
- R2 (Responsible Recycling): This certification ensures electronics are managed in an environmentally sound and secure manner, covering everything from data sanitization to worker safety.
- e-Stewards: As one of the most stringent standards, e-Stewards guarantees that no hazardous e-waste is exported and that data security protocols are strictly followed.
Always ask to see copies of these certifications and confirm they are current. A reputable partner will gladly provide this proof. By pairing a certified provider with a complete audit trail, you build an undeniable record of due diligence and give your Irving business complete peace of mind.
How to Get Started with Professional Data Destruction
Getting started with a professional data destruction plan for your Irving business is a straightforward process. At Dallas Fortworth Computer Recycling, we’ve refined our service into four clear steps, designed to move from the initial conversation to your final compliance certificate with no guesswork or operational headaches. Here’s a look at how we work with you, from the first call to the final, legally-defensible documentation.
Our process starts with a simple, no-obligation consultation to understand your specific needs. This is where we learn about the types and number of devices you need to retire—whether it's a few racks of servers, a closet full of old laptops, or specialized equipment unique to your industry.
We also use this time to map out your compliance requirements. If you're a healthcare provider governed by HIPAA or a financial services firm needing to meet FACTA rules, we align the destruction method to your exact legal and security obligations.
Step 1: Initial Consultation and Inventory
This first conversation lays the groundwork for the entire project. We work with your team to create a detailed inventory of every data-bearing asset you need to dispose of. This critical step ensures every single device is accounted for right from the beginning. Think of it as the master manifest that guides the entire process, forming the basis for a complete and auditable chain of custody.
Once we have a clear picture of your inventory and compliance needs, we provide a transparent, itemized quote. This quote breaks down all costs for the data destruction Irving service, so you know exactly what to expect.
Step 2: Secure Pickup Logistics
After you approve the plan, we schedule the on-site pickup. Our team coordinates with you to find a time that causes the least disruption to your day-to-day operations in Irving. Our professional logistics crew arrives at your location fully prepared to securely manage and pack all designated equipment.
The moment your assets are prepared for transit marks the official start of the chain of custody. Each device is carefully cataloged and placed into secure, locked containers for transport, guaranteeing integrity from your door to ours.
This documented handoff is a vital security checkpoint. It serves as formal confirmation that your sensitive assets are now in our professional care, managed under strict, auditable protocols.
Step 3: Execution and Verification
This is where your data is permanently destroyed. If you selected on-site destruction, our mobile shredding truck performs the work right at your facility, allowing your team to witness the entire process. For off-site destruction, your assets are transported in a secure, GPS-tracked vehicle to our controlled facility, where they are destroyed under constant video surveillance.
Regardless of the location, our methods are aligned with NIST 800-88 guidelines and other industry standards. This guarantees your data is rendered completely and permanently irrecoverable.
Step 4: Final Documentation and Reporting
The process isn't over until you have the paperwork to prove it. We provide a complete documentation package that serves as your irrefutable proof of compliance. This package includes:
- A Certificate of Destruction, a legal document certifying that your data was destroyed in accordance with all applicable regulations.
- A detailed Chain of Custody record, giving you an auditable trail for every asset from the moment we picked it up.
- A Serialized Asset Report that lists every individual item by its serial number for your internal records.
This final documentation package gives you the concrete evidence needed for any compliance audit. It formally closes the loop on your IT asset disposition process and protects your organization from future data-related risks.
Frequently Asked Questions About Data Destruction in Irving
Even when you have a plan in place, a few practical questions always pop up before you hand over your old equipment. We get it. To help business leaders here in Irving move forward with confidence, we’ve put together answers to the most common questions we hear about our secure data destruction process.
These are the straightforward, no-nonsense answers you need to finalize your IT asset disposition strategy and protect your organization.
What Types of Devices Need Professional Data Destruction?
It’s a common misconception that only computers and servers hold sensitive data. The reality is that any device with memory or storage capabilities is a potential liability and needs professional data destruction before it leaves your facility.
A complete inventory of assets for data destruction in Irving should always include:
- Primary Storage: Hard Disk Drives (HDDs), Solid-State Drives (SSDs), and all server equipment.
- Portable Media: Simple things like USB flash drives, external hard drives, and memory cards are often overlooked.
- Legacy Systems: Old backup tapes (like LTO), CDs, and DVDs still contain recoverable information.
- Office Equipment: Most people don't realize modern printers, copiers, and scanners have internal hard drives that store images of every document they process.
- Mobile Devices: All company-issued smartphones and tablets must be professionally sanitized.
For businesses in Irving's diverse sectors—from healthcare to manufacturing—this can also mean specialized diagnostic tools or control systems with their own embedded storage. We help you identify every single data-bearing asset so no vulnerability gets missed.
How Is the Cost of Data Destruction Determined?
There’s no flat rate for data destruction because every project is different. The final cost depends on a few key factors that are specific to your company's security needs and the scope of the job.
Think of it not as an expense, but as an investment in risk management. The cost of a data breach—in fines, legal fees, and reputational damage—far exceeds the price of secure, certified destruction.
The main drivers that influence your quote include:
- Destruction Method: Physical shredding is priced differently than certified software-based data wiping.
- Quantity and Type of Devices: The sheer volume and mix of assets naturally affect the time and resources required.
- Service Location: On-site destruction, where we bring our mobile shredding equipment to your Irving facility, has a different cost structure than our off-site services.
As your partner, we provide a clear, itemized quote based on your specific inventory. You’ll know exactly what you’re paying for and the compliance assurance it delivers.
Is a Certificate of Destruction Enough for a Compliance Audit?
A Certificate of Destruction is a critical piece of the puzzle, but for a compliance audit to go smoothly, it needs to be part of a complete documentation package. On its own, it’s not enough. Auditors want to see the full story of your assets' journey from your control to final disposition.
A truly defensible audit file includes a detailed chain-of-custody record, serialized asset lists, and corresponding recycling reports. This complete documentation creates an unbroken, transparent record that proves you’ve met your obligations under regulations like HIPAA, FACTA, and others. We provide this full suite of documentation so you can face any audit with confidence.
Ready to implement a secure and compliant data destruction strategy for your Irving business? Dallas Fortworth Computer Recycling offers certified, auditable services tailored to your specific needs. Protect your organization from risk by ensuring your data is permanently destroyed. Schedule your secure data destruction service today.
