Data destruction Plano: Secure, Certified Services for Your Business
For any business in Plano, managing old IT assets isn't just about clearing out a storage closet. It’s a critical security function. The best path forward is to work with a certified data destruction service that can guarantee every retired hard drive, server, and laptop is handled with an unbreakable chain of custody and verifiably destroyed.
Your Guide to Secure Data Destruction in Plano

Every obsolete piece of technology in your Plano office—from a forgotten server to a stack of old company laptops—holds the potential for a data breach. Managing this risk isn't just an IT problem; it's a fundamental business responsibility that protects your company’s reputation, finances, and sensitive information.
Think of it like this: you would never toss old client contracts or financial records into a public recycling bin. You'd hire a professional shredding service to ensure they are completely destroyed. The exact same principle applies to your digital assets, only the stakes are significantly higher.
Why Professional Destruction Services Are Essential
The demand for professional data destruction is growing fast, and for good reason. Stricter data privacy regulations and the sheer volume of old IT hardware piling up in businesses have made DIY solutions obsolete and risky.
Recent industry analysis shows the global market for these services is on a steep upward climb, jumping from around $11.93 billion in 2025 to a projected $14 billion in 2026. That reflects a powerful compound annual growth rate of 17.3%. This isn't just a random statistic; it directly mirrors how modern businesses create massive amounts of data on devices that must be securely neutralized at the end of their lifecycle.
Choosing a partner for data destruction in Plano means finding a provider that combines deep local expertise with enterprise-grade capabilities. This is how you achieve total peace of mind, knowing your sensitive data is handled securely and compliantly from the moment it leaves your facility.
Securely retiring old hardware is a core part of any sound IT asset disposition (ITAD) strategy. This process goes beyond just destruction, often including the responsible recycling or remarketing of retired technology.
Ultimately, a secure and auditable destruction process provides the hard proof you need to demonstrate due diligence to auditors, stakeholders, and regulatory agencies.
Quick Guide to Data Destruction Essentials in Plano
To help Plano businesses navigate this, here’s a quick summary of the most important factors to consider when you're setting up a data destruction plan.
| Critical Factor | Why It Matters for Your Plano Business | Example Service Offered |
|---|---|---|
| Regulatory Compliance | Avoids heavy fines under laws like HIPAA, GLBA, and PCI-DSS by ensuring data is destroyed according to legal standards. | Certified destruction that meets NIST 800-88 and DoD 5220.22-M specifications. |
| Chain of Custody | Creates an unbroken, documented trail for every single asset, from your office to its final destruction, eliminating security gaps. | Secure, GPS-tracked transportation and serialized asset tracking from pickup to destruction. |
| Verification & Reporting | Provides the auditable proof your business needs to satisfy internal controls, auditors, and regulatory bodies. | A formal Certificate of Destruction and detailed asset reports for every project. |
| Destruction Method | Ensures data is truly unrecoverable. Methods must match the media type (e.g., SSDs vs. HDDs). | On-site or off-site physical shredding, degaussing, and certified data wiping. |
| Environmental Responsibility | Guarantees that non-data-bearing materials are recycled responsibly in line with R2 and EPA guidelines. | e-Stewards or R2 Certified downstream recycling for all shredded materials and e-waste. |
Thinking through these key areas ensures you're not just getting rid of old equipment, but you're also building a solid wall of protection around your business's most valuable asset: its data.
Why Simply Deleting Files Is Not Enough
It’s a common and dangerous misconception in many business environments: hitting “delete” or running a standard hard drive format is all you need to do to protect sensitive information. This assumption can, and often does, lead to serious data breaches.
Think of it this way: deleting a file is like tearing the table of contents out of a book. The chapters—your data—are all still there. You’ve just removed the easy guide pointing to where they are. Someone with widely available data recovery software can piece that guide back together and read every page you thought was gone for good.
The Illusion of Deletion
When you delete a file, your operating system doesn't actually wipe the data. Instead, it simply marks the space that file occupied as available to be overwritten with new information. The process only removes the file's address pointer, not the data itself.
Until that specific physical space on the drive is overwritten—which may not happen for a long time, if ever—the original file is completely recoverable. Formatting a drive is a similarly insecure process. It’s fast precisely because it only erases the address tables, leaving the underlying data intact and vulnerable.
This is the fundamental difference between standard deletion and certified data destruction. True destruction ensures data is forensically unrecoverable, not just hidden from view. It's the only way to guarantee your business's retired assets don't become a liability.
Real-World Consequences of Inadequate Destruction
A Texas-based B2B services company learned this lesson the hard way. They assumed their standard IT protocol of formatting old office PCs and servers was enough before sending them to a recycler. They believed their client lists, financial projections, and private employee records were permanently erased.
Months later, a security researcher contacted them after purchasing one of their old hard drives online. Using off-the-shelf software, the researcher had recovered nearly all of the supposedly "deleted" data. The incident exposed the company and its clients to significant risk, forcing a costly legal response and a complete overhaul of their IT asset disposal policies.
The stakes are incredibly high. Recent statistics show that 67.7% of companies experienced significant data loss in the past year, while the remaining 32.3% faced at least minimal incidents. The financial impact is just as severe, as you can see in the shocking cost of data loss detailed on Crashplan.com.
Professional data destruction in Plano isn’t just a best practice; it's an essential safeguard against this kind of preventable disaster. Understanding how to completely wipe a hard drive securely involves methods that go far beyond standard operating system functions. Certified physical destruction and data wiping are the only methods that provide a verifiable and permanent solution, ensuring your sensitive information never falls into the wrong hands.
Meeting Regulatory Compliance in North Texas
For any business in Plano or across the wider Dallas-Fort Worth area, getting rid of old IT hardware isn't just a cleanup task—it's a legal requirement. The maze of federal and industry rules can feel overwhelming, but a solid grasp of them is the foundation of a compliant data security program. Getting this wrong doesn't just open the door to a data breach; it can bring on staggering fines and brand damage that takes years to repair.
These regulations aren't just legal theory. They create a clear business need for auditable, verifiable proof that your data was properly destroyed. For any IT leader or compliance officer, if you can't prove you destroyed it securely, you haven't fulfilled your legal duty.
HIPAA for Plano Healthcare Providers
The Health Insurance Portability and Accountability Act (HIPAA) is the bedrock of patient data protection. This applies to every healthcare organization in the Plano area, from major hospital networks to local dental and medical practices, and it covers all electronic Protected Health Information (ePHI).
Think about that old patient check-in tablet sitting in a closet. It's likely filled with names, birth dates, and medical record numbers. Under HIPAA, you're legally obligated to make that ePHI completely "unusable, unreadable, or indecipherable to unauthorized individuals." Simply unplugging it and putting it away doesn't come close to meeting that standard.
What This Means for You: You need to work with a professional data destruction Plano service that issues a formal Certificate of Destruction. This document is your official evidence that the ePHI on that old device was destroyed in line with HIPAA rules, protecting your organization from fines that can easily climb into the millions.
NIST and DoD Standards for Tech and Government Contractors
If you're a Plano tech company in the Telecom Corridor, a defense contractor, or any business that handles sensitive government information, two standards are essential: NIST 800-88 and DoD 5220.22-M.
- NIST 800-88 (National Institute of Standards and Technology): This is the modern, authoritative guide for media sanitization. It specifies three methods—Clear, Purge, and Destroy. For the highest level of security, the "Destroy" method (physical destruction like shredding) is the only way to guarantee data is unrecoverable.
- DoD 5220.22-M (Department of Defense): While it's an older standard based on overwriting data, its principles are still referenced. However, for modern hard drives and SSDs, physical destruction is now the recognized best practice to meet and exceed this standard’s intent.
For a government contractor, failing to meet these standards on retired servers isn't just a simple mistake. It's a breach of contract that can get you barred from future government work, making certified data destruction a non-negotiable part of your operational security.
Financial and Reputational Penalties of Non-Compliance
The fallout from ignoring these regulations is serious. The penalties are intentionally severe to ensure organizations prioritize data security.
A Look at the Potential Fallout:
| Regulation | Potential Financial Penalties | Reputational Impact |
|---|---|---|
| HIPAA | Fines from $100 to $50,000 per violation, with an annual cap of $1.5 million for each type of violation. | Complete loss of patient trust, public relations nightmares, and potential civil lawsuits from affected people. |
| NIST/DoD | While not a law with direct fines, non-compliance can cause the loss of valuable government contracts and trigger severe contractual penalties. | Damage to your business reputation, getting blacklisted from federal projects, and losing your competitive edge. |
| GLBA | Fines for financial institutions can hit $100,000 for each violation, with the risk of prison time for executives. | Erosion of customer confidence, negative media coverage, and intense scrutiny from federal regulators. |
At the end of the day, investing in professional data destruction services in Plano isn't a cost center. It’s insurance against catastrophic financial and reputational damage that your business simply can't afford.
Choosing Your Destruction Method On-Site vs Off-Site
Once you’ve decided on certified data destruction, the next practical question for any Plano business is where it happens. The choice comes down to two service models: on-site destruction at your location or off-site destruction at a secure facility.
Each has its own clear advantages. The right fit depends entirely on your company’s security rules, logistical capacity, and budget. It’s a lot like paper shredding—you can have a truck come to your office parking lot, or you can have sealed bins picked up for destruction at a central plant. The end result is the same, but the process and the oversight are very different.
The Case for On-Site Mobile Destruction
On-site, or mobile, destruction brings the equipment directly to your Plano office. A specialized truck containing industrial-grade shredders pulls up to your building, and your team brings the IT assets out. You can physically watch every single hard drive, SSD, or tape get destroyed.
This approach offers the absolute highest level of security and immediate peace of mind. It’s the required method for many organizations with strict compliance or internal governance rules, including:
- Healthcare Providers: Hospitals and clinics governed by HIPAA often require visual proof that patient ePHI is destroyed before any assets leave the premises.
- Financial Institutions: Banks and investment firms in Plano need to ensure client financial data is verifiably destroyed, often with stakeholders present.
- Government Contractors: Any business handling classified data usually has contractual obligations to witness the destruction process firsthand.
The main benefit is the elimination of in-transit risk. Your assets never leave your property until they are nothing but shredded fragments, making the chain of custody as short and simple as possible. For any organization where a breach during transport is an unacceptable risk, on-site is the definitive standard.
The Efficiency of Off-Site Plant-Based Destruction
With off-site destruction, a certified vendor comes to your Plano location to pick up your IT assets. They are inventoried, sealed in locked containers, and transported in GPS-tracked vehicles to a secure processing facility. There, the assets are destroyed under constant video surveillance in a controlled environment.
This model is designed for efficiency and is often more cost-effective, especially for larger projects. Think about a data center decommissioning or a company-wide hardware refresh involving hundreds or thousands of drives. Processing that much equipment on-site could be disruptive and take a significant amount of time.
Key Insight: A secure chain of custody is the backbone of off-site destruction. A reputable vendor will scan and inventory every asset at your location before sealing them for transport, providing a detailed audit trail that follows your devices from pickup to final destruction.
Off-site is a great fit for businesses that need to dispose of a high volume of media and trust their partner’s certified, audited process. This is common for large corporate offices, school districts, and tech companies that don’t have a mandate for on-premise witness verification. It’s a secure, scalable, and budget-friendly solution for routine IT asset retirement.
To better understand the security protocols involved, you can learn more about on-site hard drive shredding services in Dallas and see how they compare to a plant-based process.
On-Site vs Off-Site Data Destruction A Comparison
For businesses in Plano, deciding on the right service model is a critical step. This table breaks down the key factors to help you determine which approach best aligns with your organization's priorities.
| Factor | On-Site (Mobile) Destruction | Off-Site (Plant-Based) Destruction | Best For… |
|---|---|---|---|
| Security | Maximum. Assets are destroyed on your premises, and you can witness the entire process. Chain of custody is absolute. | High. Relies on a rigorously documented and audited chain of custody with secure transport and plant-based surveillance. | Organizations with the highest security or compliance mandates requiring visual verification (finance, healthcare, government). |
| Cost | Generally higher due to the logistics of bringing heavy equipment and personnel to your location for a dedicated service. | Typically more cost-effective, especially for larger volumes, due to the economies of scale at a centralized facility. | Businesses with large quantities of media or those looking for a more budget-friendly but still highly secure option. |
| Logistics | Can require more coordination at your site, including scheduling and providing adequate space for the shredding truck. | Simpler for your team. The vendor handles the secure pickup and transport, minimizing disruption to your operations. | Companies undergoing large-scale hardware refreshes, data center decommissioning, or those with limited on-site space. |
| Verification | Direct visual confirmation that your assets have been destroyed, supplemented by a Certificate of Destruction. | A Certificate of Destruction, serialized audit reports, and optional access to video recordings of the destruction process. | Businesses that need definitive, auditable proof of destruction but do not require personal witness of the event. |
Ultimately, both on-site and off-site destruction are secure, professional solutions when performed by a certified vendor. The best choice is the one that meets your specific operational needs and compliance obligations.
The Importance of Chain of Custody and Reporting
A Certificate of Destruction is the final piece of the puzzle, but it’s only as good as the process that comes before it. Think of it as the finish line—the race to get there must be fully documented and secure. Without a rock-solid process, that certificate doesn't hold much weight.
It’s like shipping a priceless artifact. You wouldn’t just hand it to a random courier and hope for the best. You'd demand tracking numbers, signatures at every handoff, and confirmed delivery. The same exact logic applies to your sensitive data. The chain of custody is your tracking system.
Building an Auditable Destruction Record
A robust chain of custody for data destruction in Plano isn't optional; it's a series of non-negotiable steps that create an unbroken, defensible record. This is what turns a simple disposal task into a documented, compliant security procedure. It starts the second a technician walks into your facility and only ends when you have the final report in hand.
This meticulous documentation is specifically designed to stand up to scrutiny, whether from internal auditors, industry regulators, or even legal challenges. It proves you took every reasonable step to protect the data you were entrusted with, from its first touchpoint to final obliteration.
The core principle of chain of custody is simple: every single asset is tracked, every handoff is documented, and every step is verifiable. This creates an auditable trail that proves your due diligence and eliminates the security blind spots where data could easily be lost or compromised.
The Essential Steps of Secure Chain of Custody
A truly secure process follows a clear, repeatable blueprint. For any project, whether it’s on-site or off-site, you should expect your vendor to perform these critical actions:
- Serialized Asset Scanning: At your Plano location, technicians scan the unique serial number of every individual hard drive, server, or data-bearing device. This creates the initial inventory and officially starts the custody trail.
- Secure Containment and Transport: All assets are immediately placed into locked, sealed containers. For off-site destruction, the vehicles must be GPS-tracked, ensuring their location is monitored from your facility all the way to the secure plant.
- Transfer of Liability: You should always receive a document that formally transfers custody and liability for the assets to the destruction vendor. This is a crucial legal protection for your organization.
- Destruction and Verification: The assets are destroyed according to the agreed-upon standards. This is followed by a final check to confirm that all serialized items from the initial inventory list have been processed.
This flowchart shows how these steps are applied in both on-site and off-site data destruction scenarios.
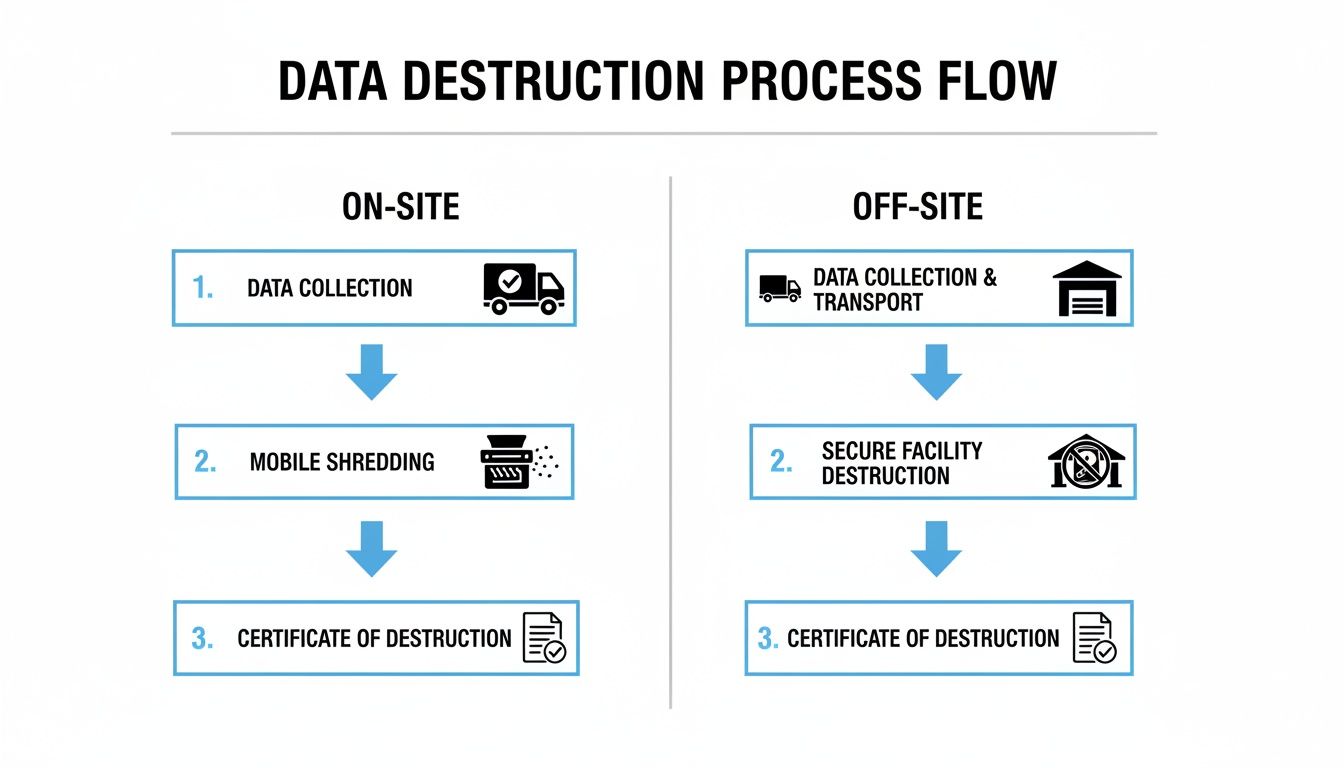
As you can see, while the location might change, the core principles of secure collection, verified destruction, and certified reporting stay exactly the same for both service models.
Your Final Proof of Compliance
At the end of the entire process, you should receive a documentation package that serves as your permanent compliance record. This isn't just one piece of paper; it’s a set of documents that, together, tell the complete story of your assets' secure end-of-life journey.
Demand these three essential documents:
- A Serialized Inventory List: This report details every single asset that was collected, identified by its unique serial number.
- A Transfer of Liability Agreement: This legal document officially transfers all responsibility for the assets from your company to the vendor.
- A Certificate of Destruction: This final certificate formally confirms that the listed assets were destroyed in compliance with specific standards like NIST 800-88.
For a deeper dive into what makes this final document so crucial for your records, you can learn more about the role of a Certificate of Destruction for hard drives in our detailed guide. This comprehensive reporting is what ultimately provides peace of mind and proves your organization’s commitment to data security.
Your Checklist for Vetting a Data Destruction Vendor
Choosing a partner for data destruction is a critical decision that directly impacts your organization's security and legal standing. It isn’t just about getting rid of old equipment; it’s about entrusting a vendor with your most sensitive information. To select a trustworthy and competent partner in the Plano area, you need to ask the right questions and know what a strong answer looks like.
Think of this process like hiring a security firm to protect your physical office. You wouldn't just pick the cheapest option. You’d run a background check, ask for credentials, and verify their procedures. The same level of scrutiny is essential when vetting a data destruction Plano vendor.
Are You Certified to NAID AAA Standards?
This should be your first and most important question. The National Association for Information Destruction (NAID) AAA Certification is the industry's gold standard. It’s a voluntary program where vendors undergo rigorous, unannounced audits to verify their security protocols, hiring practices, and destruction processes.
- Strong Answer: "Yes, we are NAID AAA Certified. You can find our certification number in the official NAID directory, and we can provide proof of our current standing." This response shows transparency and a commitment to independent verification.
- Red Flag: "We follow NAID standards" or "We are NAID compliant." These phrases are not the same as being certified. It means they haven't subjected their processes to third-party audits, leaving a significant gap in your security assurance.
Can You Detail Your Chain-of-Custody Procedure?
A secure chain of custody is the documented, unbroken trail your assets follow from the moment they leave your office to their final destruction. A vendor’s ability to clearly explain this process is a direct measure of their professionalism and attention to security.
A vague or confusing explanation of the chain of custody is a major warning sign. It suggests a process with potential security gaps where assets could be lost, misplaced, or mishandled without accountability.
Ask them to walk you through their entire process, from pickup at your Plano facility to the final reporting. This should include details on serialized asset scanning, locked transport containers, GPS-tracked vehicles, and secure facility access controls. A confident vendor will welcome this question and have a clear, concise answer.
What Specific Documentation Will I Receive?
The job isn't done until you have auditable proof in your hands. This documentation is your defense against legal challenges and your proof of compliance for both internal and external audits.
Your vendor should provide a comprehensive reporting package that includes:
- A Serialized Inventory List: This report must match every single asset you handed over, identified by its unique serial number.
- A Transfer of Liability: A formal document that legally transfers custody and responsibility for the assets from your organization to the vendor.
- A Certificate of Destruction: The final attestation that confirms all listed assets were destroyed in accordance with specific standards, such as NIST 800-88.
A vendor who only offers a generic certificate without serialized details is providing incomplete protection and leaving your organization exposed.
How Do You Handle Downstream E-waste Recycling?
Data destruction is only one part of the IT asset disposition process. After your hard drives are shredded, the remaining materials—metals, plastics, and circuit boards—become e-waste. Improper disposal can lead to environmental penalties and reputational damage.
Ask potential vendors if they are certified to R2 (Responsible Recycling) standards. This certification ensures that all downstream materials are handled in an environmentally responsible and secure manner. To learn more about this standard, check out our guide on what it means to be an R2 Certified electronics recycler.
A strong partner for data destruction in Plano will be able to provide clear answers on their recycling partnerships and prove their commitment to sustainable practices.
Frequently Asked Questions About Data Destruction
Even after deciding on a data destruction strategy, many Plano businesses still have questions about the finer points. We’ve put together straightforward answers to the questions we hear most often from IT directors, data center managers, and compliance officers in the area.
What Types of Media Can Be Destroyed?
Professional data destruction goes far beyond just old spinning hard drives (HDDs). Any device that stores digital information is a potential liability if it’s not properly decommissioned. A certified vendor can neutralize data on nearly any type of business asset.
This includes a wide range of equipment we handle every day:
- Solid-State Drives (SSDs): Because of their technology, SSDs must be physically shredded. Standard data wiping methods can leave recoverable data fragments behind.
- Magnetic Tapes: We process all formats of backup tapes, including LTO, DLT, and others.
- Servers and Network Gear: Entire server units, routers, switches, and other infrastructure can be securely processed and destroyed.
- Mobile Devices: Company-issued cell phones and tablets store a massive amount of sensitive corporate and personal data.
- Specialized Equipment: This can include proprietary data-storing components from medical, manufacturing, or laboratory devices.
A complete data destruction Plano service ensures every single data-bearing asset is accounted for and neutralized, regardless of its form factor.
Is Data Wiping as Secure as Physical Destruction?
The right answer really comes down to your goals for the asset and the sensitivity of the data on it. Both NIST-compliant data wiping and physical shredding are secure, but they’re designed for different outcomes.
Data wiping, also called sanitization, uses specialized software to overwrite a drive’s data with random characters multiple times. This makes the original data forensically unrecoverable. Wiping is a great choice when you want to preserve the physical drive for reuse, resale, or redeployment—especially for newer, high-value assets.
Physical destruction provides the absolute, verifiable guarantee that data is gone forever. Shredding a drive into tiny, confetti-like fragments makes recovery impossible. This is the required method for much of the highly sensitive data we handle and is the best practice for any end-of-life assets with no future use.
How Much Does Data Destruction Cost in Plano?
Data destruction pricing isn’t a one-size-fits-all model. The cost of your project is transparently based on a few key factors that determine the scope of the work.
Your quote will typically be based on:
- Volume of Media: The total count of hard drives, tapes, or other devices.
- Destruction Method: On-site shredding at your Plano facility is generally priced higher than off-site destruction at our secure plant due to logistics.
- Media Types: Different kinds of devices can require unique handling, which may influence the cost.
- Reporting Requirements: The level of detail needed for your audit trail and asset tracking can affect the final price.
A professional vendor will always provide a clear, itemized quote so you know exactly what you’re paying for.
How Do I Schedule a Pickup for My Office?
We designed our scheduling process to be simple and work around your business operations. A professional service provider prioritizes clear communication and logistical planning to ensure minimal disruption.
It usually starts with a quick phone call or an online form where you can outline your needs. From there, one of our specialists will coordinate a secure pickup window that fits your schedule, making the entire experience straightforward and secure from start to finish.
Ready to ensure your company’s sensitive data is destroyed with a certified, auditable, and compliant process? The team at Dallas Fortworth Computer Recycling offers secure on-site and off-site data destruction designed for the needs of Plano businesses. Contact us today to schedule your service and protect your organization from a data breach.
