Certified Electronics Recycler: A Guide for IT Directors
Old equipment tends to collect in places nobody budgets for and nobody owns. A locked storage closet. A corner of the server room. A cage in the warehouse with decommissioned switches, retired laptops, failed drives, and a few pallets of monitors from the last refresh. It looks like a space problem. It usually isn't.
For an IT director, that pile is a live risk register. Some of those assets still hold customer data, employee records, credentials, network maps, or regulated information. Others contain hazardous materials that can't be tossed into a general waste stream without creating environmental exposure. And once those assets leave your building, your risk doesn't disappear just because a vendor issued an invoice.
That is why the phrase certified electronics recycler matters. It doesn't mean "green vendor." It means you can demand documented process, verified controls, downstream accountability, and evidence that retired equipment was handled the right way.
Introduction The Hidden Liability in Your IT Storage Closet
Monday morning after a refresh project, the new laptops are deployed, the old switches are stacked in a cage, and three boxes of hard drives are sitting in a locked closet waiting for "next steps." Everyone assumes someone else owns the problem. That is how low-value surplus turns into a compliance issue with no chain of custody, no disposition record, and no clear answer when audit, legal, or security asks what happened to the assets.
The financial risk is usually hidden at first. Storage looks cheap. Delay looks harmless. Then a lease return misses its deadline, serialized assets disappear from inventory, a downstream vendor charges for hazardous items nobody identified in advance, or a data-bearing device leaves the building without documented sanitization. At that point, the cheapest disposal option is often the most expensive decision in the process.
The broader waste stream shows why informal handling fails so often. First America's e-waste statistics overview reports that the world generated 53.6 million metric tons of e-waste in 2019, with only 17.4% formally collected and properly recycled. In the U.S., 6.9 million tons were generated and about 15% was recycled.
For an IT director, the practical question is not whether old equipment should leave the building. It is whether the handoff can stand up to audit, incident response, and procurement review.
A proper IT asset disposition process ties together data security, environmental handling, asset tracking, and final disposition records. That changes the conversation from "Who can pick this up fastest?" to "Which partner reduces total exposure and can prove it?"
Why the storage closet is a governance issue
Retired equipment in storage usually falls into four risk buckets:
- Data-bearing devices that require documented sanitization or physical destruction.
- Infrastructure equipment such as servers, network gear, and UPS units that need controlled deinstallation, packing, and transport.
- Commodity electronics that may have resale value, parts recovery value, or material recovery value if sorted correctly.
- Exception items such as damaged batteries, broken screens, and legacy equipment that trigger special handling, extra fees, or added regulatory review.
One rule applies to all of them.
Practical rule: If your team cannot produce a chain of custody for retired equipment, the risk has not been removed. It has been transferred without proof.
That distinction matters. A recycler is not just hauling away scrap. Your company is handing over data risk, environmental obligations, and audit exposure at the same time.
What 'Certified' Actually Means for Electronics Recycling
A certified recycler is not just a company that says it recycles electronics. Certification means an independent program has audited the facility and its processes against defined requirements for environmental management, worker safety, operational controls, and data security.
That distinction is the entire decision.
A non-certified vendor might still be honest and competent. The problem is that you have no structured proof. You're relying on sales language, a pickup truck, and a promise that "everything gets handled properly." That isn't a control environment. That's trust without verification.

Certified process versus informal handling
Consider the difference between hiring a certified mechanic versus a person with a wrench in a parking lot. Both can touch the car. Only one works inside a documented system with inspection criteria, traceability, and accountability when something goes wrong.
The EPA pushed certification programs such as R2 and e-Stewards because electronic waste is growing 2-3 times faster than other municipal waste streams, and an estimated 80% of e-waste is untracked and likely dumped or improperly handled, according to the EPA's certified electronics recycler guidance.
That background matters for procurement because the biggest failures in this industry don't happen at the front door. They happen downstream. Material gets aggregated, resold, exported, stripped for value, or processed by subcontractors the original client never sees.
What certification changes in practice
Certification turns "we recycle responsibly" into something you can test. In practice, that means asking for evidence in areas like these:
- Scope of operations where the recycler can show which services and facilities are covered by certification.
- Documented intake controls for serialized receiving, asset logging, and exception handling.
- Data destruction procedures tied to specific media types, not broad claims.
- Downstream vendor controls so materials don't disappear into an unverifiable chain.
- Audit records from an outside body rather than internal policy statements alone.
A certified electronics recycler should be comfortable with scrutiny. If a vendor becomes evasive when you ask who handles downstream materials or how they document destruction events, that tells you more than a logo on a website ever will.
The badge matters less than the auditable behavior behind it.
What certification does not mean
It doesn't mean every item is free to recycle. It doesn't mean every asset is shredded. It doesn't mean every device is resold. It doesn't mean zero operational mistakes are possible.
It means the recycler operates inside a monitored framework designed to reduce those risks and to document what happened if your legal, security, compliance, or audit team asks later.
That is the practical value. Certification gives IT leaders a basis for governance, not just a marketing claim.
Decoding the Major E-Waste Certifications R2 and e-Stewards
Most IT directors don't need a philosophical debate about certifications. They need to know what the standard requires, what proof it creates, and whether it aligns with their risk tolerance.
The two certifications you will see most often in U.S. electronics recycling are R2 and e-Stewards. Both exist because clients need stronger controls than ordinary scrap handling provides. Both are recognized by the EPA. Both are meant to improve accountability in how retired electronics are managed.
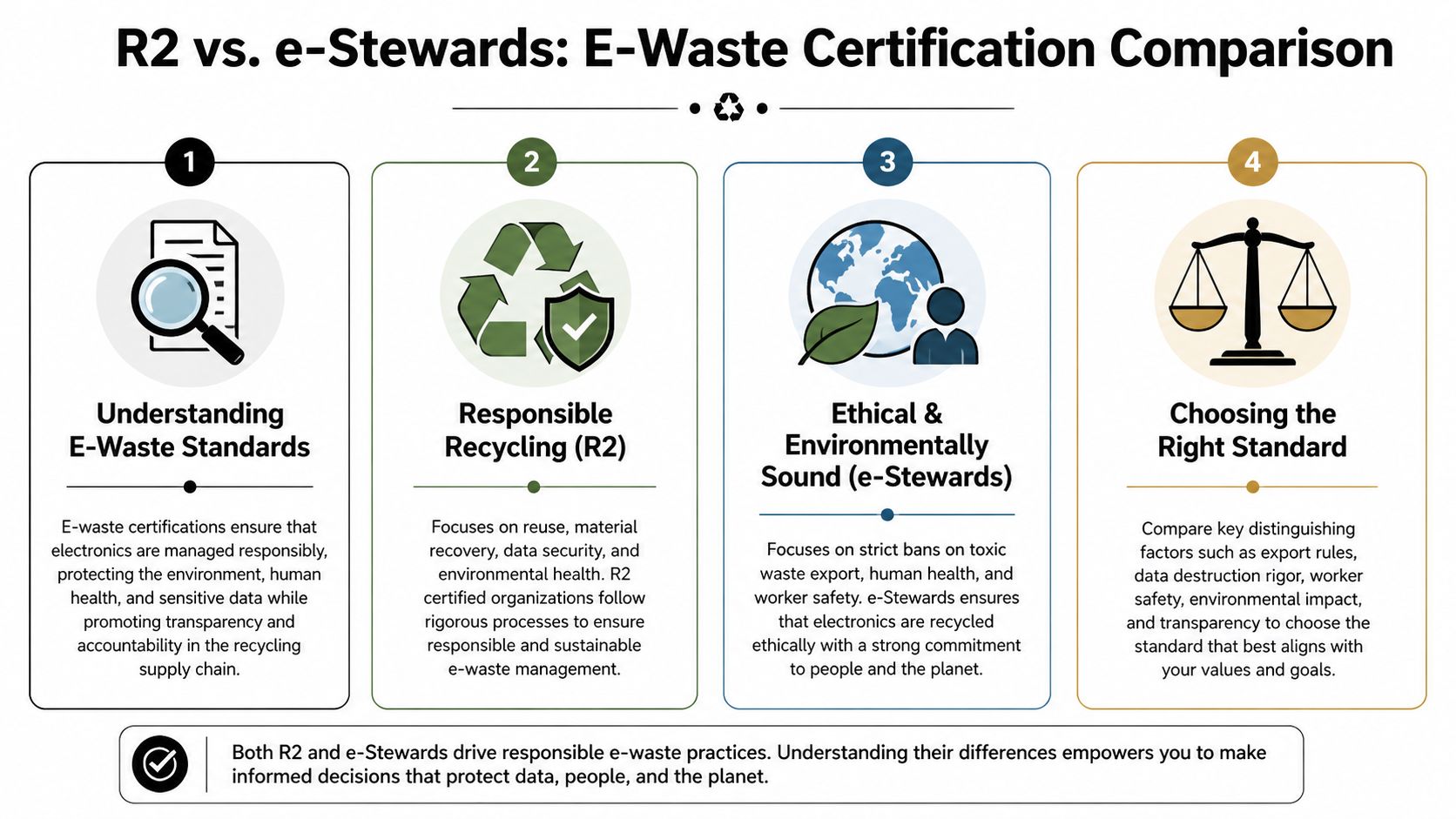
What R2 emphasizes
R2 is widely used across the industry and is built around controlled reuse, repair, recovery, and responsible disposition. For IT leaders, the operational strength of R2 is that it forces a recycler to manage the full reverse supply chain instead of only the first processing step.
The current standard is often discussed as R2v3, and facilities operating under it must show rigorous process control. According to R2v3 process details summarized by an audited provider, certified facilities can achieve landfill diversion rates exceeding 95%, must demonstrate over 90% recovery efficiency for focus materials, and must meet strict hazardous release limits through third-party audits.
Those aren't abstract environmental points. They directly affect vendor selection. If a recycler is certified under a standard with this level of materials handling discipline, you can expect stronger controls over dismantling, segregation, downstream processing, and documentation.
A useful reference point is this R2 certified electronics recycler overview, which explains how organizations use certification as a screening requirement rather than a nice-to-have.
What e-Stewards emphasizes
e-Stewards is typically chosen by organizations that want a stricter ethical position, especially around export risk and social responsibility. Its reputation in the market comes from a harder line on where hazardous e-waste can end up and how labor and environmental protections are enforced throughout processing.
For an IT director, the practical implication is straightforward. If your legal, ESG, procurement, or board oversight environment demands the strongest stance on downstream ethics, e-Stewards may fit your policies better.
The decision isn't logo versus logo
The better comparison is control profile versus control profile.
| Certification | Practical strength for IT teams | Best fit |
|---|---|---|
| R2 | Strong operational framework for reuse, recovery, data security, and downstream accountability | Organizations that need scalable ITAD with auditable process control |
| e-Stewards | Stricter posture on export and ethical handling concerns | Organizations with heightened ESG, legal, or reputational sensitivity |
What to verify beyond the label
When I review vendors, I don't stop at "Are you certified?" I want to know whether the certification covers the services my client needs.
Look at these specifics:
- Facility scope: Is the actual processing location certified, or only a related site?
- Service scope: Does the certification cover data-bearing assets, dismantling, and downstream management relevant to your project?
- Audit status: Can the recycler provide current proof without hesitation?
- Chain of custody: Are custody transfers documented from pickup through final processing?
- Exception handling: What happens to damaged, mixed, or nonstandard devices?
Decision lens: Pick the standard that matches your organization's risk posture, then verify the recycler's actual operating controls. Certification without scope clarity is weak due diligence.
The logos matter. The operating discipline matters more.
The Business Case Benefits vs The Unseen Risks
Most failed recycling decisions don't fail because someone ignored sustainability. They fail because someone optimized for pickup price and ignored total risk.
That is the wrong metric.
A certified electronics recycler should be evaluated the same way you evaluate a security control, a cloud provider, or a managed service partner. The question isn't "How cheaply can this vendor remove old equipment?" The question is "What liabilities is this vendor taking off our balance sheet, and what liabilities are they implicitly adding back?"
Where certified partners create business value
The benefits are operational, not cosmetic.
A certified partner gives IT and compliance teams something they can defend in an audit. That includes chain-of-custody records, documented data sanitization, and proof that retired assets followed an approved handling path. For regulated organizations, that paper trail is often as important as the physical destruction event itself.
Certified providers also support internal reporting. Security can confirm media handling. Procurement can validate vendor controls. Sustainability teams can report responsible diversion and material recovery using documented records instead of assumptions. If your organization cares about the benefits of e-waste recycling, those benefits only become credible when the process is documented.
What non-certified choices often hide
The risk isn't just poor environmental handling. It is loss of visibility.
A low-cost vendor may outsource transport, outsource wiping, outsource downstream processing, and still present a single invoice as if the chain were unified. If one step fails, your organization owns the consequences. The vendor may disappear. Your company name will not.
The unseen risks usually show up in these forms:
- Weak data controls where "wiped" means unverified handling by a third party.
- Missing audit records that leave legal and compliance teams with no defensible documentation.
- Downstream opacity where nobody can clearly state where materials went after first touch.
- Procurement distortion because the cheapest quote excluded reporting, special handling, or secure logistics.
- Brand exposure if equipment is later found dumped, exported improperly, or processed under questionable labor conditions.
A cheap recycling quote often excludes the controls your auditors expect. You only discover the difference when someone asks for proof.
A practical TCO view
Here is the framework I use with IT directors.
| Cost area | Non-certified vendor | Certified recycler |
|---|---|---|
| Pickup price | May look lower upfront | May include more controlled handling |
| Data destruction proof | Often vague or minimal | Usually structured and auditable |
| Downstream visibility | Frequently limited | Expected as part of vendor control |
| Internal audit support | Harder to assemble later | Easier to defend with documentation |
| Reputational risk | Higher if materials are mishandled | Reduced through verified process |
This is why the business case should be framed as total cost of ownership, not disposal line item cost.
An uncertified vendor can look inexpensive because they have pushed critical work outside the quote. Your team then spends time chasing manifests, validating destruction, answering audit questions, and resolving exceptions. That internal labor is real cost. So is the legal and reputational exposure if the process breaks.
What works and what doesn't
What works is simple. Standardized intake, secure transport, clear media handling methods, downstream documentation, and final reporting tied to actual assets.
What doesn't work is verbal assurance, generic certificates, broad sustainability language, and invoices that tell you what was paid but not what was done.
If you are accountable for infrastructure, security, or compliance, certification is not overhead. It is a purchasing control.
A Procurement Checklist for Selecting Your Recycling Partner
Most vendor reviews stop too early. The buyer confirms the company takes electronics, checks for a certificate on the website, gets a quote, and schedules pickup.
That approach misses the expensive questions.
Pricing for certified recycling is often opaque. Some nonprofits charge by the pound for certain items, and rising precious metal recovery can offset costs for high-volume B2B clients. The operational difference is that stronger vendors provide transparent quotes that include logistics, data sanitization, and auditable reporting, as outlined in this pricing and partner overview.
The quote should explain the process
If a proposal doesn't tell you what happens after pickup, it isn't a complete procurement document.
Ask the vendor to break the quote into operational components. I want to see whether the recycler is pricing transportation, on-site labor, packing, media destruction, serialized reporting, and special handling separately or bundling them into a line item that hides trade-offs.
A useful market comparison point is to review how different computer recycle companies structure services. You quickly see that the quote format itself reveals maturity. Better vendors describe process. Weak vendors mostly describe pickup.
Certified Recycler Vendor Evaluation Checklist
| Category | Question/Verification Item | Importance |
|---|---|---|
| Certification | Is the facility currently certified under R2, e-Stewards, or both, and does the certification apply to the actual processing location? | Confirms the vendor is operating under audited controls rather than marketing claims |
| Scope | Does the certification cover the services you need, including data-bearing devices, dismantling, and downstream management? | Prevents false comfort from a certificate that doesn't match your project |
| Data destruction | What sanitization or destruction methods are used for hard drives, SSDs, and other media, and what documentation is issued afterward? | Protects against breach risk and weak audit evidence |
| Chain of custody | How is equipment tracked from pickup through final disposition, and where are custody transfers recorded? | Creates defensible records for compliance and internal review |
| Downstream vendors | How does the recycler qualify and monitor downstream processors? | Reduces the risk of hidden export or improper processing |
| Logistics | Who performs pickup, what security controls are used in transit, and how are site-specific requirements handled? | Transportation is a common weak point in otherwise solid programs |
| Reporting | Will you receive serialized reporting, destruction records, and recycling documentation matched to your asset list? | Necessary for audit readiness and asset reconciliation |
| Insurance and liability | What coverage does the vendor maintain for environmental and data-related exposure? | Helps procurement and legal assess residual risk |
| Fee transparency | Are there charges for older displays, damaged equipment, mixed loads, or hazardous components? | Avoids surprise invoices after collection |
| Value recovery | Can reusable assets generate credit or offset charges, and how is that value documented? | Supports a more accurate TCO analysis |
| Service responsiveness | Can the vendor handle multi-site pickups, decommissioning windows, and restricted access schedules? | Important for enterprise rollouts and facility coordination |
Questions that separate strong vendors from weak ones
These are the questions I recommend asking live on a call, not just by email:
- Show me the reporting package: Ask for a redacted sample of the final documentation.
- Walk me through an exception: Find out what happens when they receive damaged, unlabeled, or unauthorized items.
- Explain your downstream path: If the answer is fuzzy, the process probably is too.
- Detail the fees: Specifically ask about displays, batteries, mixed pallets, loose drives, and equipment requiring manual handling.
- Clarify value return: If resale or commodity recovery applies, ask how the calculation is documented and when credits are issued.
Procurement test: If a vendor can explain security controls in detail but can't explain pricing detail, expect a billing dispute. If they can explain pricing but not controls, expect a compliance problem.
What a good quote looks like
A good quote is not always the lowest. It is the one that lets your team predict the full engagement.
You should be able to answer these questions before issuing a purchase order:
- What exactly will be picked up?
- How will assets be tracked?
- How will data-bearing items be handled?
- What events generate added charges?
- What final records will we receive?
If the answer to any of those is "we'll figure it out after pickup," keep looking.
How Dallas Fortworth Computer Recycling Delivers Auditable Compliance
A strong ITAD engagement should feel controlled from the first call to the final certificate. Not flashy. Not vague. Controlled.
That means the recycler gathers enough operational detail before pickup to define scope, identify regulated or unusual equipment, plan transportation, and set reporting expectations. The job should not depend on improvisation once the truck arrives.
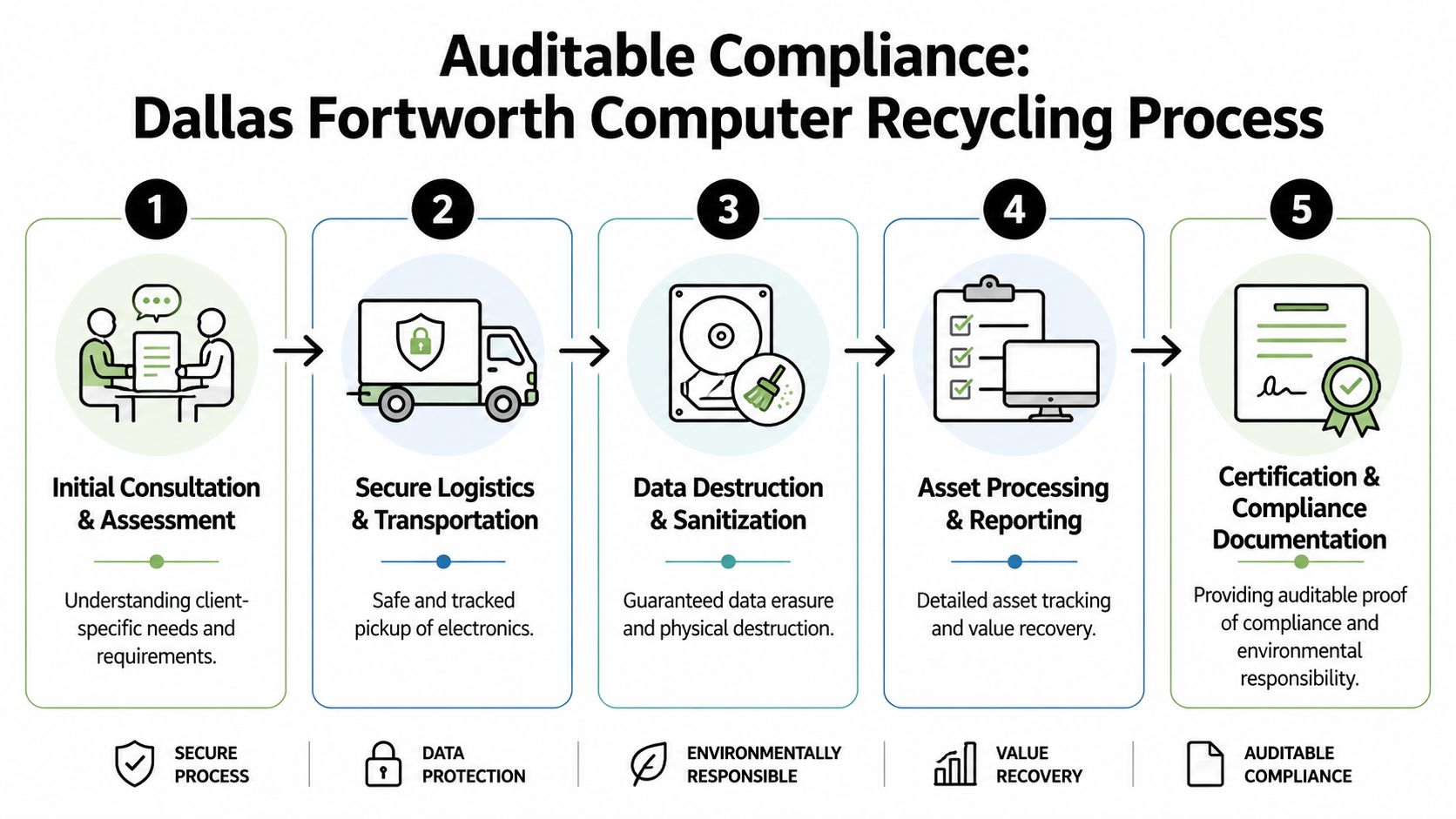
What a disciplined engagement looks like
Dallas Fortworth Computer Recycling is built for organizations that need nationwide B2B service, secure handling, and documented compliance. In practice, that means the engagement starts with assessment, not dispatch. The provider clarifies asset types, pickup conditions, access limits, and reporting needs before scheduling logistics.
During collection, the key issue is custody control. Equipment has to move from the client site into a documented handling stream, with each transfer recorded in a way the client can defend later. That matters most in office closures, refresh cycles, and data center decommissioning projects where multiple stakeholders are involved and asset counts can shift quickly.
The five steps that matter
This is the operational pattern IT leaders should expect:
Initial consultation and assessment
The recycler reviews asset mix, project timing, site conditions, and any compliance requirements tied to the equipment.Secure logistics and transportation
Pickup is scheduled around business constraints, and the movement of equipment is controlled rather than treated like ordinary freight.Data destruction and sanitization
Media-bearing devices are handled under defined destruction or sanitization procedures so the client can document what happened to the data, not just the hardware.Asset processing and reporting
Equipment is sorted for reuse, recovery, or recycling, with reporting tied back to client expectations for auditability.Certification and compliance documentation
The client receives records that support internal security review, procurement validation, and regulatory response if needed.
Why documentation is the real deliverable
The physical work matters, but the lasting value is in the records. When a recycler issues a certificate of destruction for hard drives, the point isn't paperwork for its own sake. The point is to create evidence your organization can produce later.
That is where experienced providers separate themselves from commodity haulers. They understand that the audience for final documentation isn't just IT. It may also be legal, compliance, internal audit, risk management, finance, and board-level oversight.
Your recycler is part of your compliance chain. Choose one that behaves like it knows that.
Why this model works for enterprise clients
Mid-size and enterprise teams usually need three things at once: predictable scheduling, secure media handling, and reporting that can stand up to scrutiny. Dallas Fortworth Computer Recycling's operating model is aligned with that reality. Its nationwide service approach, responsiveness, and focus on B2B workflows reflect what procurement and infrastructure teams need during large retirement events.
The result is not just cleaner disposition. It is less internal friction. Fewer unanswered questions. Fewer last-minute exceptions. Better records when someone asks, months later, what happened to a specific batch of drives or a retired rack of servers.
That is what auditable compliance looks like in practice.
Conclusion From End-of-Life Disposal to Strategic Lifecycle Management
A certified electronics recycler isn't a convenience vendor. It is a risk-control decision.
The equipment sitting in storage, stacked in a lab, or caged in a data center has already reached the point where ordinary operational thinking stops working. At end of life, the important questions are no longer performance and uptime. They are chain of custody, data destruction, downstream accountability, environmental handling, and audit evidence.
That shift is why mature IT organizations treat ITAD as part of lifecycle management, not cleanup.
The practical framework is clear. Verify certification. Confirm scope. Review downstream controls. Demand transparent pricing. Inspect the reporting package before pickup. If a recycler can't provide auditable answers before the work starts, they won't provide them after the equipment leaves your site.
A good partner doesn't just remove retired assets. A good partner helps IT, security, procurement, and compliance close the loop in a way the business can defend.
That is the business case. Less hidden liability. Better auditability. Stronger control over data, environmental exposure, and vendor risk.
If your team needs a partner that treats electronics disposition as a compliance and security function, not just a pickup service, Dallas Fortworth Computer Recycling can help. They support nationwide B2B IT asset disposition, secure data destruction, data center decommissioning, and documented end-of-life processing for organizations that need clear chain of custody and audit-ready reporting.
